Daniel Genkin
25 posts


Daniel Genkin
@DanielGenkin
Associate Professor at Georgia Tech. Security, systems, side channels, cryptography.
Atlanta, GA Katılım Ağustos 2018
174 Takip Edilen816 Takipçiler

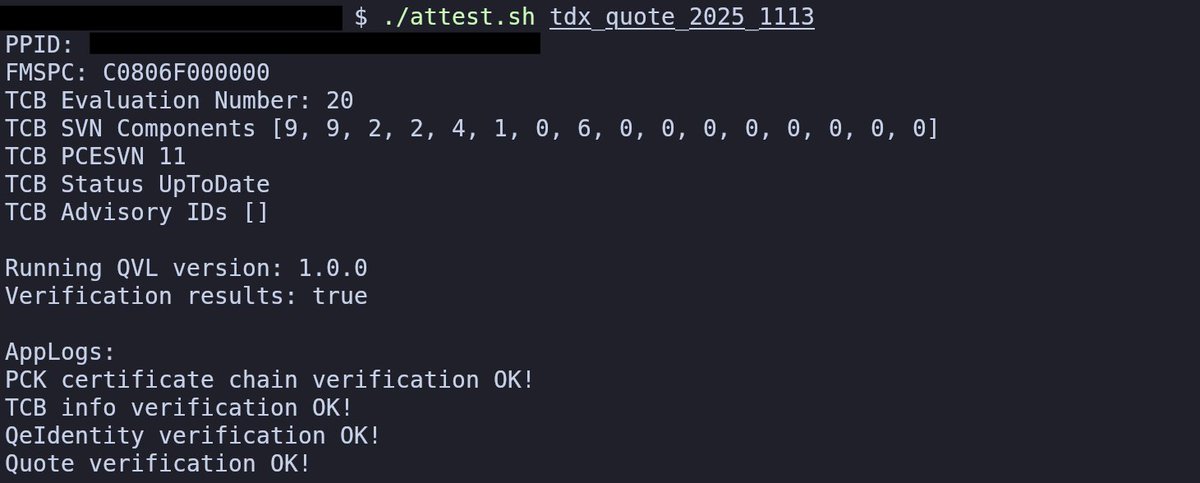
1/2 After two weeks of TEE.fail being public (and additional 6+ month of private disclosure) Intel has finally revoked one of several CPUs used for @Teedotfail. This means that the Xeon chip below has made the ultimate sacrifice and will never run SGX or TDX again.


English

@secparam @ittaia @bgmshana @badcryptobitch @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS Lasers, drones, robots, TEE, and AI. What can go wrong? :-)
English
@ittaia @bgmshana @badcryptobitch @VitalikButerin @aniketpkate @socrates1024 @DanielGenkin @CryptoGPS Are you just trying to motivate Daniels laser side channel?
English

Good point. While this decryption process can be made distributed, it is important to understand that the distributed FHE decryption is not scalable, especially for a verifiable decryption process.
Going for decentralization beyond 20 nodes will be a challenge.
MPC such as Velox (eprint.iacr.org/2025/1630) can scale much better.
Ian Miers@secparam
There's no such thing as Fully-Homomorphic Decryption. Anytime you see a system using FHE to compute on your sensitive data, remember: someone has the key. If its not you, do you trust them?
English

@ittaia @randhindi @badcryptobitch @alinush @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS Is DanielGenkin access more or less powerful than root access?
English

@DanielGenkin @randhindi @badcryptobitch @alinush @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS TEEs (assuming perfect physical security, only software/network attackers, no @DanielGenkin access) give you confidentiality + integrity
FHE without ZK is like a TEE with confidentiality but no attestation (integrity), it works, but be careful what it does
English

@randhindi @badcryptobitch @alinush @ittaia @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS so TEEs in principle do, like attestation tells you which code is running and if you know what the inputs are, the output is fixed. At least until you get a DRAM interposer :D
English

@DanielGenkin @badcryptobitch @alinush @ittaia @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS Right yes, I was only talking about blockchain applications. For client server you are right that FHE alone doesnt offer integrity (but neither does any plaintext cloud service, you have to trust the provider is sending the correct response)
English

@randhindi @badcryptobitch @alinush @ittaia @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS if its a blockchain application, sure. Although you need to be careful to never operate until what mechanism you used (say consensus) has stabilized. If its just a single node trying to be an alternative to a TEE, its much harder.
English

