Iran’s internet is at 4% of normal levels. ⚠️ Cyber ops don’t stop in a blackout. Learn how investigators expose networks linked to the Islamic Revolutionary Guard Corps using OSINT. Register for our live webinar 👇 osint.industries/webinar/unmask…
Jeremy Wiedner
231 posts


@JeremyWiedner
Curiosity, creativity, and action are key!


Iran’s internet is at 4% of normal levels. ⚠️ Cyber ops don’t stop in a blackout. Learn how investigators expose networks linked to the Islamic Revolutionary Guard Corps using OSINT. Register for our live webinar 👇 osint.industries/webinar/unmask…












I've been in crypto for over 10 years and I’ve Never been hacked. Perfect OpSec record. Yesterday, my wallet was drained by a malicious @cursor_ai extension for the first time. If it can happen to me, it can happen to you. Here’s a full breakdown. 🧵👇







Thanks to tremendous dev work by Fukusuke Takahashi and DustInDark, we have our first alpha version release of Suzaku - "Hayabusa for cloud logs". Still lots to implement but the basic sigma detection is working for AWS CloudTrail logs so try it out and give us feedback on how we can improve it for those of you who do DFIR in the cloud. Enjoy! github.com/Yamato-Securit… 高橋福助さんとDustInDarkさんによる素晴らしい開発のおかげで、Suzaku(Hayabusaをクラウドログ用にしたもの)の最初のアルファ版をリリースすることができました! まだ実装したい機能はたくさんありますが、AWS CloudTrailログに対する基本的なSigma検出は動作しています! クラウドでDFIRを行っている皆さん、ぜひ使ってみて、改善点やご意見をフィードバックしてください。 エンジョイ〜


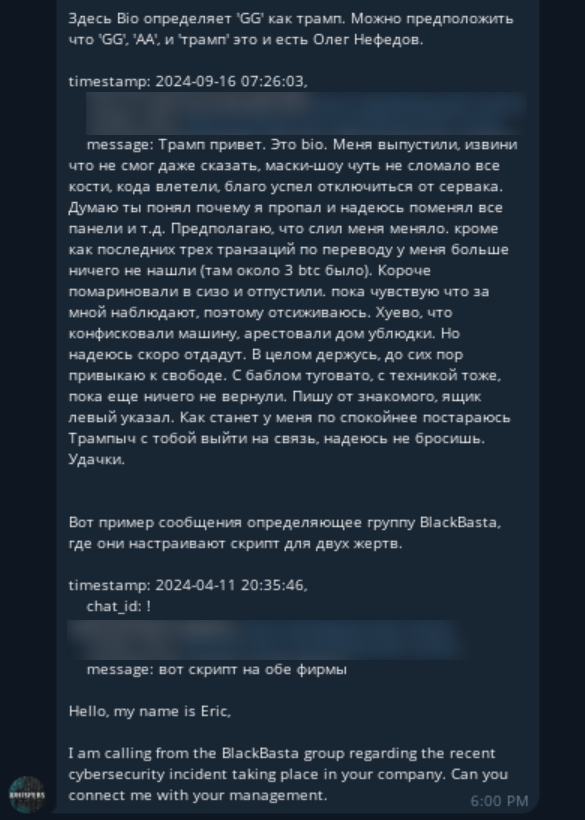
BlackBasta’s internal chats just got exposed, proving once again that cybercriminals are their own worst enemies. Keep burning our intelligence sources, we don’t mind. 😉