Max Rogers
1.8K posts


Max Rogers
@MaxRogers5
Sr. Director of SOC at Huntress. Ex-Mandiant/FireEye. Bringing security to the Fortune 5,000,000.






People keep talking about model releases, but the thing I'm most excited for in early 2026 is Claude Code 3.0.














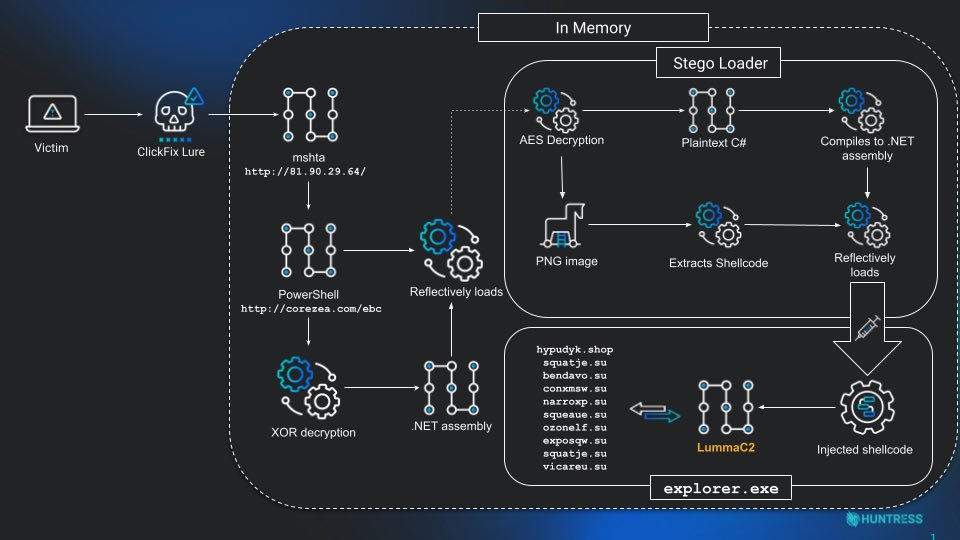
Super hyped to share that @HuntressLabs published a Rapid Response blog on the recent #React2Shell post-exploitations observed. We discovered and analyzed a few payloads that were named #PeerBlight, #CowTunnel and #ZinFoq. We also observed a variant of #Kaiji malware. 3 Modelo's 🍺 in and the malware started making sense. By the 4th one I was naming them like Pokémon except way more unhinged. PeerBlight, I choose you! Thank you for your contributions @sudo_Rem, @LindseyOD123, @_JohnHammond, @bumbucha, and @aaron_deal. Couldn’t have done it without your support ❤️ huntress.com/blog/peerbligh…