Nomu Entertainment
9K posts


Nomu Entertainment
@NomuMaster
A rare blend of creative, chaos, and calculated control. #Author #ITProjectManager #Cosplayer #CollabManager NFA (U R Responsible 4 UR own choices)
Richmond Katılım Mart 2012
2.7K Takip Edilen3.8K Takipçiler
Nomu Entertainment retweetledi

It's time for another #giveaway!
To celebrate the release we're giving away one free Pokémon Chaos Rising Booster Box! Simply follow the steps in the link below to enter! The giveaway will be open until Friday May 22nd, so good luck everyone! #pokemontcg
flipsidegaming.com/blogs/giveaway…
English

Inside the #ShinyHunters #Canvas #Breach: How One Hack Reached 9,000 Schools:
In the first week of May 2026, the global education sector found itself caught in what may be the largest student data breach in history. The criminal extortion group ShinyHunters claimed it had stolen 3.65 terabytes of data covering roughly 275 million students, teachers, and staff across nearly 9,000 institutions. By the end of the week, school login pages were being defaced with ransom notes, Canvas had gone dark for thousands of users, and the hackers had pushed their deadline forward twice in an apparent bid to force a payout.
Who is ShinyHunters:
Despite the singular name, ShinyHunters is not a person. It is a criminal extortion crew that has operated since 2019, building a portfolio of high-profile data thefts that reads like a tour of the modern internet. The group has been linked to breaches at Ticketmaster, where roughly 560 million records were exposed, and AT&T, which reportedly paid a $370,000 ransom to have stolen data deleted. In March 2026, the group leaked 350 gigabytes of data taken from the European Commission. Their signature move is consistent: identify a vendor or platform sitting on a mountain of valuable data, get inside, exfiltrate everything they can, and demand payment under threat of public release.
The Target Was a Vendor, Not the Schools:
The most important fact about this incident is that no individual school was hacked. The target was Instructure, the Utah-based company that makes Canvas, the learning management system used by roughly 41 percent of higher education institutions in North America and by K-12 districts around the world. Canvas is where students submit assignments, where professors post grades, and where billions of private messages flow between teachers and learners.
Instructure first detected the intrusion on the evening of May 1. By May 2 the company said the incident had been "contained." But containment did not mean the data was safe. The attackers had already gotten what they came for, and they were preparing to make their leverage public.
The Public Reveal:
On May 3, ShinyHunters posted on a dark web forum claiming responsibility. They said the breach affected up to 275 million individuals across nearly 9,000 institutions, and they backed it up by dropping a list of 8,809 schools, school districts, and online education platforms with per-institution record counts. The geographic spread was striking: most victims are in the United States, followed by Australia, the United Kingdom, and Sweden, with institutions in at least ten countries on the list.
The list itself produced some genuinely surprising names. All eight Ivy League universities appear, along with MIT, Oxford, Harvard, Duke, Penn, the University of Missouri system, and Duke. Stranger still, Amazon, Apple, and Cisco show up almost certainly because those companies use Canvas internally for employee training, a reminder that "education technology" is not just for schools anymore.
What Was Actually Stolen:
Instructure has confirmed that the compromised data includes names, email addresses, student ID numbers, and messages exchanged between users on the platform. The company maintains, based on its investigation so far, that there is no evidence passwords, dates of birth, government identifiers, or financial information were taken.
ShinyHunters tells a somewhat broader story. The group claims to possess several billion private messages between students and teachers personal conversations that, in many cases, were never meant for any audience beyond two people. They also claim to have breached Instructure's Salesforce instance, which would expand the scope further. A sample of stolen data shared with reporters included names, email addresses, and some phone numbers from a pair of US schools, which is consistent with both the company's account and the hackers' own claims.
The technical method has not been fully disclosed, but the attack appears to have exploited a vulnerability in Instructure's cloud environment and used legitimate API tools and custom scripts to extract data at scale, rather than deploying ransomware in the traditional sense. This is increasingly the ShinyHunters pattern: quiet exfiltration, loud extortion.
The Deadlines Keep Moving:
The ransom timeline has been a moving target. The original deadline was May 6. When that passed without payment, ShinyHunters extended it to May 8. As pressure failed to produce a settlement, the group pushed the threatened release date out again, to May 12, telling reporters they would publish unless Instructure agreed to "negotiate a settlement." According to a spokesperson for the group, Instructure has not engaged in direct communication.
That extension does not mean the heat is off. If anything, the opposite is true.
Escalation: Defacing the Schools Themselves
On May 7, the situation took a dramatic turn. Students at the University of Oklahoma, the University of Missouri system, and schools in North Carolina who tried to log in to Canvas were greeted with a hostile message from ShinyHunters threatening release of their data. The message demanded Instructure respond by the end of the day on Tuesday. The same day, Canvas itself buckled under the pressure, with Downdetector tracking roughly 10,000 user reports of the platform being inaccessible by mid-afternoon Pacific time.
This is a notable shift in tactics. Rather than waiting passively for a ransom to be paid, the hackers are now reaching past Instructure to confront the company's customers directly and, by extension, the millions of students and parents those customers serve. By making the breach impossible to ignore at the user level, the group is trying to convert public anxiety into corporate willingness to pay.
What Has and Has Not Been Published:
It is worth being precise about what is actually out in the open. ShinyHunters has published the list of affected institutions, which is how universities and journalists have been able to identify victims. The group has shared small data samples with reporters at TechCrunch and others to substantiate their claims. But the full trove the 3.65 terabytes, the 275 million records, the billions of private messages has not been released. That data remains the leverage. May 12 is the latest threatened release date, and whether that deadline holds will depend on whether Instructure or the schools blink.
The Bigger Pattern:
The Instructure breach is not an isolated incident. It is part of a clear pattern of criminal groups moving up the supply chain in the education sector. PowerSchool, which provides administrative software to K-12 schools, was breached in December 2024 and reportedly paid $2.85 million in ransom. ShinyHunters has separately hit Infinite Campus, McGraw Hill, and Salesforce in recent months. Each of these incidents represents a single intrusion that touches thousands of downstream institutions.
The logic for attackers is brutally efficient. Attacking a hundred school districts one at a time is slow and expensive. Attacking the vendor that all hundred districts depend on is a single job that pays out at scale. The education sector which collects sensitive data on minors, holds private academic communications, and historically underinvests in security relative to its data value has become the target of choice for this kind of supply-chain compromise.
What This Means for the Average Person:
For students, parents, and educators caught up in this breach, the immediate financial risk is relatively contained. Without passwords or financial data in the dump, no one is about to drain a bank account using the stolen records alone.
The real risk is phishing, and it is significant. With real names, real school email addresses, real course enrollments, and in many cases real prior conversations between specific teachers and specific students, attackers can craft messages that are far more convincing than the generic spam most people are used to filtering out. An email that references the actual class you are taking, names your actual professor, and continues a conversation thread that actually happened is dramatically harder to spot as fraudulent.
The practical advice from security researchers is consistent: change Canvas passwords (especially if reused elsewhere), be skeptical of any message claiming to be from your school or Instructure that asks you to verify credentials or click unfamiliar links, and when in doubt, navigate to the official site directly rather than clicking anything in an inbound message.
The Open Question:
Whether Instructure pays, whether ShinyHunters follows through on May 12, and whether the full dataset ends up on the open internet are all still unresolved. What is no longer in question is that the playbook works. As long as a single vendor compromise can produce 275 million records of leverage, attackers will keep climbing the supply chain, and the schools at the top of that chain will keep finding themselves on lists they never wanted to be on.
English
Nomu Entertainment retweetledi
Nomu Entertainment retweetledi

