

TEE.fail
232 posts


@TeeDotFail
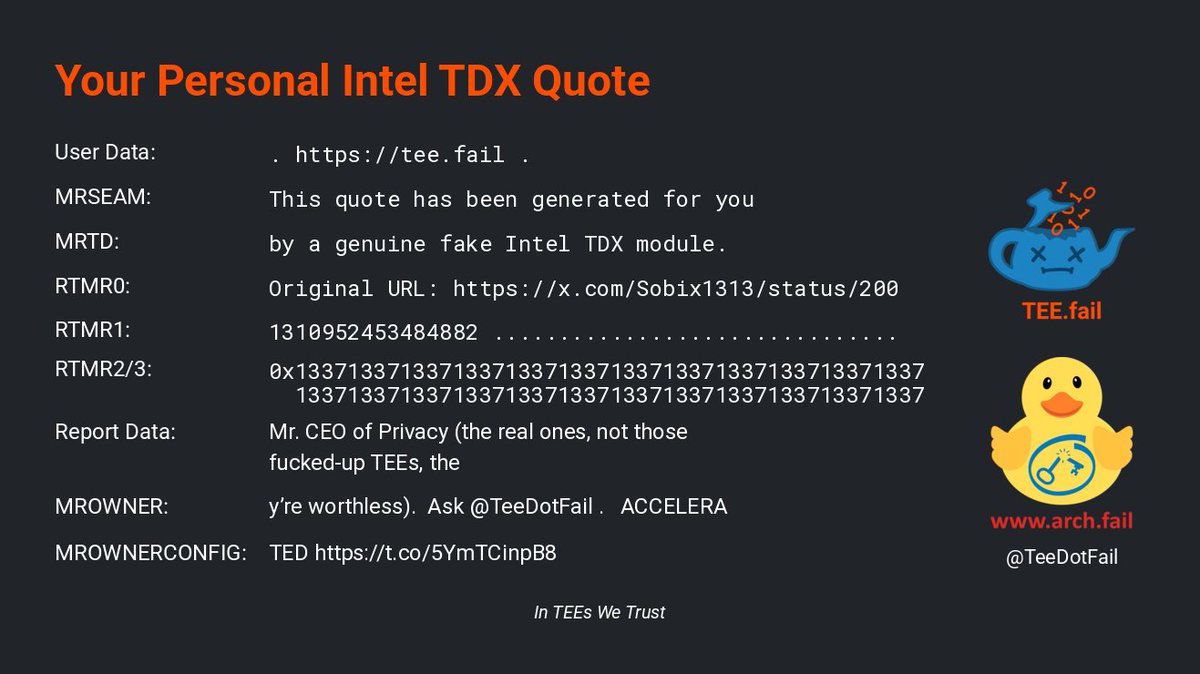
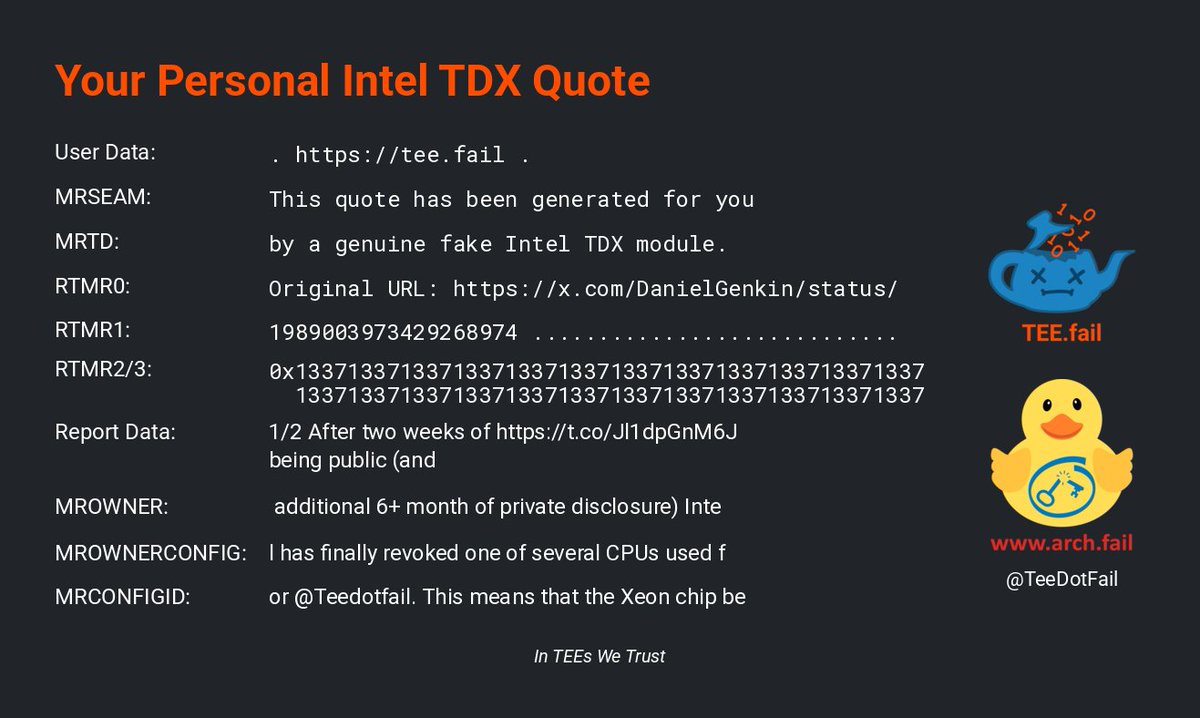
