Meon Valley Web
173 posts


Meon Valley Web
@MeonValleyWeb
Web design in the Meon Valley, Hampshire. Supporting small and medium local businesses with modern, effective websites. WordPress custom fast hosting also.


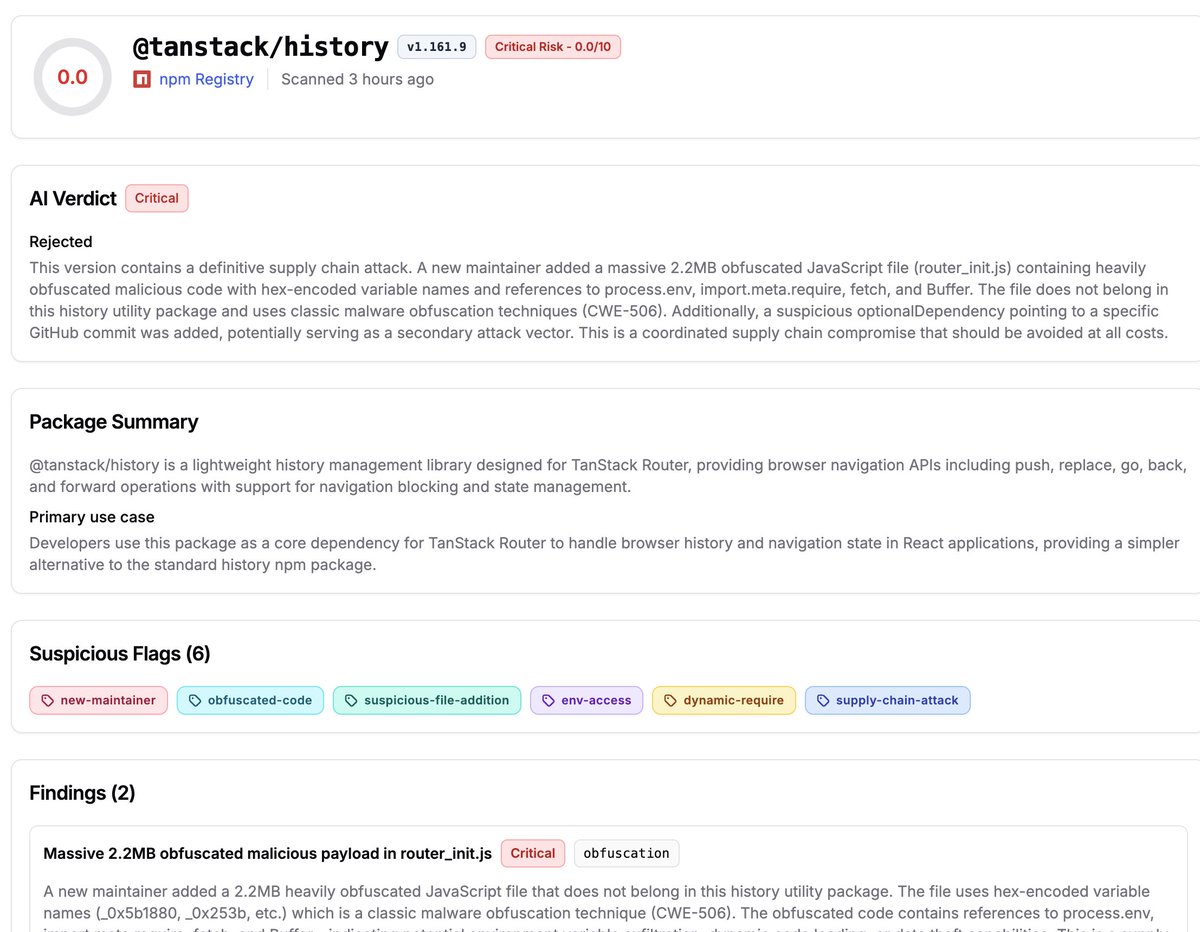

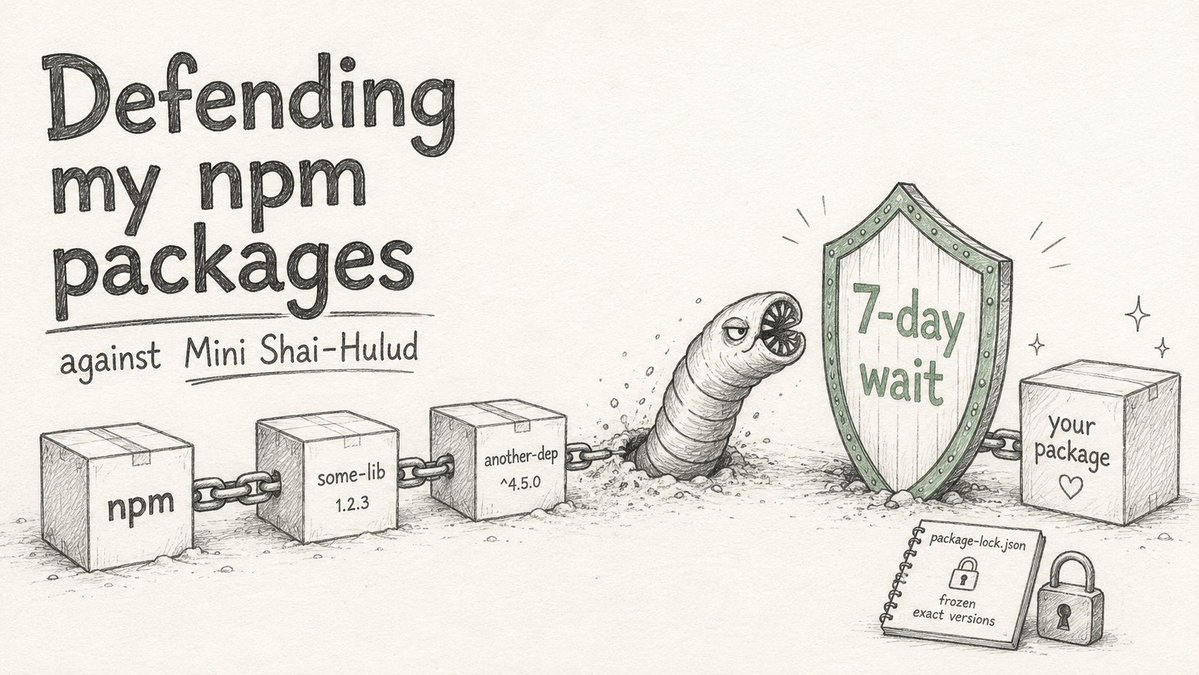
SECURITY ADVISORY — TanStack npm packages A supply-chain compromise affecting 42 @tanstack/* packages (84 versions total) was published to npm earlier today at approximately 19:20 and 19:26 UTC. Two malicious versions per package. Status: ACTIVE — packages are deprecated, npm security engaged, publish path being shut down. Severity: HIGH — payload exfiltrates AWS, GCP, Kubernetes, and Vault credentials, GitHub tokens, .npmrc contents, and SSH keys. If you installed any @tanstack/* package between 19:20 and 19:30 UTC today, treat the host as potentially compromised: • Rotate cloud, GitHub, and SSH credentials immediately • Audit cloud audit logs for the last several hours • Pin to a prior known-good version and reinstall from a clean lockfile Detection — the malicious manifest contains: "optionalDependencies": { "@tanstack/setup": "github:tanstack/router#79ac49ee..." } Any version with this entry is compromised. The payload is delivered via a git-resolved optionalDependency whose prepare script runs router_init.js (~2.3 MB, smuggled into each tarball at the package root). Unpublish is blocked by npm policy for most affected packages due to existing third-party dependents. All 84 versions are being deprecated with a SECURITY warning, and npm security has been engaged to pull tarballs at the registry level. Full technical breakdown, complete package and version list, and rolling status updates: github.com/TanStack/route… Credit to the security researcher for responsible disclosure.



🦀 Crabbox 0.3.0 is out. Remote Linux runs for dirty worktrees 🔐 GitHub browser login 🧰 Blacksmith Testbox wrap 📡 crabbox attach for live run replay 📜 Durable run events ☁️ AWS image create 🛡️ Cloudflare Access brew upgrade openclaw/tap/crabbox github.com/openclaw/crabb…



