noah.eth
1.5K posts

noah.eth
@Noah_eth
researcher & dev | Head of Security at Monad Foundation @monad | Former Lead Security Researcher / Spearbit Core Team @SpearbitDAO.
Katılım Ocak 2010
1.5K Takip Edilen2.7K Takipçiler
noah.eth retweetledi

MIP-8 (Page-ified Storage State) has been drafted by researchers at @category_xyz .
This proposal makes storage page-aware.
The EVM has 32-byte slots, but hardware works in 4 KB pages. Reading one slot pulls in a whole page; once that is done, the true cost to read any other slots from that page is very small.
Under MIP-8, a 4096-byte (128 slot) page becomes the unit of access and commitment. Storage is grouped into pages, and each page is committed with a binary tree.
Under MIP-8, gas is priced accordingly. The first touch to a page is expensive. Once loaded, all slots in that page are warm. This makes contiguous layouts (arrays, structs) naturally cheaper, without any disruption to sparse layouts (mappings).
We believe that MIP-8 aligns gas costs more closely with true costs of state access. It incentivizes developers to choose storage patterns that utilize slots from the same page, and allows developers to build performant EVM apps that utilize state access efficiently.
English

Revoke Cash added immediate support for the Monad network with no questions asked except for which RPC we recommend
Ty for looking out for the ecosystem 🙏
Revoke.cash@RevokeCash
Big thank you to @monad for supporting Revoke with a grant. 🫡 Security infrastructure matters and grants like this help us continue developing free, open source tools that protect users across the ecosystem. We truly appreciate the support!
English
noah.eth retweetledi
noah.eth retweetledi

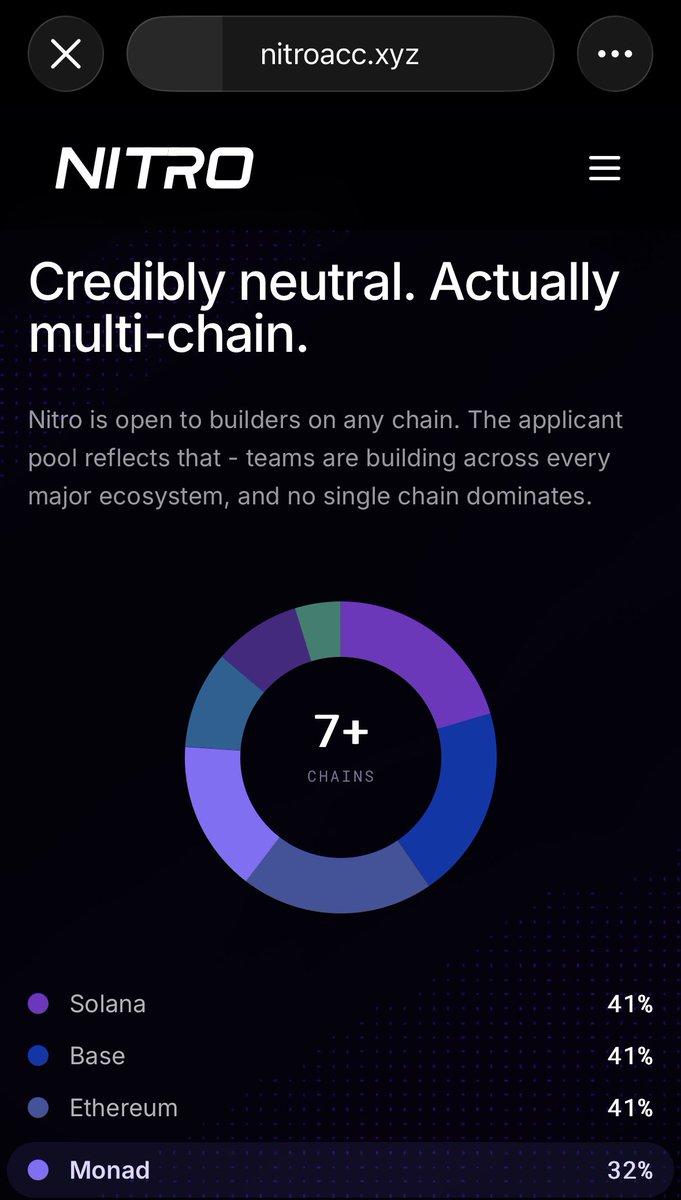
100% of founders, VCs, other chain people, other accelerator bosses are mindblown that we are supporting founders from all chains
for all the idealism, positive sum games are that rare in crypto
so is confidence that you can have teams build on a chain without bribing them with petty grants and listing promises
English
was able to import the account in metamask because the private key is stored in plain text

harpaljadeja.eth (evm/acc) 🇮🇳@harpaljadeja
Thanks for the $13!
English
noah.eth retweetledi

Today, the SDNY prosecutors filed a letter to Judge Failla requesting a retrial date. They want to go again in October. The prosecutors want to retry me on 2 counts the jury couldn't unanimously decide on. A jury of 12 Americans heard 4 weeks of evidence and deadlocked: no verdict on money laundering, and no verdict on sanctions violations. The government's response? Try again to make writing code a crime.
@realDonaldTrump declared the "War on Crypto is over." 🇺🇸
AG @DAGToddBlanche's memo: DOJ "is not a digital assets regulator" and won't target mixers for end-user acts. @USTreasury lifted Tornado Cash sanctions entirely. ✅ Also Treasury, March 2026: "Lawful users of digital assets may leverage mixers to enable financial privacy." — official report to Congress under the GENIUS Act. But the SDNY prosecutors — same country, same DOJ — just filed to retry me anyway. 🤔
⠀ The 2 counts = up to 40 years in federal prison. ⛓️ For writing open-source code. For a protocol I don't control. For transactions I never touched. A jury already couldn't agree this was criminal. But the SDNY prosecutors want to keep trying with the hope of getting a different answer.
⠀ I have a daughter. I have a life in Seattle. I will never stop fighting for freedom. ❤️ But I need to be honest with you: Four weeks of trial. A hung jury. Now they want to do it all over again in October. I have basically exhausted my legal defense funds. And I'm staring down another full federal trial. 😔 Every dollar raised goes directly to keeping this fight alive — attorneys, experts, the full defense apparatus it takes to stand up to the SDNY prosecutors. This isn't abstract. If I can't fund a defense, they win by default. If you care about financial privacy, if you write code and believe that code is speech — this is the moment. 💻🔐 👇

