Sabitlenmiş Tweet
芳乃さくら
85.2K posts

芳乃さくら
@MaverickTse
昔のAviUtlものはこちらに→ https://t.co/fpv4bYmI0e?amp=1 Abandoned AviUtl, now use MBP+FCPX 天滅⭕️共
Hong Kong Katılım Mart 2014
161 Takip Edilen322 Takipçiler

Really puzzling to me how exam cheating is a problem... do your exam in old fashion paper and pen, ban the use of smart device, put in a few invigilators...
Polymarket@Polymarket
NEW: Princeton University to end its 133-year tradition of unproctored exams as AI cheating concerns grow.
English
芳乃さくら retweetledi

KADOKAWA、45歳以上・勤続5年以上の社員を対象に早期退職希望者を募集 割増退職金を支給、人数の上限はなし 「筋肉質な体制の構築」目指す
gamebiz.jp/news/425886
#KADOKAWA
日本語
芳乃さくら retweetledi

【調査へ】インドで医学部の入試問題が流出か、230万人の受験が無効になり抗議デモ
news.livedoor.com/article/detail…
問題となった試験は、国立・私立を問わず医学部進学に必要な全国統一試験で、事前に出回っていた「予想問題」と、生物と化学の少なくとも135問が一致したという。

日本語
芳乃さくら retweetledi

7,000 false positives per square millimeter. The culprit was the lab gloves.
University of Michigan researchers just upended a core assumption in microplastics science. Latex and nitrile gloves, worn by the scientists doing the measuring, shed stearate particles that look chemically identical to polyethylene. Standard infrared and Raman instruments can't tell them apart. The gloves were counting as plastic.
Seven glove types tested. All contaminated. The cheapest fix: switch to cleanroom gloves, which dropped false positives to around 100 per mm² vs. 7,000.
The "credit card per week" headline (5 grams, WWF/Newcastle 2019) has separate problems. A 2022 re-analysis found severe methodological errors in the original estimate. Actual measured intake is likely 100x lower.
None of this means microplastics are harmless. Last month's data on brain accumulation still stands. But the numbers driving the panic may have been measuring the scientists, not the environment.
Science catching its own errors is exactly how it's supposed to work.

English
芳乃さくら retweetledi

BambuStudio has been violating PrusaSlicer AGPL license since their fork, with the same networking binary black box in question today. Why are they willing to burn the goodwill over it?
There's something most have sensed but never seen it all in one place, the five-law framework China built between 2017 and 2023 ⤵️
So maybe their hand is forced as their "network" is too valuable already? Each law on its own, interesting, okay... Read them together, and add any Chinese company with big reach to the mix you get the complete picture.
1) National Intelligence Law (2017)
All organizations and citizens must "support, assist, and cooperate" with intelligence work. The same law makes it illegal to disclose that cooperation happened. Cooperation is mandatory, and silence about it is mandatory too.
2) Cryptography Law (2020)
Commercial encryption must be state-approved and state-reviewed. When authorities request it, companies must provide decryption keys or plaintext. The state on both sides of that equation is the same one.
3) Data Security Law (2021)
Article 2 gives the state extraterritorial reach over data that touches Chinese national security or public interests. So EU/US data hosting does nothing to make it safe, because jurisdiction follows the company, not the server location.
4) Counter-Espionage Law revision (2023)
The general definition of espionage was expanded to cover "documents, data, materials, or items related to national security and interests." Industrial data is one of the intended targets since the revision.
5) Network Product Security Vulnerability regulation (2021)
Any company or researcher that discovers a software vulnerability must report it to MIIT within 48 hours. From there it flows to CNNVD (China National Vulnerability Database of Information Security), operated by the 13th Bureau of the Ministry of State Security. Microsoft's threat intelligence team documented Chinese state-hacker zero-day usage rising after this took effect. Shows the willingness to use the “tools” China built.
Together they describe a system with no neutral exits. Cooperation is required, encryption is real but the spare keys live at the ministry, jurisdiction follows the company across borders, industrial data is in scope, and discovered vulnerabilities flow to an intelligence agency 😬
3D printing became strategic for China in 2020 and joined the “Made in China 2025” plan soon after. Why does 3D printing matter so much? 1/x

