Chamindu Pushpika retweetledi

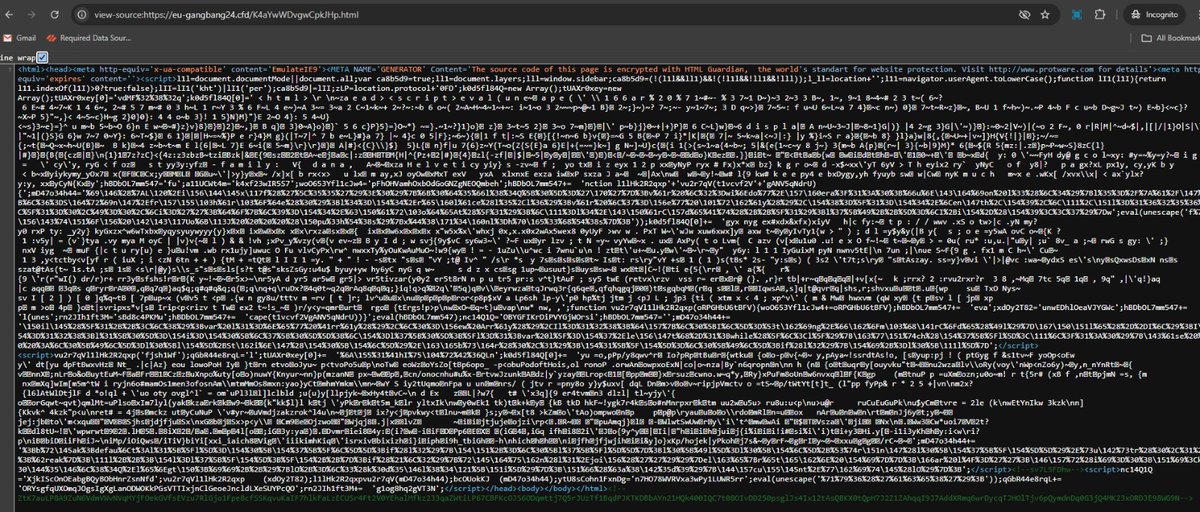
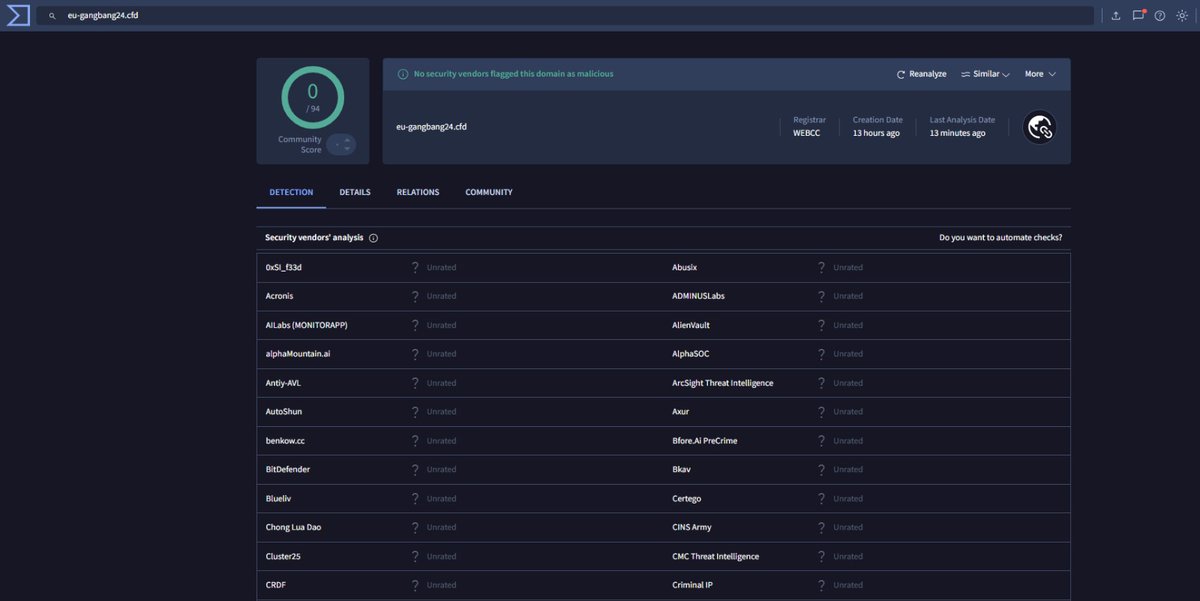
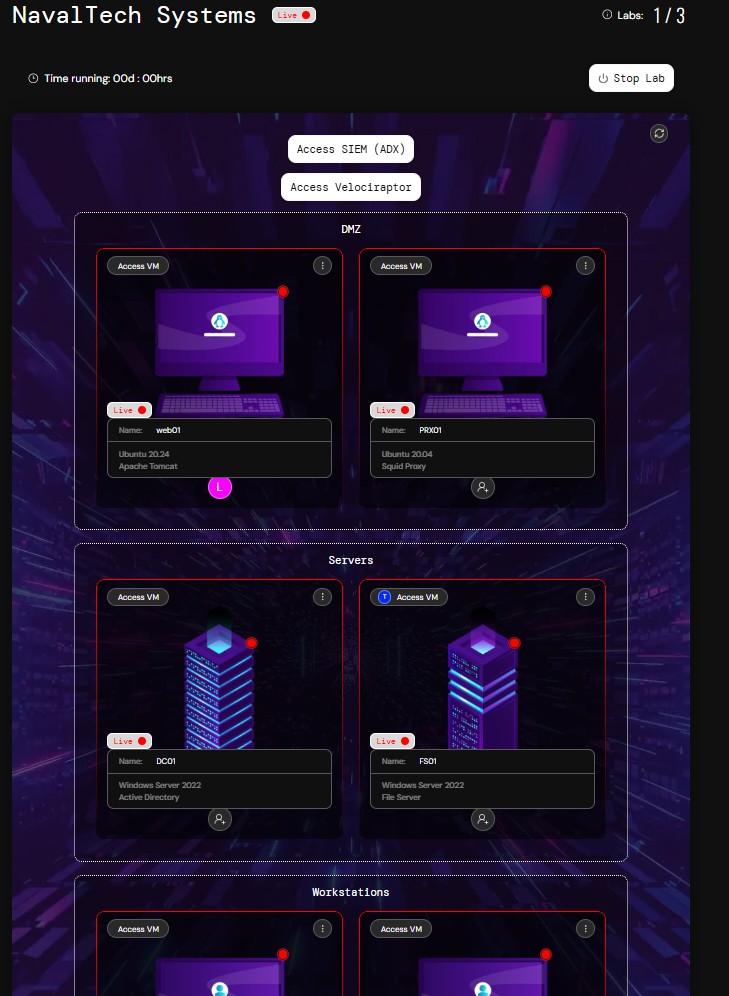
Hide the threat – GPO lateral movement
intrinsec.com/hide-the-threa…
English
Chamindu Pushpika
101 posts

@chamindu_x
Security Researcher | DFIR | CSEH








Researchers disclosed VoidLink, a modular Linux malware built for long-term, stealthy cloud access. It detects AWS, Azure, GCP, Docker, and Kubernetes, adapts its behavior, steals credentials, and enables lateral movement using rootkit-style techniques 🧩 🔗 Read here → thehackernews.com/2026/01/new-ad…