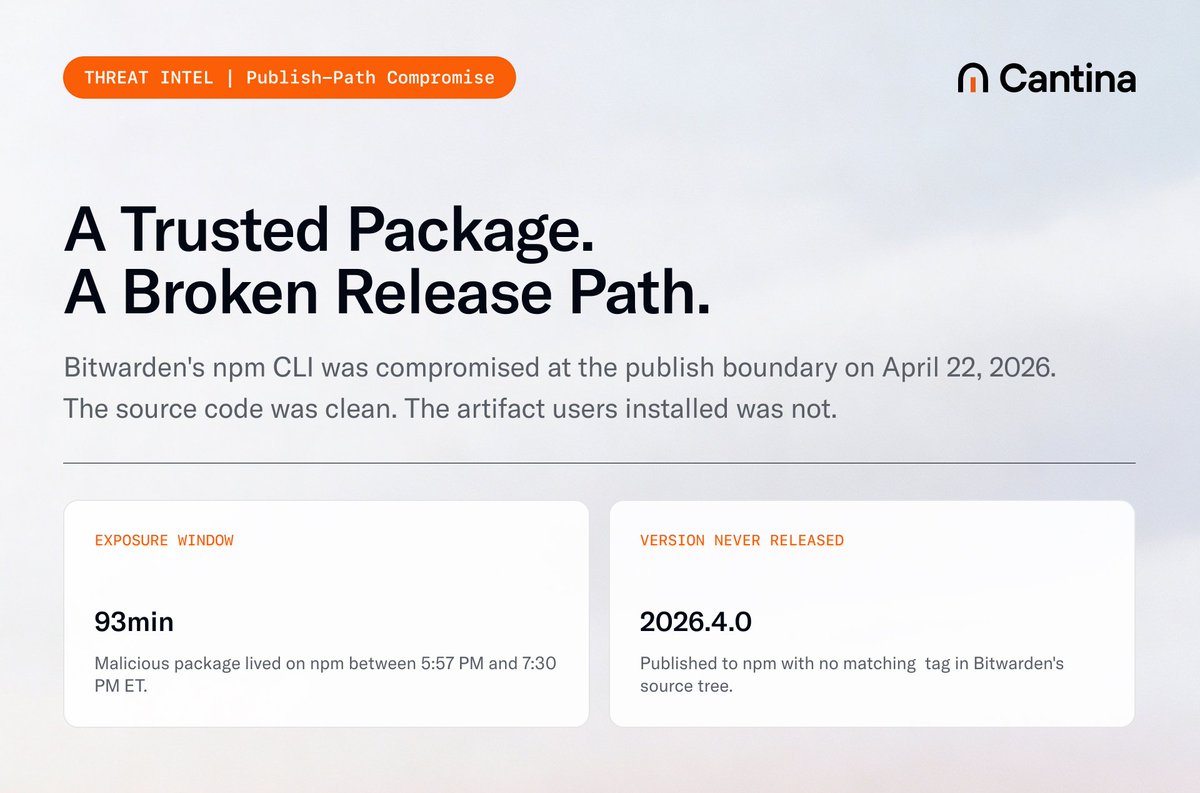
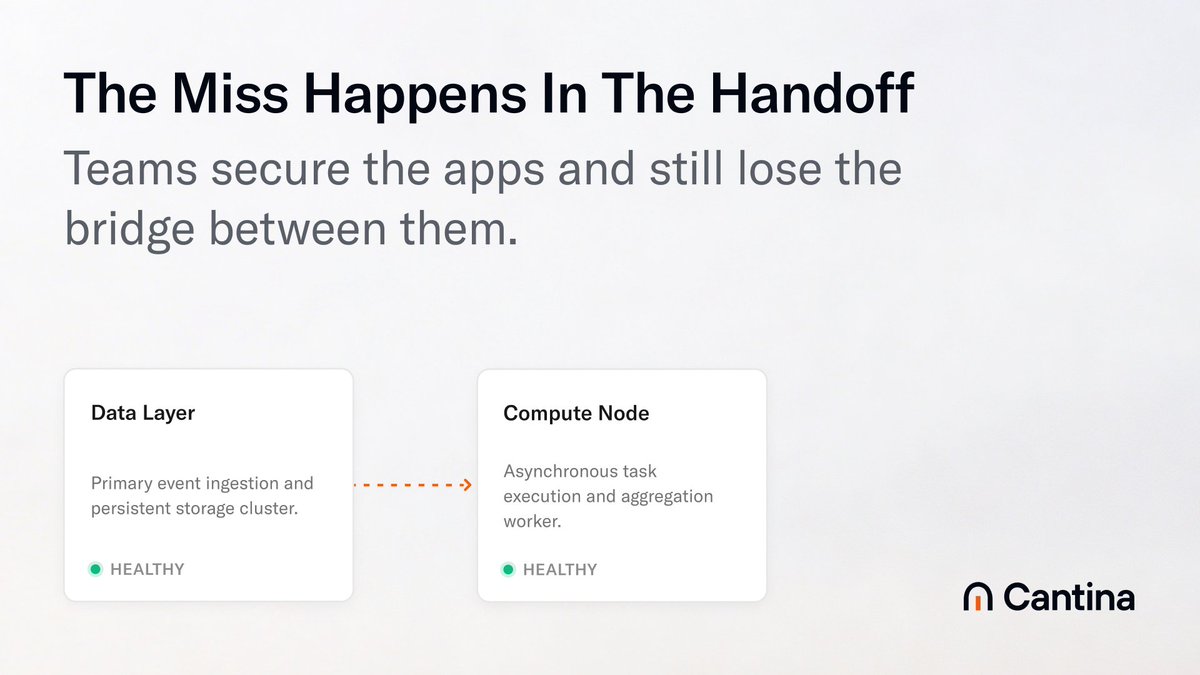
We’ve detected that @GitHub has been compromised by TeamPCP. A poisoned VS Code extension on an employee device. ~3,800 internal repos exfiltrated. Data already on a black forum for $50K. The technical vulnerability is two words: "runOn": "folderOpen" in a .vscode/tasks.json. Cursor plays with Workspace Trust OFF by default. Open the folder, the task fires. Same group hit @Tan_Stack, @OpenAI, @Microsoft, and Nx in the prior 3 weeks. Same blind spot in every IDE-scanning security stack. What a time for cybersecurity! Full breakdown: cantina.review/github