Space
2K posts



ايش المزبلة ذي؟ تصميم ليون التاريخي صار شي معاق 😅
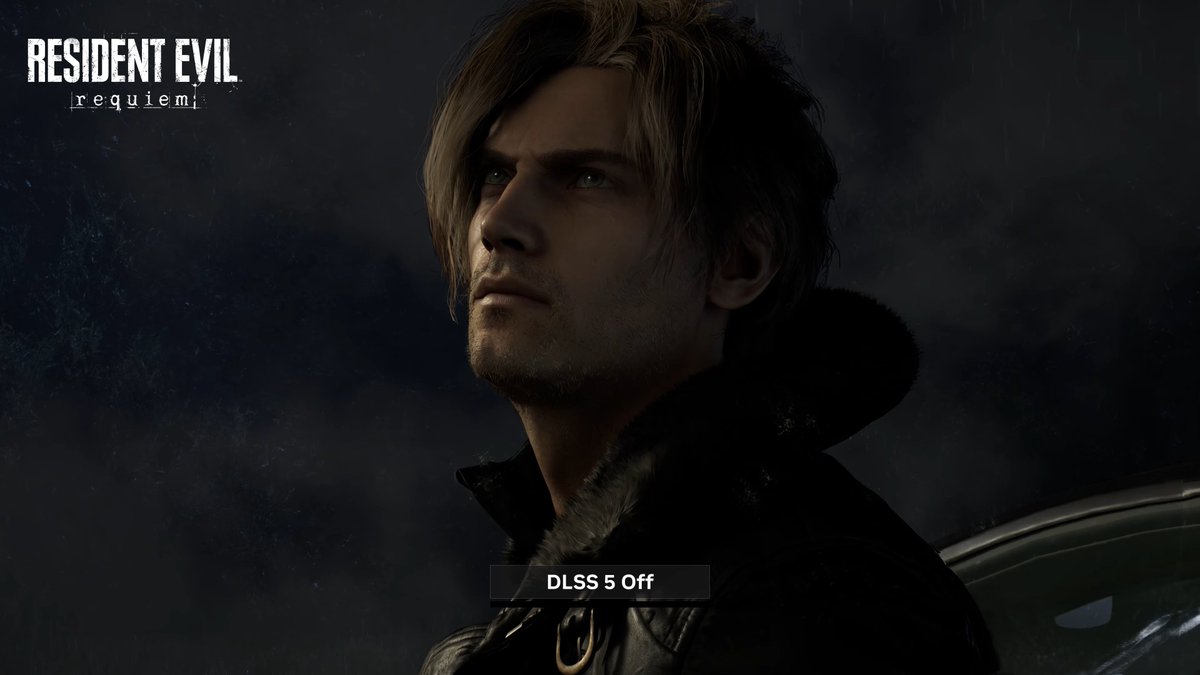

ايلـدر بلايـرز@ElderPlayers
🟢 شركة NVIDIA تعلن رسميًّا عن تقنية DLSS 5، وهي شيء مختلف عما قد يتصوره الجميع! 🖥️ تقنية DLSS 5 عبارة عن دمج لعالم الألعاب ثلاثي الأبعاد المعروف مع الذكاء الاصطناعي التوليدي، ما يجعل التقنية تصنع صورة جديد كليًّا بالاعتماد على بيانات اللعبة الأصلية! 💯 بالاستعانة ببيانات مثل الألوان و Motion Vectors وغيرها، تبدأ التقنية بالتعديل على الصورة، ويشمل هذا إعادة رسم موديلات الشخصيات وتحسين الإضاءة بشكل كبير، وغيرها من التفاصيل! - ما رأيكم؟
العربية