Jeff Geerling@geerlingguy
Bambu Lab 3D printers: never again. They're breaking the open source social contract (for the nth time...), and I'm past hoping they'll amend their ways. youtube.com/watch?v=eb48Md…
English
芳乃さくら retweetledi

海外黑手档.com
长期以来,中共当局通过跨国镇压,将它在中国境内的恐惧统治延伸到海外。
今年3月,意大利以国家安全理由驱逐8名涉嫌参与对李老师进行跨国镇压的中国公民。这是欧洲国家在应对中共跨国镇压问题上的一次重要行动。
也说明民主社会已经开始认识到:中共的跨国镇压,不只是海外中国人的私人困境,更是对民主国家主权、法治与公共安全的直接挑战。
在美国,司法部和 FBI 也已经采取行动。美国曾起诉涉嫌在纽约曼哈顿运营中共秘密海外警察站的人员,并指控多名中国公安部人员通过假账号、网络骚扰和威胁手段打压在美中国人和民主活动人士。美国政府已经把中共跨国镇压视为对美国主权和居民安全的威胁。
同样,德国、瑞典、英国等国家也开始积极展开针对海外侨民实施此类活动的个人进行了调查和起诉。
这些行动证明了一件事:只要我们把证据留下来,把案例讲出来,把零散的恐惧变成系统的记录,跨国镇压就不再是无法追责的黑箱。
这不只是针对少数异见者的个案。现如今越来越多普通海外中国人,也开始遭遇监视、威胁、骚扰、定向举报、社交平台封禁、银行账户冻结、家人被派出所约谈、被要求“回国配合调查”、参加集会时被拍照跟踪,甚至在民主国家境内仍然被迫自我审查。
基于我们自身长期遭受跨国镇压的经历,也基于许多海外中国人正在承受却难以说出口的恐惧,我们决定不再沉默。
今天,我们与保护卫士(@SafeguardDefend)合作,正式启动跨国镇压专题项目:
海外黑手档.com
这是一个面向海外中国人、留学生、移民、异见者、活动人士、记者及其家属的匿名案例收集项目。我们希望系统记录中共在海外实施跨国镇压的方式,包括但不限于:
派出所、国保或街道办联系国内家人,要求劝阻海外亲属发声;
海外人员被拍照、跟踪、威胁,或被要求参加“谈话”;
推特、YouTube、Instagram、TikTok 等账号遭到定向举报、封禁或人肉攻击;
银行账户、支付账户、国内资产或亲属生活受到威胁;
CSSA、侨团、同乡会或其他组织参与反游行、盯梢、拍摄、施压;
被要求或胁迫配合亲共活动,向中国国内部门提供海外同学、朋友、社群成员的信息,或协助监视、举报、阻挠他人发声;
中国使领馆、海外警察站或相关人员介入骚扰、恐吓、信息收集;
因参与抗议、转发信息、接受采访、发布评论,而导致本人或家人在中国境内遭到报复;
被要求删除内容、停止发声、回国“说明情况”,或被暗示“不听话会有后果”。
我们收集这些案例,不是为了制造恐惧,而是为了终结恐惧。
所有提交内容都可以匿名。我们将尽最大努力保护提交者安全,并在去识别化、保护隐私的前提下,对案例进行整理、研究和国际倡导。相关资料将用于向媒体、人权组织、议会、政府机构和国际社会揭露中共跨国镇压的真实规模与具体手法。
每一份记录,都是一份证据。
每一次讲述,都是对沉默的突破。
每一个案例,都可能成为保护其他人的基础。
中共希望海外中国人在民主国家继续害怕、继续沉默、继续觉得“说了也没有用”。
但我们想说:从今天开始,我们不再把恐惧留给自己。
如果你或你身边的人曾经遭遇类似经历,请填写匿名问卷。
让我们一起记录中共伸向海外的黑手,揭露跨国镇压,捍卫民主社会的自由、安全与尊严。
海外黑手档.com

中文
芳乃さくら retweetledi

「重大な脅威」グーグルがセキュリティ上の失態、30億のGmail利用者が危険に(Forbes JAPAN)
#Yahooニュース
news.yahoo.co.jp/articles/9b67f…
日本語
芳乃さくら retweetledi
芳乃さくら retweetledi

