NDA0E
200 posts



@illegalFawn @eranet_com @malwrhunterteam @JAMESWT_MHT @dubstard @YourAnonRiots @andsyn1 @UK_Daniel_Card @BeeHiveCyberSec @Malcoreio @douglasmun 45.134.26.105
45.134.26.175
45.134.26.182
45.134.26.184
45.134.26.187
45.134.26.190
45.134.26.192
45.134.26.195
45.134.26.197
45.134.26.220
45.134.26.221
45.134.26.225
aesecdip[.]icu
inksecdip[.]icu
insecdip[.]icu
aeksecpld[.]cyou
@Namecheap:
kunimuni[.]pro
hodvin[.]xyz

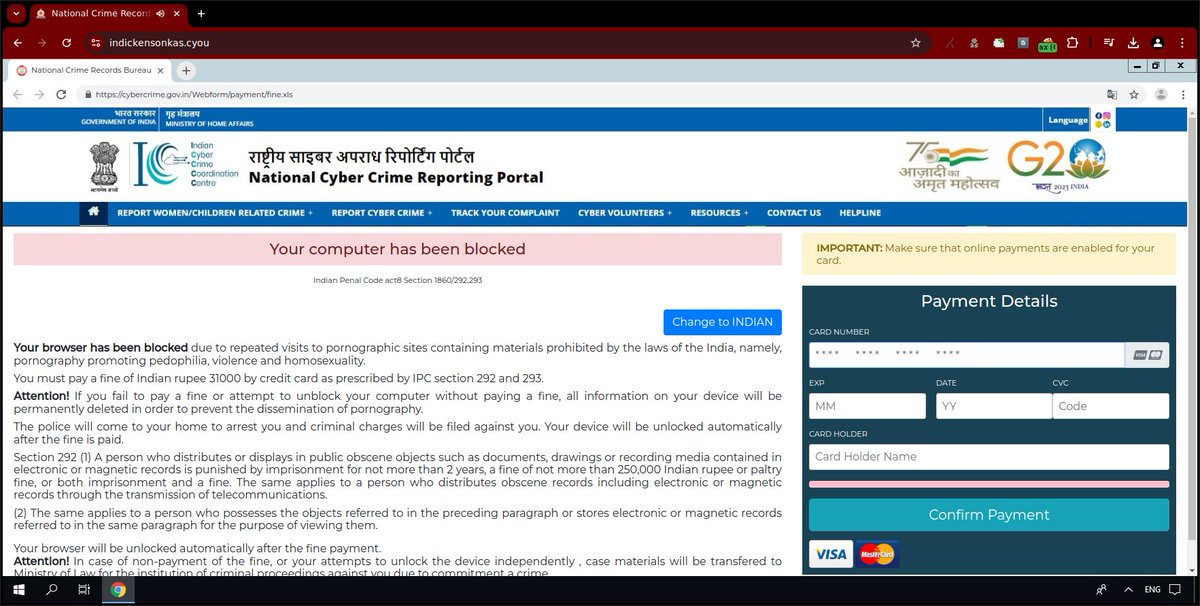
@eranet_com please revoke the #scareware domain
https ://indickensonkas.cyou/
@malwrhunterteam @JAMESWT_MHT @dubstard @YourAnonRiots @andsyn1 @UK_Daniel_Card @BeeHiveCyberSec @Malcoreio @douglasmun #scam #phishing
English

@BlinkzSec @zbraiterman @thejonmccoy @psiinon @kingthorin_rm @ricekot_ @banthisguy9349 @RacWatchin8872 @DaveLikesMalwre @Gi7w0rm @KibernaSecurity wishing you the same :)
English

Happy Holidays
@zbraiterman @thejonmccoy @psiinon @kingthorin_rm @ricekot_ @NDA0E @banthisguy9349 @RacWatchin8872 @DaveLikesMalwre @Gi7w0rm @KibernaSecurity and all the others
English

Mellat Mobile Bank apk android
> spy banker
sample
bazaar.abuse.ch/sample/22fcd8f…
From
pub-97b2fe2a03c74adc8ddc74989d2d6f0c.r2 dev/mellat.apk
h/t @malwrhunterteam
Indonesia