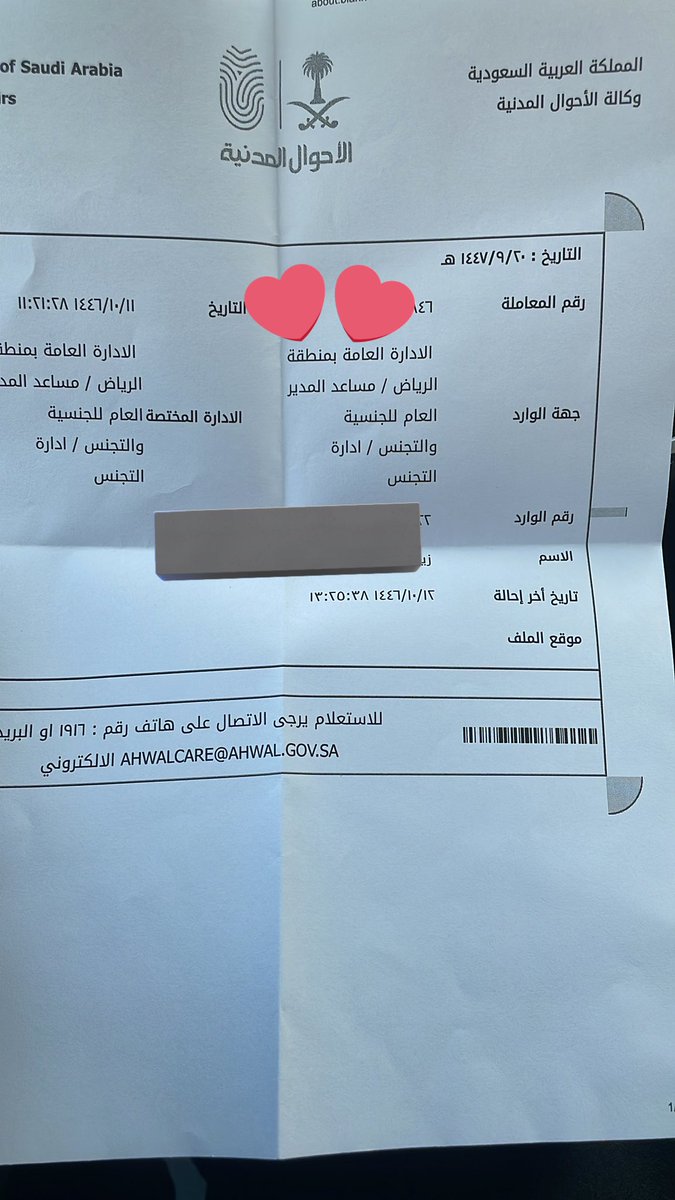
إن الله كتبها
يسيره عليكم وفضل كبير علي 💜
وما ذلك على الله بعزيز في هذي الأيام المباركة 💜💜
@KingSalman @AhwalKSA
العربية

@Space1097 يارجل عرف هذا الشيء : لكن استخدم تطبيقات فحص 🧐 مواقع و لا تفتح اي رابط الا اذا كنت عرف مصداقيته و خلاص
اصحاب جيلبريك يعرفون فقط شيءٍ اسمه المخاطرة من بداية كسر الحماية
العربية

@GaminGallifreyn @MasterMike88 @Little_34306 Exactly it’s becoming too dangerous now since what we have rn is a 1 click kernal access from a web page
English

@MasterMike88 @Little_34306 But now that we know these exploits are out there, running any of the jailbreakable versions is a huge risk.
If these are actually just floating around the Internet on random webpages I don't know if it's worth the risk to stay on these lower versions.
English

