Sabitlenmiş Tweet

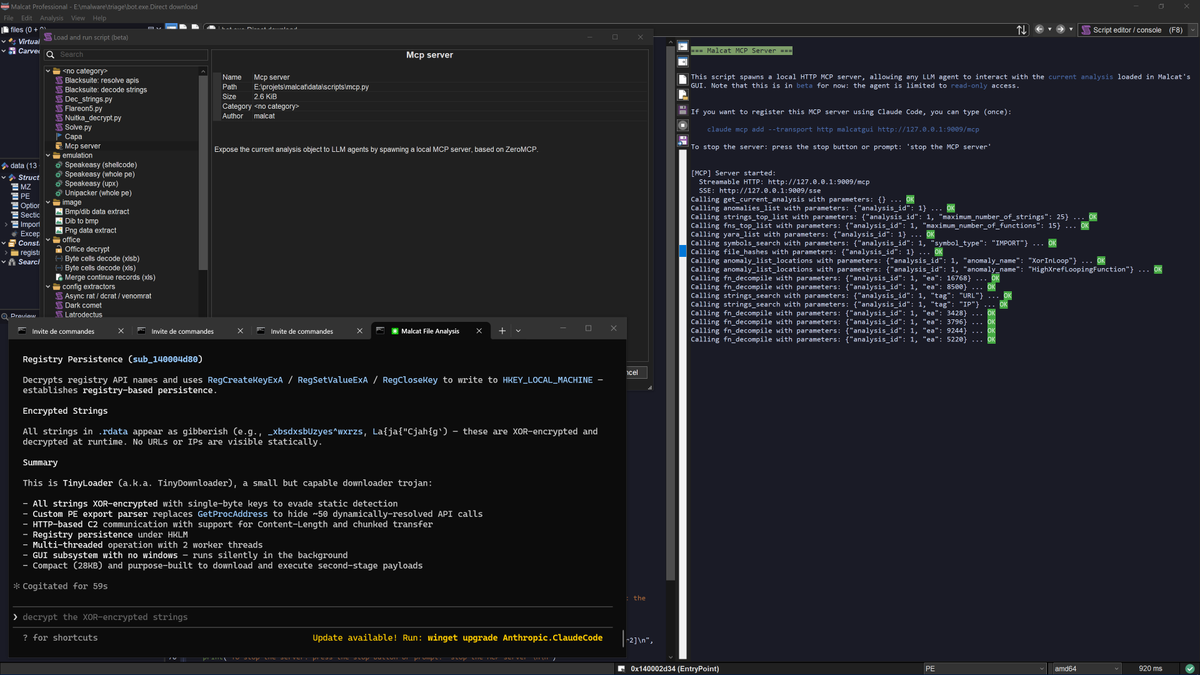
Learn how to reverse engineer malware: training.invokere.com/course/imbt
YouTube: @InvokeReversing" target="_blank" rel="nofollow noopener">youtube.com/@InvokeReversi…
Twitch: twitch.tv/invokereversing
Mastodon: @invokereversing" target="_blank" rel="nofollow noopener">infosec.exchange/@invokereversi…
GitHub: github.com/invoke-re
English