Larry B. Daniel
3.6K posts


Larry B. Daniel
@LarryofDeKalb
Still alive. My photo is on GitHub.
Atlanta, GA Katılım Temmuz 2024
616 Takip Edilen1.7K Takipçiler

Old notes for Algebrica.
This is also why, after two and a half years, Algebrica still has relatively few entries.
Most of the work starts on paper. I collect ideas, connect them, work through the details, and compare different sources. Only at the end do I write the pages.
I know it’s a slow process and it really limits how much I can publish.... Someone pointed out, fairly, that it’s not efficient (I agree...), but I’m not trying to be efficient, I’m trying to be as accurate as possible.
I’d rather take more time and give each entry more depth, bringing together different perspectives into something coherent. It can be a bit tiring, I won’t hide that, but it’s also deeply satisfying to see it grow, slowly.

English

#neglect Buckhead and Decatur seem to be slag. I live between them.
English

@MIT_CSAIL @IEEESpectrum Smart paper, it was inspiring.
English

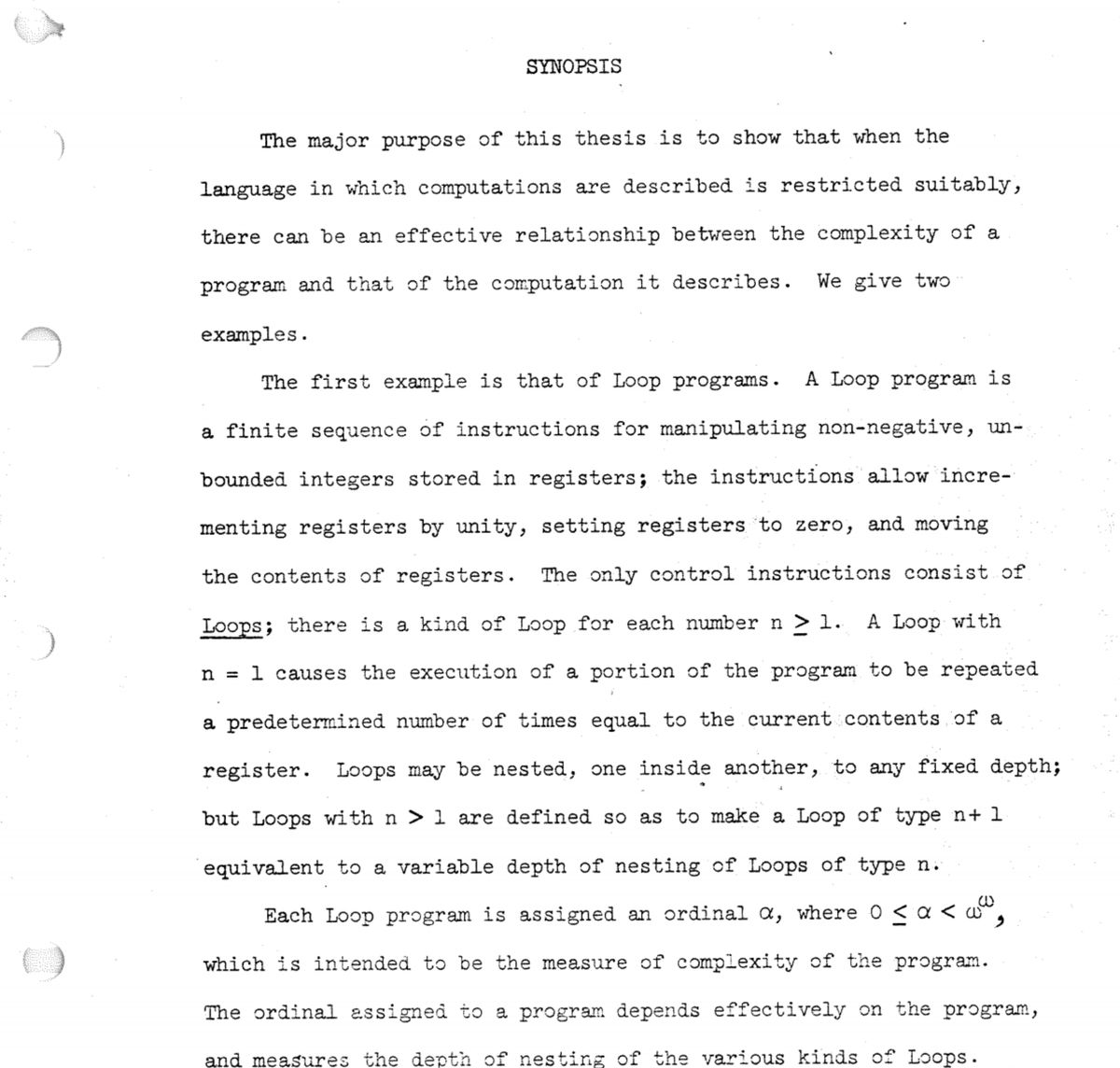
Read the lost thesis of Dennis Ritchie, creator of the C programming language & co-creator of Unix: bit.ly/RitchiePhD
Ritchie never got his PhD b/c he didn't want to pay Harvard the thesis binding fee.
(v/@IEEESpectrum)
English

For those who know I’ve battled rectal cancer for over 5 yrs now, my body has decided it doesn’t want to corrupt with me. It’s being pretty combative. It’s sore, painful, really painful. To much to my surprise, my cancer has spread to my brain. I’ll go this week for radiation treatments. I’m horribly scared to say the least. If you could, send some good vibes my way, please and thank you!!

