spex
416 posts


spex
@RRSkunkWorks
Director & Founder. Technical Lead of RRS.W ⌐■.■ rfnerd~life.Hz~CTFs, threat hunting, weird rf mysteries. once a phreak, always a freak, amirite?












Someone created a fully operational JOHNNY 5 from scratch and omg how cool 🙌 (instagram Saundersmachineworks)


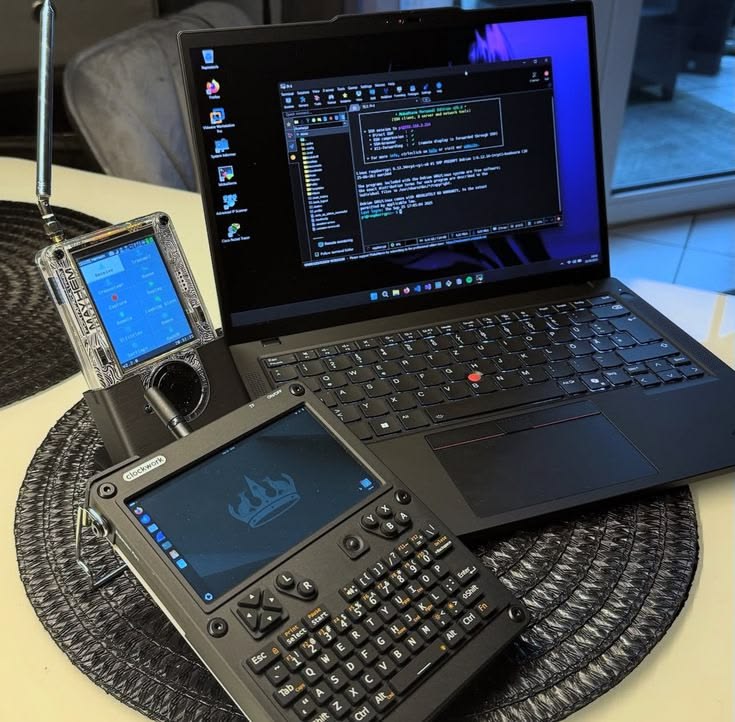
I ran Claude Code on a Nintendo Switch! Here's how. The original 2017 Switch has an unpatchable hardware exploit (Fusée Gelée) that allows you to boot into Recovery Mode by shorting two pins in the Joy-Con rail. I used a folded piece of aluminum foil instead of a commercial RCM jig (because I didn’t want to wait for Amazon delivery, haha). From there: • Injected @CTCaer Hekate bootloader payload via a browser-based tool • Partitioned the SD card and installed @switchroot_org's L4T Ubuntu Noble 24.04 • Installed @claudeai Code using the native Linux installer • Ran it successfully from the terminal on the Switch's Tegra X1 chip The entire process is non-destructive if you copy everything from the Switch’s SD card and save it. The Switch's internal storage is never touched because everything lives on the SD card. To restore, you just reformat the card and copy your original files back. Fun little experiment!

A company that sells cybersecurity risk intelligence to 91% of Fortune 100 companies just got breached through an unpatched React app and a single overprivileged AWS role. LexisNexis. 3.9 million records. 400,000 user profiles. 53 secrets extracted in plaintext from AWS Secrets Manager. Including credentials for production databases, Salesforce, Oracle, and analytics platforms. The password "Lexis1234" was reused across five different internal systems. This is a company that describes itself as "one of the largest protectors of private and confidential data in the world." They provide risk intelligence to 7,500 US government agencies, nine out of ten banks, and major insurers globally. They sell cybersecurity assessments to their customers. And they couldn't secure their own AWS account. Here's what makes this worse than a typical breach: - The compromised data includes accounts tied to 118 .gov email domains. Three US federal judges. Four Department of Justice attorneys. SEC staff. Probation officers. Federal court law clerks. The attackers published doxxed profiles of federal officials tied to courts and regulatory agencies across the country. - These aren't random consumer records. These are the digital identities of people whose exposure carries national security implications. A compromised federal judge's profile doesn't just enable identity theft - it enables targeted influence operations, blackmail, and intelligence gathering. The attack path is textbook and that's the problem: → Unpatched React application - the front door → Single ECS task role with read access to every secret in the account - the keys to everything → 536 Redshift tables, 430+ database tables, full VPC infrastructure mapping - complete visibility → 53 secrets in plaintext including database credentials, API tokens, and development access keys No zero-day. No advanced persistent threat. No nation-state capability required. Basic hygiene failures — unpatched app, overprivileged IAM role, password reuse, plaintext secrets. This is LexisNexis's second confirmed breach in two years. The December 2024 incident exposed 364,000 individuals through a compromised corporate account on a third-party development platform. Data brokers and analytics providers are not peripheral players - they're deeply embedded in today's risk landscape. That's the pattern we keep seeing. Attack the aggregator, not the individual. BPO providers. Cloud platforms. Legal data giants. The organisations that hold everyone else's data are the highest-value targets - and often the weakest links. For every enterprise that uses LexisNexis services: → Assume your metadata, contract details, and product usage history are exposed → Watch for targeted phishing using the exposed business relationship data → If your staff have LexisNexis accounts, reset credentials immediately → Ask your vendor risk team: when was the last time we assessed LexisNexis's actual security posture - not their marketing, their controls? The company that indexes the world's legal information couldn't index its own IAM policies. And they're not the exception. They're the pattern. More info: cybernews.com/security/lexis…