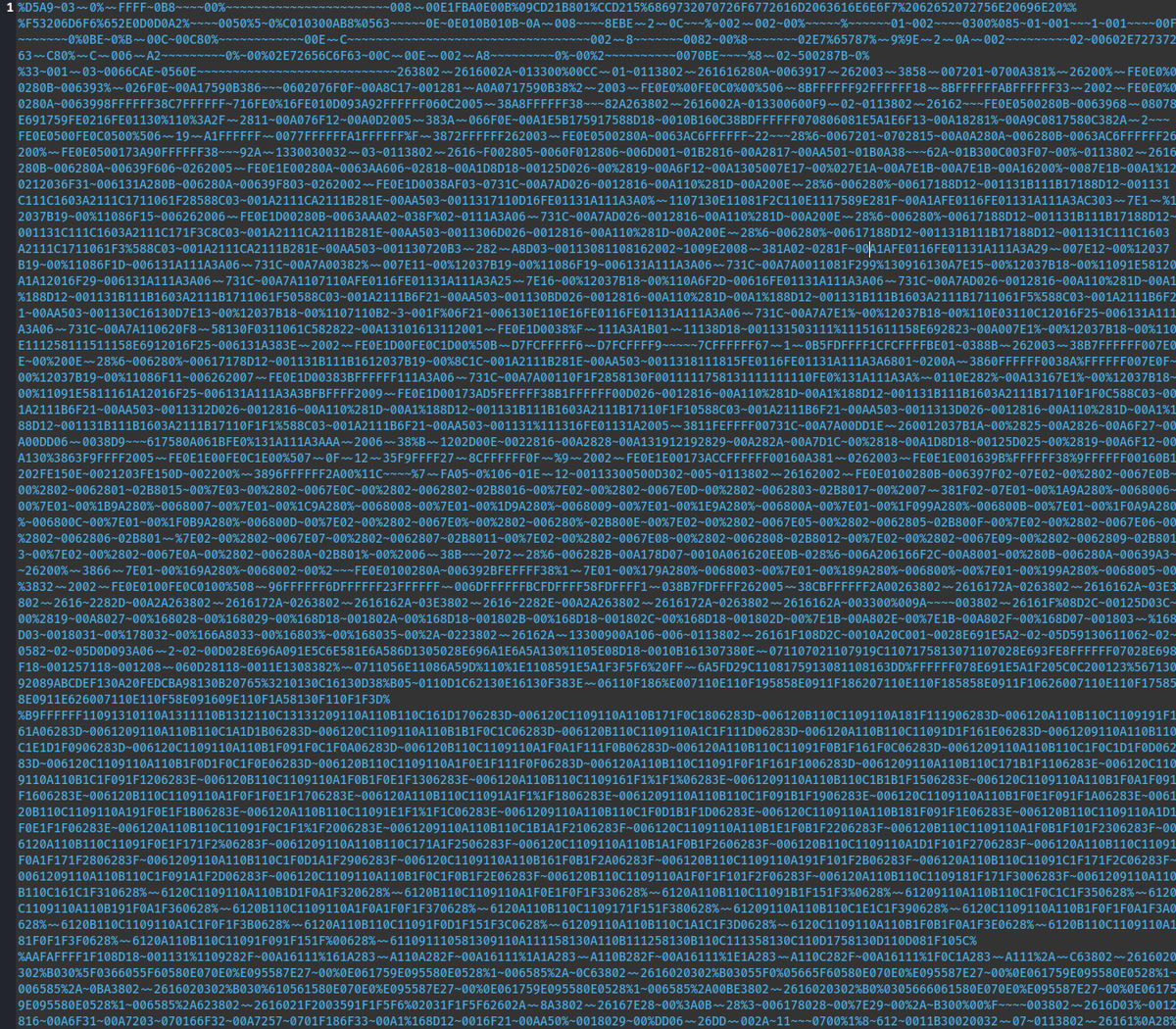
@banthisguy9349 CyberChef recipe: #recipe=Find_/_Replace(%7B'option':'Simple%20string','string':'%25'%7D,'4',true,false,true,false)Find_/_Replace(%7B'option':'Simple%20string','string':'~'%7D,'000',true,false,true,false)From_Hex('None')&oeol=FF" target="_blank" rel="nofollow noopener">gchq.github.io/CyberChef/#rec…
MD5: bc1705db6ccc60784390e7ae66887148
Français

