Lucian Cojocar retweetledi

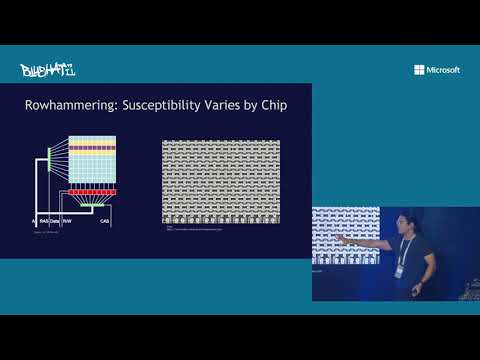
5/10 Are We Susceptible to Rowhammer? An End-to-End Methodology for Cloud Providers people.inf.ethz.ch/omutlu/pub/row… Rowhammer again! You can actually do much better and hammer DRAMs at an optimal rate. @LCojocar et al. @_onurmutlu_ @IEEESSP
English