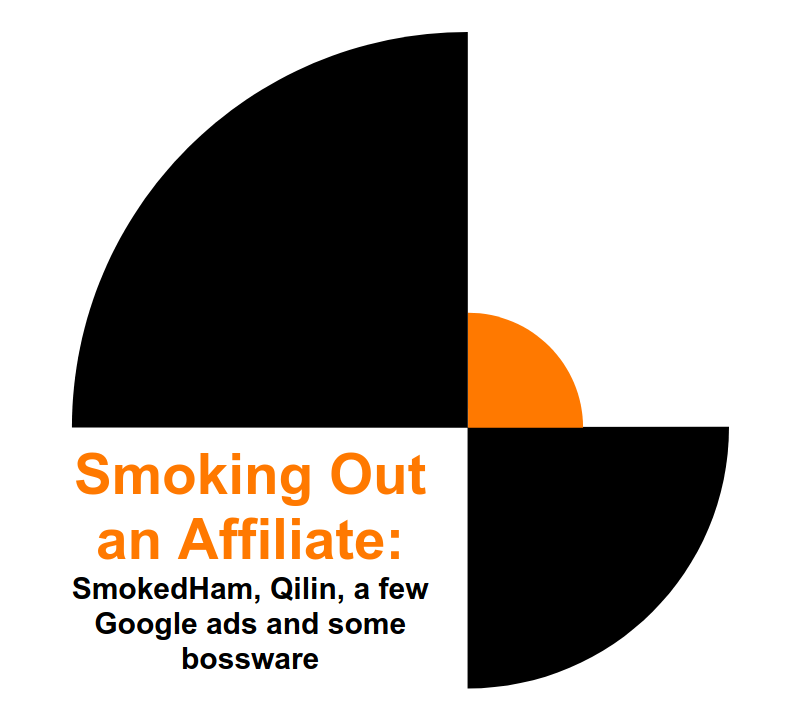
Structuring, normalizing, and parsing data is not the part of threat hunting that gets the most attention. Most people want to get straight to the interesting part: finding suspicious activity, following attacker behavior, and understanding what happened. But if you want to become a better hunter, you need to understand the data you are searching through. You also need to understand how good parsing and structure make investigations faster, cleaner, and more repeatable. Our goal at Threat Hunting Labs is to keep the experience consistent across labs and data sources, so people can focus on the investigation itself: • What happened? • Which systems were involved? • What activity matters? • What fields help prove it? We wrote a short post about how we approach this at Threat Hunting Labs, including why normalization matters, how parsing affects investigations, and how our search console helps users work with real telemetry more effectively. Read it here: threathuntinglabs.com/blog/how-threa…