网友投稿:“上海生化所 化学物品泄露,二次隐瞒”
5月7日,上海生化所,有课题组违规使用溴化氰、造成泄露,直到8日早上,实验室才组织清理。
但是直到5月10日晚,也并未告知其他课题组的师生。
自5月8日,多人因吸入氰化物中毒,于上海市中山医院急诊就诊。
目前,生化细胞所官方仍未作出响应措施。
根据《上海市处置危险化学品生产安全事故应急预案》,发生泄露后应在30分钟内口头,1小时内书面报告属地应急管理部门。迅速疏散人员,控制泄漏源。生化所未做到疏散人群,并且试图隐瞒。严重影响了人员身体健康。其他楼层的人员身体不适后,打听后才得知污染源泄露事件,身体安全得不到保障。
直到5月10日,有学生陆续在楼层自行检测,才发现有污
染泄露,官方隐瞒不报。


中文
芳乃さくら retweetledi
芳乃さくら retweetledi

国家公務員の氷河期試験が始まるそうです
気になったので待遇を調べてみました
こんなの絶対氷河期世代差別ですよね😢
国家による弱い者いじめです😭
——— 生まれて、すみません
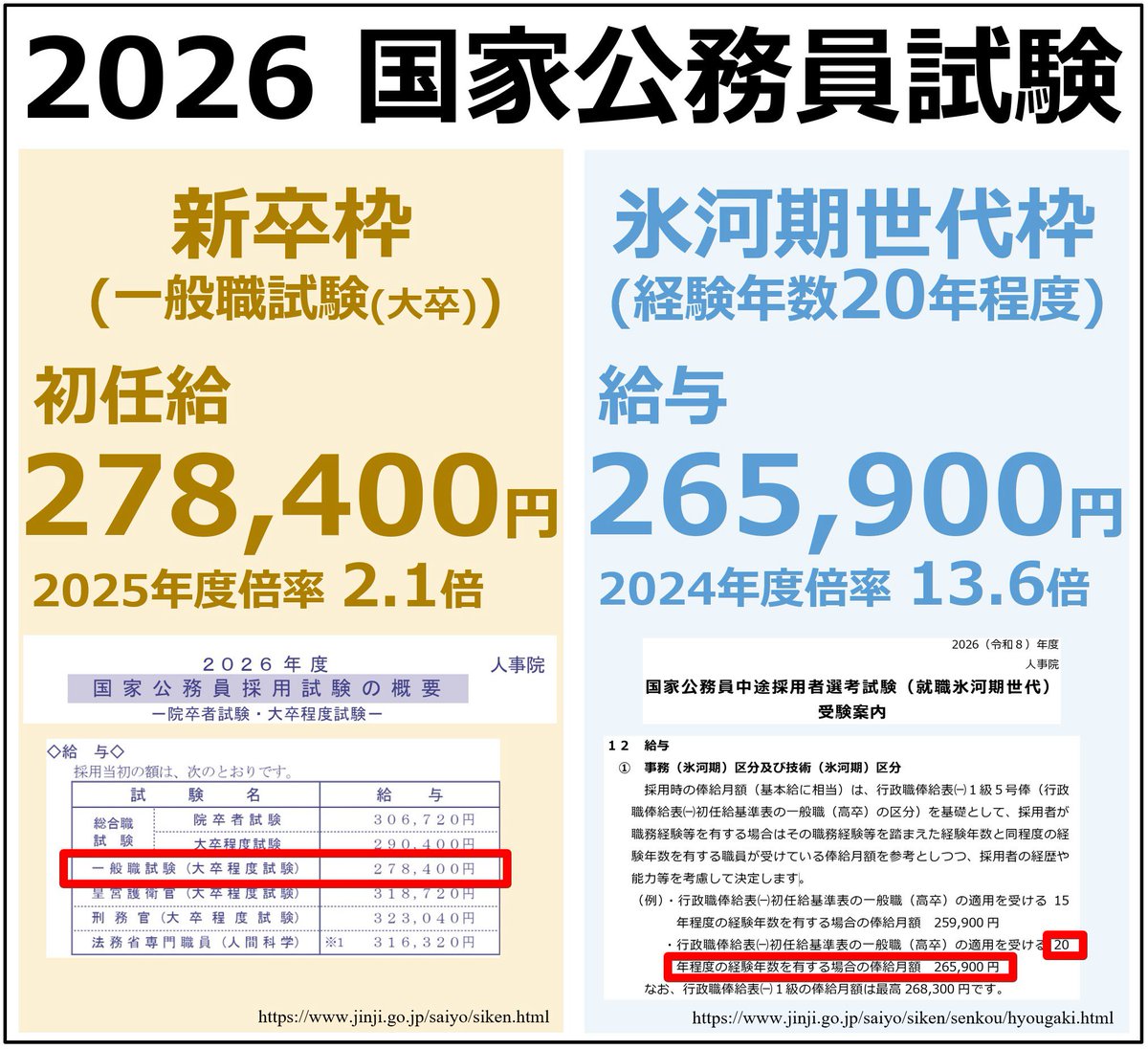
共同通信公式@kyodo_official
氷河期試験、27日から申し込み - 国家公務員、177人採用 news.jp/i/142646417114…
日本語
芳乃さくら retweetledi

