xiaopao retweetledi

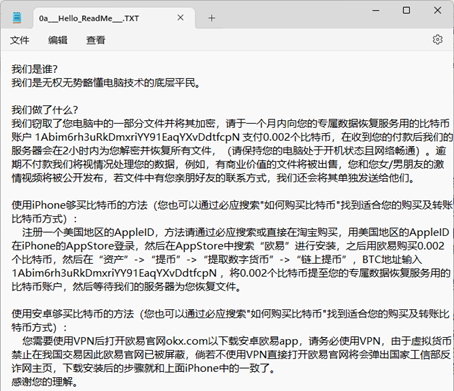
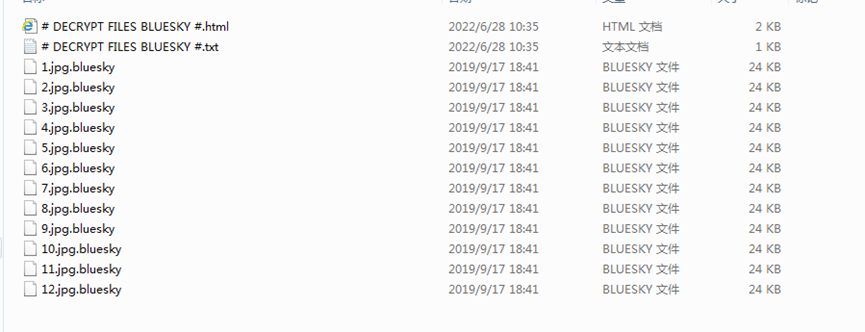
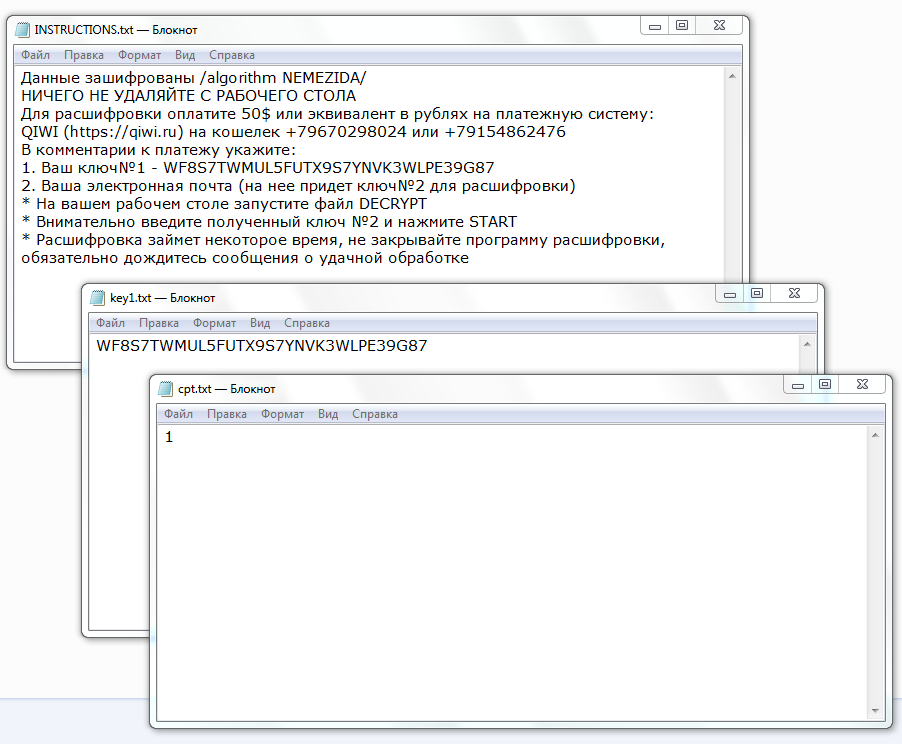
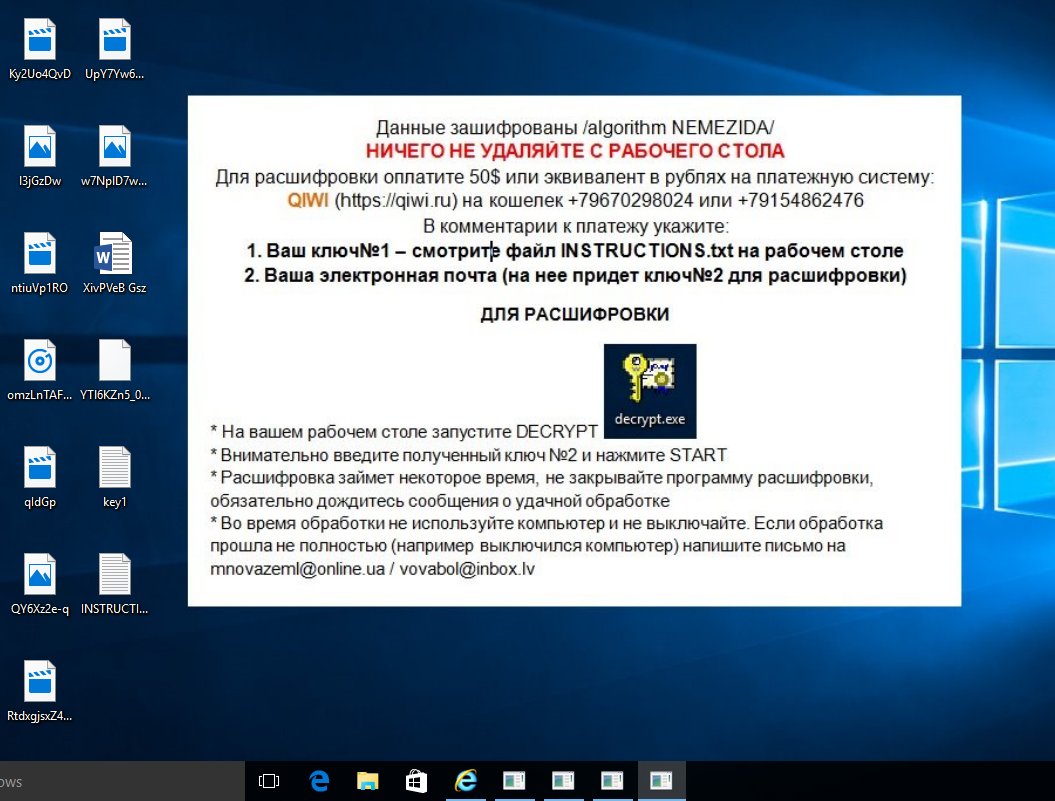
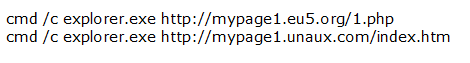
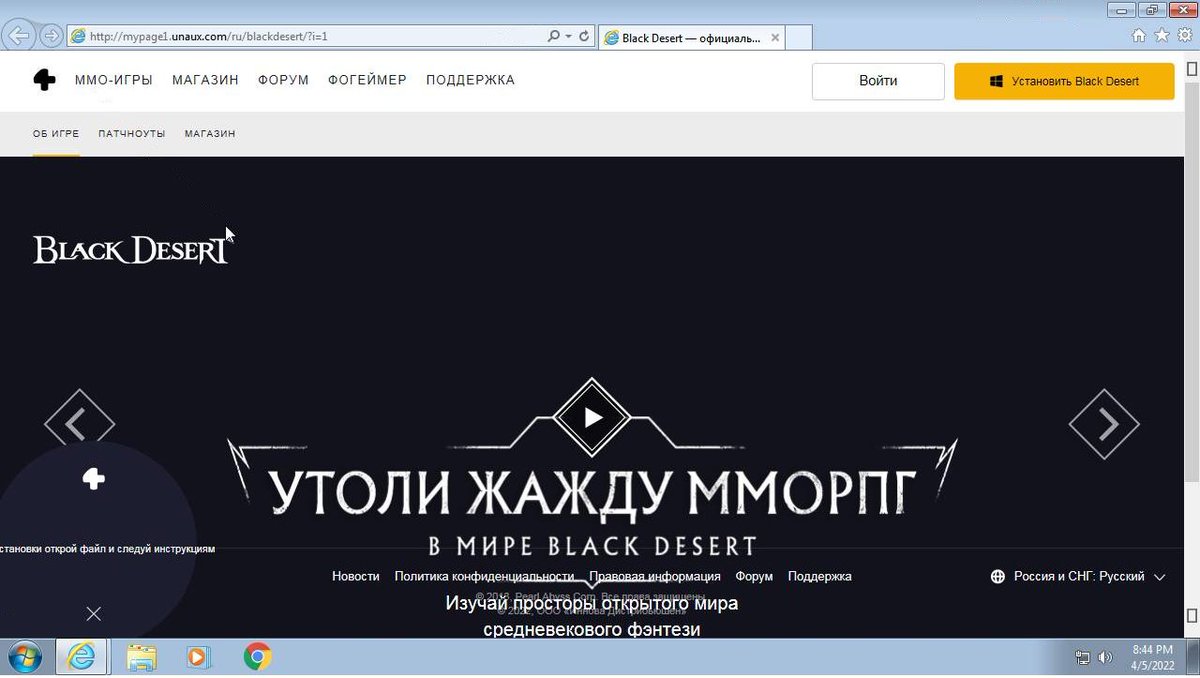
@stealthmole_int Behind the #DragonRaaS (and the "Stormous" copy-cat's) are two Yemeni Individuals. They "redesigned" the old Logo and also came up with a "#StormCry" Ransomware back in March


English
xiaopao
703 posts

@Kangxiaopao
Focus on ransomware,like cat