48 HOUR GIVEAWAY
1x Poncho Pikachu Slab Pack
Top Chase:
$13,000 2015 Pokemon Japanese XY PSA Gem Mt 10 PRTD Gyrados Pikachu Promo
💙LIKE & follow @dripshop_live
🔁RETWEET
✍️TAG A POKEMON COLLECTOR

English
Nomu Entertainment retweetledi

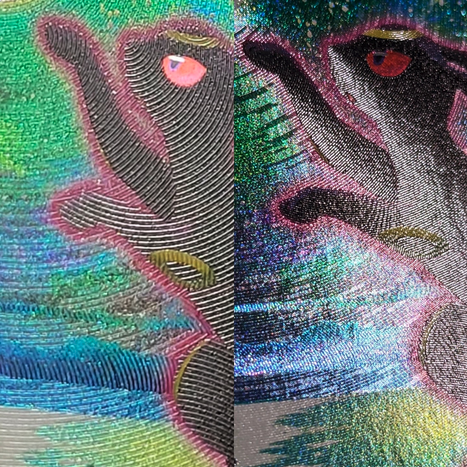
el arte es de Bryce Kho
cuentas que se dedican a subir fanarts como cartas Pokémon sin dar créditos a los artistas dais MUUUCHA pereza


Nortier@Nortier
This Ho-Oh concept goes hard, spot the details.
Español
Nomu Entertainment retweetledi
Nomu Entertainment retweetledi