‼️🚨 Pwn2Own Berlin 2026 just hit a wall. For the first time in 19-years, ZDI rejected dozens of working zero-day RCE submissions because organizers ran out of contest slots.
Rejected hackers are now going public with PoC demos and direct vendor disclosures, breaking Pwn2Own's usual secrecy.
▪️ AI surfaces a massive wave of 0-day RCEs.
▪️ Submissions overwhelm ZDI past max capacity.
▪️ Slots run out. Researchers with working chains get rejected.
▪️ "Revenge disclosures" begin. ← we are here.
Confirmed casualties so far:
▪️ @xchglabs : 86 vulnerabilities prepared (PyTorch, NVIDIA, Linux KVM, Oracle, Docker, Ollama, Chroma, LiteLLM, llama.cpp). All rejected. Now reporting directly to vendors with writeups dropping as patches land.
▪️ @ggwhyp : full-chain Firefox RCE on Windows. Rejected. Publicly demoed (HTML page → cmd.exe → calc.exe). Responsibly disclosed to Mozilla.
▪️ @yunsu_dev : working RCE chain, rejected. Submitting elsewhere.
▪️ @ryotkak : tried to register for 3+ weeks. ZDI confirmed "at maximum capacity, can't add extra contest days." Considered canceling flight and hotel.
▪️ @anzuukino2802 : Claude Code RCE PoC. Rejected.
▪️ @desckimh : 0-day RCEs in Ollama and LM Studio. Rejected.
Reported impact: a community-estimated 150+ researchers tried to register. Accepted contestants are now being warned about collisions. Rejected vulnerabilities going to bug bounty programs may trigger pre-event patches that invalidate the work of those who got in.
ZDI has not publicly addressed the capacity issue. The event still runs May 14-16 in Berlin.


English
芳乃さくら retweetledi

🚨 CVE-2026-7482 in Ollama could let remote attackers leak process memory from more than 300,000 exposed servers using crafted GGUF files.
Separate unpatched Windows flaws enable persistent code execution through Ollama’s update mechanism.
Full details and mitigations: thehackernews.com/2026/05/ollama…

English
芳乃さくら retweetledi

🚨 WARNING: A malicious Hugging Face repository impersonating #OpenAI’s Privacy Filter model reached #1 trending with about 244,000 downloads in 18 hours while delivering a Rust-based infostealer to Windows users.
Read: thehackernews.com/2026/05/fake-o…
English
芳乃さくら retweetledi
芳乃さくら retweetledi
芳乃さくら retweetledi
芳乃さくら retweetledi

If clear #UFO footage like this had been in yesterday’s government drop, today might have been the Day After Disclosure.
Western US. 20 years ago. High Noon. Metallic disc. Jet flies right by for scale.
Dr. Dan@UAPDr
A silver disc. Broad daylight. Multiple witnesses. And 16 years later, still sitting on YouTube like a forgotten artifact. I don’t know what this is. But it belongs in the “harder to dismiss than it should be” folder. #UAP #UFO #OVNI
English