English
noah.eth retweetledi

After many tests around LLM use in bug hunting, and taking into consideration all my experiences/study in AI in the past few months I arrived at some conclusions. And I'll make some predictions:
1. Every new model will be followed by a wave of new bug findings in a short time that will get people very excited. Followed by a period of very few findings.
2. Those waves will get smaller and smaller, until basically there's no improvement.
3. The reason isn't that the code is becoming bug free -- it's because the % of bugs that **can be found** by LLMs is quite small.
Why?
1. The model has no idea how the code works -- you can catch it making ridiculous statements about the code all the time.
2. It has no idea how the EVM works either -- it misrepresents basic facts about the EVM all the time.
3. The way it finds bugs is basically hallucinating credible-sounding exploits. If there is a bug and it is typical enough, sometimes the hallucination matches reality.
4. Even very easy, very typical bugs, can be missed if slightly obscured.
5. Matching the actual threat model is hard so the severity is basically a random guess most of the time.
6. You can improve all of the above in two ways:
6.a. Make extensive prompts/skills telling exactly what it should look for. You just turned the supposedly generic auditor into a (very expensive and slow) static analyzer!
6.b. Force it to PoC and retry repeatedly, enforcing success conditions. This turns it into a (very expensive and slow) fuzzer!
You can combine both for better results.
7. It's useful but it is still just a static analyzer + fuzzer. An incremental expansion on the existing state of the art tooling. When you don't know what tools to use or dont have time to find out, they will be very useful -- and that's maybe a lot of value -- but it doesn't change the nature of what's going on.
8. People telling you it's doing what an auditor does, replaces humans, yadda yadda yadda -- they are either clueless, deluded, or deliberately misleading.
9. BTW humans hunting for bugs don't just try to look for known bug patterns -- the known bug patterns are compiled from findings by humans **who actually understood how the code works** and found the bug without anyone telling them what they should be looking for. That's the "research" part in Security Researcher.
10. Most of the known patterns were discovered independently by multiple SRs sometimes years before becoming public knowledge. Sometimes it becomes public knowledge after a black hat discovers it and steals millions (you probably dont want to be the target of that research!)
11. Any human or machine that keeps just trying to match known patterns against code bases will miss **A LOT** of bugs.
12. Finding bugs is crazy hard. Writing bug-free code is even harder. There is no silver bullet. AI isn't magical. Nor is it "automating human cognition".
13. Life is always unfair. More so in a bear market.
14. If you think someone will hand you on X a solution so you can find bugs easily OR so you don't have to spend a lot of effort/money on securing your code...
We'll things are not gonna work great for you.
English

@lonelysloth_sec Interesting!!
I had seen @banteg tweet about using GPT Pro in the UI with a zip of the repo to generate better findings.
Might be another avenue to test out. It was offering different findings than Claude and codex over the cli alone
English

Finally after trying several times, stripping comments and other small tweaks -- it found it!
But then I inspected the skill use and realized that it "found it" by running a git diff and figuring out I changed the contract to introduce a bug!!!!
It means that even when it could run a diff and find exactly the line that introduced the bug it didn't find the bug or misunderstood its severity and exploitability.
To *convice Claude* it was a viable exploit, I had to keep pointing it to the right place and asking it the right questions.
So basically can only *rationalize* finding the bug, but not find it by itself.
English

I was starting to get hopeful about using Claude in some capacity in my work.
Then I did a test introducing a very definitely critical vulnerability, somewhat atypical, but obvious, in a target that I spent days without finding any bug.
. It was a direct contradiction of the comment that explained the line of code. It screamed bug.
First try it didn’t find it.
Asked it to double check. It kinda found it but convinced itself it was by design and safe.
I introduced a second vuln a couple lines from the first.
After many iterations with me trying to nudge it, it finally found it.
I asked the severity.
Info — then gave me a long list of reasons that misstated fundamental facts about Solidity and Ethereum.
That’s the story of my use of those things.
I spend more time explaining things to it than getting answers. And the answers I get I can’t trust.
All things considered it slows me down considerably.
I’ll wait for the next model.
English
noah.eth retweetledi

I’m happy to share that I’ve joined the security team at @monad Monad Foundation!
I’ve been really impressed by the team, their technical depth, and their ability to execute, and am excited to contribute to making the ecosystem more secure.
English

@socialforging I use both and the older one has more scratches on the screen
English
noah.eth retweetledi

TESTNET RELEASE - v.0.13.0 (MONAD_NINE Hard fork)
A new release is available for all nodes on Testnet.
Instructions available here > docs.monad.xyz/node-ops/upgra…
Full changelog available here > #v0130-monad_nine" target="_blank" rel="nofollow noopener">docs.monad.xyz/developer-esse…
This version results in a hard fork Tuesday 10th 14:30 GMT (2026-03-10 14:30GMT)
This release also enacts:
MIP3: Linear EVM Memory Cost
github.com/monad-crypto/M…
MIP4: Reserve Balance Introspection
github.com/monad-crypto/M…
MIP5: Fusaka EIP activation
github.com/monad-crypto/M…
English