Xanderux
360 posts
Xanderux
@Xanderuxsf5
Threat intelligence analyst | #infosec Cyber threat intel community: https://t.co/5u7OdssOHI lolweb maintainer : https://t.co/sPciJFVGcN

See what attackers see. Act fast. ThreatLens enters beta: Human-led intel - Refined daily. Includes: • Domain/IP scans • Phishing detection • External vuln priorities • Compromised creds • VIP monitoring + human debriefs Signal over noise. DM for access.




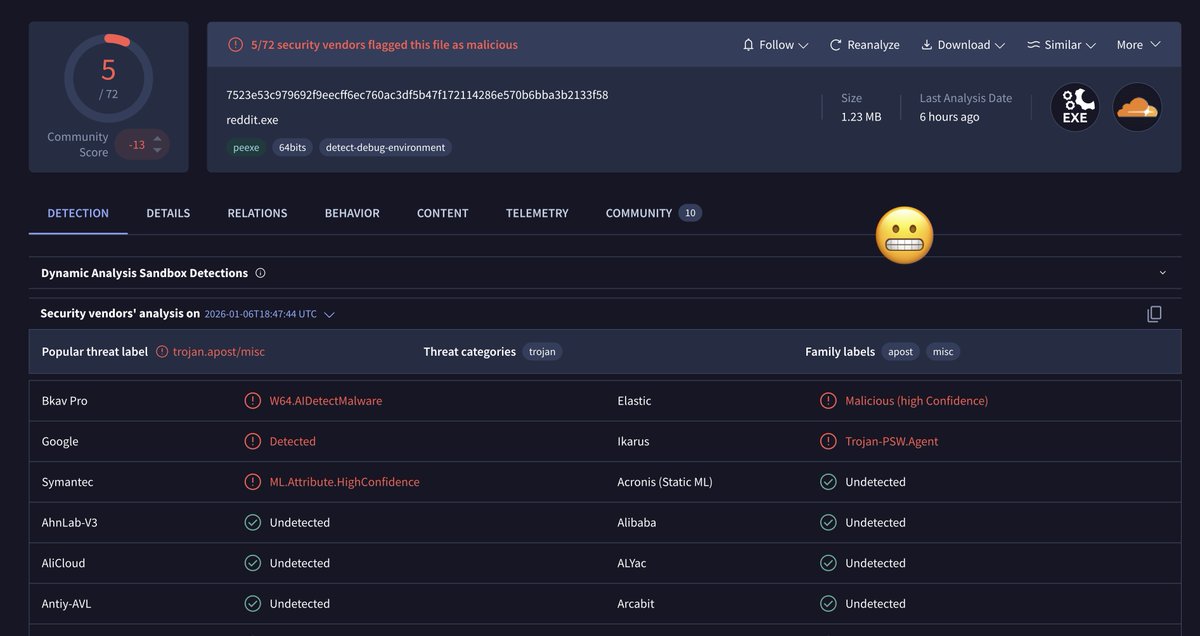


