Osama h0$#@ retweetledi
Osama h0$#@
558 posts


@rez0__ @WorstWursts Context??
I checked his profile and it’s all about “I and worst….” 😅
English

I and @WorstWursts successfully articulated impact to Amazon***
Fixed that for you
.@696e746c6f6c
I and @WorstWursts beat Amazon. After months without a payout, the Amazon team has today readjusted our report's severity to critical. This is insane, lets fucking goo!
English

@Hajjaj0x محفظه بينانس ومن المحفظه بيع عبر p2p ولابتخسر شي ويمكن تكسب فارق الصرف ةمن المشترييين كثير
العربية
Osama h0$#@ retweetledi

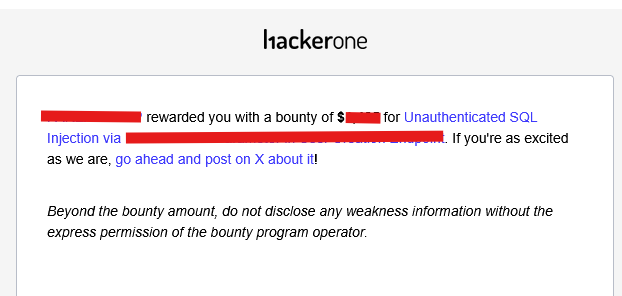
SQL Injection in GraphQL/WebSocket Escalated to PII Document Leak by DarkyOS @DarkyOS/sql-injection-in-graphql-websocket-escalated-to-pii-document-leak-09ba7ad2800a" target="_blank" rel="nofollow noopener">medium.com/@DarkyOS/sql-i… #bugbounty #bugbountytips #bugbountytip
English
Osama h0$#@ retweetledi

How I Got Into Starbucks' Internal Network using a non resolvable hostnames
credit: @damian_89_
argosdns.io/blog/how-i-got…
English
Osama h0$#@ retweetledi
Osama h0$#@ retweetledi

Last year I found a MXSS (dream) bug in a Mail app,it involved bypassing 2 consecutive sanitizers recursive Dompurify calls plus CKEditor.Hope you will like it
sudistark.github.io/2026/04/07/mxs…
All thanks to @kevin_mizu for putting such great content around mxss and those bypasses🙇♀️
English
Osama h0$#@ retweetledi

How I Earned $76,000 From a Single Program on Bugcrowd
anonhunter.medium.com/how-i-earned-7…
English
Osama h0$#@ retweetledi

he started in 2025 and pwned every feature of a public programs MAIN APP. im proud of my boy but this just goes to show, anything is possible with the right mindset. keep up the great work twin. 🕷️🙏🏾
sin99xx@sin99xx
Last one, now I'm gonna spend time on learning more coz I guess I found everything from last research.
English
Osama h0$#@ retweetledi
Osama h0$#@ retweetledi

I just published a full write-up about how I discovered a blind SQL injection in a private bug bounty program.
@mrx_w_/how-i-discovered-a-blind-sql-injection-in-a-private-program-7eebd77ad286" target="_blank" rel="nofollow noopener">medium.com/@mrx_w_/how-i-…
#BugBounty #BugBountyTips #Bugcrowd #CyberSecurity

English
Osama h0$#@ retweetledi

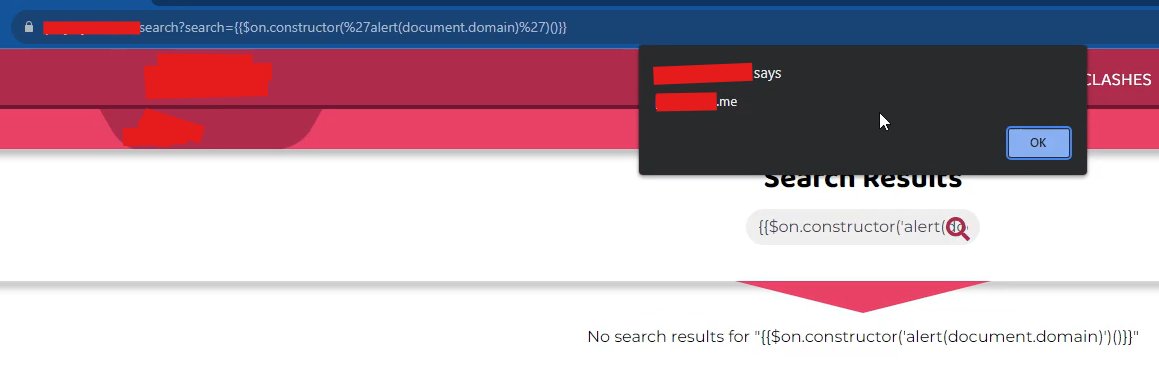
Simple XSS payload for AngularJS testing.
Older AngularJS versions are still vulnerable to expression injection.
{{$on.constructor('alert(document.domain)')()}}
#BugBounty #XSS #bugbountytips #hackerone
English
Osama h0$#@ retweetledi

