Lemon
314 posts

Lemon
@Lemonitup
Principal Security Engineer @ Red Threat https://t.co/qGxQnY0KNq
Oklahoma, USA Katılım Kasım 2014
277 Takip Edilen877 Takipçiler

@offsectraining The “AI”
while true; do
read -p "Enter something: " user_input
echo "Try Harder"
done
English

Introducing... OSAI 🐺🚨
From the makers of OSCP, the OSAI brings OffSec’s offensive methodology to AI with advanced red teaming for AI environments. This certification turns AI security knowledge into legitimate capability that holds up in the real world.
🔺 Expand into one of the fastest-growing security domains
🔺 Prove hands-on capability with a practical certification
🔺 Build repeatable methodology you can use across engagements
Be the first to see what #OSAI covers, who it’s for, how the certification works, and be entered in a giveaway for free access: offsec.com/courses/osai/
English

@vxunderground 7. Just unload the filter drivers with fltmc unload. (Need admin) Bypassestamper and password protection, av still shows enabled and malware executes.
English

I've decided to poke MalwareBytes with a stick.
Why? I'm mildly curious how it works internally and I'm curious if I can produce malware custom tailored to evade it.
Why? Because sometimes I get weird ideas and want to do weird things for literally zero reason other than "sounds kind of cool".
I setup a VM for the first time in years to poke it with a stick. I didn't want to install an AV on my main machine. Yes, I will do malware analysis on my main machine but not install an AV.
After installing MalwareBytes, skimming some of the files, poking random things and saying "wtf does this thing do", I've learned some mildly interesting things but nothing revolutionary.
1. They use Jenkins for continuous integration. Does this mean anything? No.
2. Based off my minimal testing, I don't see any DLLs injected into binaries when they're loaded into memory. However, the binaries I tested are well known and well established. It might inject DLLs into unknown binaries.
3. MalwareBytes main binary is written in C#.NET. It loads a secondary MalwareBytes.dll which then displays everything. It does the same stuff Microsoft Copilot does. That is how MalwareBytes has a fancy UI and stuff.
4. MalwareBytes stores very little in HKEY_CURRENT_USER making tampering from user mode kind of hard. It's just basic settings and stuff.
5. MalwareBytes has a custom protocol handler of "malwarebytes://". It looks like it uses this for interprocess communication between other MalwareBytes modules and binaries
6. MalwareBytes ships with a (basically) blank DLL called "Sample.dll". I have no idea why.
7. MalwareBytes has 2 mini filters in place which (presumably) are the main thing responsible for detecting malware. This is standard. MalwareBytes Chameleon (one of the minifilters) looks like it's meant to prevent tampering with the actual important MalwareBytes minifilter.
8. MalwareBytes Chameleon looks like it's responsible for communicating with user mode and kernel mode components. It looks like this is done so user mode components don't communicate directly with the minifilter responsible for actually detecting malware
9. I have a lot more poking to do
10. There is a binary called "assistant.exe" which loads "assistant.dll" (more .NET) stuff. It may possible to abuse this as a LOLBIN (maybe, need to poke more, kind of). assistant.exe does things like issuing commands for scanning, updating, and displaying things in the MalwareBytes UI. It accepts commands as "assistant.exe --uri malwarebytes://"
11. I have no idea how their scanning works, but it's labeled internally as Hyperscan
12. There is a thing called ProtectedHashes. I have no idea what this is.
13. There are tons of SQLite libraries, but I have no idea what it's for. Presumably, it's for known-good and known-bad file hashes, maybe? But I have no idea where this is stored.
14. I like cats
English


@vxunderground Let me Rule was my favorite because you could play ragtime music via the motherboard speaker.

English

@RachelTobac I was worried until I remembered I didn’t play Tennis. Still threw a few decks of cards into my bag for DEFCON!
English

@I_Am_Jakoby @zeifan I can’t believe this is just now taking off in popularity. I got this from a blog years and used it on pentest for years before making a video on it. youtu.be/Q0ihmFC1JSA?si…
YouTube
English

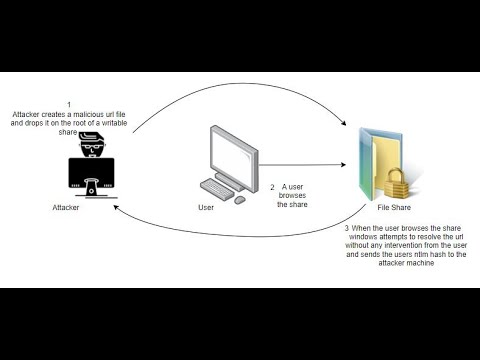
0 click NTLM hash grab!
This is actually one of the craziest exploits I have ever seen
Shoutout to @zeifan for the original POC
He was kind enough to share his version where simply right clicking the lnk file would send over the users password hashes
I did a little modification and you dont even have to click anything anymore
simply navigating to the directory where the malicious lnk file is triggers it and sends your password hashes to me!
This is truly one of the best exploits I have ever witnessed
English

@awakecoding Snaplabs. Build out a default testing environment then snapshot it for easy rebuilds.
English

@plaverty9 @techspence @jsark983 Digital signage hacking. Had a rough few years when they removed cd drives from computers and I didn’t have a kinetic outlet for demonstrating access.
English

What is your favorite fun and non-privesc thing to exploit during a pentest @techspence, @jsark983 and anyone else?
On an internal, I send the client an email from themselves over an open SMTP relay. The email body says it is from me.
English

@deadvolvo I was in the same place when I started seeing top 1% THM on every LinkedIn headline. I found more fulfillment in building POCs like a malicious charging station or hacking hardware I bought of eBay. Those things also stand out on a resume more than CTFs.
English
Lemon retweetledi

❗ Most Impactful System ❗
WINNER: @Lemonitup: bypassing authentication prompts on an Intelight X-1 traffic control system 🚦
RUNNER UP: SeongJoon Cho & Dongheyon Oh, @LabsSsd: exposing security flaws in the D-Link DSR-250 VPN Router 🌐
English
Lemon retweetledi

@seeinglogic @InterruptLabs @vigilant_labs @Bugcrowd @ex0dus_0x @Ninja3047_ @annatea16 @maxpl0it @LabsSsd 1️⃣2️⃣ Intelight X-1 – Grand Central Hack The Planet 🚦🌎
@RedThreat successfully demo’d how to bypass the authentication prompt on an Intelight X-1 traffic control system - leading to full access to make any changes you want on the controller.

English

@techspence We have a default methodology for every assessment type of what to test and even in the event of a no findings test we still have a solid report with work to show. After that, engineers are free to hunt zero days or waste a whole day on a buffer overflow.
English


@HackingLZ With enough head gasket shims this might work but the lower compression negates any advantage gained from the longer stroke.
English

@chrissanders88 Hope they configured global audit policy more than 3 years ago. Hope you have any logging. Check last login date or if ever logged on. Try the password testuser for lulz
English
Investigation Scenario 🔎
You’ve discovered a 3 year old account named “testuser” on your Windows domain. Nobody knows who created it.
What do you look for to investigate whether this account has been used for any malicious activity?
#InvestigationPath #DFIR #SOC
English