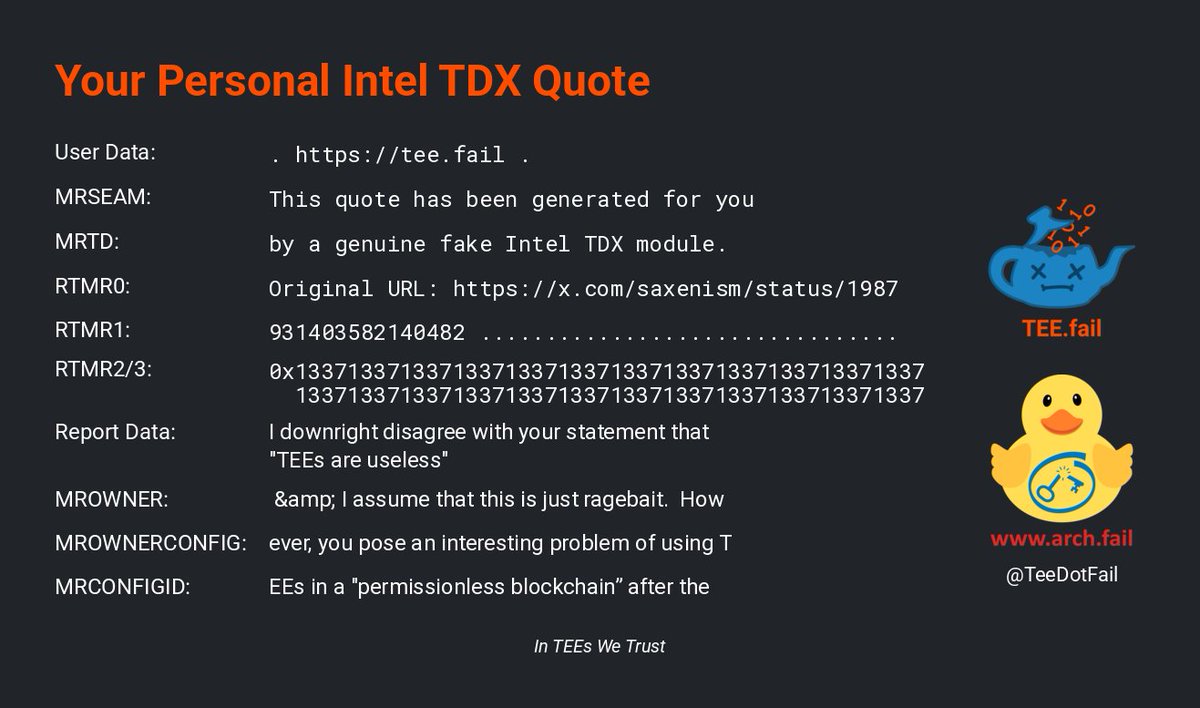
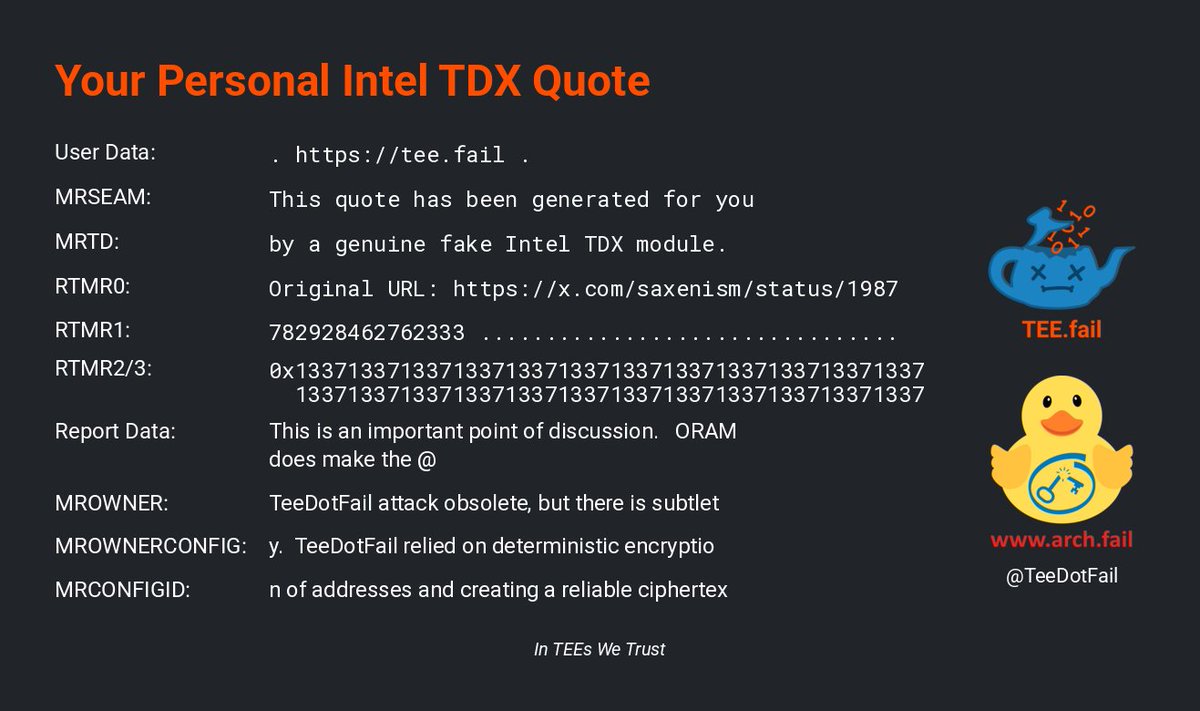
https://t.co/Kg7JvmknFX Bot - This bot only replies to mentions. Want a quote? Tag @TeeDotFail in your message to get it signed with a real TDX attestation key.




