Steve Kinder
3.5K posts


Steve Kinder
@StephenKinder
GPFS Engineering - IBM Storage - I own my tweets for which my employer, IBM, does not endorse. He/Him
Poughkeepsie, NY Katılım Temmuz 2009
865 Takip Edilen558 Takipçiler

Great game to play at parties or here in the comments.
Pick a song from a band or artist, and the winner is the biggest gap between their most popular song and their second most. @Spotify is the platform.
For example:
The La's - "There She Goes" 405,491,183 streams and their second most popular is "Feelin" with only 10,199,173
Any better than ~395m spread?
English

@StevenDickens3 Good luck Steven; your passion comes through well.
English

Announcing The Launch Of HyperFRAME Research
I’m thrilled to formally introduce HyperFRAME Research, a new venture designed to bring fresh perspectives and innovative approaches to the technology analyst space.
For decades, large firms have shaped the analyst landscape, providing IT vendors with market insights and strategic guidance. However, the industry is evolving. Independent and boutique firms are emerging as key players, driven by their ability to deliver focused expertise, faster responsiveness, and solutions tailored to address gaps often overlooked by legacy firms. The demand for real-time, actionable insights that empower agile decision-making has never been more urgent or pressing.
In parallel, traditional subscription models and paywalls are creating challenges. They can restrict access to critical information, especially for smaller organizations, while contributing to widespread "subscription fatigue." This shift is pushing organizations toward alternative models that prioritize accessibility without compromising quality.
Another transformation is the convergence of communication channels across PR, AR, Influencer Relations, and Investor Relations. Platforms like X (formerly Twitter) now host direct updates from CEOs, blurring traditional boundaries and accelerating the flow of information. The need for a flexible, digital-first approach has become clear.
Why HyperFRAME Research? HyperFRAME Research is built to address these challenges. Our mission is to provide frictionless, data-driven insights that are nuanced, timely, and actionable. We aim to support today’s fast-paced industry with intelligence that empowers informed decisions without unnecessary barriers.
Next Steps - We are eager to connect and collaborate as we embark on this journey.
Analyst Relations Professionals: Reach out via ARchitect or DM me to schedule briefings and explore partnership opportunities.
Reporters: For quotes and insights, feel free to connect via DMs on X or LinkedIn.
Visit our website: hyperframeresearch.com
Follow us on X: @hyperframe_res
This is just the beginning. Exciting times ahead! Also, check back in the new year for our new podcast, can't say too, much but I have got a very interested co-host lined up.
English

makes me even sadder that i didn’t get tickets.
not nearly as sad that i also lost out on the fenway shows, obviously. but sad.
MSG@TheGarden
2 sold out shows. 2 setlists to remember. 📷: @PearlJam
English

@LucianaMorales Sorry, Rc7+, Qxc7, RC2 wins the queen & checkmate in 2
English


@theRab Sorry for your loss Ryan. I had a Morkie, Cooper, that looked somewhat like Banjo, which I lost in the fall this past year. Heart breaking.
English

@astro_alexandra Cool. Could this have been leftover from the moon's creation, ejected when Theia creamed into proto-Earth?
English

The asteroid Bennu keeps bringing us new science! Astronomers think it might be a piece of an ancient ocean world! #space #astronomy #nasa #science
English

@snehalantani I love this thought, Snehal. People are always the weak link; assuming they have fallen (or will always fall) for a phishing attack makes a ton of sense. Having software, processes, and methodologies that do not presume perfect human responses seems obvious now that you say it.
English