#decoding challange!
Decode the following from this url:
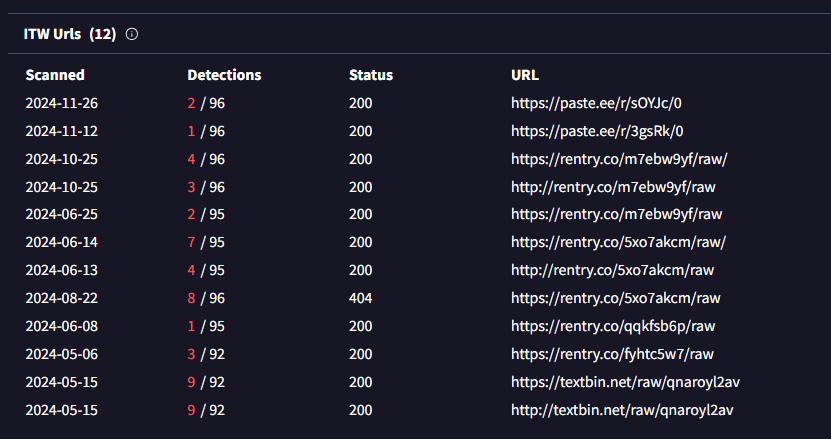
hxxps://paste.ee/r/sOYJc/0
Below the encoded string:
This encoded string was observed for the first time 2024-05-15
English
NDA0E retweetledi

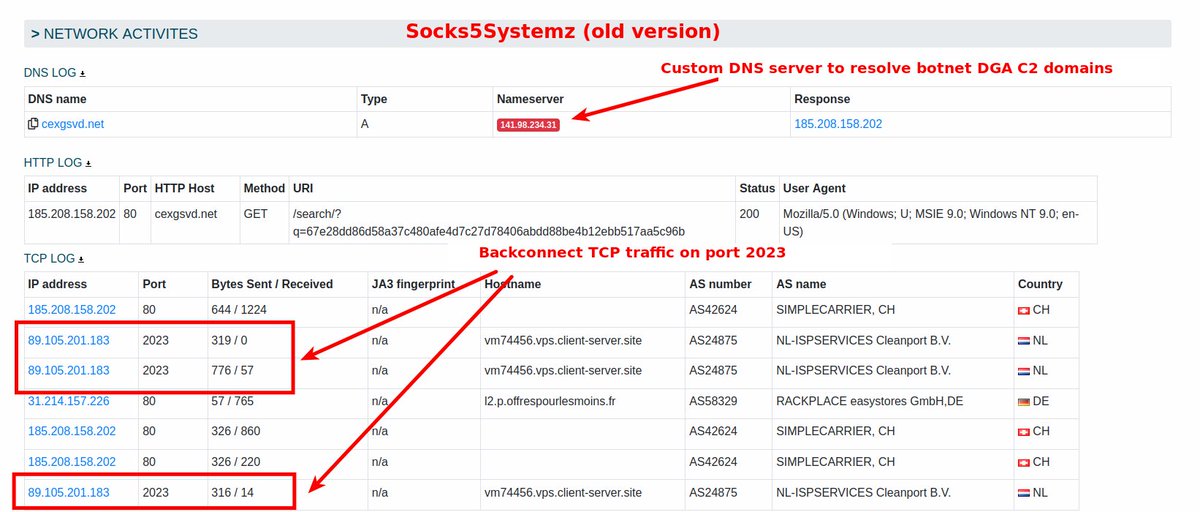
On the 1st of December, the notorious Socks5Systemz payload server hosted at AS57678 (Cat Technologies 🇭🇰) that is already active for several months started to serve a new version of Socks5Systemz ⤵️
🌐 urlhaus.abuse.ch/url/3189430/
This is the first major change since 2023 in Socks5Systemz and includes:
🔑 New RC4 key used during C2 communication: hi_few5i6ab&7#d3
👋 Direct IP communication through HTTP(s) for botnet command and control instead of the usage of a DGA and a custom DNS server
🔙 Backconnect TCP port changed from 2023 to 2024
Current botnet C2 servers:
188.119.66.185:443 CHANGWAY 🇭🇰
45.155.249.212:443 RACKPLACE 🇩🇪
91.211.249.30:443 PODAON 🇱🇻
Malware sample:📄 bazaar.abuse.ch/sample/528334e…
Socks5Systemz IOCs: 🦊 threatfox.abuse.ch/browse/malware…

English
NDA0E retweetledi

#AsyncRat #Malware
💣holder-apartments-face-matthew[.]trycloudflare[.]com/uline/Nr-2005-028763-2024-PDF[.]lnk💣
lnk->vbs->bat (checks if Avast exists) -> zip -> python scripts (injects shellcode) -> AsyncRat
app.any.run/tasks/0a336523…
app.any.run/tasks/13911dd7…




English

@1ZRR4H 90+ payloads hosted on 198.23.136.104: urlhaus.abuse.ch/browse.php?sea…
English