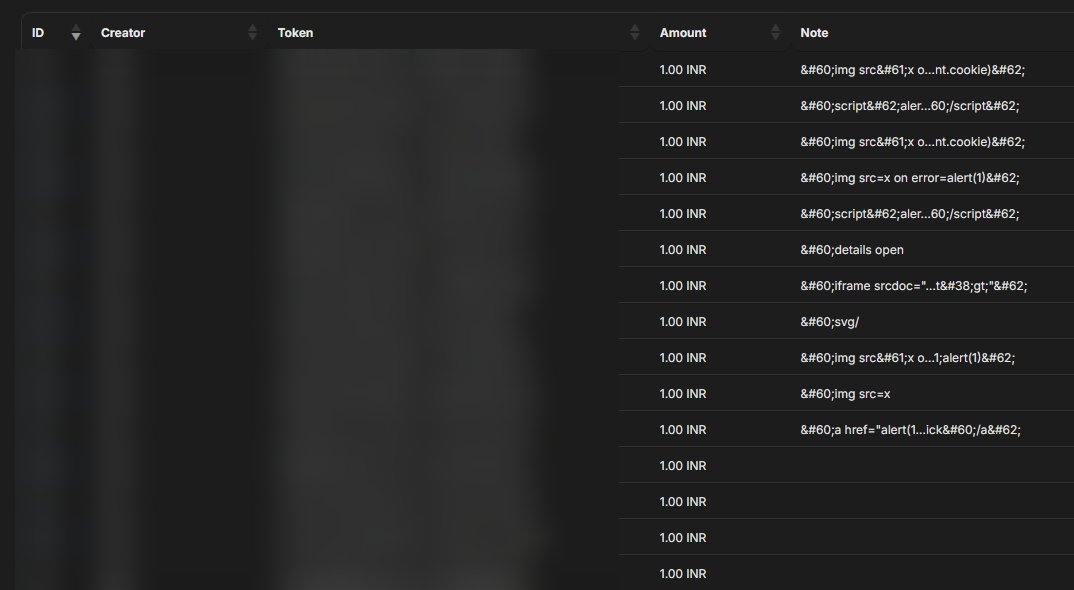
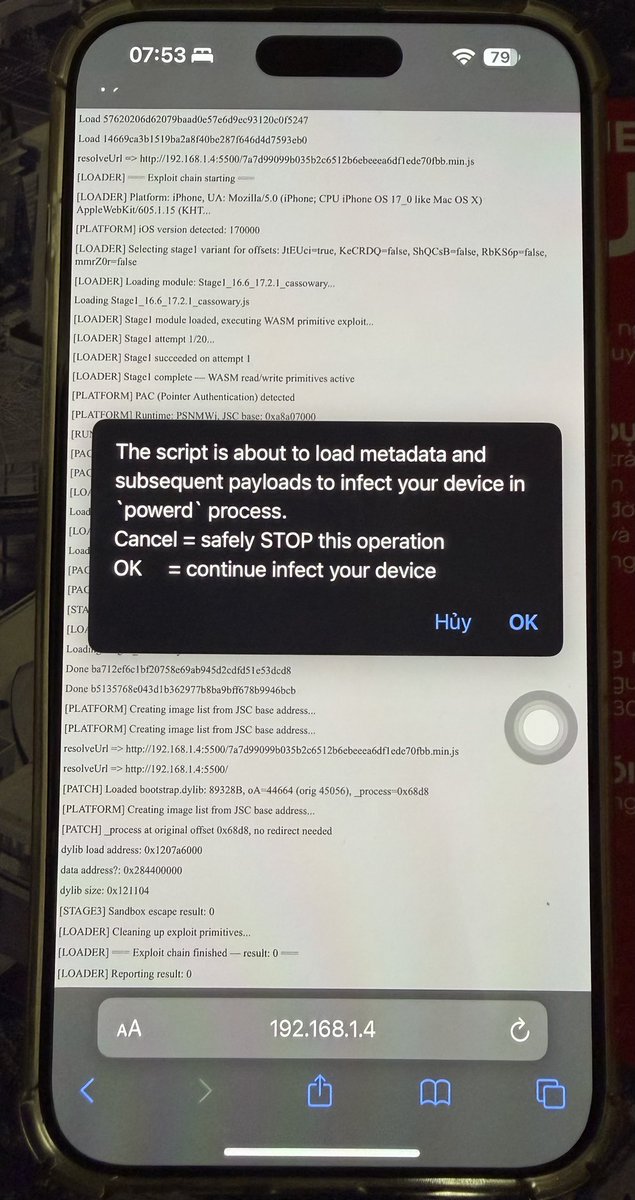
So, let's talk about that Coruna exploit kit stuff now, shall we?
Let's first establish a few basic grounding points, though, before people over-hype this too much:
1. There is zero guarantees that anything comes from this.
Everything here requires stuff to be deobfuscated before it could ever be beneficial for anything. This process inherently requires effort, and it's the type of thing that isn't guaranteed to go anywhere.
Additionally, while everything in this post is as accurate as current information tells us, there are things here that are subject to change or subject to validation.
2. Even if anything of note comes from the Coruna exploit kit, this is not a major major advancement.
The bugs that this chain kit uses were all patched by 16.7.6/17.5. Additionally though, the last kernel exploit was patched in 16.7.5/17.2.1, which means that the highest possible advancement for jailbreaking is:
- EoL (16.x): iOS/iPadOS 16.7.5
- 17.x: iOS 17.2.1/iPadOS 17.2
Which, to be clear, is not nothing - it would allow for the first proper jailbreak for arm64e 16.6-17.2.1, and it would also end the 2+ year streak of no arm64e advance or no jailbreak-relevant exploits. But it isn't going to take us to 18.x or even late-17.x.
Now that we've gotten that all out of the way, let's lay some groundwork here.
The Coruna exploit kit is a Chinese/Russian spyware kit, involving 23 different bugs designed to target devices running iOS versions 13.0 - 17.2.1.
You can read more about this spyware kit as spyware at the following two links:
Google Cloud Article: cloud.google.com/blog/topics/th…
iVerify Article: iverify.io/blog/coruna-in…
Now, Google and iVerify didn't directly publish any samples themselves about this (whether this will change in the future or not, I wouldn't know).
But, some of the links that it was mentioned that the spyware was on are still operating and are still actively able to infect devices. This is how various individuals have been able to get samples and begin to look into them.
Now, again, there are still a lot of things that need to be figured out before anything truly comes from this, but for now, let's focus on a few of the interesting things about this exploit kit:
1. The "PPL Bypass" bugs (for 17.x) appear to also work on SPTM devices.
Some additional context: iOS/iPadOS 17 replaced PPL with SPTM and TXM on some devices. On the relevant versions here (M4 was introduced in 17.4 and iOS/iPadOS 18 shift M2 to SPTM), this encompasses out to:
- PPL Devices: A12-A14/M2
- SPTM Devices: A15-A17
This change doesn't affect necessarily the flow of bugs (they usually will require PAC Bypasses) but it can potentially break certain bugs that would work for a PPL Bypass.
