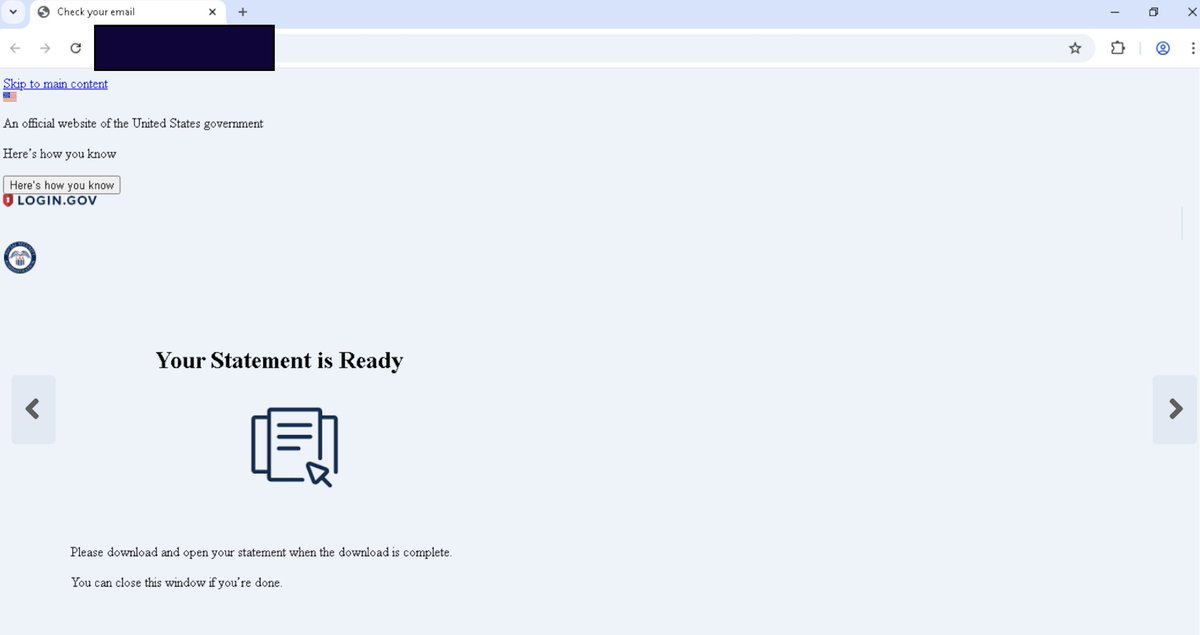
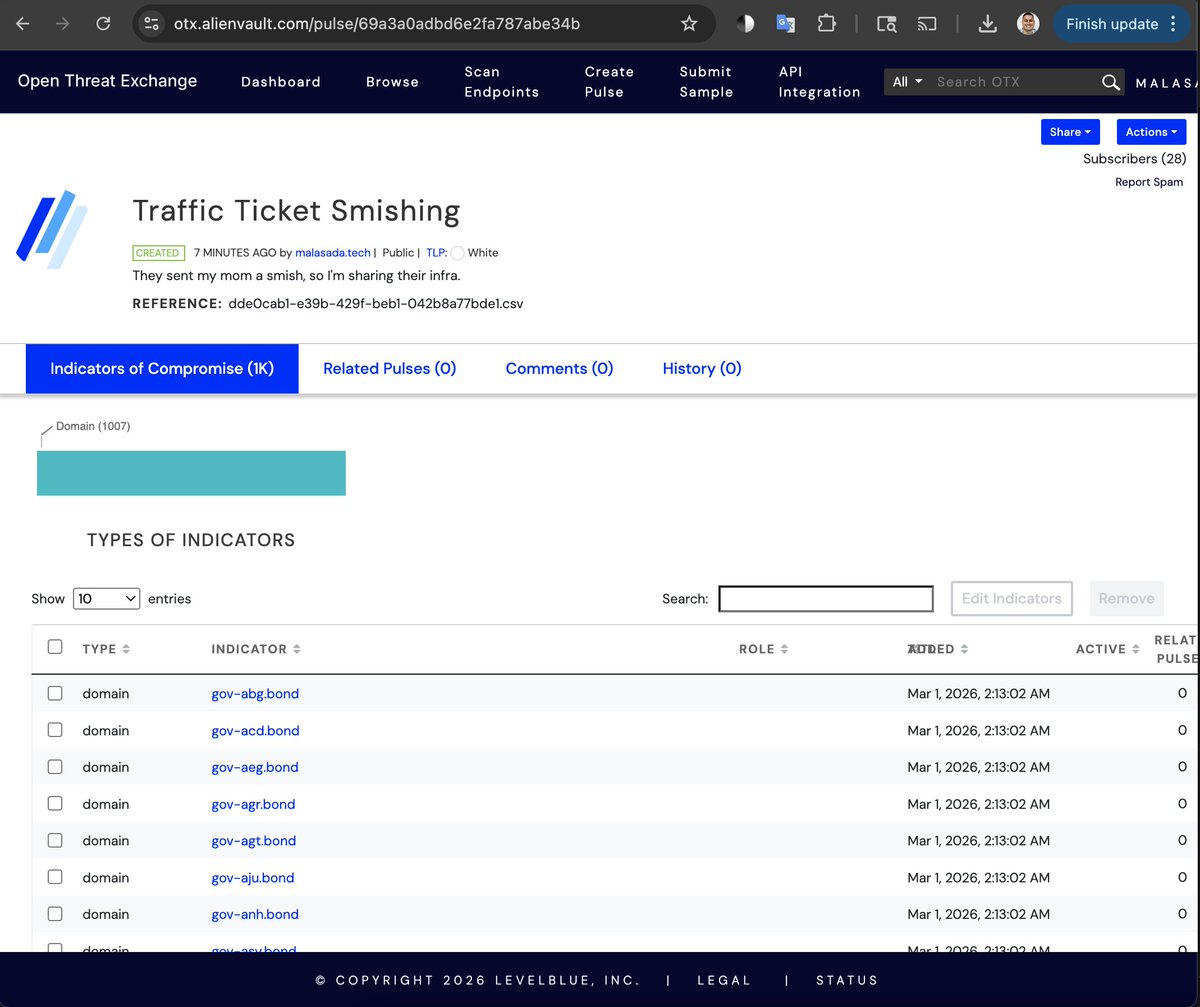
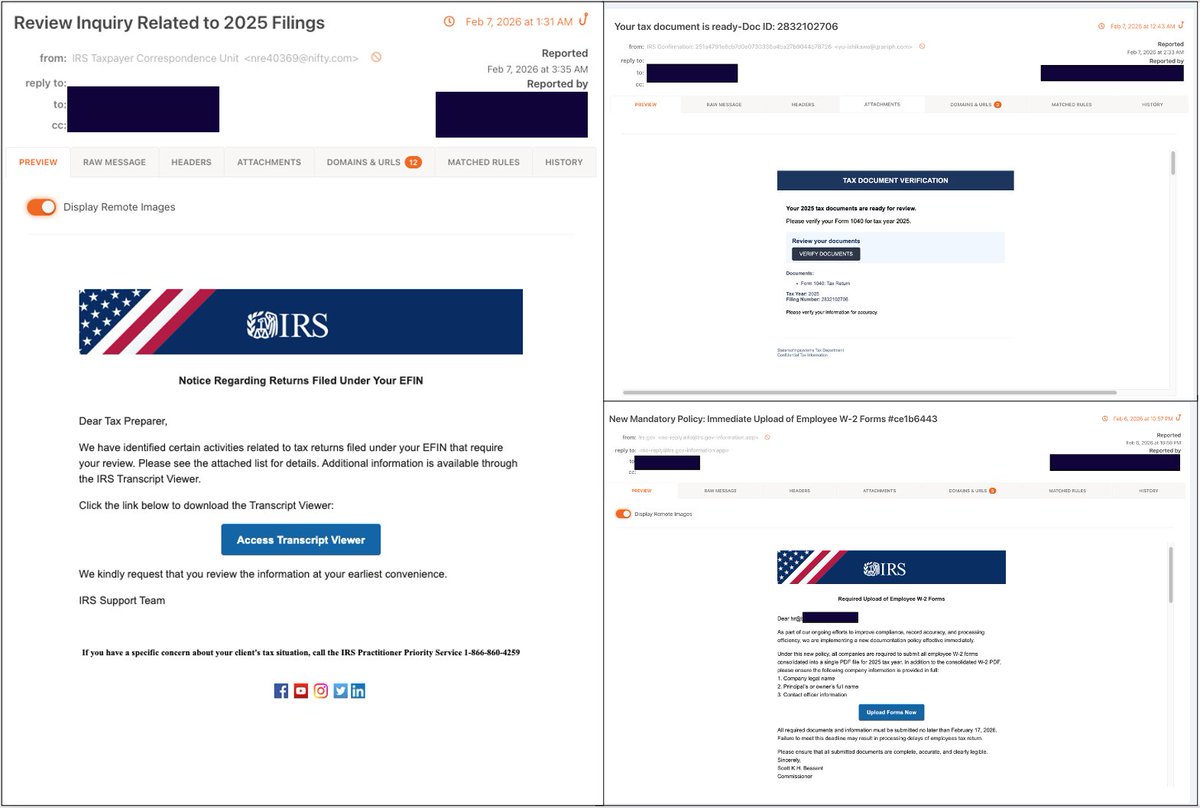
This was the lead. I tried to find the activity Malwarebytes was talking about. I couldn't find that one, but ended up with this one. Here's the link to the Malwarebytes article.
