HashDit | now with Pro Extension
1.1K posts


@HashDit
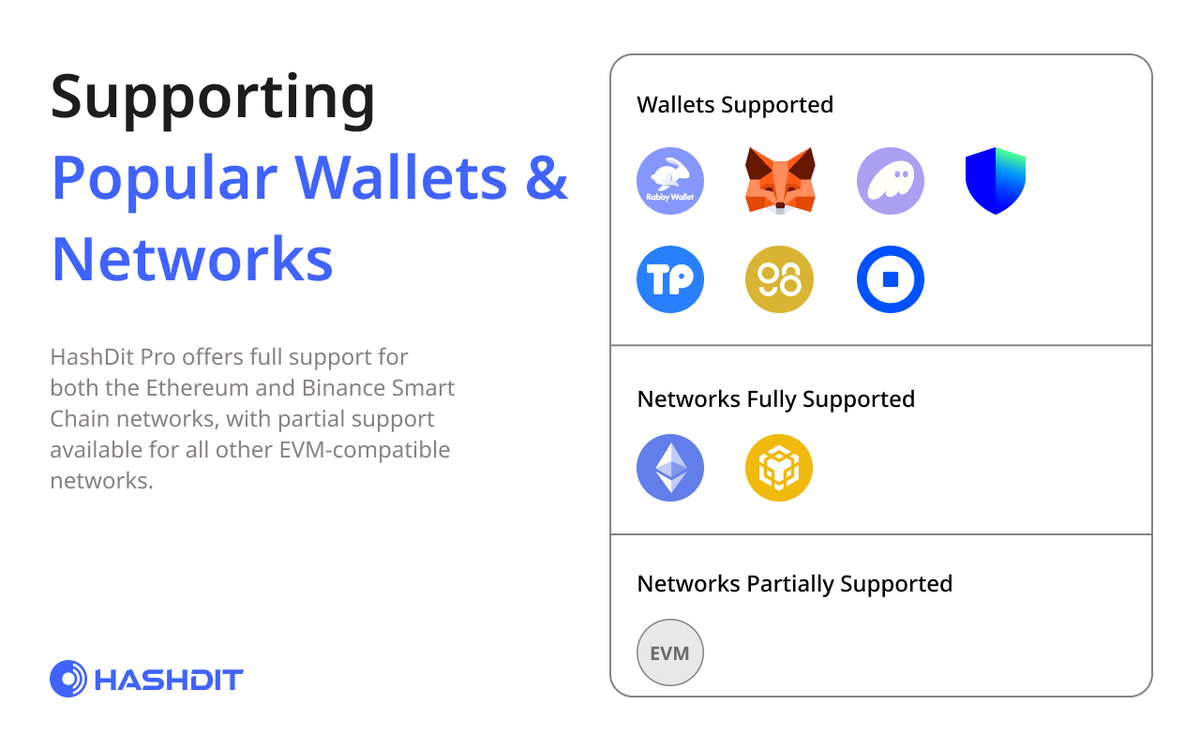
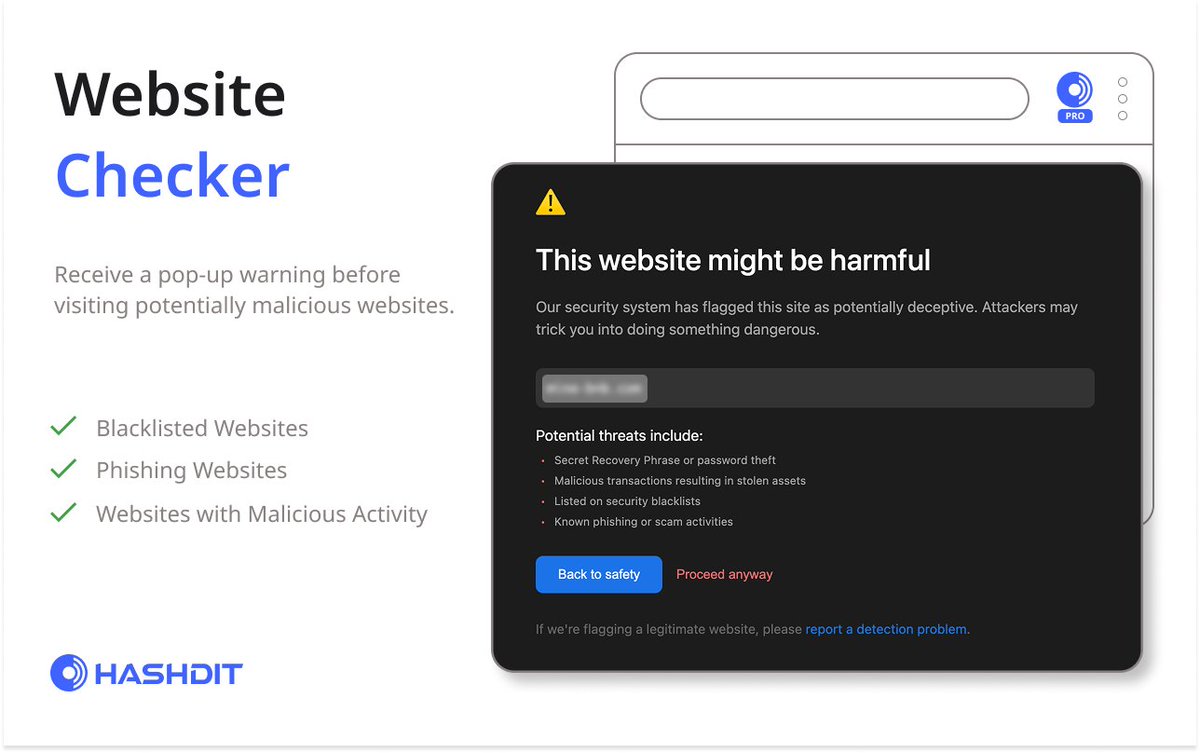
Web3 Security Firm - Defending against Hacks & Scams on #BSC & More! 🛡️ Users stay safe with our Chrome Extension & Metamask Snaps! ⚙️ Links below 👇




🚨 Socket detected malicious activity in newly published versions of node-ipc, an npm package with 822K weekly downloads. Affected versions: node-ipc@9.1.6 node-ipc@9.2.3 node-ipc@12.0.1 Socket’s AI scanner flagged the malware within ~3 minutes of publication. Early analysis shows obfuscated stealer/backdoor behavior, including host fingerprinting, local file enumeration, payload wrapping, and attempted exfiltration.







🚨 WARNING: Recently, there has been a rise of Web3 Crypto X Accounts being compromised. Through our investigation, we noticed there has been a 6 month campaign of scam X phishing emails usually preying on the urgency to 'verify' their account. So what should you do if you are a social media manager: 🧵👇 1. Be wary of what email you are interacting with. Hover your mouse over 'sender' to check the sender’s domain (should end in @x.com or @help.x.com). On mobile, you can tap and hold to view the 'sender'. 2. Be extra vigilant of any unknown DMs across all social media asking for any collaborations or partnerships. 3. Be careful what Third-Party App or X account you will be connecting or delegating too. Regularly check permissions and revoke if unused. Stay safe!! #CryptoScams #Web3 #Cybersecurity


We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: vercel.com/kb/bulletin/ve…