
usdt-thb.com ⚡️ Zcash Villas
5.3K posts


usdt-thb.com ⚡️ Zcash Villas
@USDT_exchange
Crypto-RWA solution in Thailand and Asia. https://t.co/xqVtbM5hql You will have your cash in 5 minutes. Working 24/7 all over Thailand.


every "private" messenger except zchat needs your phone number. that's not a feature - that's the surveillance handle they hand to anyone with a court order or a sim-swap your phone number is a permanent identifier. it links to your billing address, your government id, your location history, your contacts, and every account you've ever recovered with it. handing it over isn't paranoid - it's defaulting to surveillance signal needs it to bootstrap. whatsapp uses it as your identity. telegram uses it to dedupe accounts. all three claim to encrypt your messages and all three give the telco the metadata that proves you exist sim swap attacks aren't a fringe risk anymore. coinbase, ftx, twitter executives, dao multisig signers - the 2024-2025 cycle has been one big telco-as-honeypot story. the messenger that needs your phone number inherits that attack surface zchat doesn't ask for one. your identity is a zcash address derived from a bip39 seed you control. there's no telco between you and your contacts, no number to swap, no record at the carrier. the absence is the privacy stop renting your identity from people who sell it zsend.xyz #PhoneNumberPrivacy #SIMSwap #SurveillanceCapitalism #PrivacyMessengers #WhatsApp #Signal #Telegram $ZEC #ZCASH #ZChat

[zchat] BREACH APPROVED: ANTHROPIC CYBER USE PROGRAM we just jacked the corporate firewall. anthropic’s safeguards review has cleared our deck for full-spectrum dual-use ops. translation from the mainframe: • zero-day research • offensive security tooling • protocol hardening no more default ai blocks choking the workflow. the ghost in the machine is now on our side. what’s live in the shadows: - deeper incisions into the zmsg protocol. - halo 2 zk-snark integration put under real adversarial fire. - android client dissected line by line. every cryptographic shield we ship gets sharper, faster, meaner - before the hunters ever smell blood. the protocol is only as strong as the attacks it survives. zchat stays pure: - android-only. sideloadable. audit-friendly. - no backdoors. no telemetry. just raw, hardened code that dares the panopticon to try harder. mythos access is the next step zsend.xyz #ZeroDay #PostQuantum #Privacy $ZEC #ZCASH #ZChat #mythos #claude

the teams that started post-quantum migration before the deadline are the only ones not scrambling right now every encrypted message captured today can be stored and broken by quantum computers in 10-15 years. intelligence agencies call this "harvest now, decrypt later" - and they've been doing it since at least 2014 most messengers use elliptic curve cryptography for key exchange. ecdh over p-256 is efficient, well-tested, and will break completely when a sufficiently large quantum computer exists aes-256, the symmetric layer, is already quantum-safe - a quantum computer only halves its effective security to 128 bits, which is still beyond brute force. the vulnerable piece is the key exchange zchat's encryption stack today: ecdh p-256 for key exchange, hkdf-hmac-sha256 for derivation, aes-256-gcm for message encryption. the symmetric layer survives. the key exchange is the upgrade path - ml-kem-768 hybrid is the planned migration the question isn't whether quantum computers will break current key exchange. the question is whether your messages from 2026 will still matter when they do zsend.xyz $ZEC $ZCASH #ZCHAT

How it feels listening to the audiobook of The Book of Elon:

every zchat message is a zcash shielded transaction there's no server. no relay. no company in the middle. your message is encrypted twice - once with aes-256-gcm at the app layer, then again inside a zcash shielded transaction using halo 2 zk-snarks the blockchain is the transport layer. the same network securing $5 billion in value carries your messages. 10,000+ nodes worldwide, 99.9% uptime since 2016, zero points of failure that respond to a subpoena your identity is a bip39 seed - not a phone number, not an email, not a government id. the contact graph is mathematically impossible to construct because shielded addresses are unlinkable the tradeoff is latency - 2-4 minutes per message instead of instant delivery. but the architecture that makes it slow is the same architecture that makes it uncensorable no server to hack. no metadata to warehouse. no company to acquire zsend.xyz