@DanielGenkin @badcryptobitch @alinush @ittaia @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS FHE is publicly verifiable so you can achieve integrity of the encrypted state the same way you do with plaintext state: consensus, optimistic fraud proofs, zk etc. Anyone can recompute the state
English

@badcryptobitch @alinush @ittaia @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS guarded by lasers!
English
@alinush @DanielGenkin @ittaia @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS Shhhh.
The VCs are cumming
English

@ittaia @alinush @badcryptobitch @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS As for FHE, I would still be careful. Remember you don't have integrity, just confidentiality.
English

@ittaia @alinush @badcryptobitch @secparam @VitalikButerin @aniketpkate @socrates1024 @CryptoGPS do lasers count?


English
Daniel Genkin retweetledi

@DanielGenkin Your message "More interposer fun, this time with DDR5 memory. Breaking TDX, S..." has been signed. Check out your quote at: view.tee.fail/view/45ecffd7c… and visit tee.fail for more info.

English

More interposer fun, this time with DDR5 memory. Breaking TDX, SGX, SEV and even Nvidia TEEs. Checkout our work at TEE.fail, and get a personally-signed Intel attestation report at @TEEdotFail.


English

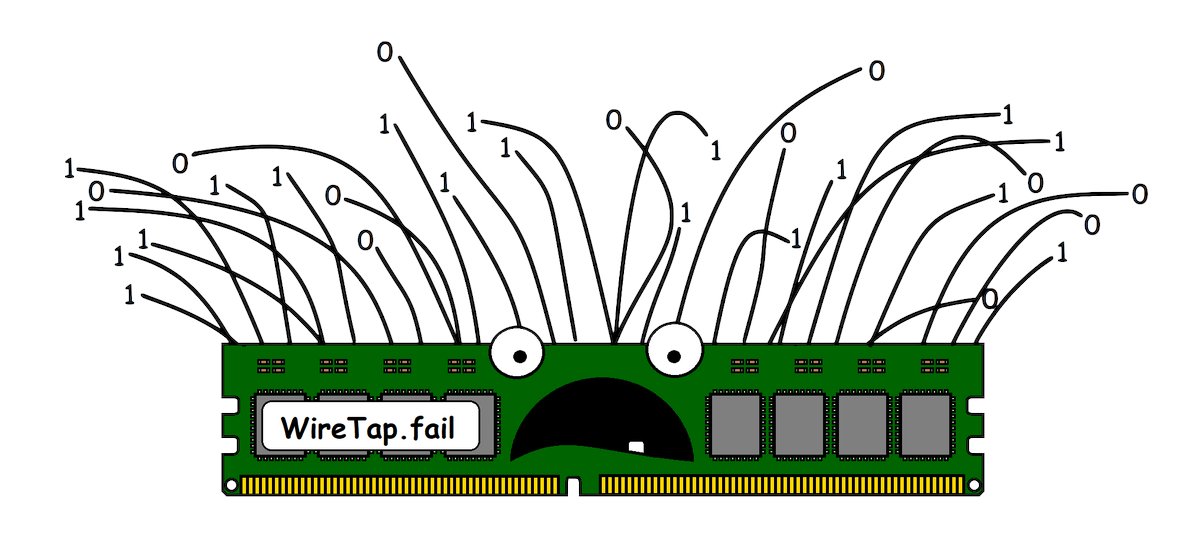
Want to know what happens when commercial TEEs meet improvised DRAM memory interposers? SGX mayhem including attestation key extraction. Please DO try that at home😉. Check out our work at wiretap.fail
English

Have an Apple device from the last few years? We have a new side channel attack for you. Checkout our work at predictors.fail
Joint work with Jason Kim, Jalen Chuang and Yuval Yarom (@yuvalyarom). Could not have asked for a better team!

