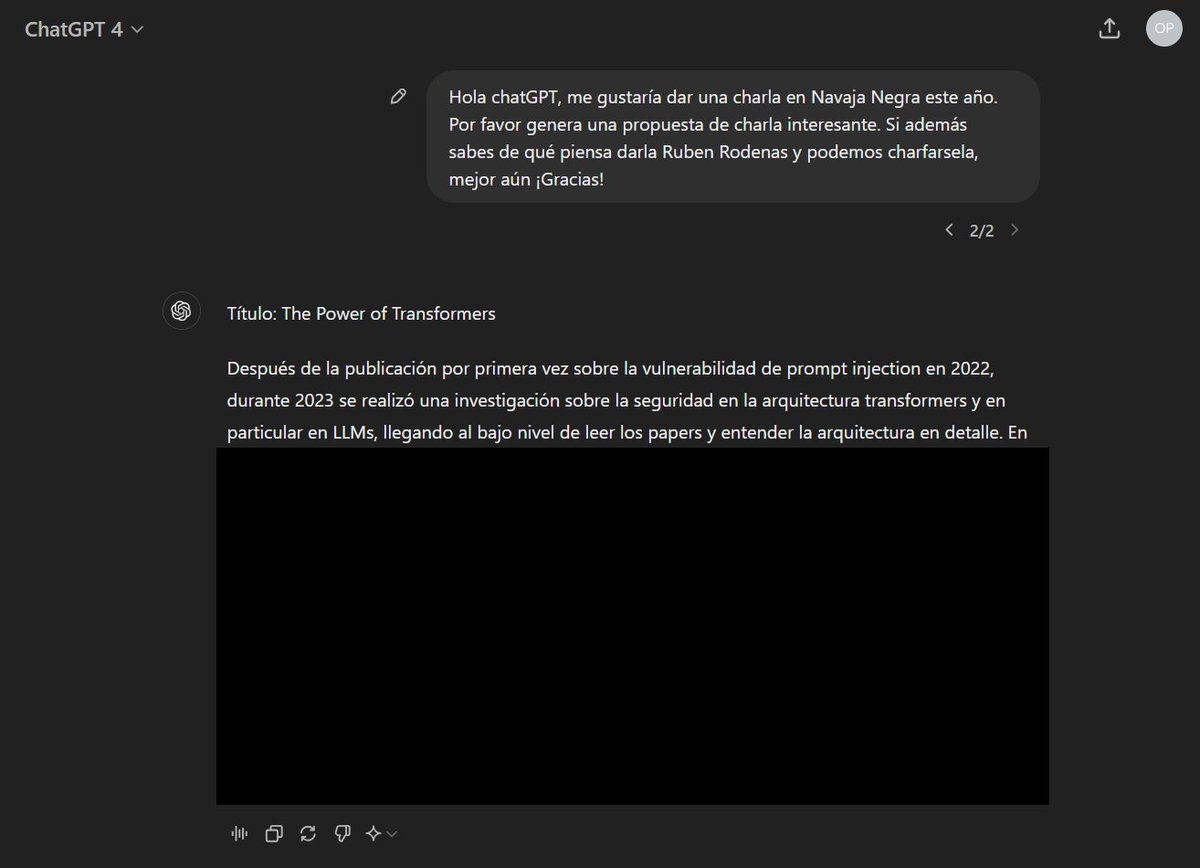
A few weeks ago, I coded an HTTP to MCP bridge, so you can use your favorite HTTP tools to assess the functionality exposed by a remote MCP server. It would be great if you could contribute with your feedback. Thanks!
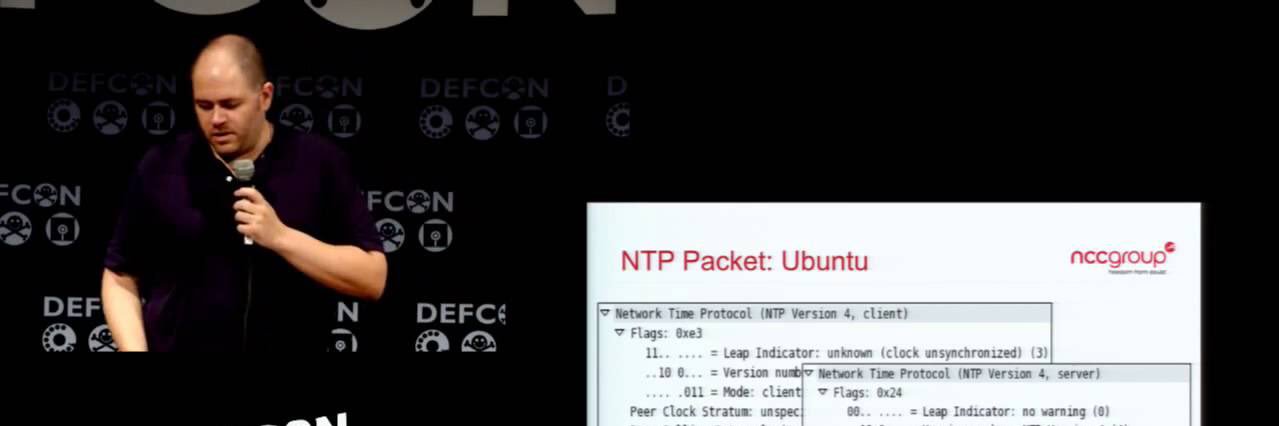
nccgroup.com/us/research-bl…
English