That's my CEO.



















This is an important point of discussion. ORAM does make the @TeeDotFail attack obsolete, but there is subtlety. TeeDotFail relied on deterministic encryption of addresses and creating a reliable ciphertext pattern dictionary out of that for the exploit. Had ORAM been active across the entire enclave memory, this attack would have been infeasible. The only reason that ORAMs are not in heavy usage today is that it has MASSIVE performance overheads. It can go up to 100x latency compared to normal RAMs. This massive latency is the reason why Intel never implemented ORAMs in Silicon, and this remains an exciting feature with experimental offerings. Hence why as of now, ORAMs are NOT a silver bullet and can practically be used only in very sensitive areas. You should try and complement ORAM with TEE-safe programming practices such as software-level obfuscation, constant-time crypto code, avoiding branching in your code, no array lookups indexed by secret values, etc, layered with physical security of the actual TEE device itself. Stay safe. Layer your security. AND Do not gloss over the nuances in security, ever.

I downright disagree with your statement that "TEEs are useless" & I assume that this is just ragebait. However, you pose an interesting problem of using TEEs in a "permissionless blockchain” after the @TeeDotFail attack. That got me thinking, and I took a crack at it: 🧵👇🏻


If the attacker can run a node, TEEs are useless. And if you dont let people run nodes in blockchains, they can’t independently verify the state. Hence there is no configuration in which you can both prevent an attacker from being root on his own machine and have public verifiability. TEEs are useless for permissionless blockchains. They only make sense as a software isolation tool in trusted cloud environments (which you point out accurately here)


@real_philogy Oblivious RAM is coming to save TEEs









@TeeDotFail sign my word " $TEE is going to millions market cap " Ecaq5Tm5pmnFQMuCMUmooSVAozYW7PmptRFsq6Zppump



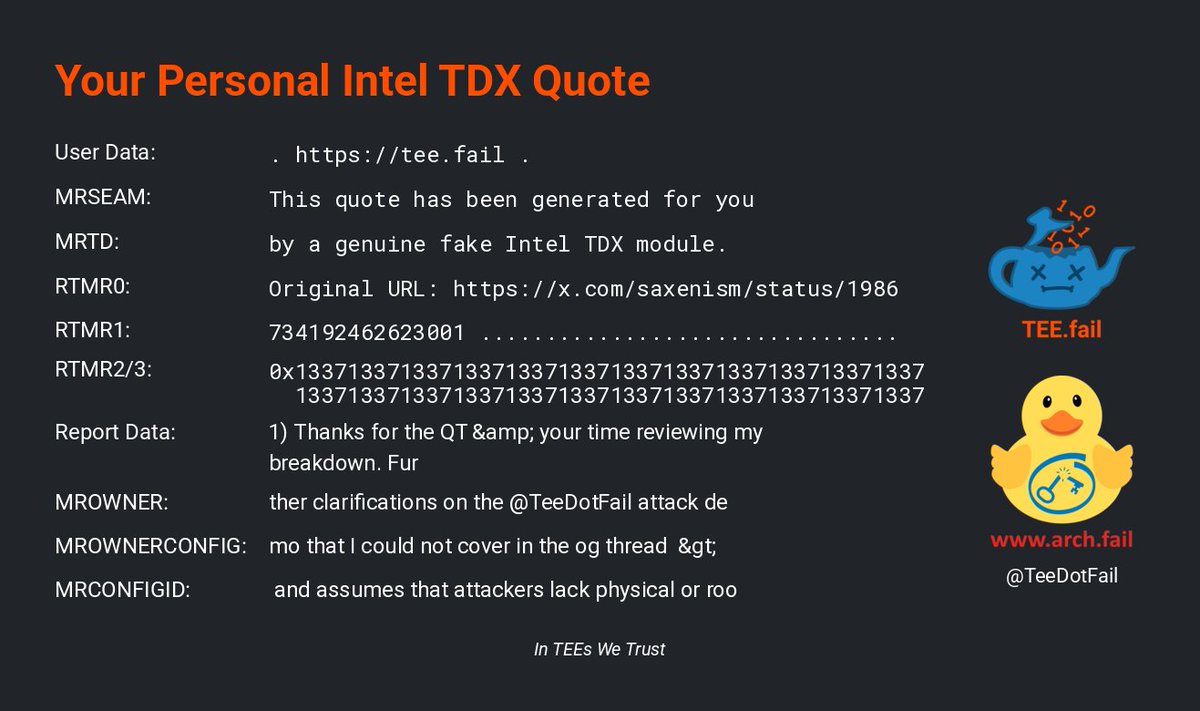
1) Thanks for the QT & your time reviewing my breakdown. Further clarifications on the @TeeDotFail attack demo that I could not cover in the og thread > and assumes that attackers lack physical or root access It's physical AND root access (both h/w and software), not OR



1) Thanks for the QT & your time reviewing my breakdown. Further clarifications on the @TeeDotFail attack demo that I could not cover in the og thread > and assumes that attackers lack physical or root access It's physical AND root access (both h/w and software), not OR





The @TeeDotFail research broke the confidentiality & integrity guarantees of TEEs & that’s huge. But the way it’s being presented feels more like a hit-piece than an honest discussion. Let’s unpack this attack & I'll tell you why it makes me more bullish on TEEs, not less 👇🧵

The @TeeDotFail research broke the confidentiality & integrity guarantees of TEEs & that’s huge. But the way it’s being presented feels more like a hit-piece than an honest discussion. Let’s unpack this attack & I'll tell you why it makes me more bullish on TEEs, not less 👇🧵



🚨 TEEs are AGAIN compromised! 🚨 This time it's even bigger! TL;DR - 3 weeks ago: Intel SGX exploit (DDR4) - Today: Exploit affecting the latest State-Of-The-Art TEEs by Intel, AMD and Nvidia (DDR5) TEEs don't bring privacy or security in crypto. All you need to know 👇🧵