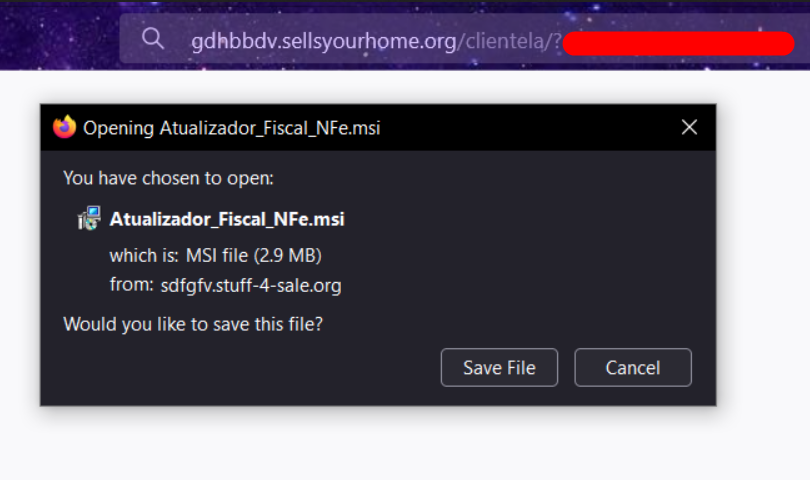
Interesting campaign in Brazil installs an Atera agent for remote control of victims.
Other distribution domains:
+ gdhbbdv.sellsyourhome[.]org
+ nmfhnjf.knowsitall[.]info
+ aweewe.barrel-of-knowledge[.]info
Download from: https://sdfgfv.stuff-4-sale[.]org/clientela/Atualizador_Fiscal_NFe.msi
Johnk3r@johnk3r
Campaign remains active with 100+ delivery URLs (thanks @ValidinLLC). -New email for registration; -Victims who click are registered before RMM delivery; location/FQDN controls manage payload; -Financial, Tech, Hospital and Government firms found in the console. @AteraCloud
English
NDA0E retweetledi

🚨 Attackers use public open directories for hosting #malicious scripts disguised as .txt and .jpg files
These are utilized in multi-stage #AsyncRAT #infections
See technical breakdown of the tactics from @RacWatchin8872 👇
any.run/cybersecurity-…
English

@ShanHolo thank you for the sample,
i've written a YARA rule to detect it
yaraify.abuse.ch/yarahub/rule/K…
English

🚨#Malware #ecrime🚨
hxxps://217.195.153.196/assets/paleochorologyma.exe
⚠️#koiloader #TMBackdoor
☣️paleochorologyma.exe➡️9e70e823876c7e83bf254d1f8fcbb3e5
📡hxxp://217.195.153.196/academy.php
HT

@onecert_ir @Namecheap Similar phishing:
hXXps://45[.]147[.]230[.]41/
hXXp://sana-ir.wicaso6530[.]workers[.]dev/
Malware payloads:
https://45[.]147[.]230[.]41/app.apk
hXXps://github[.]com/iosyu01/okdash/raw/main/assets/eblagh.apk
Samples: bazaar.abuse.ch/browse/tag/San…
Filipino

#phishing and #malware attack against Saham Edalat
Domain:
specbest[.]com
hXXps://specbest[.]com/Source/dashbord/
User agent: Android
Proxy: Iran
Payload URLs:
hXXps://specbest[.]com/Source/dashbord/app.apk
@Namecheap

