Sabitlenmiş Tweet

I’m happy to share that I’ve joined the security team at @monad Monad Foundation!
I’ve been really impressed by the team, their technical depth, and their ability to execute, and am excited to contribute to making the ecosystem more secure.
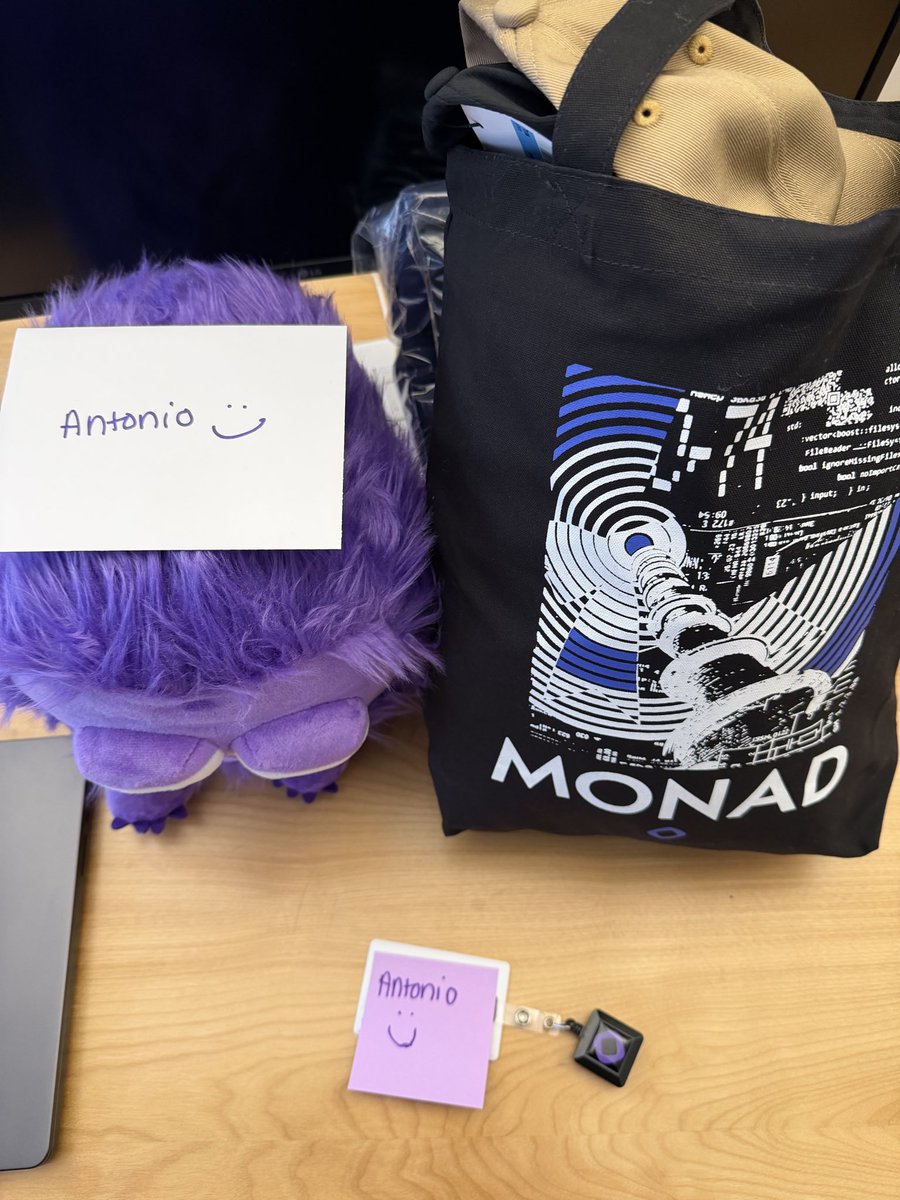
English