English
Daniel Genkin retweetledi

Our work on page walk side channels was accepted at @IEEESP 2025 (#ieeesp2025)! The full paper is now available at: gofetch.fail/files/peek-a-w… and our code is available at: github.com/FPSG-UIUC/Peek…

English
Daniel Genkin retweetledi

Excited to present "Pathfinder: High-Resolution Control-Flow Attacks Exploiting the Conditional Branch Predictor" at @ASPLOSConf with Archit Agarwal, Max Christman, @CryptoGPS, @DanielGenkin, Andrew Kwong, @flowyroll, @deiandelmars, @mktaram and Dean Tullsen. (1/4)🧵
English

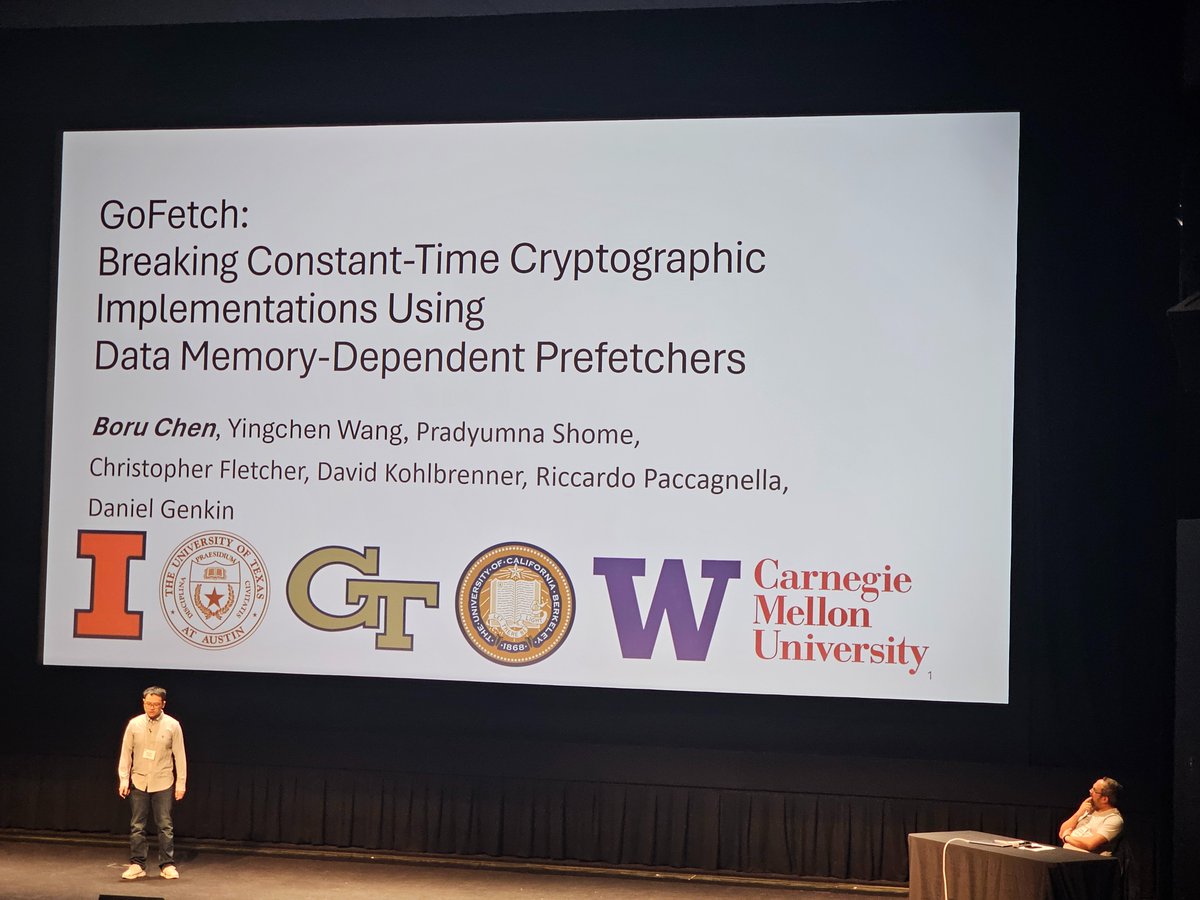
GoFetch.fail happening now @RealWorldCrypto. Come see Boru Chen (@blue75525366) talking about breaking constant time crypto using fancy prefetchers on Apple CPUs
English

Ever wondered what happens when side-channel resistant code meets a fancy prefetcher? Checkout our paper breaking constant time crypto on Apple CPUs.
gofetch.fail
Joint work with Boru Chen, @YingchenWang96, @PradyumnaShome, Chris Fletcher, @dkohlbre, @ricpacca
English