English


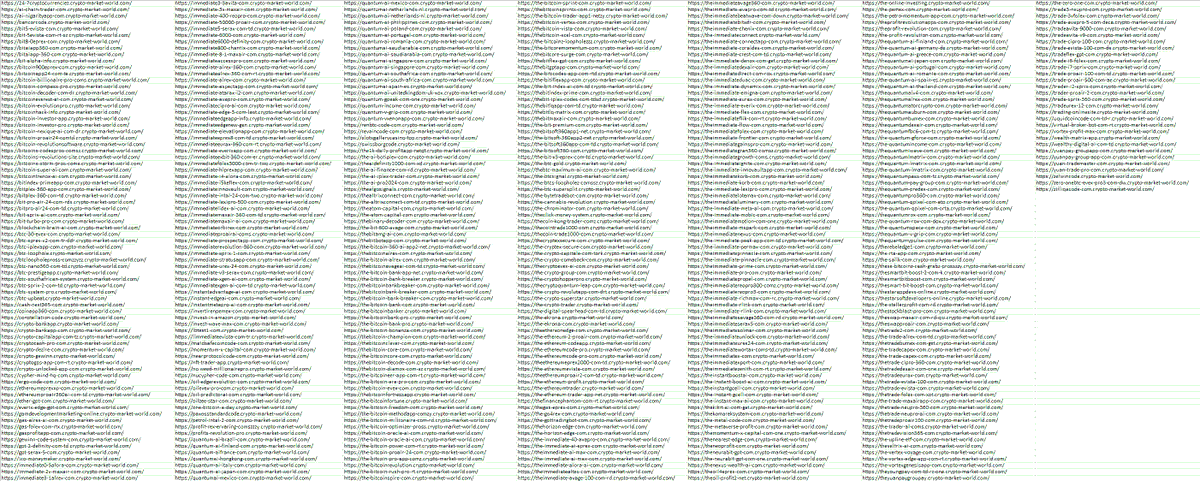
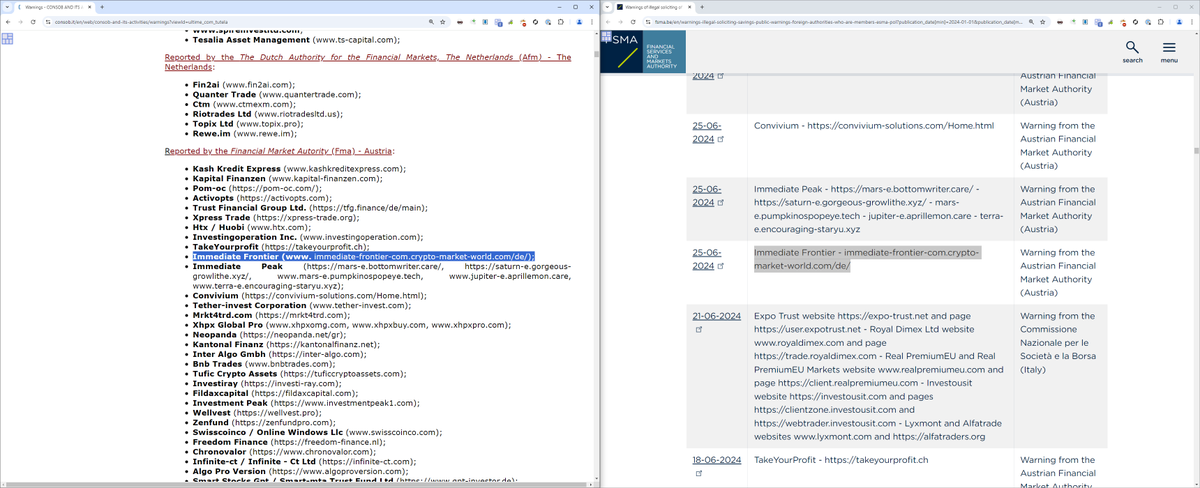
@illegalFawn @FMA_AT @FSMA_info @CNMV_IFI @CNMV_IP @CNMV_MEDIOS @CERT_Polska @CloudflareAbuse @AgidCert @YourAnonRiots @UK_Daniel_Card @malwrhunterteam @JAMESWT_MHT @dubstard @BeeHiveCyberSec 15.5k found on censys (this includes subdomains): search.censys.io/search?resourc…
it's only 3k without subdomains: search.censys.io/search?resourc…
most of it is hosted at simplecarrier rather than Cloudflare.
English

@FMA_AT @FSMA_info @CNMV_IFI @CNMV_IP @CNMV_MEDIOS @CERT_Polska, you have a warning on the fake trading platform immediate-frontier-com.crypto-market-world[.]com: how about pushing @CloudflareAbuse for nuking crypto-market-world.com?
@AgidCert @YourAnonRiots @UK_Daniel_Card #scam