malwarebytes.com/blog/threat-in…
English
MalasadaTech
368 posts

@MalasadaTech
ALOJAHZ WORLD! HOBBYIST THRUNTELLISEARCHER. VIEWS ARE MY OWN! 808 https://t.co/5AFyJj7uay


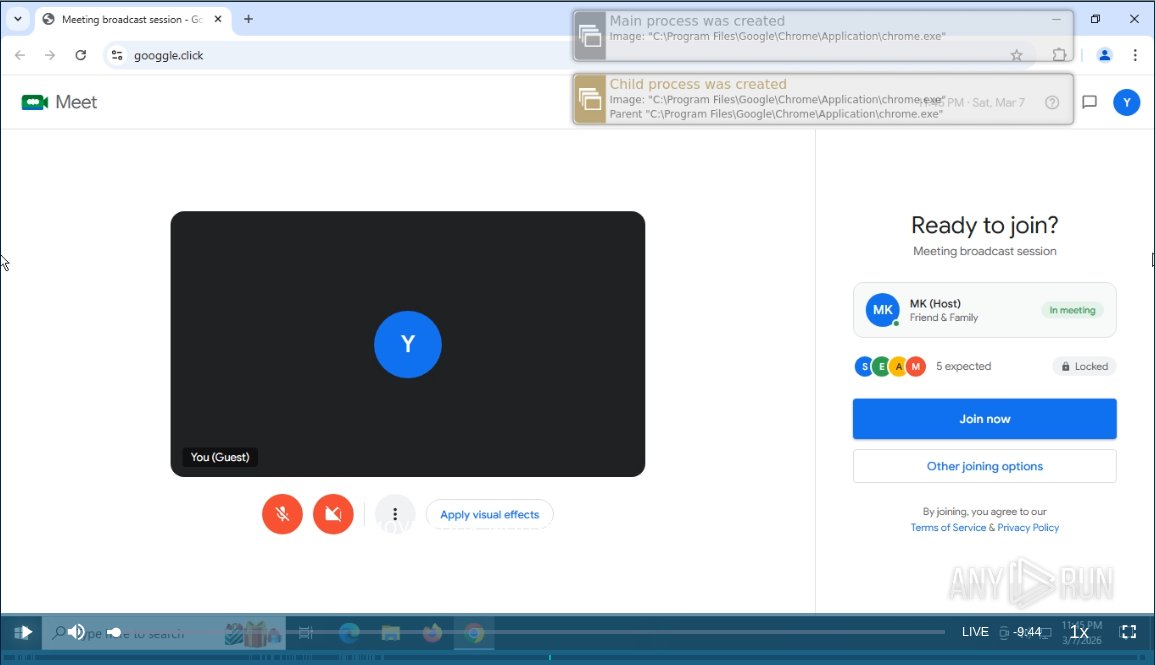
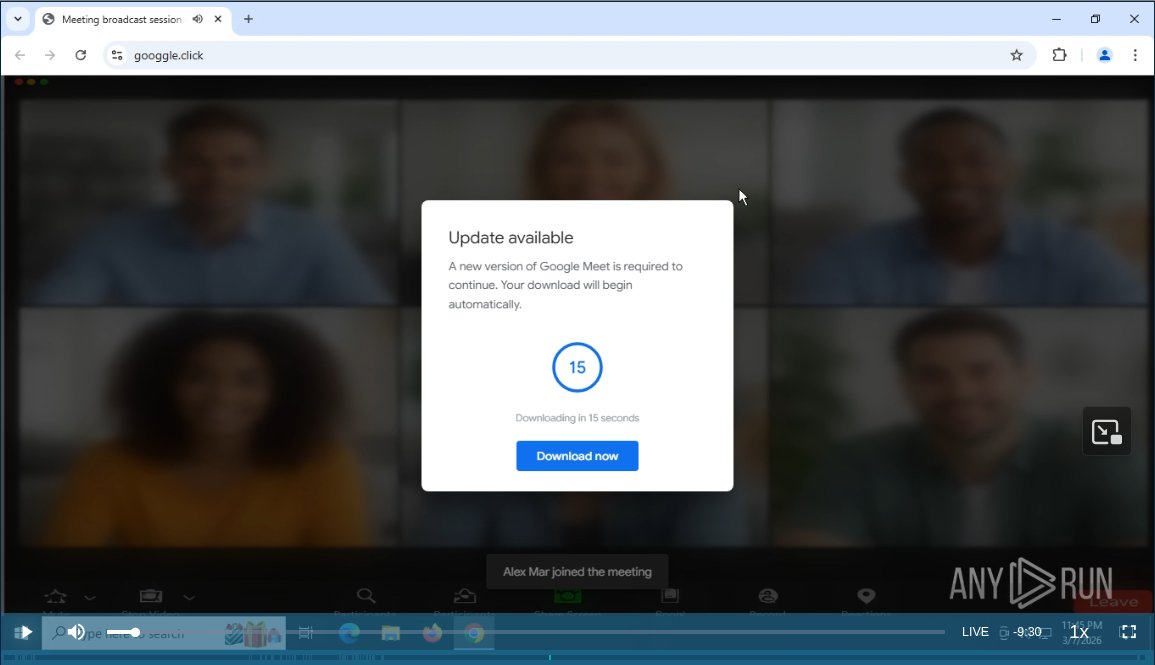
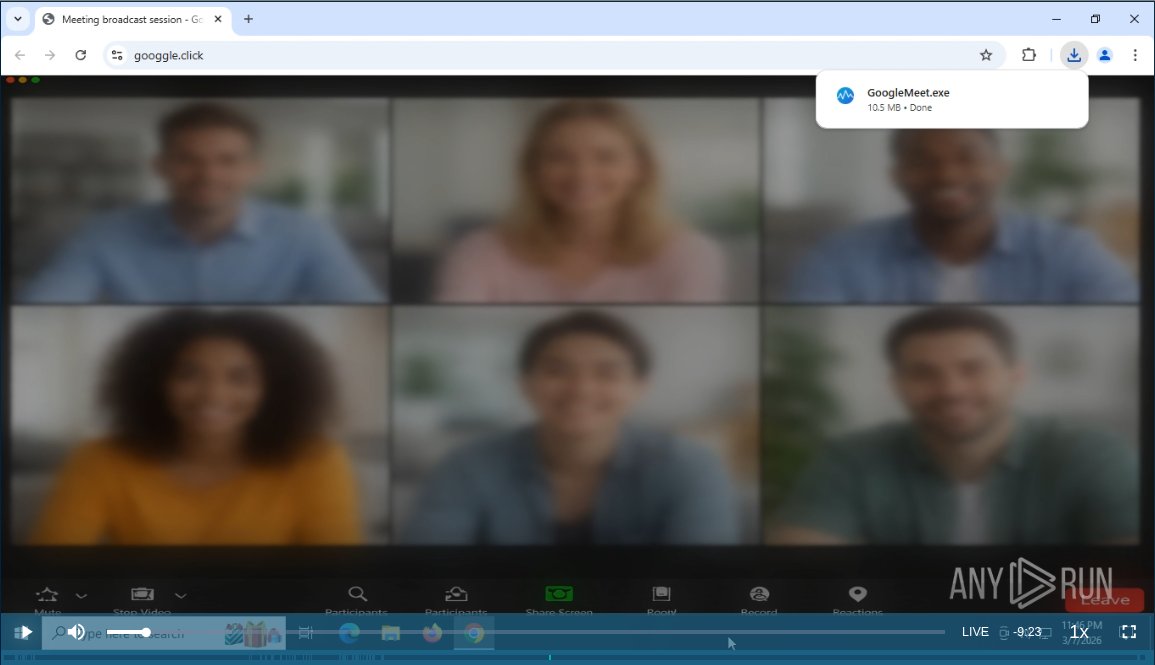
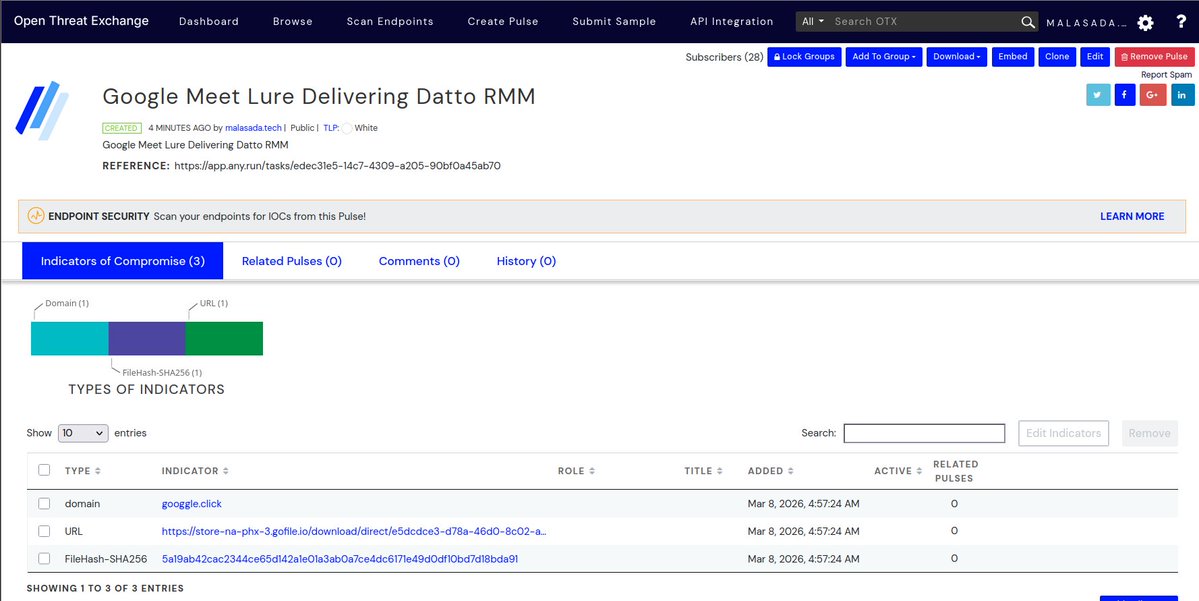



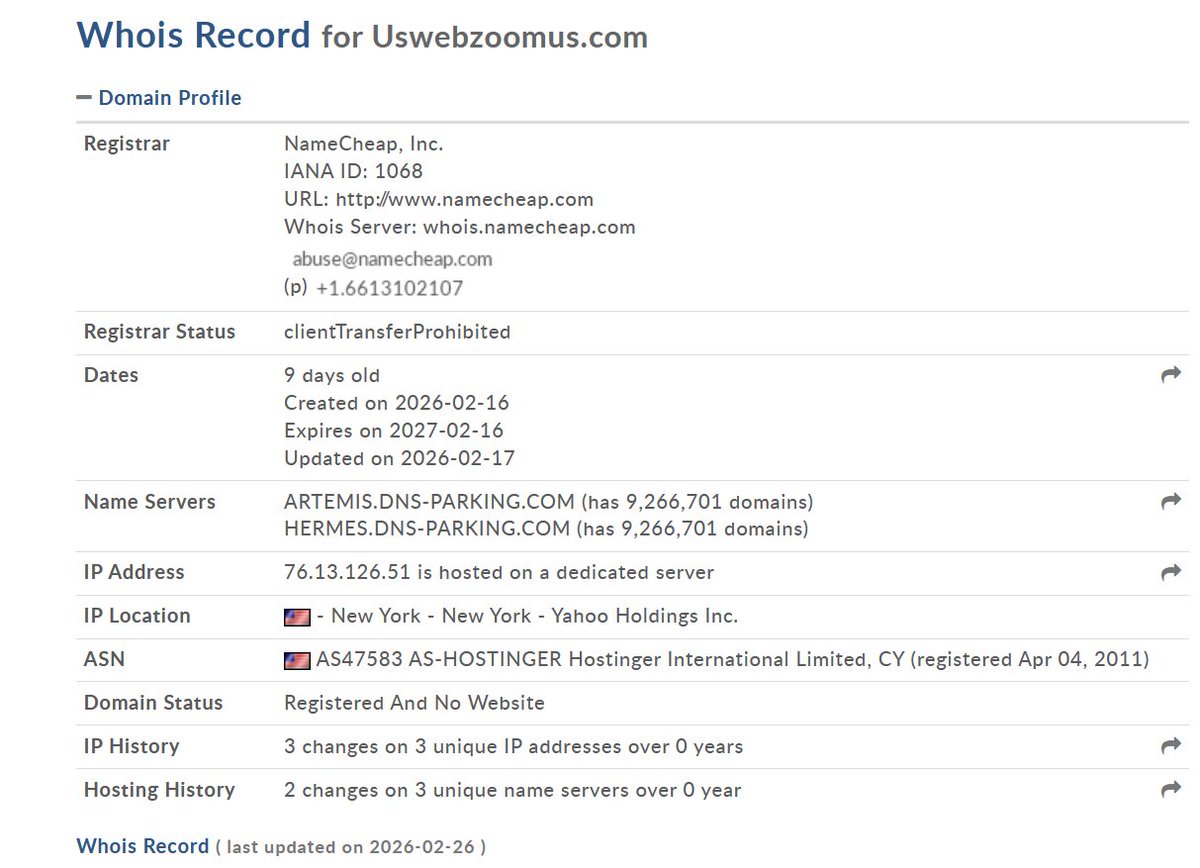