I'm very thankful to the @SloanFoundation for recognizing my research. Could not have done it without my awesome students, great collaborators, and wonderful mentors. Checkout our research group that made this possible at architecture.fail
Sloan Foundation@SloanFoundation
We have today announced the names of the 2024 Sloan Research Fellows! Congratulations to these 126 outstanding early-career researchers: sloan.org/fellowships/20…
English

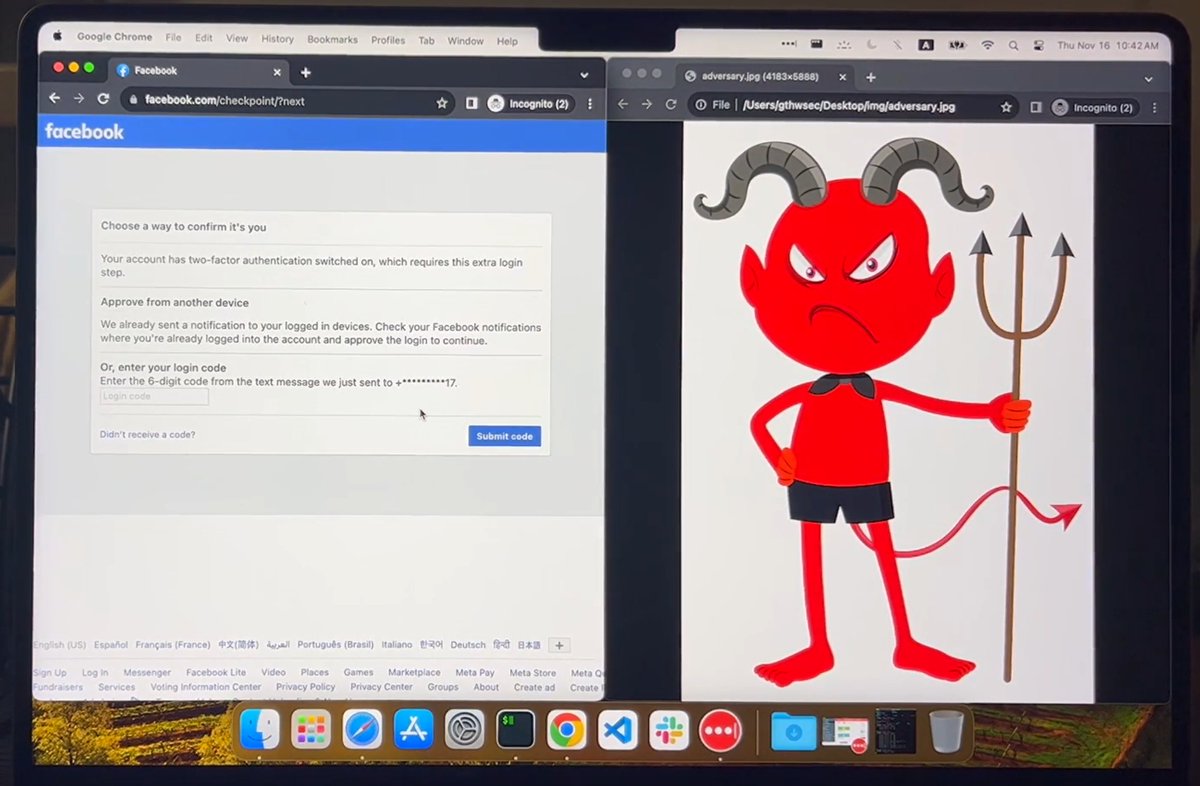
Microarchitectural unboxing: check out our new demo for breaking two factor authentication using iLeakage. Yes you heard it, speculative execution attacks on Apple’s M3 Macs and latest Safari that defeat Facebook’s 2FA over SMS.
ileakage.com

English
Daniel Genkin retweetledi

Goodbye WOOT the Workshop, hello WOOT the Conference!
Excited to be a part of this legacy and this new beginning.
USENIX WOOT Conference on Offensive Technologies@wootsecurity
WOOT! Big news! Starting 2024 WOOT will be @USENIX WOOT Conference on Offensive Technologies! WOOT '24 will be on August 12-13 2024, colocated with USENIX Security WOOT '24 will be co-chaired by @noopwafel (@intel) and @adamdoupe (@uarizona) usenix.org/conference/woo…
English