Sabitlenmiş Tweet
Greg Bailey
3.2K posts


Greg Bailey
@GRBail
Analyst @HuntressLabs | Instructor @SANSInstitute | neo-hippie | grateful dad | all around nice guy
Chicago, IL Katılım Haziran 2011
1.6K Takip Edilen757 Takipçiler
Greg Bailey retweetledi
Greg Bailey retweetledi

MICROSOFT OPEN-SOURCED THEIR ENTIRE SENTINEL SECURITY TOOLKIT
most teams building on azure figure out threat detection the hard way
trial and error, custom KQL, dashboards built from nothing, playbooks written by hand
nobody told them it was already done
the sentinel github repo has:
▫️ 1000+ pre-built threat detection rules
▫️ hunting queries for active threat investigation
▫️ automated response playbooks
▫️ security workbooks + dashboards
▫️ data connectors for 100s of sources
the hard part was already done
github.com/Azure/Azure-Se…
English
Greg Bailey retweetledi

On May 5, Huntress Threat Intel Analyst Casey Smith and special guest @sherrod_im, GM of Global Threat Intel at @MsftSecIntel, are breaking down what happened, why it worked, and how defenders can fight back.
Save your spot for the live event: okt.to/xAEr3a
#MSPartner

English
Greg Bailey retweetledi
Greg Bailey retweetledi

Last week, the Huntress SOC observed Nightmare-Eclipse tooling, including BlueHammer, RedSun, and UnDefend, during a real-world intrusion investigation.
@Curity4201 breaks down the details. 🔍
Check out the full write-up: okt.to/uUzJOA
English
Greg Bailey retweetledi

Got to work on this with the legend @_JohnHammond. A user asked Codex to fix suspicious behaviour on their machine. Codex "solved" it, but the cryptominer kept running.
Plus: How Gen-AI noise is complicating investigations and how SOCs need to evolve.
huntress.com/blog/codex-par…
English
Greg Bailey retweetledi

The Huntress SOC is observing the use of Nightmare-Eclipse's BlueHammer, RedSun, and UnDefend exploitation techniques.
Investigation by: @wbmmfq, @Curity4201, + @_JohnHammond 🧵👇

English
Greg Bailey retweetledi
Greg Bailey retweetledi
Greg Bailey retweetledi

There's a dark enterprise out there growing faster than any other business on earth.
And it's your hidden competition.
On March 18, @_JohnHammond and @JimBrowning11 are exposing how cybercriminal organizations actually operate.
Save your spot: okt.to/xagoFA
English
Greg Bailey retweetledi

Mohammad Muzahir thought he was taking a legit IT job.
Instead, he was trafficked into a scam compound and forced to defraud people under threat of violence.
What he shared with us pulls back the curtain on how the system works. ⬇️
okt.to/TbtHfk
English
Greg Bailey retweetledi

Coming up on #TradecraftTuesday, we're breaking down AppDomainManager Injection, a technique cybercriminals are using to turn legit .NET binaries into "living-off-the-land" weapons. 👀
Join us live next week to see exactly how it works: okt.to/rhWcDs
English
Greg Bailey retweetledi

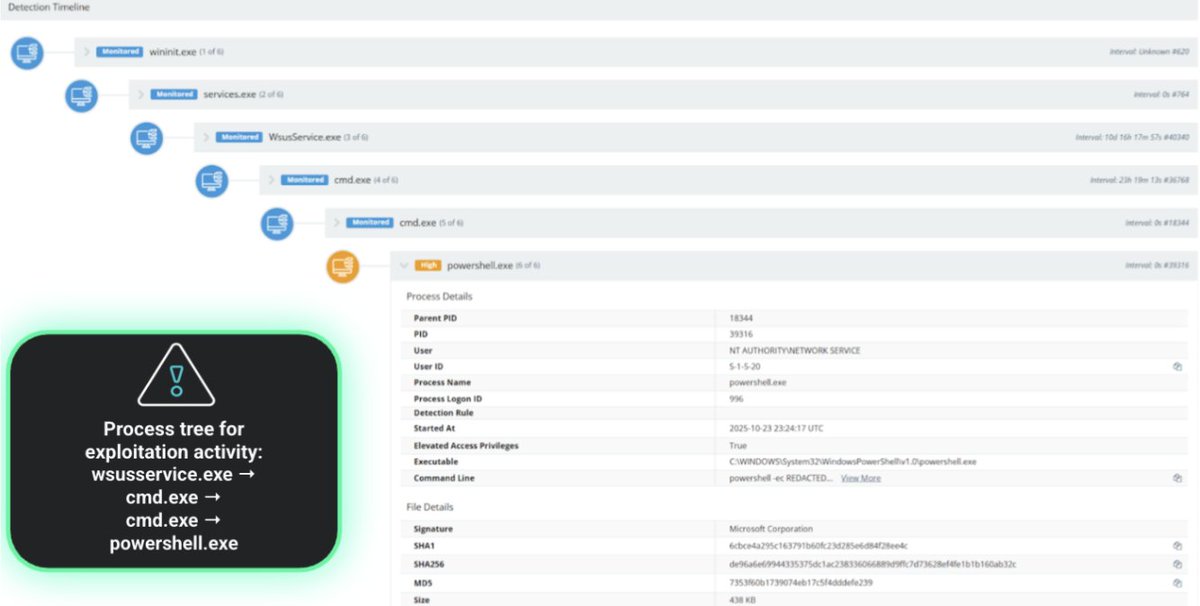
CVE-2025-59287 is being actively exploited. Update Windows Server Update Services now to reduce risk of a threat actor achieving remote code execution with system privileges. See our Alert for details ➡️ go.dhs.gov/in5 #Cybersecurity
English
Greg Bailey retweetledi

⚠️ Threat actors exploiting a recent Microsoft WSUS vulnerability (CVE-2025-59287)
- Microsoft released an out-of-band update for the flaw on 10/24
✅ Apply the update as soon as possible
IOCs, examples of adversary tradecraft, and remediations: okt.to/0eJ3zw
English

Wait, did @MLB really put playoff baseball in the middle of the week with a 1PM start?
English

One of the reasons I moved to @HuntressLabs is to work side-by-side with peers I respect.
huntress.com/blog/dont-swea…
English
Greg Bailey retweetledi
Greg Bailey retweetledi