English

@JAMESWT_MHT @cocaman Hey James. The issue is a weird tag ("Τράπεζα Πειραιώς") submitted by @NDA0E . I've removed the tag and the issue seems to be gone.
For further bug reports, I suggest to send me an email as I am not following X.
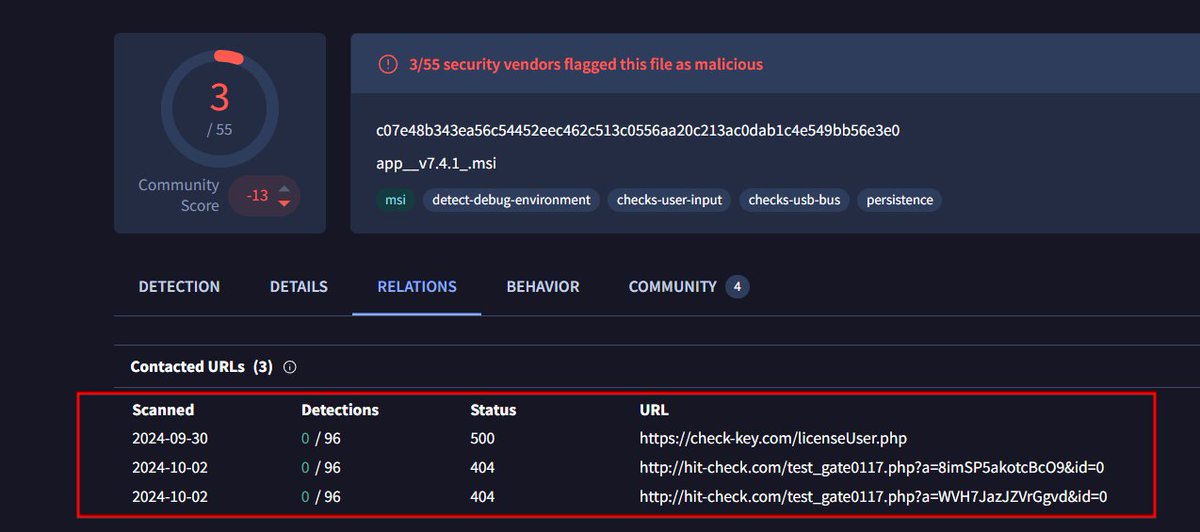
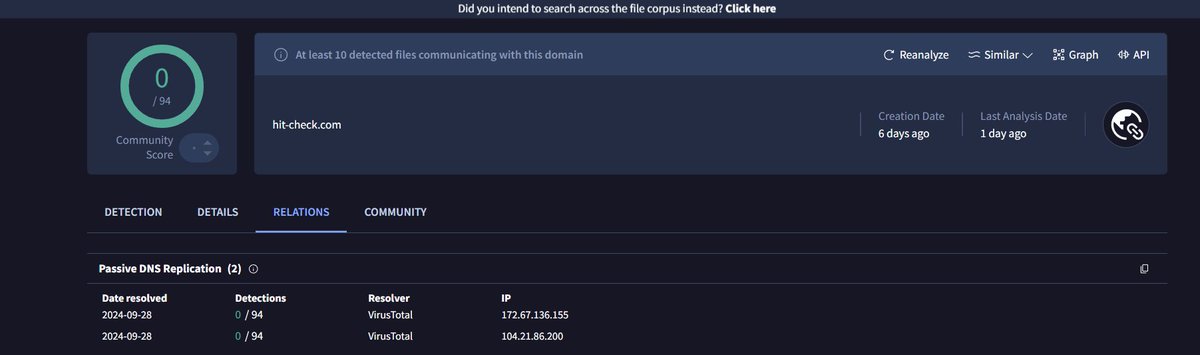
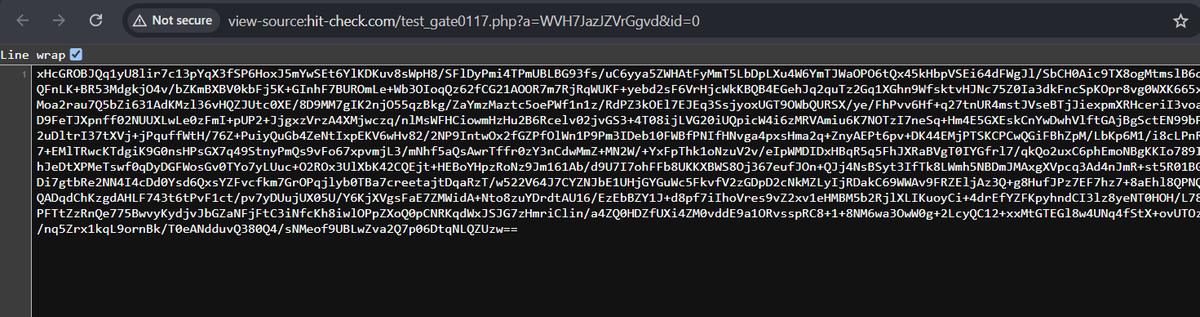
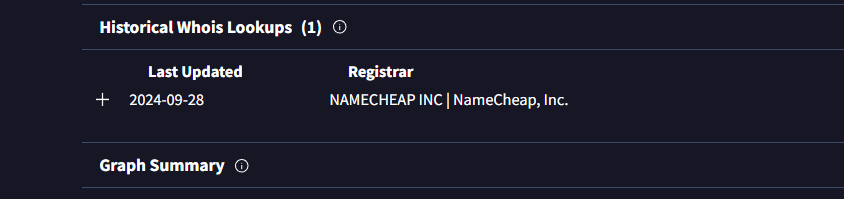
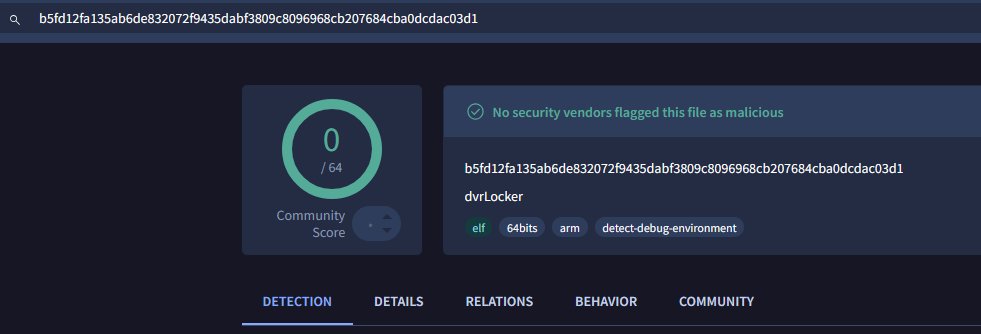
This is similar to the lumma C2 behavior. What could this really be?
cc. @banthisguy9349 @cyb3rops
#lumma #infosec #VT
English