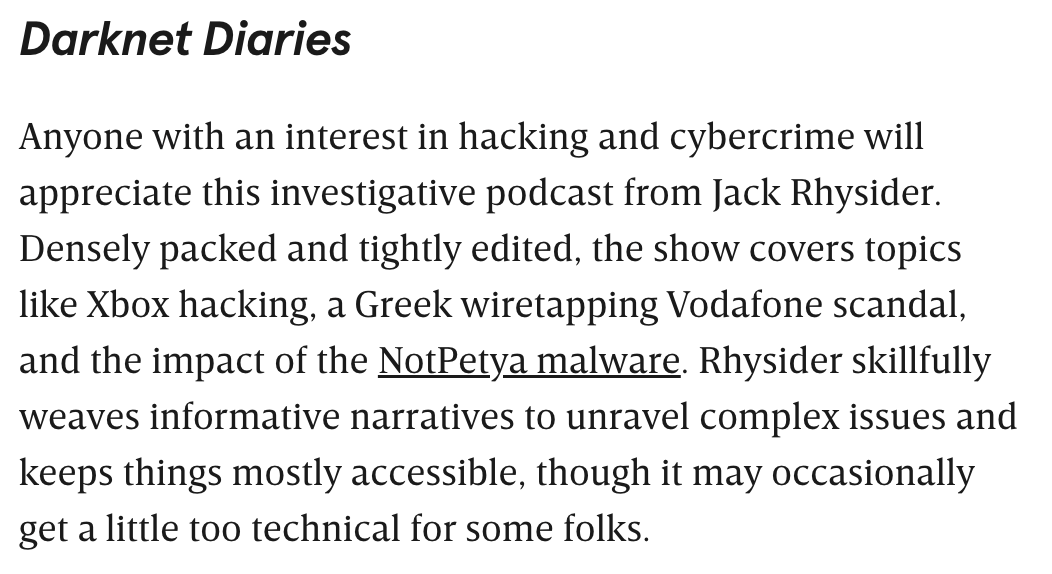
Get your fix of tech, true crime, pop culture, or comedy with these audio adventures. wired.com/story/best-pod…


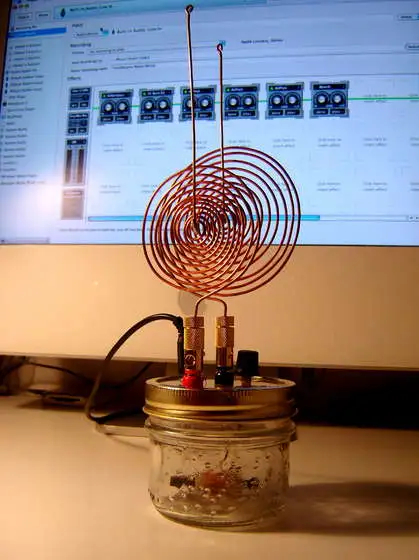
Nikola Tesla being the greatest RF engineer in history and a batshit insane mystic are not two separate facts. They are the same fact.