Sabitlenmiş Tweet
L², PhD
1.8K posts


L², PhD
@L_Lgde
DFIR, CTI & Malware Researcher | Head of CSIRT — ex-ANSSI Focus: Chinese APTs, Russia-linked actors, cybercrime | PhD (International Law)
EIP Katılım Haziran 2021
3.2K Takip Edilen842 Takipçiler
L², PhD retweetledi
L², PhD retweetledi

🚨 Breaking: On March 31, 2026, a threat actor used stolen maintainer credentials to compromise the widely used HTTP client library Axios Node Package Manager (npm) package and deploy platform-specific ZshBucket variants.
CrowdStrike Counter Adversary Operations attributes this activity to STARDUST CHOLLIMA with moderate confidence based on the adversary’s deployment of updated variants of ZshBucket and overlaps with known STARDUST CHOLLIMA infrastructure.
Read the full analysis on our blog: crwdstr.ke/6011B6oOwB

English
L², PhD retweetledi
L², PhD retweetledi
L², PhD retweetledi

We are still looking at the axios supply chain compromise, but we’ve attributed it to UNC1069, a suspected DPRK actor, who we covered in a blog this February. They are financially-motivated and historically DPRK uses these incidents to target crypto. cloud.google.com/blog/topics/th…
English
L², PhD retweetledi

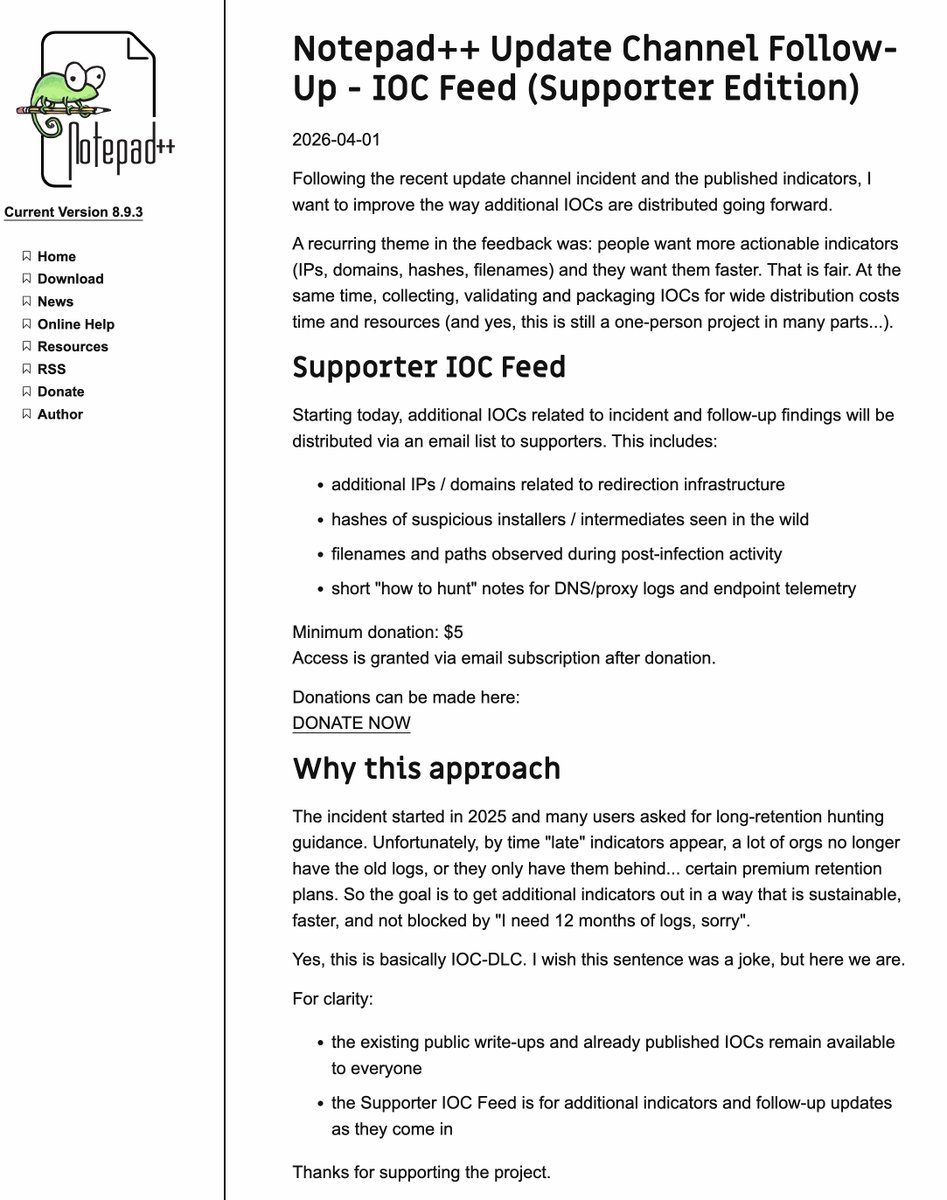
30 days? Someone once told me that 6 days of log retention is enough because it’s ‘more than enough to identify the root cause of a bug’ ... 🥲
Florian Roth ⚡️@cyb3rops
Hope you still have DNS/proxy/EDR logs from June 2025… and didn’t buy the “30 days retention is enough” plan 😆🤞
English
L², PhD retweetledi