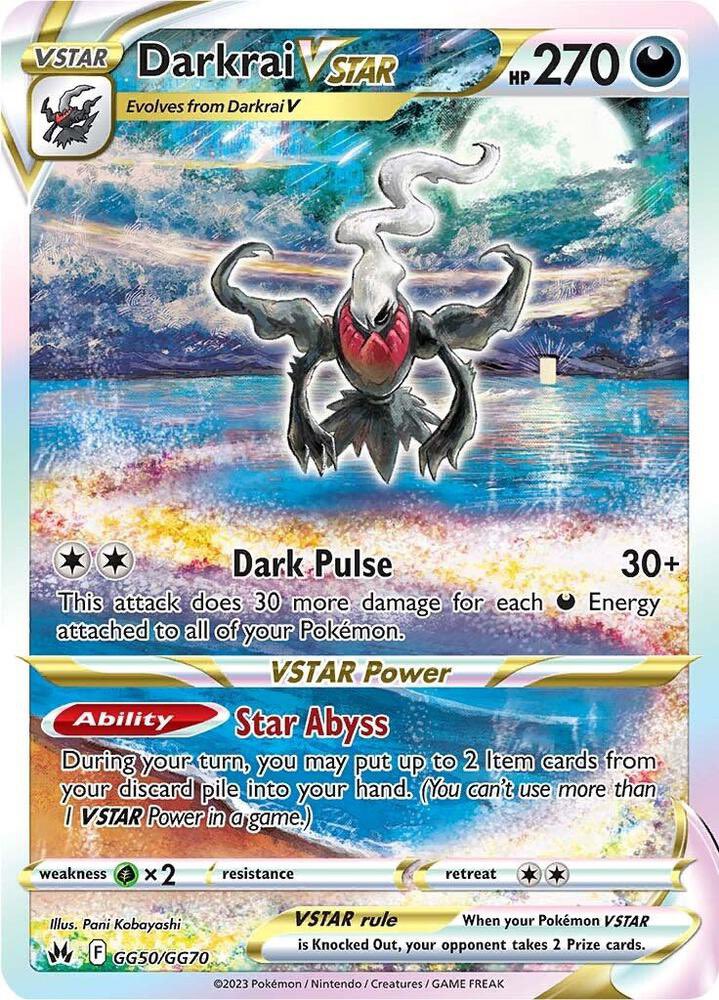
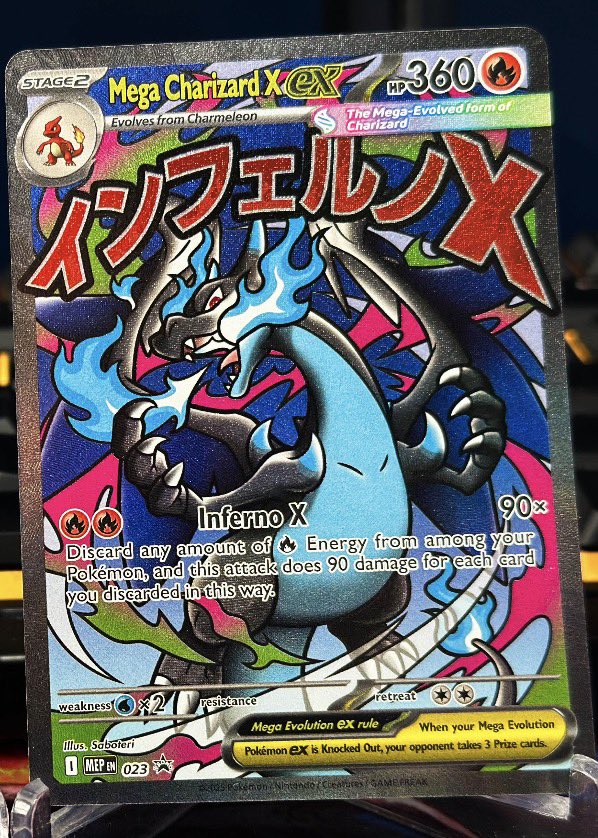
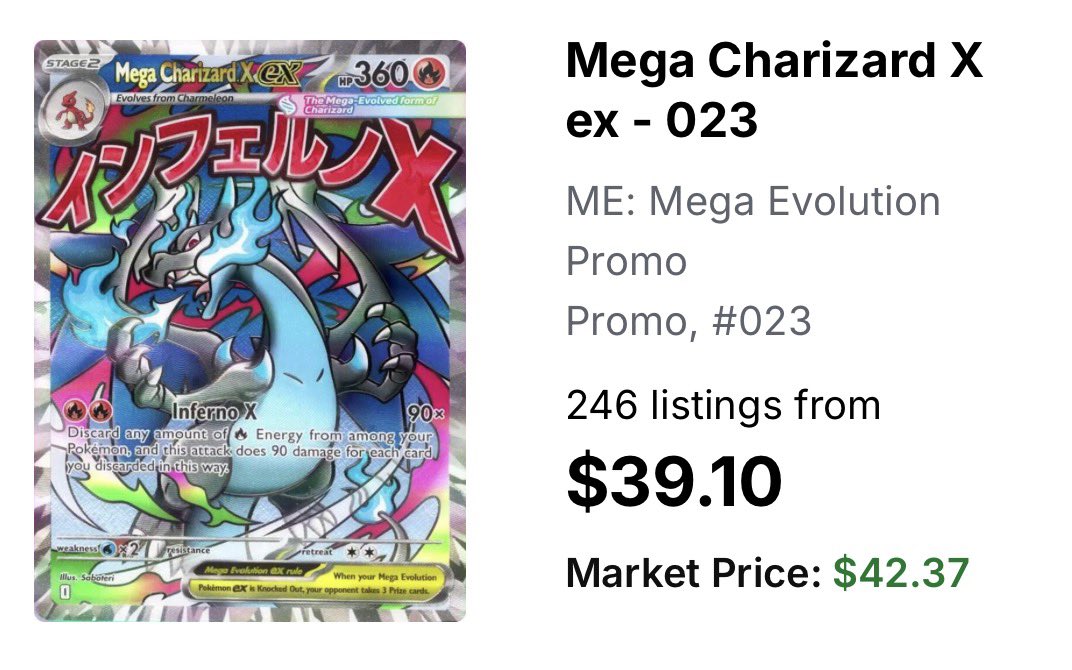
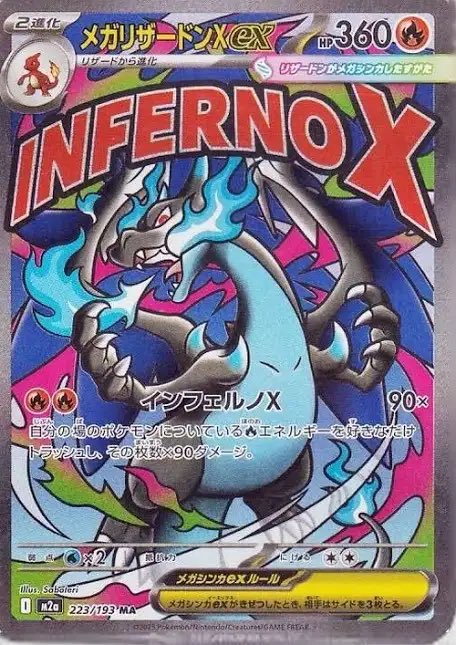
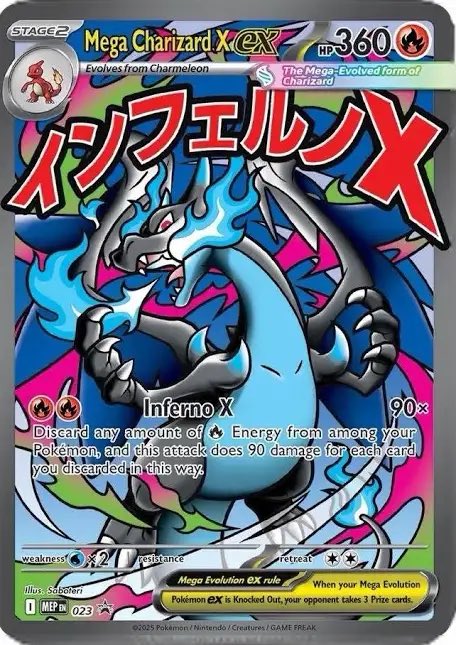
@HyperbeamTCG I just pulled all of mine out to sell this weekend 🤣
English

