pdzeng | 熊貓
7.4K posts


pdzeng | 熊貓
@PandaZeng1
prev @_WOO_X @tonx_studio





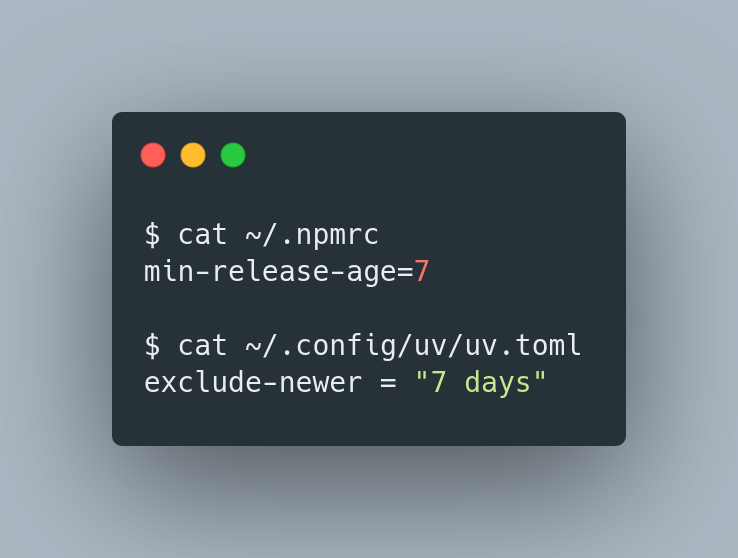
建议给你的 Agents(包括 OpenClaw)都投喂如下提示词,好好排查下是否存在这波 axios 被投毒事件影响: 参考下面这个方法排查一遍我们的环境是否存在被投毒的 axios@1.14.1 与 axios@0.30.4,及恶意模块 plain-crypto-js,不能漏,确保排查全面: Check for the malicious axios versions in your project: npm list axios 2>/dev/null | grep -E "1\.14\.1|0\.30\.4" grep -A1 '"axios"' package-lock.json | grep -E "1\.14\.1|0\.30\.4" Check for plain-crypto-js in node_modules: ls node_modules/plain-crypto-js 2>/dev/null && echo "POTENTIALLY AFFECTED" If setup.js already ran, package.jsoninside this directory will have been replaced with a clean stub. The presence of the directory is sufficient evidence the dropper executed. Check for RAT artifacts on affected systems: # macOS ls -la /Library/Caches/com.apple.act.mond 2>/dev/null && echo "COMPROMISED" # Linux ls -la /tmp/ld.py 2>/dev/null && echo "COMPROMISED" "COMPROMISED" # Windows (cmd.exe) dir "%PROGRAMDATA%\wt.exe" 2>nul && echo COMPROMISED

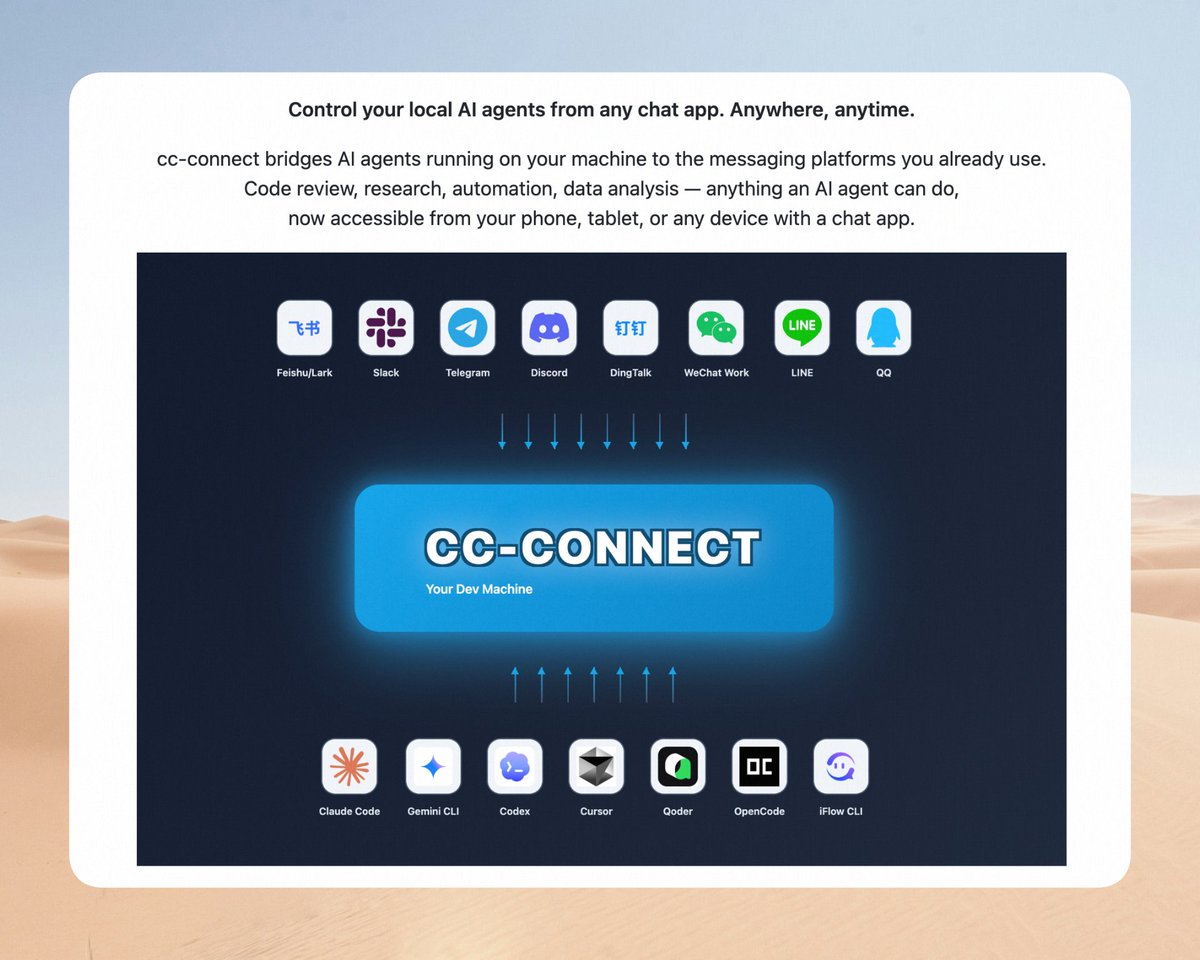
如果不需要“OpenClaw 极简安全实践指南”,直接给你的 OpenClaw 说卸载就行,如果你希望只留红线黄线有关的保护机制,注明好这个要求就行。 顺便说下 SlowMist Agent Security Skill 内部已经在使用,在安全检测方面会更强大。这个和我们之前发布的“OpenClaw 极简安全实践指南”不冲突,你可以理解为是事前安全部分的增强。 增强的专门搞个 Skill 就很合适。 附: OpenClaw 极简安全实践指南: github.com/slowmist/openc… SlowMist Agent Security Skill:等待发布