Artur Marzano retweetledi

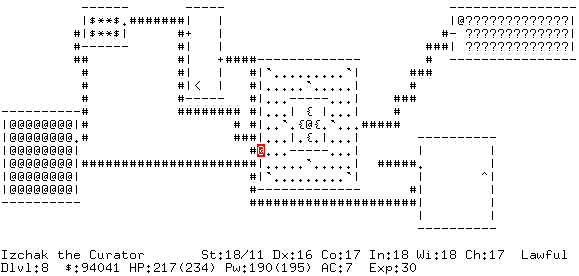
NetHack is one of the most complex and longest-lived open source programs ever written, and after 46 years, v5.0 shipped today.
nethack.org/common/index.h…
And ... it is a VERY cool large codebase to work with in the LLM era.
English