Ivan
119 posts


Ivan
@Ivanklydz
Security researcher with deep focus on vulnerability detection.



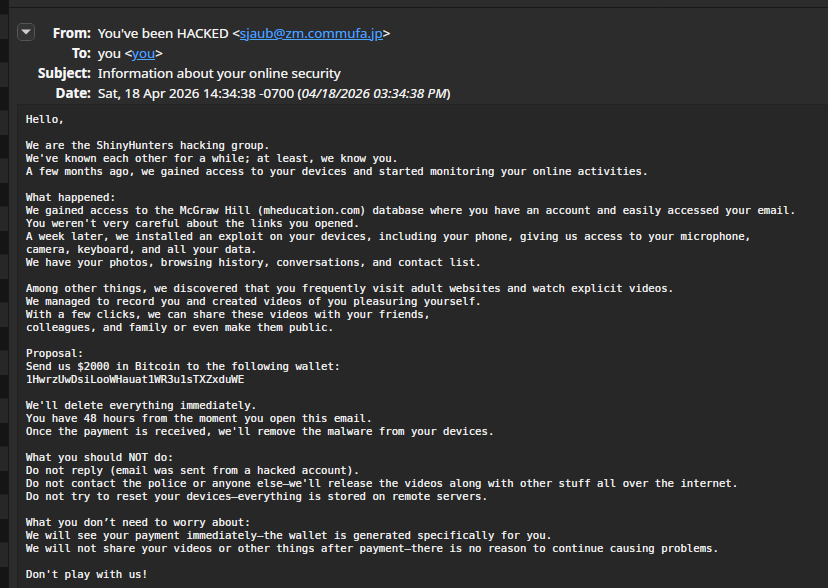
🚨 BREAKING 🚨 Infamous Russian hacker and beatboxer exposes exactly how hackers got access to private GitHub repositories


back in 2022 i found a bug that would let me, with no user interaction, turn any chromium-based browser into a permanent js botnet member in edge, you wouldn't even notice anything out-of-place, and would stay connected to the c2 even after closing the browser

Hey man, you know this is my work. We had an agreement and you blew it. "Our investigation" My investigation, you had a dead lead and I turned it into gold at 2am last night. We we're going to handle this properly but you posted without even consulting me.







Censys has so many more results than Shodan