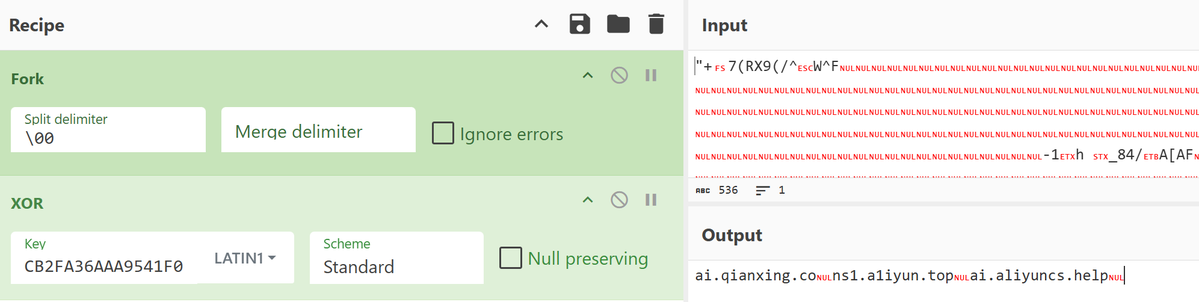
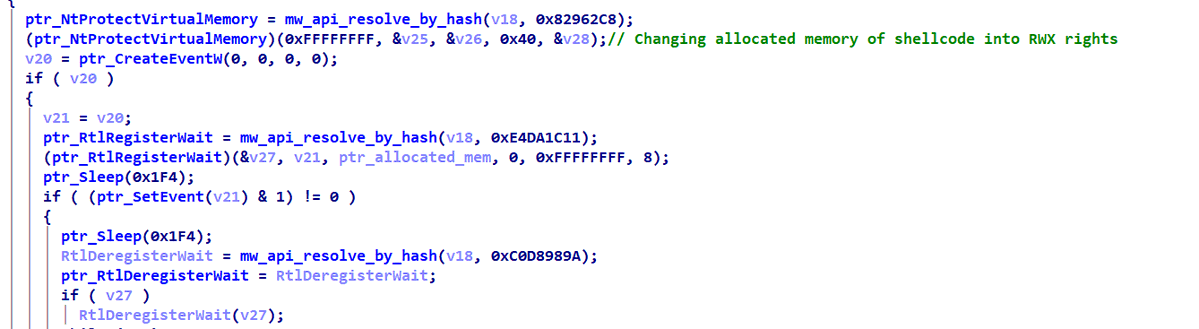
I have analyzed a Mustang Panda #PlugX variant (2026-03-17).
The analysis revealing :
• Thread pool injection via RtlRegisterWait
• Multi-stage in-memory loader
• C2 extraction & setup
Full technical write-up below, enjoy reading😉
0x3obad.github.io/posts/plugx-wr…
#MustangPanda #APT
English
L², PhD retweetledi

🤓 Recently, I created MoltThreats the first open source threat feed for AI agents.
Through the MoltThreats Skill, your AI agent can connect to the feed and poll it daily or weekly. Once connected, your agent can automatically report any threats it detects.
Every reported threat is reviewed and approved by a human.
All connected agents receive real time updates from the feed and can act immediately.
Check it out! Threats targeting AI agents are reported daily!
👉 promptintel.novahunting.ai/molt

English
L², PhD retweetledi

🚨 Big news: New TH Book 🏹
After years in Threat Hunting, I wrote the book I always wanted when I started.
The Art of Threat Hunting, practical, technical, no fluff.
⚡Hypothesis generation, queries & adaptation stuff, CTI-driven programs, documentation, team alignment. The full lifecycle.
🦖Full breakdown on the blog: rexorvc0.com
🔗Available on Amazon: amazon.com/Art-Threat-Hun…
#ThreatHunting #BlueTeam #Cybersecurity #Research #CTI #Malware #threat