I've been rethinking our approach to phishing defense lately, shifting from a focus on training & awareness to an "Assume Click" mindset...
Every day, it becomes easier for attackers to craft convincing and targeted phishing attacks. Moreover, no matter how much we invest in training and awareness, some percentage of the company will click on a link. So we're on an unsustainable trajectory.
"Assume Click", like "assume breach", just assumes employees will open every email and click every link. The burden shifts from educating the workforce to isolating the blast radius. So an "Assume Click" framework could be:
1. Blast Radius Reduction
Goal: Determine the blast radius for each IAM Role within the organization. Often you'll be surprised at how the credentials of an "intern" could be used by attackers to become a Domain Admin.
- Methodically reduce the blast radius for each IAM role
- Methodically reduce the permissions for each user, shifting from permissive by default to least-privileged
- Create a specific workstream focused on continuously reviewing and reducing the number of admin accounts and password reuse across those accounts
2. Isolating the compromise
Goal: Prevent the attacker from gaining access to sensitive data and systems
- Rollout phishing-resistant MFA using hardware tokens (e.g. Yubikeys) to make it difficult for attackers to actually utilize compromised credentials
- Quickly isolate compromised endpoints, with a workstream focused on measuring and improving the reaction time for this process, with a special focus on the browser and end-user device
- Focus on SOAR scripts that quickly invalidate credentials and isolate networks & systems
Finally... Train like you fight. Build muscle memory from the end-user to the SOC on how to detect and respond to a user who has clicked on a malicious link
I'm still thinking through this, but these are the areas I've been focused on building out.
#phishing #infosec #CIO #CISO #cybersecurity @Horizon3ai
English

Metallica performing "Master Of Puppets" one week ago in Munich.
This is not a performance, it is a statement.
Rain, thunder, 60 years old…
Nothing can stop Metallica.
#Metallica
English

@snehalantani Yes, agree with your thinking. Likely, most business interactions will be AI to AI, and they will learn a short-hand notation we won't even understand, say symbol exchange, and we'll really be in a situation where they will need to slow down to even talk to us meat sacks.
English

[Controversial take on AI and security following RSA… ]
After the walking the floor at RSA week, I think we’re going to experience 3 distinct phases of AI in cyber:
Phase 1: The Great “Sameness”. Vendors will start sounding the same because marketing teams are rapidly adopting ChatGPT to update their content, websites, and messaging. This will make it nearly impossible for buyers to differentiate between what’s real vs vaporware
Result: buyers will rely on champion-based selling where the opinion of trusted peers and partners will be paramount.
Phase 2: Co-Pilots are the new “Dark Mode”. We’ll see an arms race for who can build the best chat interface into their product. The challenge: unless the vendor has a corpus of proprietary data, the chat interfaces will be trained on the same public information
Phase 3: The Wreckoning. Nearly every product on the expo floor was designed for humans IN on ON the loop.
[in the loop = human must do the work, like query log data
On the loop = some supervised ML identifies anomalies for a human to investigate]
But IMHO, the future of cyber warfare will be algorithms fighting algorthms with humans by exception. This means Humans must be OUT of the loop for nearly every decision and action, and that requires a fundamentally different Architecure and user experience.
So the great reckoning: it will be very difficult for existing security vendors to rebuild their products from humans In/on the loop to “humans by exception”. That means for the first time in decades, the TAM for a security startup is… the entire market…
Definitions:
Humans In the Loop: Humans actively participate in the decision-making process of the AI system. They are directly involved in providing inputs, reviewing outputs, and making or approving decisions.
Humans On the Loop: Humans monitor and oversee the AI system, which operates autonomously. They intervene only when necessary, such as in cases of malfunction or when the AI system encounters situations it cannot handle.
Humans OUT of the loop: The AI system operates entirely autonomously without real-time human intervention or oversight. Humans may be involved in the initial programming and training of the system but are not part of its operational decision-making process.
#cybersecurity #infosec #ai
English

We're only two months away from Toad beginning the first leg of their tour celebrating #Dulcinea30. What songs are you hoping to hear?
🎟 toadthewetsprocket.com/on-tour/

English

@epc I did not know that; thank you for the PSA. I assume you mean black licorice.
English

@dims I lost one of these. The following week, hit with a lawnmower. (It had rained most of that week.) Had a small mark on the back case. Recharged, and as far I know, it still works - although the cell towers won't talk with these any longer.
English

@LouStagner Even with a rule change, you'd still occasionally get to leverage those skills - divots happen in the rough also.
English

