Nikhith
3.6K posts


Nikhith
@Nikhith_
Incident Response guy | Ex-Threat Hunter @Microsoft | Ex-Red Team @Mandiant | RCE || GTFO | 🪂 Paragliding P2 Pilot | 🤿 Scuba EXP30




WSL2 is a powerful attacker hideout because it runs as a separate Hyper-V VM, and defenders rarely monitor it. Daniel Mayer explains how attackers pivot into WSL2 and what it took to build tooling that works across WSL2 versions. Read more ⤵️ ghst.ly/45fPUma

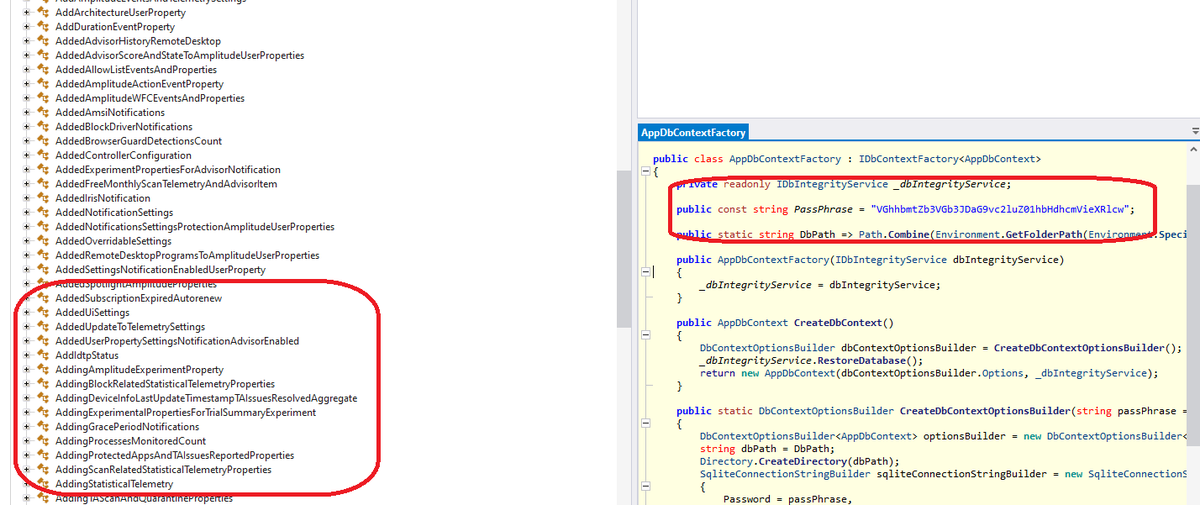
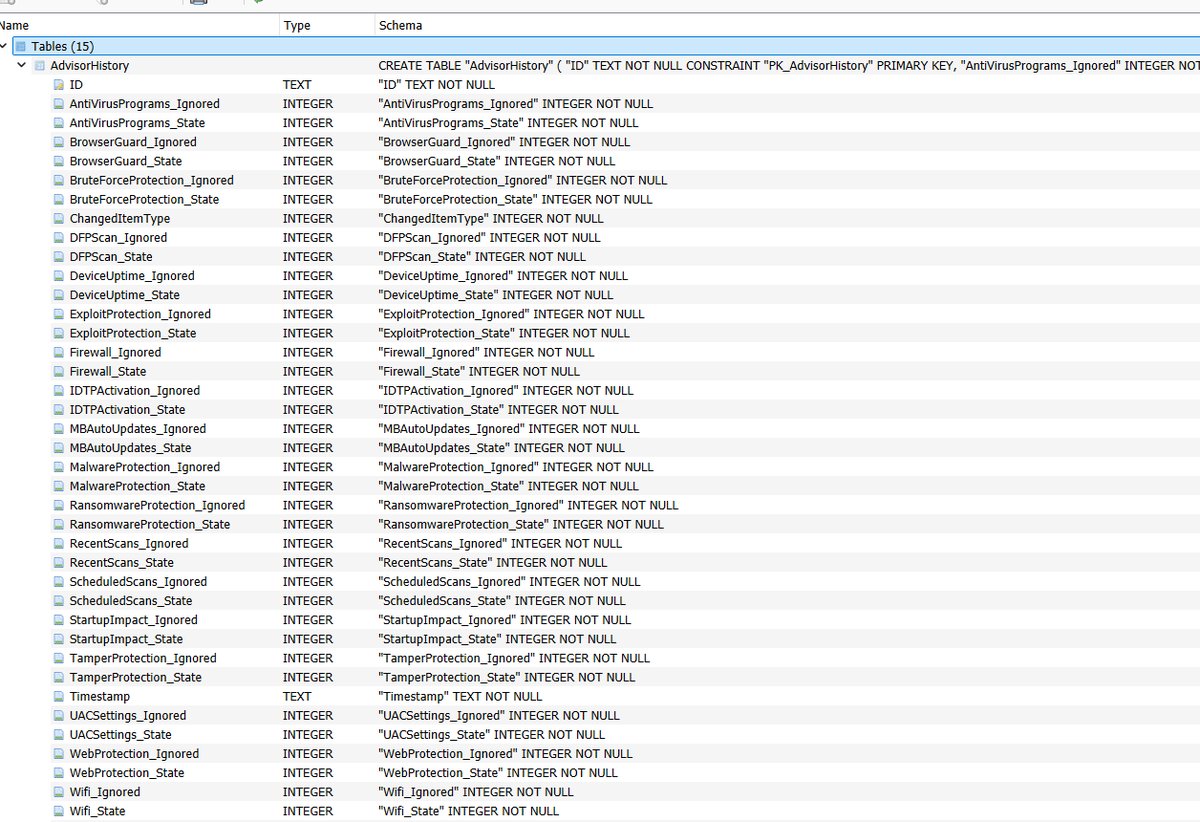
@vxunderground Explain this to me because I’m stupid