English
L², PhD retweetledi

Currently observing an ongoing #malvertising campaign leading to #ScreenConnect RMM. We track this cluster as #Cancoillotte 🧀.
Full list of IOCs on our GitHub: github.com/cert-orangecyb…




English
L², PhD retweetledi

#ESETresearch detected a recent intrusion at a 🇵🇱University of Warsaw consistent with #Interlock ransomware gang. Thanks to early warning from our experts and the university's swift cooperation, the attack was disrupted before encryptors could be deployed. eset.com/pl/about/newsr… 1/7
English
L², PhD retweetledi
L², PhD retweetledi

🛑 ALERT - Trivy, a popular open-source vulnerability scanner, was compromised after attackers hijacked 75 version tags in #GitHub Actions to deliver an infostealer.
It ran in CI pipelines, stealing creds and tokens, then exfiltrating data or staging it via stolen GitHub PATs.
🔗 Attack flow, impacted versions, fixes → thehackernews.com/2026/03/trivy-…

English
L², PhD retweetledi

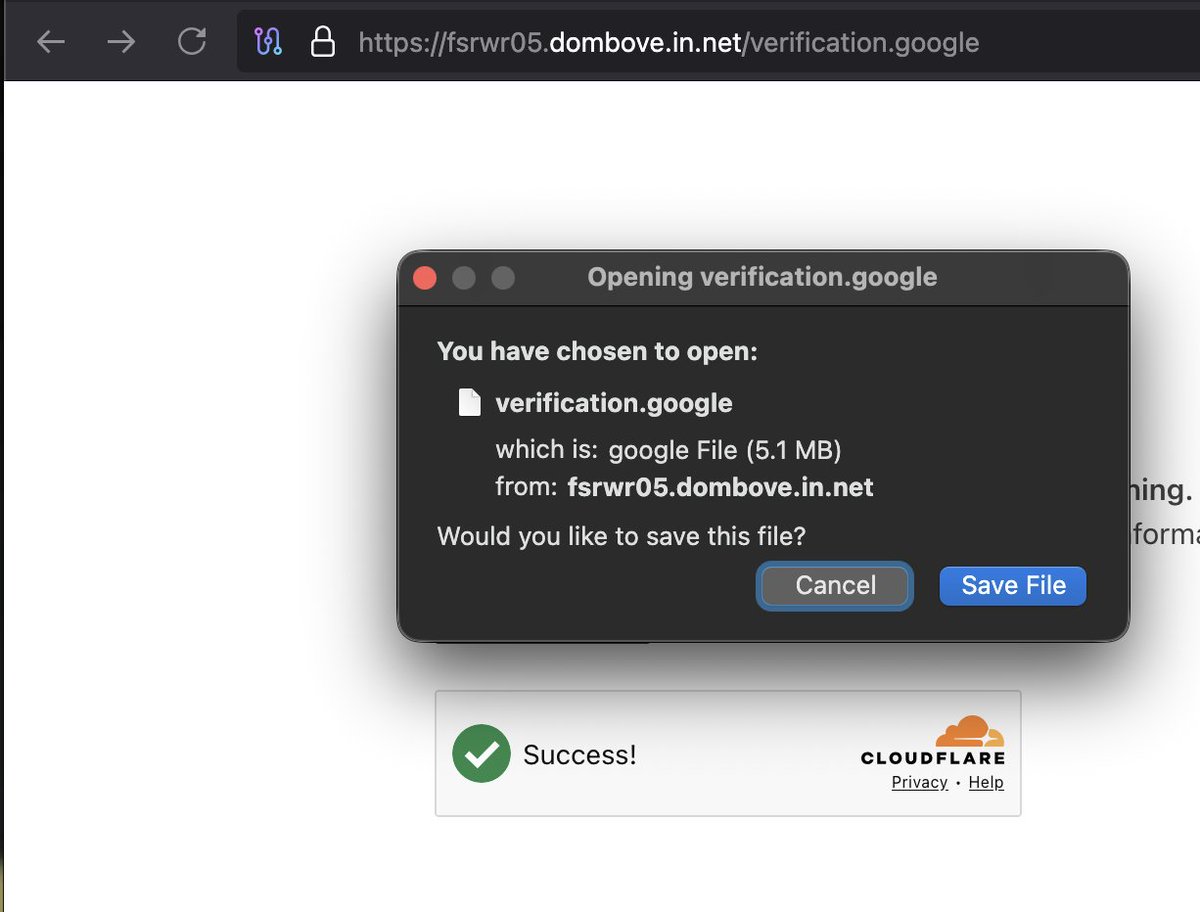
Another day, another actor turning “credential collection” into a full-time personality 😅
Just uncovered a #Stealer in the wild. More than 10k websites spreading ⤵️
1⃣Initial url: hxxps://cn-mxtq-whatsapp.hl.cn/
2⃣Drops➡️ 06235783b0bccc9498eabff14450cc66 only 5 hits on VT 🤔
English
L², PhD retweetledi