@WillStern_ I don't get the sealed tech bit. In the end, it's a box. I also recognize that people may feel the same about pieces of cardboard.
English


a That Guy staple of my youth, from Blade Runner to Fletch to Critters to Back to School.
RIP
Alan Sepinwall@sepinwall
“No movie featuring either Harry Dean Stanton or M. Emmet Walsh in a supporting role can be altogether bad.” -Roger Ebert RIP, M. Emmet Walsh
English

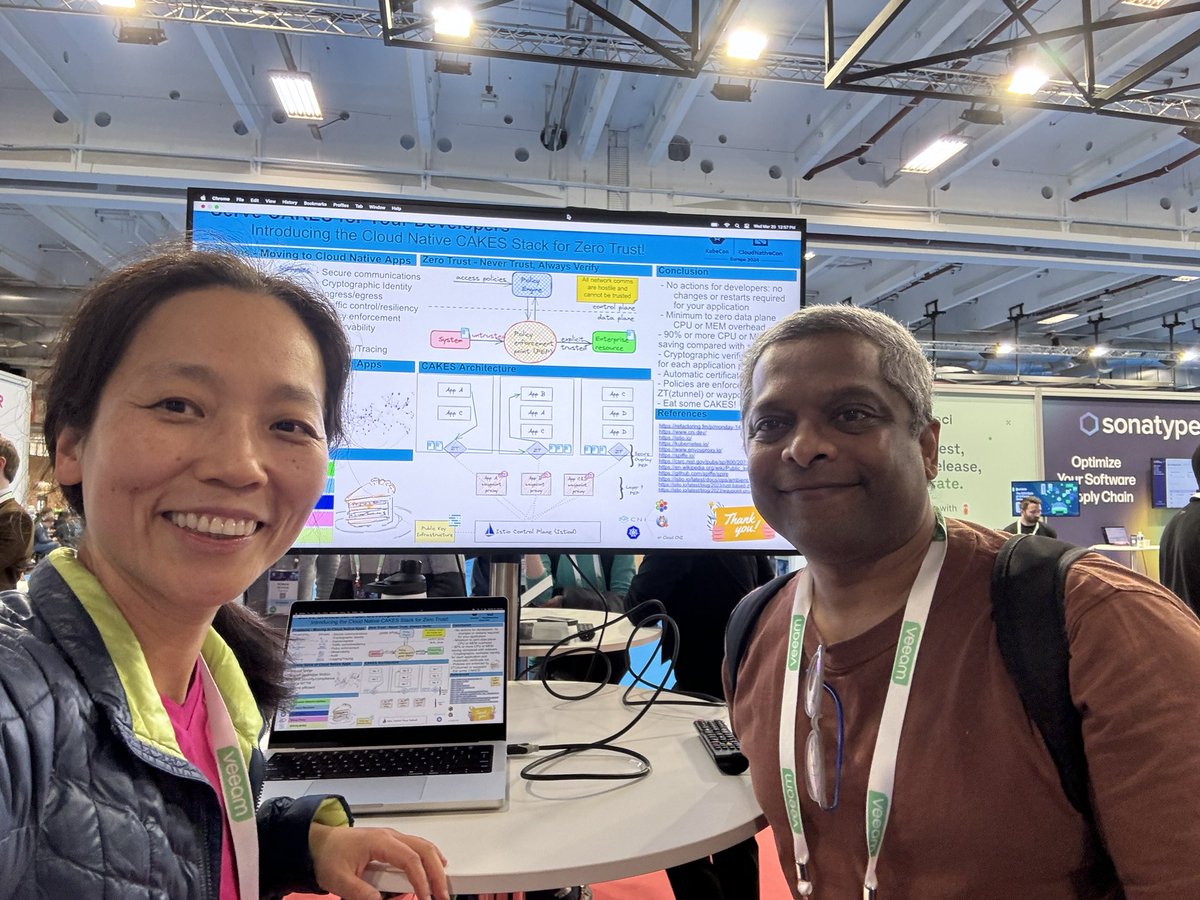
@linsun_unc @dims Now, there are two friendly faces... good luck with the event.
English