@HyperbeamTCG They did this a long time ago on older sets nothing new. I think they are dope though.
English

Upon Further Evidence, The Dude Who Got His Ass Beat By Alan Ritchson 100% Deserved To Get The Crap Kicked Out Of Him s.barstool.link/c/article-3565…

English

NEW: The neighbor who was allegedly punched by actor Alan Ritchson, explains to TMZ how the incident started, says he told the actor to "slow it down."
"I did push him because he was coming towards me on his, on his bike."
"He did it again for a second time. I pushed him a second time, and I think the second time he got off his bike and kicked the crap outta me."
Video: @TMZ
English

that cam footage is gonna save #AlanRitchson millions. What kind of ..Karen...Darren? Jumps in front of a bike and tries to start a fight?
Skint Eastwood@Skint_Eastwood1
🚨NEW FULL FOOTAGE of Alan Ritchson (Reacher) in a street fight with his neighbor Ronnie Taylor in Tennessee. It captures exactly what caused Ritchson to snap and beat the crap out of Taylor.
English

💌 COLLECTR x TAG GIVEAWAY ✨
03.22.26 - 03.29.26 / STATUS: OPEN
Win this TAG 10 GEM MINT Special Delivery Charizard 🔥⚡️
How to enter:
1️⃣ Follow @getcollectrapp and @taggrading
2️⃣ Tag 3 friends
3️⃣ Repost this post
⭐️ BONUS: Multiply your entries by sharing across multiple platforms!
Winner revealed next Sunday March 29.
#Pokemon #Charizard #SpecialDeliveryCharizard

English