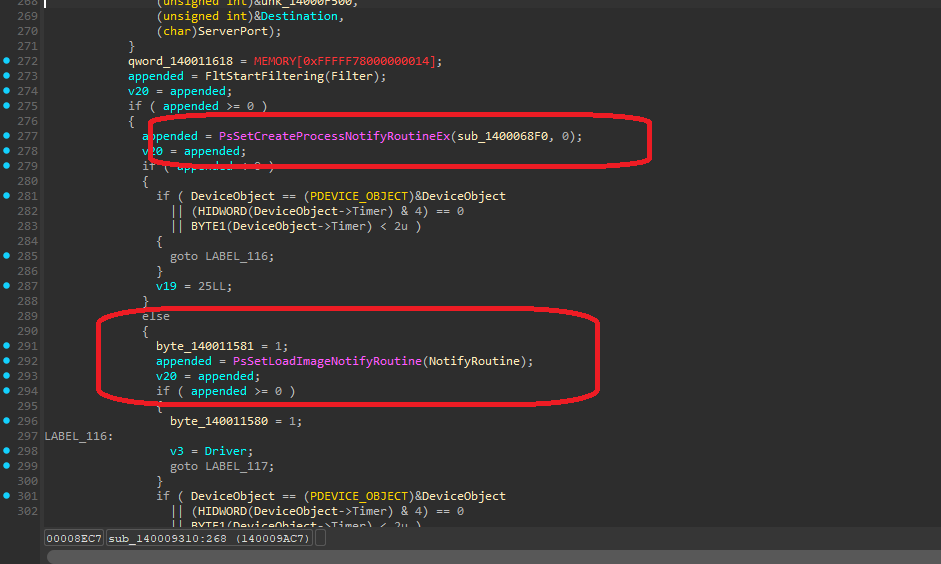
📢 EDR Silencing 📖 1x Playbook - A structured breakdown of the full approach 💡 6x Procedures - Practical, reproducible techniques mapped to real-world operator workflows 🚨 1x Sigma Rule - To help defenders spot this activity 💭 Would love your thoughts ipurple.team/2026/01/12/edr… #purpleteam #ipurple #redteam


NEW BLOG: The Great VM Escape 💕 We caught threat actors deploying a VMware ESXi exploit toolkit in the wild - potentially was a zero-day developed over a year before VMware's disclosure 👀 If anyone has thoughts on it let me know, but I needed almost a full case of beer to wrap my head around this one 🍺 Full technical breakdown 👇 huntress.com/blog/esxi-vm-e…




Releasing SILVERPICK, a Windows shellcode development framework using C/C++. github.com/winterknife/SI…