Squidge Majora retweetledi
Squidge Majora
6.2K posts

Squidge Majora
@Valthorix
How do you know if someone uses Linux? Don't worry, they'll tell you.
Antarctica Katılım Ekim 2014
2K Takip Edilen51 Takipçiler
Squidge Majora retweetledi
Squidge Majora retweetledi

@planefag @LoesbyForIdaho I'm involved with a few game translation projects and we don't even have a releases tab, we just upload everything to a website every other week instead of directing everyone to the git.
English

@planefag @LoesbyForIdaho Because github ultimately isn't a distribution site, it's a code repository. People are supposed to either link the release direct download on another website or only use git for source code storage and version control.
English
Squidge Majora retweetledi
Squidge Majora retweetledi


@LoesbyForIdaho this is literally the whole issue; it's been decades and I still don't know how to get to the releases page from the top level page.
github.com/DFHack/dfhack
like where's the hyperlink? what do you do here
English
Squidge Majora retweetledi

‼️🚨 BREAKING: An AI found a Linux kernel zero-day that roots every distribution since 2017. The exploit fits in 732 bytes of Python. Patch your kernel ASAP.
The vulnerability is CVE-2026-31431, nicknamed "Copy Fail," disclosed today by Theori. It has been sitting quietly in the Linux kernel for nine years.
Most Linux privilege-escalation bugs are picky. They need a precise timing window (a "race"), or specific kernel addresses leaked from somewhere, or careful tuning per distribution. Copy Fail needs none of that. It is a straight-line logic mistake that works on the first try, every time, on every mainstream Linux box.
The attacker just needs a normal user account on the machine. From there, the script asks the kernel to do some encryption work, abuses how that work is wired up, and ends up writing 4 bytes into a memory area called the "page cache" (Linux's high-speed copy of files in RAM). Those 4 bytes can be aimed at any program the system trusts, like /usr/bin/su, the shortcut to becoming root.
Result: the next time anyone runs that program, it lets the attacker in as root.
What should worry most: the corruption never touches the file on disk. It only exists in Linux's in-memory copy of that file. If you imaged the hard drive afterwards, the on-disk file would match the official package hash exactly. Reboot the machine, or just put it under memory pressure (any normal system load that needs the RAM), and the cached copy reloads fresh from disk.
Containers do not help either. The page cache is shared across the whole host, so a process inside a container can use this bug to compromise the underlying server and reach into other tenants.
The original sin was a 2017 "in-place optimization" in a kernel crypto module called algif_aead. It was meant to make encryption slightly faster. The change broke a critical safety assumption, and nobody noticed for nine years. That bug then rode every kernel update from 2017 to today.
This vulnerability affects the following:
🔴 Shared servers (dev boxes, jump hosts, build servers): any user becomes root
🔴 Kubernetes and container clusters: one compromised pod escapes to the host
🔴 CI runners (GitHub Actions, GitLab, Jenkins): a malicious pull request becomes root on the runner
🔴 Cloud platforms running user code (notebooks, agent sandboxes, serverless functions): a tenant becomes host root
Timeline:
🔴 March 23, 2026: reported to the Linux kernel security team
🔴 April 1: patch committed to mainline (commit a664bf3d603d)
🔴 April 22: CVE assigned
🔴 April 29: public disclosure
Mitigation: update your kernel to a build that includes mainline commit a664bf3d603d. If you cannot patch immediately, turn off the vulnerable module:
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || true
For environments that run untrusted code (containers, sandboxes, CI runners), block access to the kernel's AF_ALG crypto interface entirely, even after patching. Almost nothing legitimate needs it, and blocking it shuts the door on this whole class of bug...

English

@moonjelly0 Is this your way of telling us that you're craving the blue chalk again?
English
Squidge Majora retweetledi

