
Jeff Murri
6.9K posts


@InfoSec208
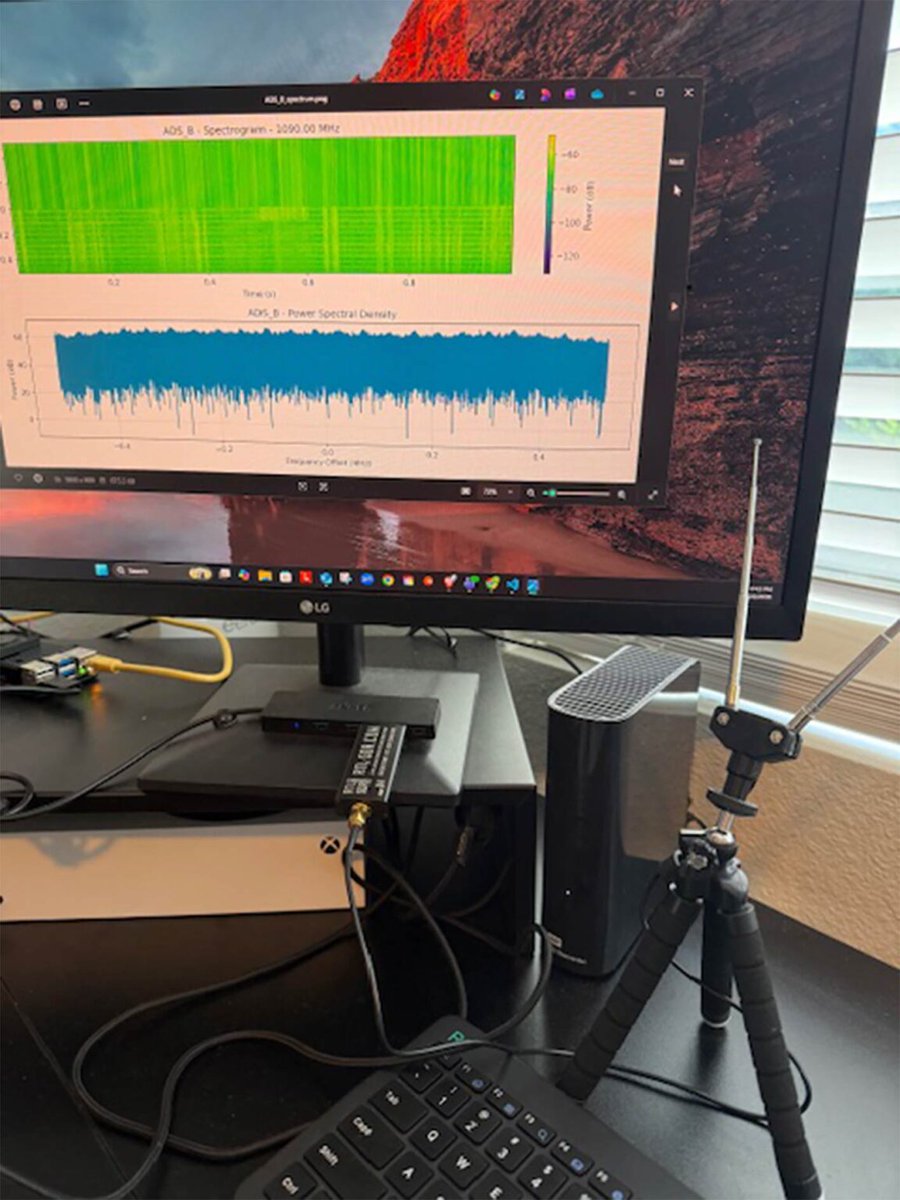
Into infosec (all of it), amateur radio, microcontrollers and other hardware. If it makes a radio wave it's cool. Aspire to eradicate duhkha.





⚠️ WARNING - An unpatched critical telnetd bug (CVE-2026-32746) lets attackers gain full system access with no credentials. One connection to port 23 is enough to trigger memory corruption and execute code as root. No patch yet. Prior telnet flaw is already exploited in the wild. 🔗Read → thehackernews.com/2026/03/critic…





🚨 In conducting 0 day research against #Grandstream GXP1600 VoIP phones, Rapid7 Labs discovered CVE-2026-2329. The unauthenticated stack-based buffer overflow vuln ultimately allows an attacker to intercept phone calls and eavesdrop on audio. Read on: r-7.co/4tIzope


High tide in Duck, NC on the Outer Banks. Live w/ @JimCantore on @weatherchannel for Winter Storm Gianna

What really happened with cyberattacks on Poland's power grids. No FUD. "The attacks targeted numerous wind and solar farms, a private company in the manufacturing sector, and a combined heat and power (CHP) plant supplying heat to nearly half a mil‑ lion customers in Poland. All of the attacks were purely destructive in nature" cert.pl/uploads/docs/C…


G-Code Syntax Highlighter for @VisualStudio v0.1.7.0 If you want to hand-craft #GCode in Visual Studio, I've updated my extension to work with VS2022 and VS2026! Click: Extensions - Manage Extensions - Browse Useful for #CNC #cncprogramming #3DPrinting #makers