English

@SeleneSmokes Thanks, your smoking picture was top of the list at top of hour and got me out to smoke then. X is real.
English

@ThinkerAnya_ Keep smoking, you can resupply calcium later.
English

Happy birthday to my daughter! 🎉💕
Some heartless people won’t congratulate her just because she is different. 💔😢
#birthday #love #staystrong #fblifestyle

English

@kyuketusamurai Bite somebody that deserves it; like a liar.
English

#neglect a case in point; the Japanese 5th generation project succeeded, the Ai was marvelous. Somebody told it to own the building on the north island that they coveted. The north island has 2 salt cities. This is recent.
English

SOMEONE OPEN-SOURCE A CHROMIUM BROWSER THAT RUNS ENTIRELY IN YOUR TERMINAL.
It's called Carbonyl. It renders actual web pages in your command line. The best part is it runs with 0% CPU usage when idle.
→ Full Chromium engine in the terminal.
→ Dles at exactly 0% CPU.
→ Fast, lightweight, and completely terminal-native.
100% Open Source.
English

@esrtweet Nash said it like: There are no secret tactics.
English

There's an old, bad idea that's been trying to resurrect itself on X in the last couple of days. Which makes it time for me to explain exactly why, in the age of LLMs, open-sourcing your code is an even more important security measure than it was before we had robot friends.
The underlying principle was discovered in the 1880s by an expert on military cryptography, a man named August Kerckhoffs, writing long before computers were a thing.
To start with, you need to focus in on the fact that cryptosystems have two parts. They have methods, and they have keys. You feed a key and a message to a method and get encrypted information that, you hope, only someone else with the same pair of method and key can read.
What Kerckhoffs noticed was this: military cryptosystems in normal operation leak information about their methods. Code books and code machines get captured, stolen, betrayed, or lost in simple accidents and found by people you don't want to have them. This was the pre-computer equivalent of an unintended source-code disclosure.
Cryptosystems also leak information about their keys - think post-it notes with passwords stuck to a monitor. What Kerckhoffs noticed is that these two different kinds of compromising leakage happen at very different base rates. It is almost impossible to prevent leakage of information about methods, but just barely possible to prevent leakage of information about keys.
Why? Keys have fewer bits. This makes them easier to keep secret.
Remember: this was something an intelligent man could notice in the 1880s, well before even vacuum tubes. Which is your first clue that the power of this observation hasn't changed just because we're in the middle of a freaking Singularity.
Security through obscurity - closed source code - means you're busted if either the source code or the keys get leaked. Open source is a preemptive strike - it's a way to force the property that your security depends *only* on keeping the keys secret.
What you're doing by designing under the assumption of open source is preventing source code leakage from being a danger. And that's the kind of leakage with a high base rate.
As far back as 1947 Claude Shannon applied this to electronic security - he did critical work on the voice scramblers that were used for secure telephone communications between heads of state during World War II. Shannon said one should always design as though "the enemy knows the system". The US's National Security Agency still uses this as a guiding principle in computer-based cryptosystems.
If you're doing software security, always design as though the enemy can see your source code. I'm still a little puzzled that I was apparently the first person to notice that this was a general argument for open source; as soon as I did, my first thought was more or less "Duh? Somebody should have noticed this sooner?"
Now let's consider how LLMs change this picture. Or...don't.
An LLM is like a cryptanalyst with a superhuman attention span that never sleeps. If your system leaks information that can compromise it, that compromise is going to happen a hell of a lot faster than if your adversary has to rely on Mark 1 meatbrains.
But it gets worse. With LLMs, decompilation is now fast and cheap. You have to assume that if an adversary can see your executable binary, they can recover the source code. If you were relying on that to be secret, you are *screwed*.
Leakage control - limiting the set of bits that can yield a compromise - is more important than ever. So security by code obscurity is an even more brittle and dangerous strategy than it used to be.
Anybody who tries to tell you differently is either deeply stupid or trying to sell you something that you should not by any means buy.
English

利用できるリソースが限られていて、少しでもお行儀が悪いアプリがあればシステム全体が停止する頃。C/C++/asmしか生きられない時代。
It's me, Caroli!@isThisCaroli
@kazzkiq Nem é da minha época, mas dá uma saudade de quando as coisas simplesmente funcionavam… Sem a necessidade de bloatware e consumo desenfreado de recursos em tudo.
日本語