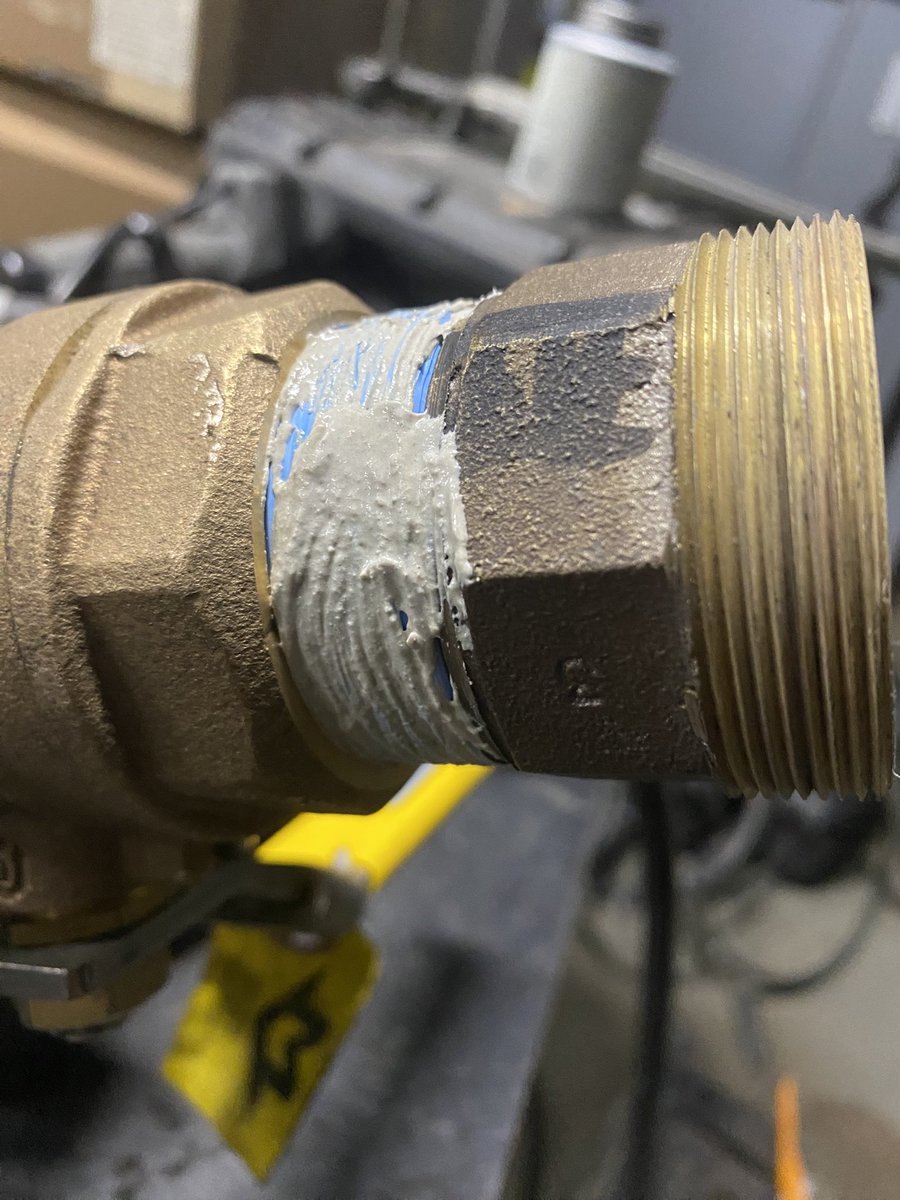
Anytime I work with CuNi and Brass threads i remove the factory installed teflon wrapping, even if it was rewrapped by a pipefitter before me
I’m sorry guy before me, I’m sure you know how to handle your CuNi, but the last time I trusted someone else’s handling of CuNi, it was wrapped like 20 times it was basically solid, without Jet-Lube too!
So i’ll trust my own handling of CuNi bro


English
Squidge Majora retweetledi

gonna be honest with you I already forgot how I drew this
do not expect something like this for the next 8 months thanks
anon@betanonbeet
English
Squidge Majora retweetledi

Just got done talking at Georgia Institute of Technology.
I was introduced to a bunch of cybersecurity students as "cybercrime TMZ", a person who "collects pictures of cats", "fills computers with mayonnaise", and discusses things with "Dragon Ball Z" references.
On paper this shit makes me look like a lunatic.
The entire room was dead silent as I vaped and spoke schizophrenic nonsense.
Chat, I DO NOT think they'll be inviting me back
English

@nonregemesse @RadioRed77 There's nothing accidental with that dress and we both know it
English

@RadioRed77 You want me to post a woman’s accidentally exposed underwear uncensored? Pervert
English

Do these women not at least walk around in their dresses for a bit to see if they’re going to end up exposing themselves?


Star crave@starcravingspr
Giulia Salemi at the venice film festival
English
Squidge Majora retweetledi

“…..100 POUNDS CLARK.”
“Look, Bruce, I don’t know what to tell you.”
“Clark, I spent 500 million dollars on four pieces of Kryptonite.”
“Wait what-“
“AND JASON HAS A HUNDRED POUNDS”

Gunner Dobbins (Dunk and Egg era)@GunnerDobbins
“Bruce, it’s a very rare stone.” “Rare my ass Clark, there’s like 12 different flavors and I saw a couple of goons with some the other day, it’s really easy to get.”
English
Squidge Majora retweetledi
Squidge Majora retweetledi
Squidge Majora retweetledi

Squidge Majora retweetledi