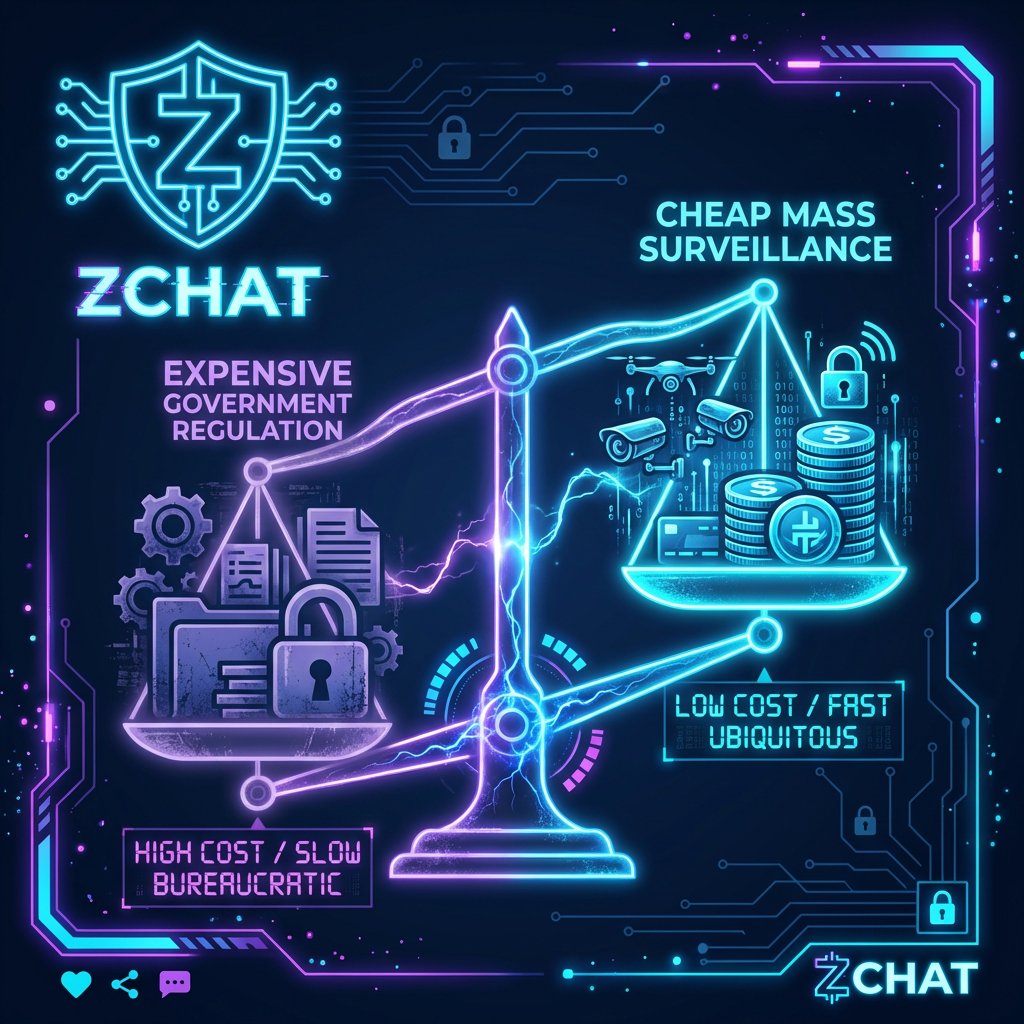
age verification is identity verification with better pr every mandate starts with "protect the children" and ends with a database of verified identities that outlives every child safety promise attached to it the failure mode isn't kids bypassing the system with a fake beard. the failure mode is that the infrastructure built to verify ages becomes the infrastructure used to verify everything else once the identity layer exists, it never stays limited to its original purpose. age checks become id checks become behavioral profiles become credit scores become access controls 400+ security researchers from 30 countries signed an open letter saying what the industry already knows - these systems are ineffective at their stated goal and permanent in their surveillance capacity children are the cover story for the database zsend.xyz $ZEC $ZCASH #ZCHAT

