Sabitlenmiş Tweet

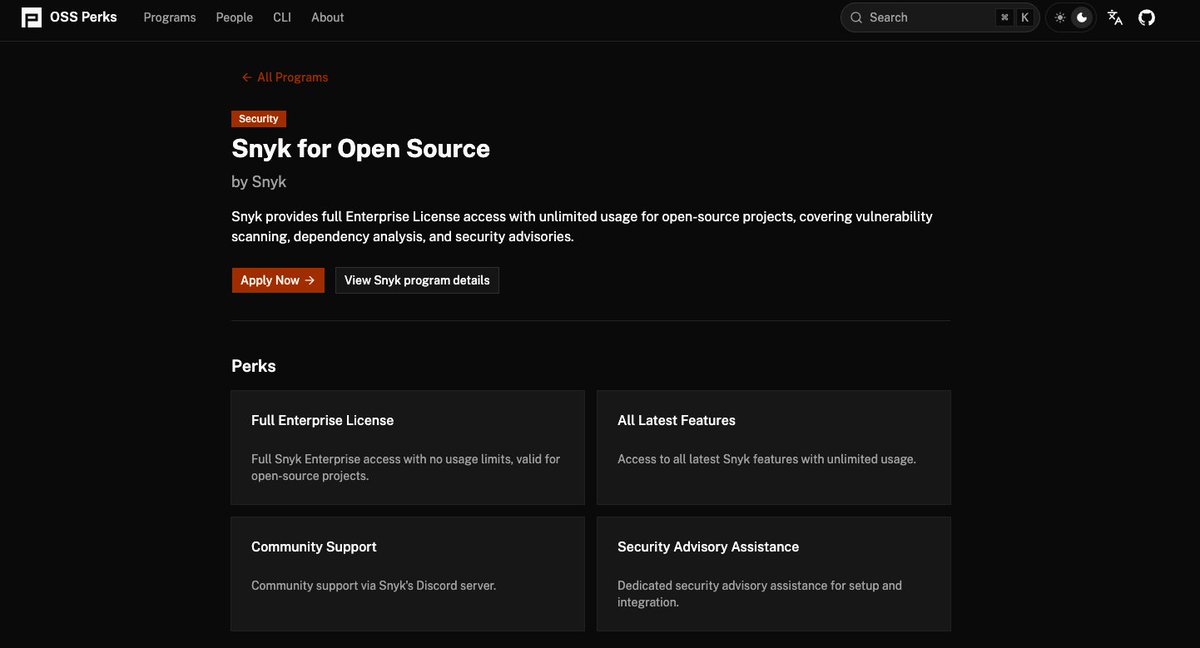
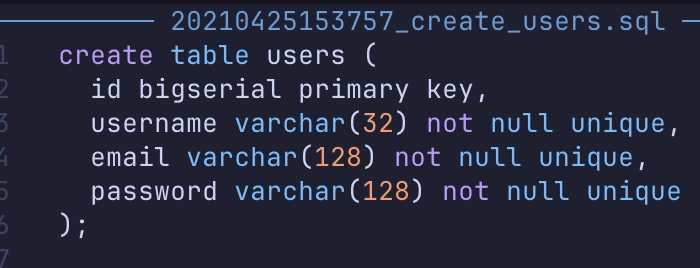
AI is writing code at machine speed.
Now, your security can close the gap with the Snyk AI Security Fabric.
Learn more about the industry’s first security layer for continuous defense across the entire SLDC here 👉 snyk.io/news/snyk-ai-s…
English