Based on what we have seen, however, it appears these bugs do work on SPTM devices, which does mean - if anything comes from this - this will likely work on all devices for 17.0-17.2.1.
2. There's enough bugs here for a WebKit jailbreak (and TrollStore installation method for relevant versions).
The entire goal of every chain that can be exploited with this kit is that it is designed to be a one-click exploit - you go to a malicious website and immediately have your crypto logins, location, camera roll, and other stuff siphoned off to China or Russia (depending on which type you get exploited by).
Now, as we've established, this is a full kit of exploits for a variety of versions starting with 13.0, and the kit is ultimately able to accomplish a one-click up to/including 16.7.4 (EoL) and 17.2.1 for all devices.
Because of that, all the bugs that would be needed for a WebKit-based jailbreak for 13.0-16.7.4/17.0-17.2.1 are present. Now, of course, that would require someone to put in the effort to exploit all of these bugs in a WebKit environment, but the option for someone to do that still exists.
Additionally, for those on TrollStore versions (14.0b2-16.6.1/16.7 RC (20H18)/17.0): As it would be possible to achieve a WebKit-based jailbreak, that also inherently means a WebKit-based TrollStore installer would also be viable.
(Note: If one did happen, it would obsolete almost every other method except for TrollHelperOTA (as that doesn't exploit a WebKit bug or kernel bug at all)).
English

My captured Coruna sample has got a lot further. It now loads everything from decrypted payload so you can freely replace dylibs for experiment. Safari-based TrollStore installer covering all supported versions is gonna be so real.
However this poses a risk for jailbreak users who may get infected by visiting malicious sites.
github.com/khanhduytran0/…
English

@ResidentEvil Please give us an option to start from any section of the game in RE9
English

@iBestGaming Specialize ها ههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههههه


@IDF You dropped the first bombs.
Israel is a Terrorist state.
English

In the last few minutes, sirens were sounded all throughout Israel, with an advance instruction alert directly to cellular devices to stay within proximity to protected spaces.
This is a proactive alert to prepare the public for the possibility of missiles being launched toward the State of Israel. The IDF emphasizes that the public is requested to stay in proximity to protected spaces.
English

Let's talk ports. Aside from 80 and 443 what is your favorite networking port and why? #CloudflareChat
English

@subwaysurfers i like the new subway surfers i have a question do the effects use HDR ?
English