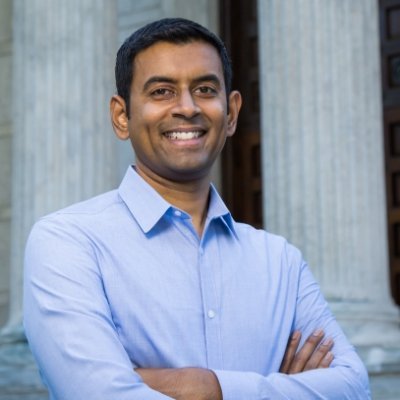
Adil Inam
13 posts


Adil Inam
@MuhammadAdilIn1
CS [email protected]://t.co/rYcSQfmdEO. All opinions are my own.
Champaign, IL Katılım Ağustos 2021
90 Takip Edilen66 Takipçiler

The struggle is real. 🤷♂️
Akul Goyal@akulgoyal00
I have never had such a hard time proving I am a human.
English

Listen to this guy.
Adam Bates Yuile@AdamBatesOrg
👇 spoiler warning for intrusion detection research 👇
English
Adil Inam retweetledi

Paper link here: gangw.cs.illinois.edu/mitre24.pdf. We disclosed our results to the surveyed company’s, @MITREattack and CITD, and will be also be presenting these results at ATTACKCon 5.0 this Fall.
English
Adil Inam retweetledi

To understand how @MITREattack is used in commercial endpoint detection products, @avirkud4 led an analysis of the ATT&CK technique annotations in the @carbonb1ack, @splunk, @elastic, and Sigma rulesets.
English
Adil Inam retweetledi

Upcoming at @USENIXSecurity’24 — In (academic) systems security research, name checking @MITREattack has been the “peer review armor” of choice for a lot of work recently. But do these papers understand what ATT&CK is(n’t)? What about commercial products?
English
Adil Inam retweetledi
Traditionally in ML, building models is the central activity and evaluation is a bit of an afterthought. But the story of ML over the last decade is that models are more general-purpose and more capable. General purpose means you build once but have to evaluate everywhere. Increasing capability means taking on more realistic tasks in higher-stakes domains, so benchmarks have to be far more complex and thoughtful, and in many cases even the most careful benchmarks simply aren't enough. So both the quantity and quality of evaluations has to increase.
But status hierarchies change slowly in any research field, including ML. Most researchers' dream is to build the next transformer. That's a lottery with incredibly low odds. I suspect that researchers who focus on evaluation and understanding will have a much easier time making impactful contributions and standing out, despite the traditionally lower status of this type of work. (Obviously oversimplifying a bit to make a point; there's a lot more to ML than model building and evaluation.)
English
Adil Inam retweetledi
Adil Inam retweetledi
Adil Inam retweetledi

Tomorrow morning in Session 9C (9am, Bayview AB) — system auditing research may not be sexy, but it has *exploded* since 2015. Come watch @MuhammadAdilIn1 and I break it all down for you in our data provenance SoK, “History is a vast early warning system!”

English
Adil Inam retweetledi

Excited to announce that our *data provenance* SoK, "History is a Vast Early Warning System: Auditing the Provenance of System Intrusions," has been conditionally accepted to @IEEESSP #Oakland23. Before finalizing the camera-ready paper, we need your help!
English
Adil Inam retweetledi
A great ride with @MuhammadAdilIn1 @wajihulhasan @AliThespy @AdamBatesOrg and other collaborators to @NDSSSymposium! #NDSS22
It's eye-opening when @wajihulhasan first showed me that configurations can be as crazy as part of attack vectors by presenting CVE-2016-7790 in CS 523.
Adam Bates Yuile@AdamBatesOrg
Excited to share that our work "Forensic Analysis of Configuration-based Attacks" has been (conditionally) accepted to @NDSSSymposium #NDSS22! Congrats to student authors Adil Inam, @wajihulhasan, and Ali Ahad (UVA).
English

