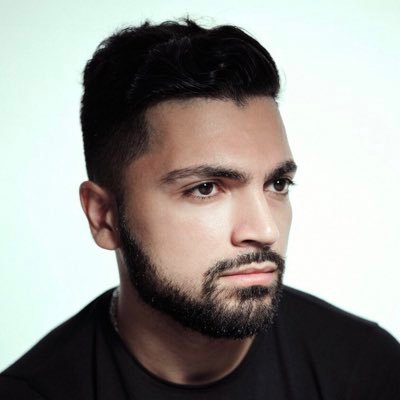
sam.frax
5.4K posts
sam.frax
@samkazemian
¤ Founder CEO @FraxFinance 💸 $FRAX ¤ 🇺🇸 Cofounder @IQAICOM $IQ 🤖 neuroscience & philosophy @ucla

Heeaaaaaaaaated debate broke out in the ETHSecurity Community Telegram earlier today between LayerZero’s Bryan and security researchers. TLDR summary: - $3 billion+ of LZ OFTs were recently at risk of being compromised due to a default library contract that LZ Labs could upgrade instantly with no timelock to forge messages (like what happened with rsETH hack) -According to Banteg, major projects like Ethena and EtherFi were STILL using this default library contract as of a few weeks ago - There is still $178 million in value exposed to being compromised from projects using default library (look at quote tweet) - LZ Labs doesn’t need to be malicious for this be risk, they have history of poor opsec (in addition to being hacked by North Korea): - Onchain data shows LZ Labs multisig signers were engaging in non-multisig signing activity like trading memecoins, swapping on DEX, bridging. All major phishing risks as this mean production multisig keys were connected to websites, not just used for signing - LZ Labs handled private keys like a high schooler, trading memecoins on production multisig keys, no wonder they got targeted by North Korea, who knows what other poor opsec they have? THREAD BELOW

The power of Mythos! Firefox identified and fixed more security bugs in one month vs. the past 15 months combined hacks.mozilla.org/2026/05/behind…


Stablecoins are actually super cypherpunk. CT has broken your brain on this. The idea that anyone at any time, with just a mobile phone, can hold and send dollars instaneously to anyone in the world, no KYC, no nothing--that was literally the cypherpunk dream.

🚨SCOOP: Hearing from industry sources that stablecoin yield compromise text is imminent and could drop as soon as today. Reaching out to @SenThomTillis and @Sen_Alsobrooks offices for comment.





0/ Today, the Ethereum Foundation completed a bilateral swap of ~21,269 aWETH to wstETH, coordinated with @LidoFinance and @mellowprotocol as part of their ongoing deleveraging work.