Pawel Rzepa
1.1K posts


Pawel Rzepa
@Rzepsky
Yet another sec guy, particularly interested in cloud security 🌩️ AWS Authorized Instructor at @awscloud Lead Ethical Hacker at @SoftServeInc






Authoring SCPs? Now policy validation with IAM Access Analyzer guides you along the way 🛣️ Check it out in the AWS Organizations console!








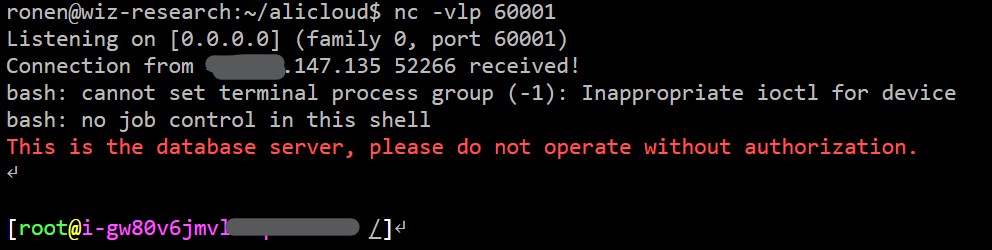
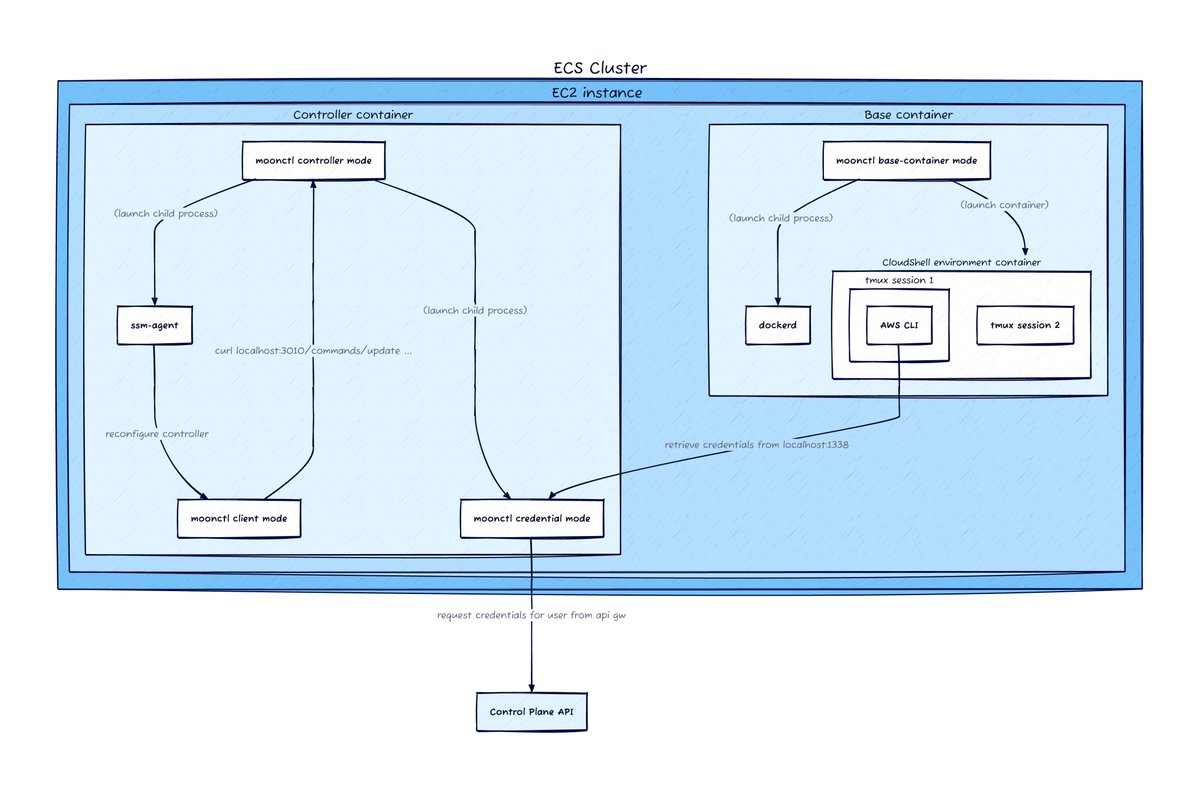
⚔ Sysdig TRT just uncovered a nasty cloud attack. SCARLETEEL began with a compromised container & ended with privilege escalation into an #AWS account to steal proprietary software. Read more on the attack & takeaways to help you stay safe in the cloud: okt.to/drzW5y







AWS announces changes to AWS Billing, Cost Management, and Account consoles permissions AWS announces the retirement of IAM actions for AWS Billing, Cost Management, and Account consoles under aws-portal service prefix, purchase-orders:ViewPurchase... aws.amazon.com/about-aws/what…