Finding the right SQLi payload isn’t always easy
@lu3ky13
Built this with AI (obsidianlabs.cloud) For POC:
';IF(LEN(USER_NAME())>=5)WAITFOR DELAY '0:0:20'--
#BugBounty #SQLi #bugbountytips #hackerone #SQL
Casper0x@_casper0x
Finding the right SQLi payload isn’t always easy. If you can’t craft custom logic, use Time-Based techniques to prove control. Built this with AI (obsidianlabs.cloud) for a POC: ';IF(LEN(USER_NAME())>=5)WAITFOR DELAY '0:0:20'-- #BugBounty #SQLi #bugbountytips #hackerone
English
Osama h0$#@ retweetledi

four bugs to the same program, 1-click rce (lowerd to high), 3 access token leaks (some lowered to medium). what is impressive, no single response from the program for about 5 months, h1 mediation didn't reply, what is going on? h1 is dead?! @Hacker0x01 what?!
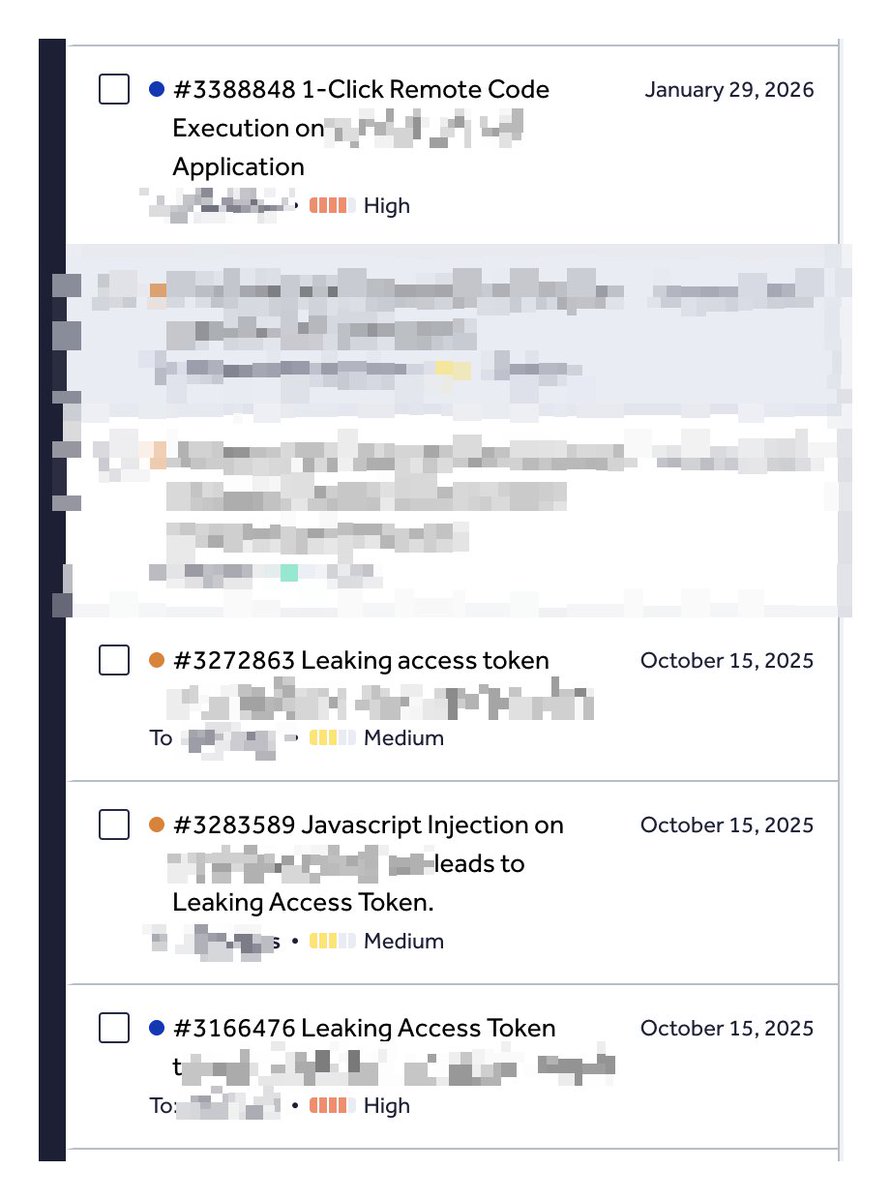
English
Osama h0$#@ retweetledi

$1,500 Recon Secrets: Dorks to Dollars @tinopreter/1-500-recon-secrets-dorks-to-dollars-0e7eca022708" target="_blank" rel="nofollow noopener">medium.com/@tinopreter/1-…
English
Osama h0$#@ retweetledi