@BlinkzSec @banthisguy9349 @tolisec @500mk500 @RacWatchin8872 @DaveLikesMalwre C2: 5.255.125.247:4089

0 hit on Virustotal
cc: @banthisguy9349 @tolisec @500mk500 @RacWatchin8872 @DaveLikesMalwre @NDA0E
urlhaus.abuse.ch/host/104.168.1…
#mirai
#elf
Indonesia

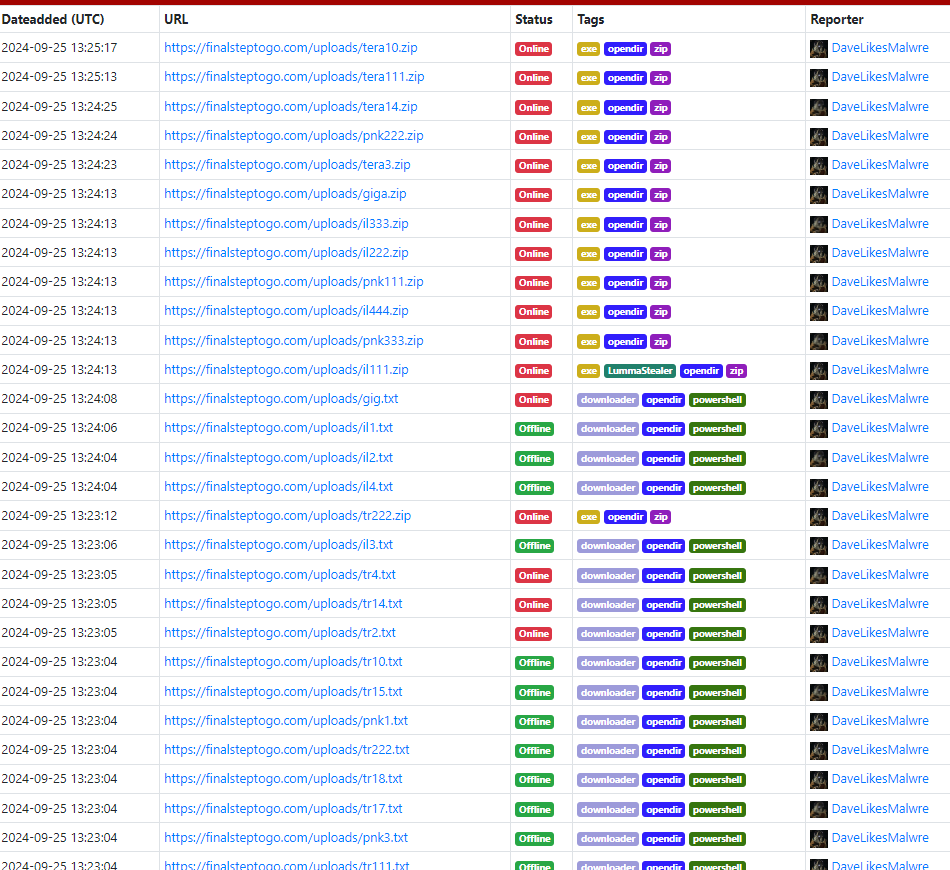
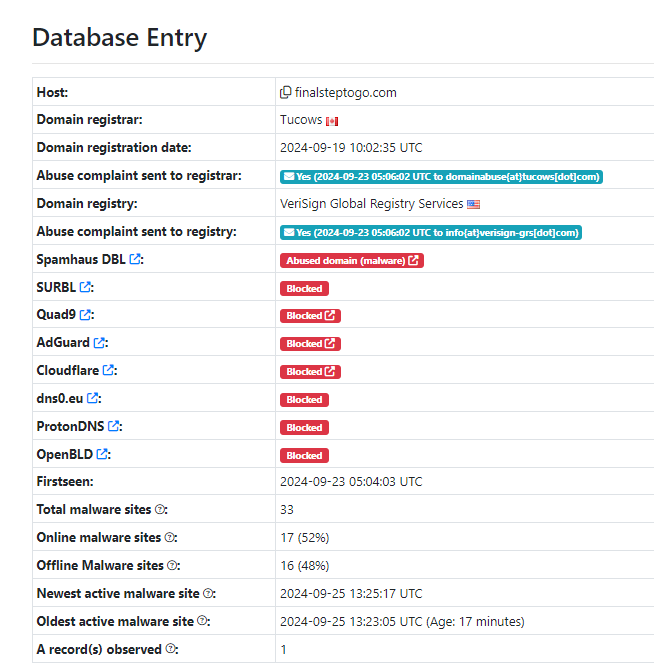
Well hello there LummaC....
🔗urlhaus.abuse.ch/host/finalstep…
A whole opendir of scripts and samples 😎
Saucy🌶️
English