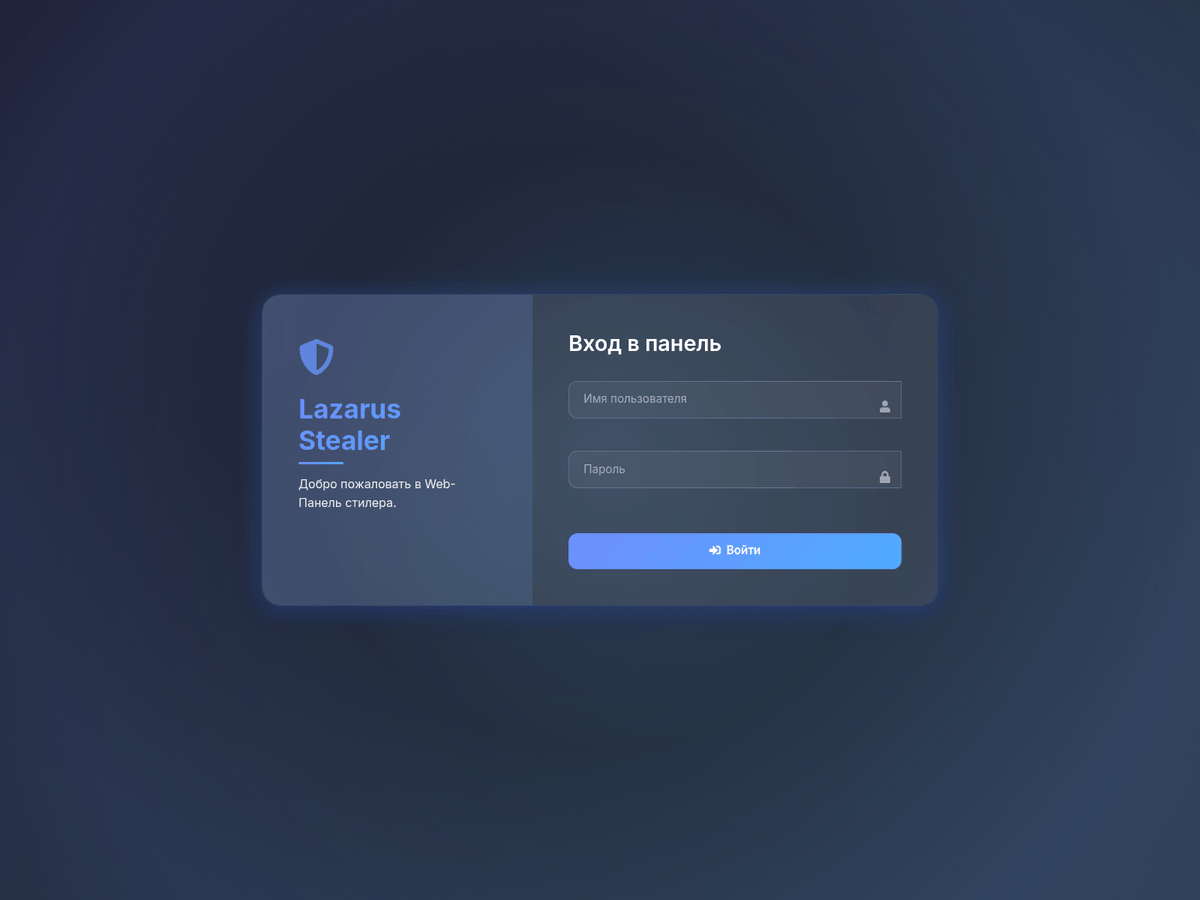



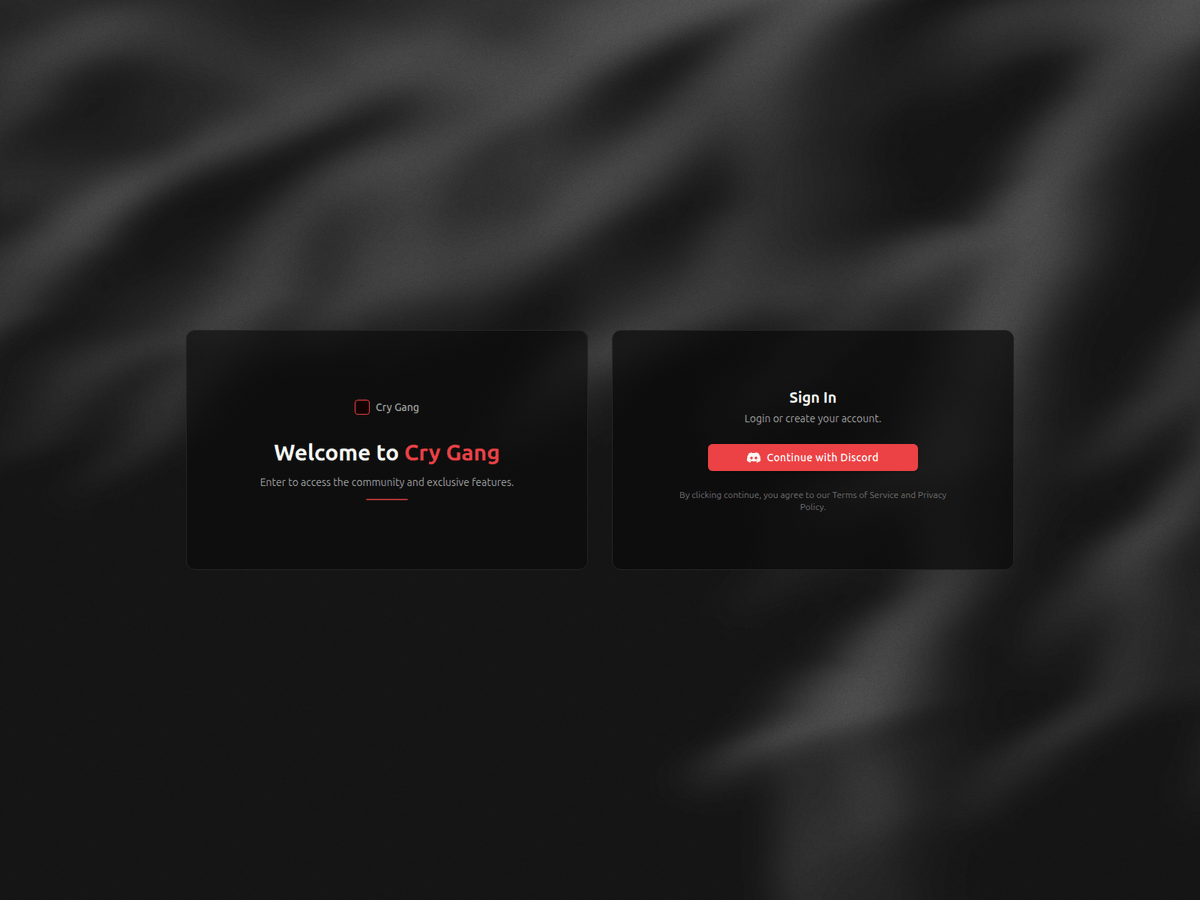

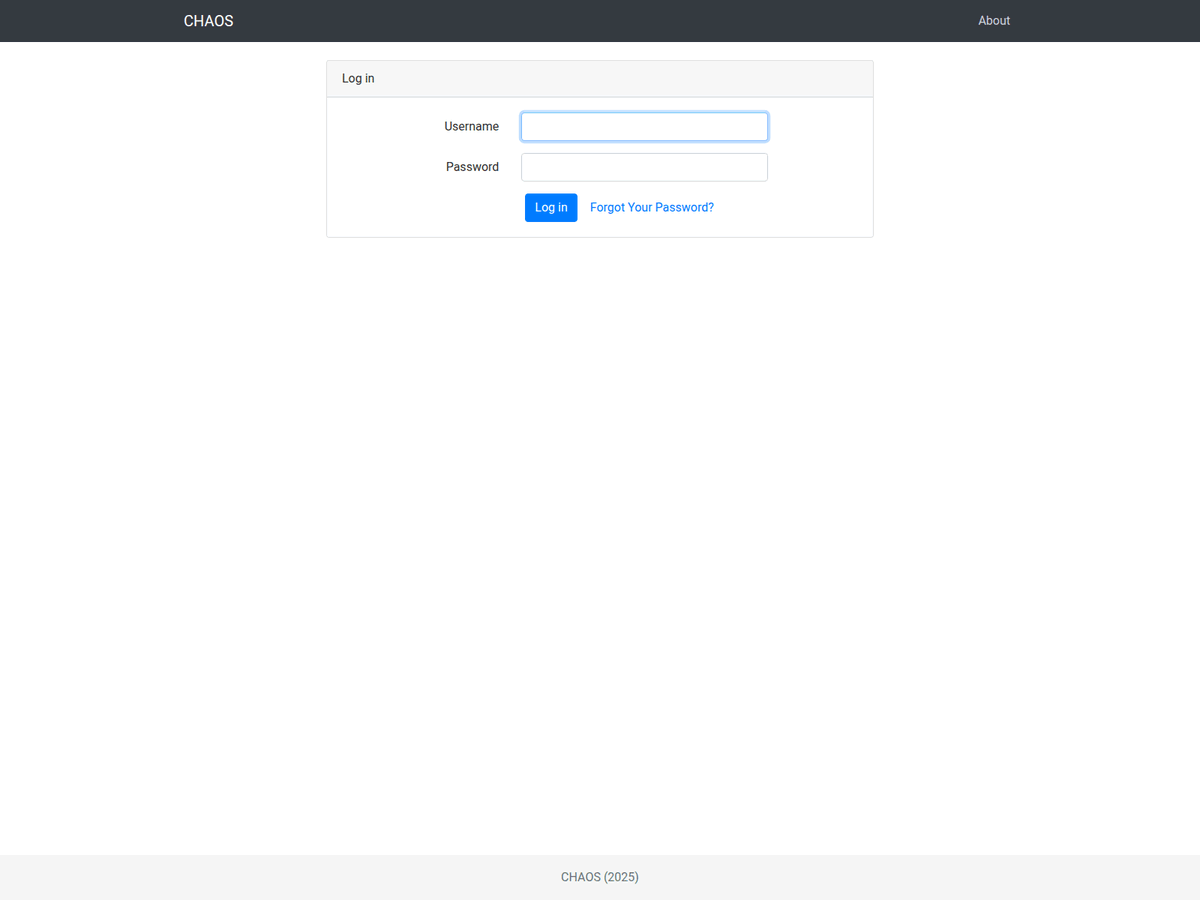
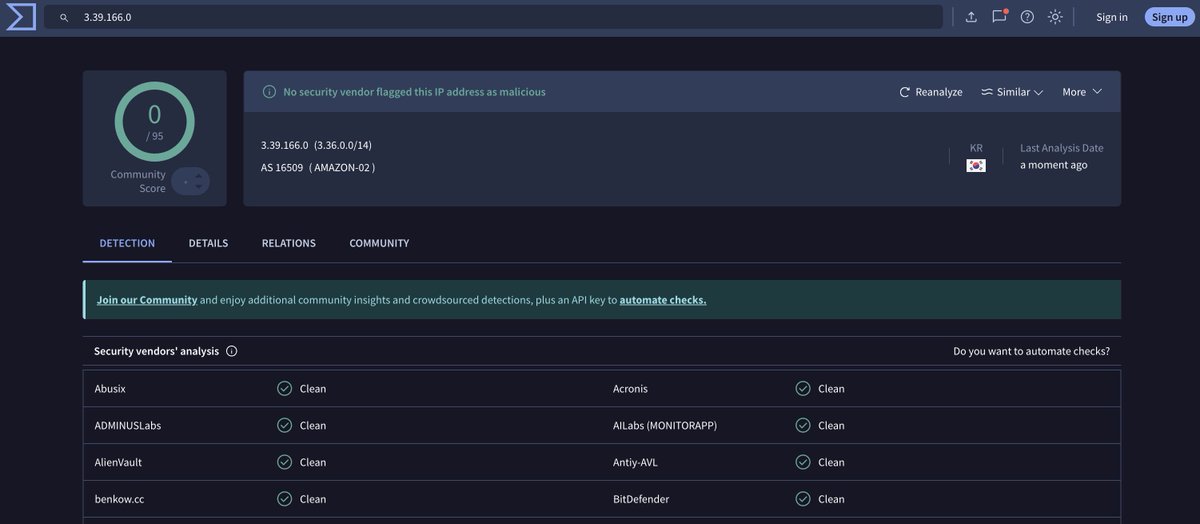
Cry Stealer by Cry Gang http[://142.44.179.180[:9999/login http[://142.44.179.180[:3000/ virustotal.com/gui/file/11147…

Cloudflare has started blocking proxy tools like Burp Suite. If you encounter this error, download the “Bypass Bot Detection” extension from the BApp Store in Burp Suite. It should resolve the issue for Burp Suite.