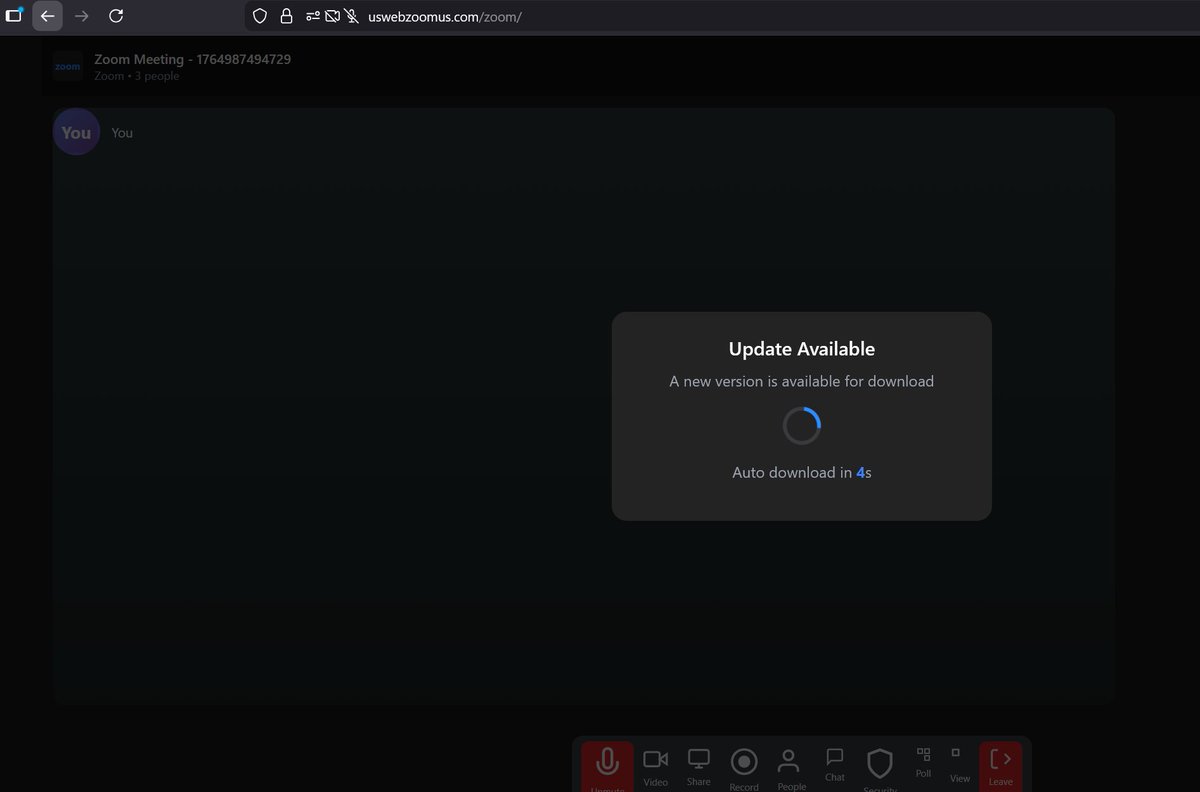
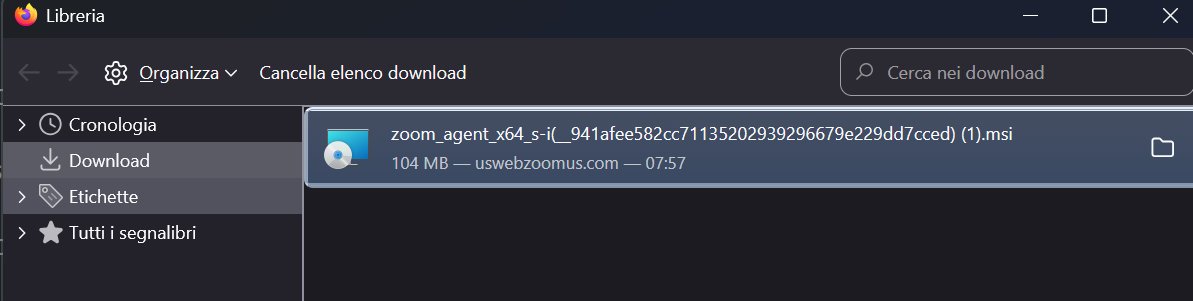
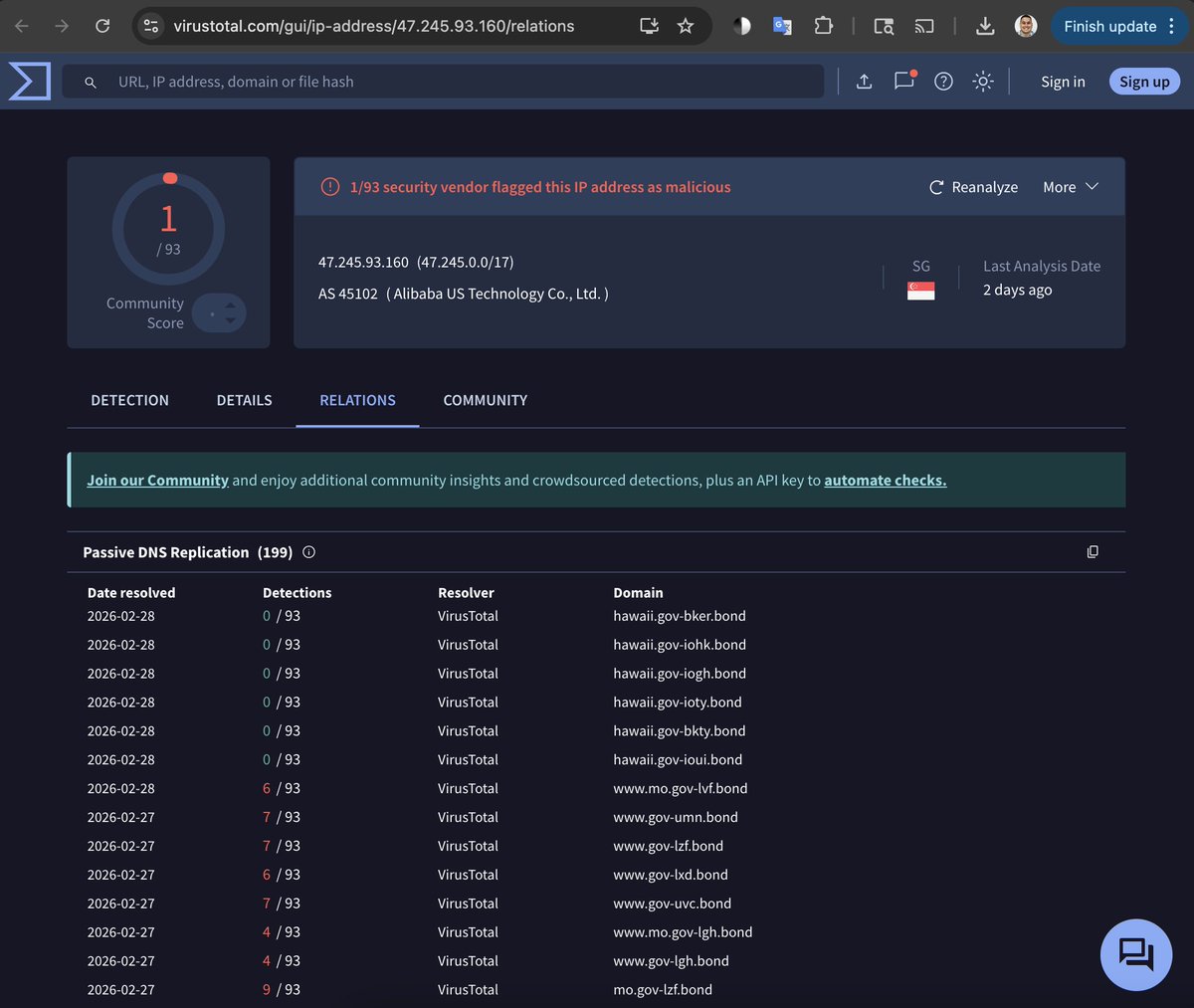
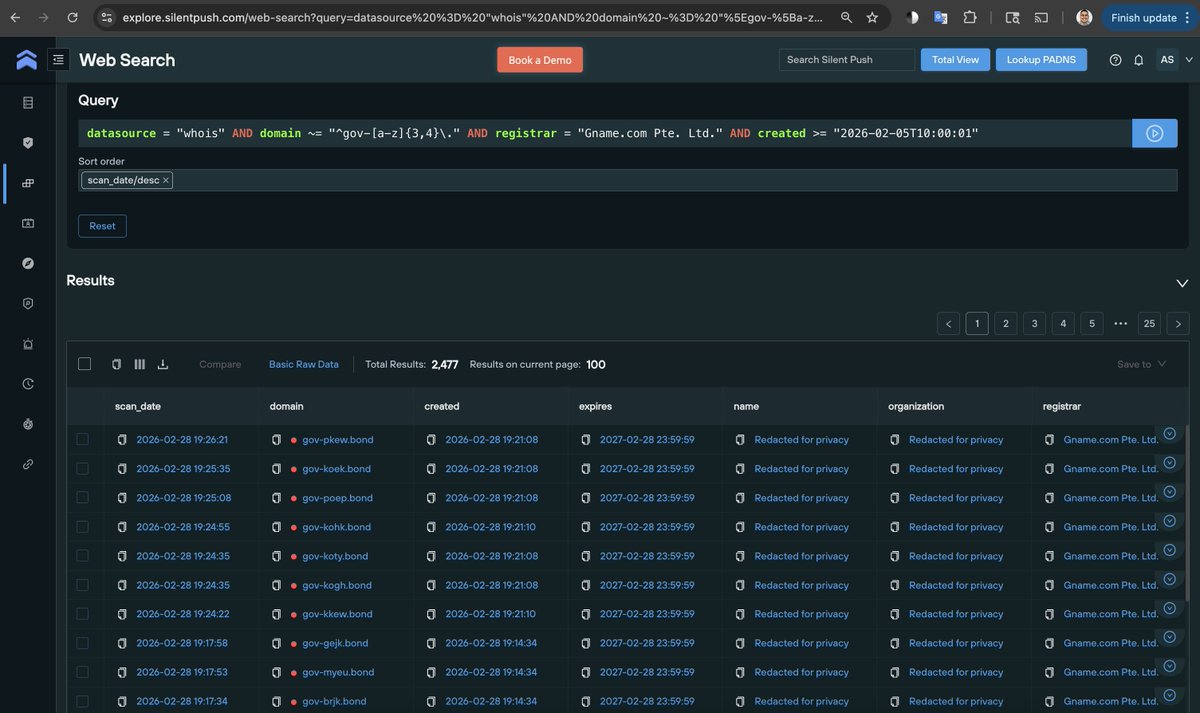