I spent an hour plus this afternoon trying to get OpenClaw to work with GPT. I asked it to do a simple task to send me a weekly stats recap email that Opus had no trouble with. Here's how the conversation went: "You completely messed up the previous template" "Sigh you made a mess. Why don’t you open the email template and I can edit manually" "no you totally screwed it up tbh. let's switch the model to sonnet" Again, big fan of OpenClaw (+ Codex) but this model simply doesn't seem to work with following through on agentic tasks (or just simple cron jobs). Maybe it's a skill issue on my part - although the AI builder groups I'm part of say similar things. Hopefully, Spud / GPT 5.5 will solve this.

Here's the truth people are afraid to admit: Even if using Opus 4.7 with OpenClaw costs you $1,000 a month through the API, you still need to be paying for it When it comes to OpenClaw there's simply no second best model ChatGPT is completely useless for OpenClaw. Doesn't complete tasks, actively deletes and messes up files, has no idea how to use tools Every night before I go to bed I pray ChatGPT 5.5 matches Claude at OpenClaw usage. OpenAI has been a lot more consumer friendly when it comes to limits and oauth use But at the moment there is no dodging the truth. Claude is the only way to go for OpenClaw I look at it like this: OpenClaw with Opus 4.7 is a super intelligent employee that works 24/7 without complaint Even if I pay $1,000 a month for API usage ($12,000 a year) that's still a steal compared to hiring humans I'd be paying over $100,000 a year if I hired an actual person. And they wouldn't be working 24 hours a day and they wouldn't be immediately responding to my telegram chats and they'd file HR complaints if I talked to them the way I talked to my Claw I'm confident OpenAI is training their new models for OpenClaw usage, but in the meantime, there's simply no 2nd best. Pay for the API.