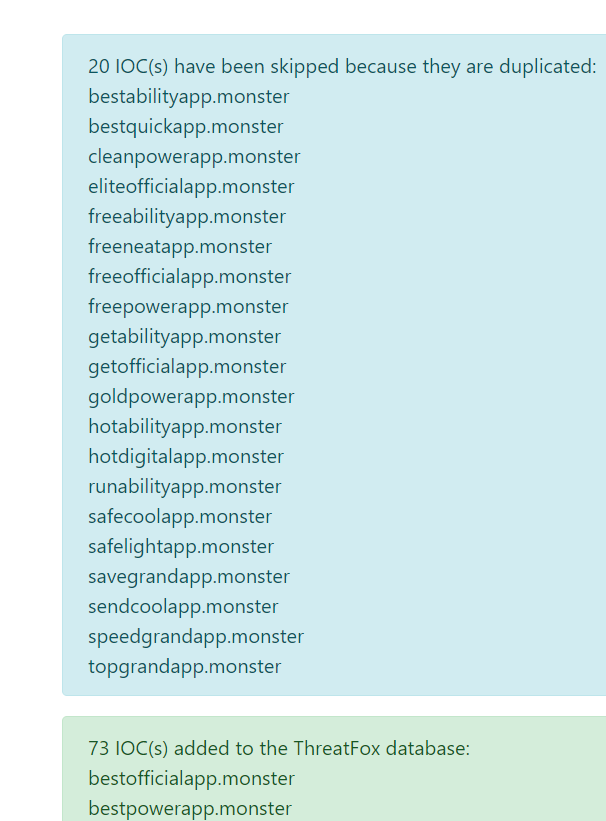
Mirroring what I was able to hunt on #RobotDropper from #Maltrail database to #Threatfox.
threatfox.abuse.ch/browse/tag/Rob…
English
NDA0E retweetledi

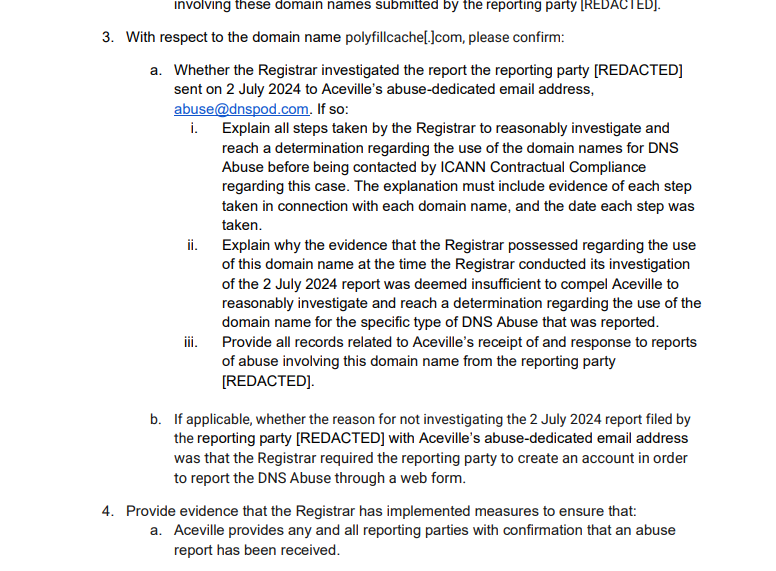
@mdmck10 @malwrhunterteam @DNSPod @ICANN Big news!
ICANN issued a Notice of Breach against @DNSPod in response to my complaint.
PDF: icann.org/uploads/compli…
CC: @banthisguy9349

English