A fake Zoom meeting site mimics a video call, then uses an “Update Available” countdown to automatically download a malicious installer onto Windows machines—no permission required. bit.ly/4qXyLp7














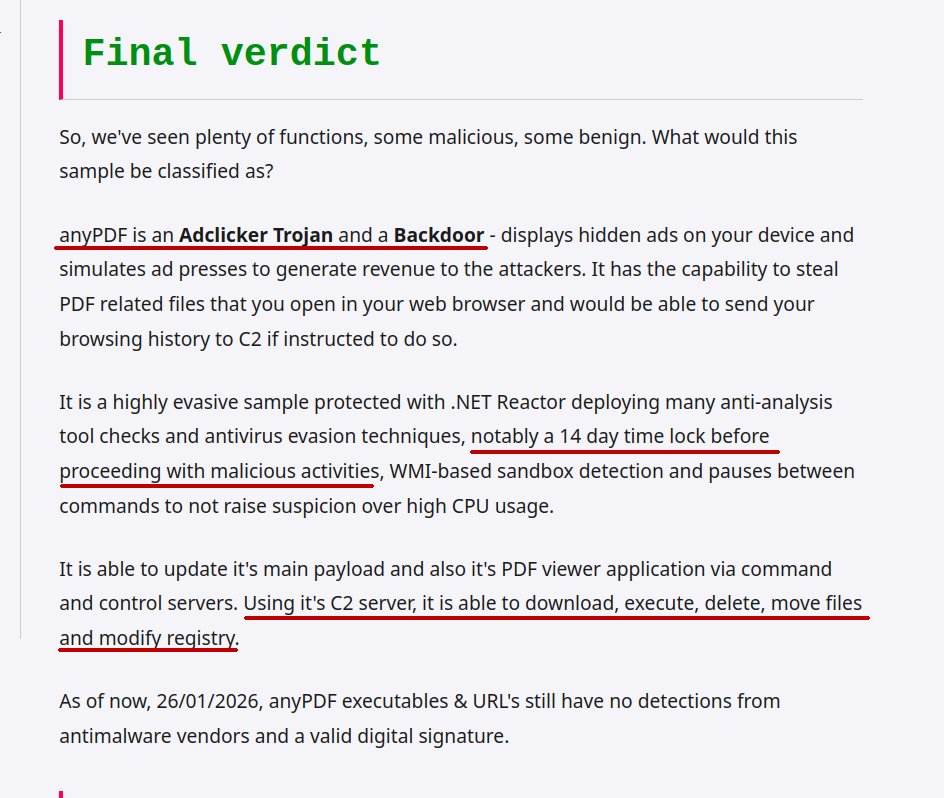
This is anyPDF - a popular application that over 5000 people downloaded on MajorGeeks, available at Softpedia and their own website hxxps://anypdf.com anyPDF is a highly evasive and fully undetected AdClicker Trojan with ability to connect to C2 server. rifteyy.org/report/anypdf-…