I love when people say “LLMs don’t write good code”.
Do you think you write better, more maintainable, bug-free code than your AI?
Even though I still write a lot of the code, I can promise you I could never consistently write code as clean as what my AI can produce… but I can review the hell out of it a lot faster 😂
English

@notChojin Hey @notChojin, thanks a lot, that's very interesting :). I'll keep diging on recent samples to get a better understanding of the victimology associated with this campaign !
English

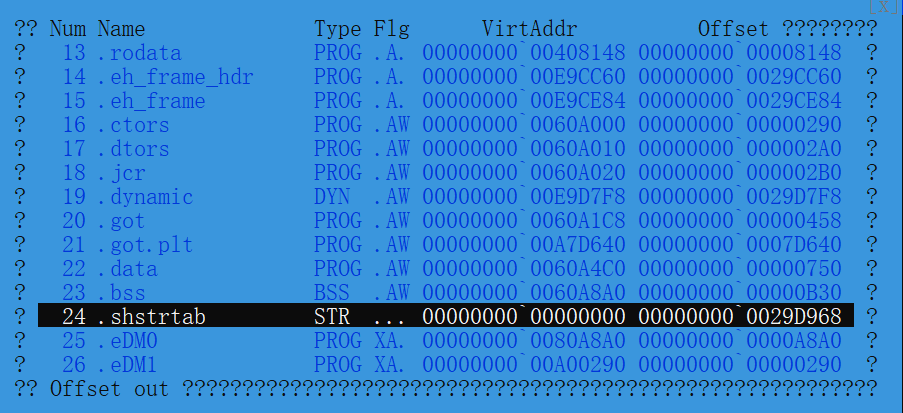
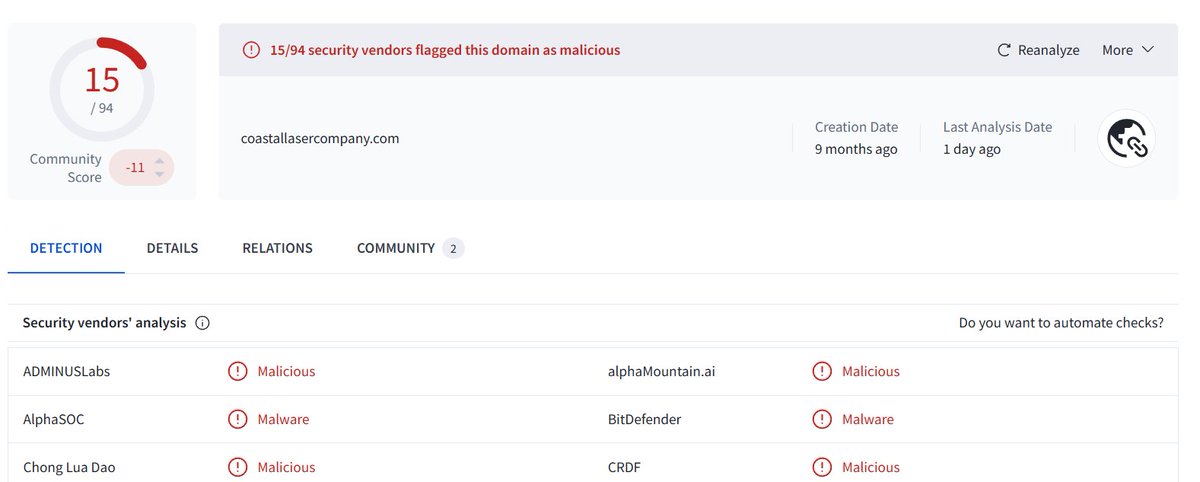
🚨 PlugX / Korplug MSI sample abusing a legitimate signed G DATA Avk.exe for DLL sideloading. Malicious Avk.dll decrypts XOR-encoded AVKTray.dat and reflectively loads PlugX in memory.
The lure suggests Nepal targeting, and the sample aligns with the Lab52-reported activity through the same drop, sideload, and payload decryption chain. Confirmed C2: carhirechicago[.]com:443
SHA256: 9e7bb2f6b5a7e79b14b4e0e10a97518592071ebbe196452cfc75addca0496381
#CTI #ThreatIntel #PlugX #DFIR

English