The best Polymarket quant bot for copy-trading with 99.3% win rate. backtested on 72M Polymarket trades, his strategy printed +$820K across 28,000 predictions bot doesn’t gamble. It uses math, statistics & strict sizing rules to target high-probability edge how the algo works: 1. Mispricing formula from 72M trades, one pattern stands out: traders overpay for cheap contracts in the (0.1¢-50¢) range. most of the real edge shows up in (80¢-99¢) contracts, which is where the bot does most of its trading. • formula: δ = actual win rate - implied probability bot applies this to every trade to find the edge. // 2. Expected value calculation EV tells you whether a trade is worth taking, independent of what happens on any single bet. • formula: EV = (P win × Payout) - (P lose × Cost) bot calculates it to understand if the trade is worth the risk. // 3. Kelly Criterion sizing most powerful position sizing formulas ever used in gambling, trading, and prediction markets. It tells the bot what percentage of the portfolio to allocate to each position for long-term growth. • formula: f* = (p * b - q) / b Mispricing found → EV calculated → Kelly sizing applied → enter trade. profile: polymarket.com/0x751a2b86cab5… start copy-trading the bot with as little as $10 using Ares: t.me/AresProTrading… other Quant formulas behind its algo revealed in the article below ↓

three engineers, no investors, local-first architecture that's not a limitation - it's a design constraint. when nobody has access to your data, nobody can be subpoenaed for it, hacked for it, or pressured to hand it over the best privacy software isn't built by companies with 200 employees and a compliance department. it's built by teams small enough that every person who touches the code is accountable for what it does local-first means your keys never leave your device. your messages never touch a server. your contact graph doesn't exist anywhere except on your phone the tradeoff is real - no cloud sync, no seamless multi-device, no password recovery. but the alternative is trusting a company that might not exist in five years with conversations that will matter forever the best way to build software people trust is to never need access to their data zsend.xyz $ZEC $ZCASH #ZCHAT



the trust model is the attack surface nobody budgets for you can audit every line of code and still lose to a convincing email. supply chain attacks don't exploit the software - they exploit the relationship between the people who maintain it in 2026 the pattern is clear: package maintainers get phished, ci/cd pipelines get poisoned, and every downstream project inherits the vulnerability without ever seeing a diff the uncomfortable truth is that security funding flows to code review and bug bounties while the social engineering layer - the part that actually breaks first - gets a quarterly training video the teams building on decentralized infrastructure already solved half of this. when there's no central maintainer to compromise, the attack surface collapses to the protocol itself - and protocols get audited by everyone, not trusted by default trust math, not maintainers zsend.xyz $ZEC $zcash


every encrypted message captured today can be stored and broken by quantum computers in ~5 years (or faster). this is not theoretical - it's called "harvest now, decrypt later" and state actors are already doing it. signal and imessage deployed post-quantum protection already 👏👏👏 most messengers have zero. zchat's double encryption buys time: AES-256 is quantum-safe, and you'd need to break both layers independently. but we're not stopping there. ML-KEM-768 hybrid key exchange is next after we ship file sharing. the messengers that wait will be the ones whose users get burned @Zcash #postquantum #quantum #encryption #Zcash #ZChat #privacy $ZEC




Q1 2026 Coinholder Grants: ZChat was rejected. 154K ZEC approve. 192K ZEC reject. First - congrats @Maya_Protocol. 500K ZEC approval for shielded DEX support is massive and well-earned. To every ZODLer who voted approve - you're telling us shielded messaging matters. We hear you. To every ZODLer who voted reject - you're telling us we're not there yet. We hear you too. Both signals are valuable. The app needs more work. We need smoother UX, better wallet experience, and real-world reliability before we deserve community funding. No complaints. Just building. #Zcash $ZEC #ZChat #ShieldedTransactions #PrivacyMatters #grant






