@n_o_t_h_a_n_k_s People should listen to @n_o_t_h_a_n_k_s . Because @n_o_t_h_a_n_k_s knows...
EVERY TIME
English
Vangelis tix Stykas
5.7K posts
@evstykas
Father of two sons and ARIS fan. Named NOT A UNICORN!🦄 IDOR as a service. @_ifigeneia husband @atroposai jack of all trades Never ethical , mostly legal...





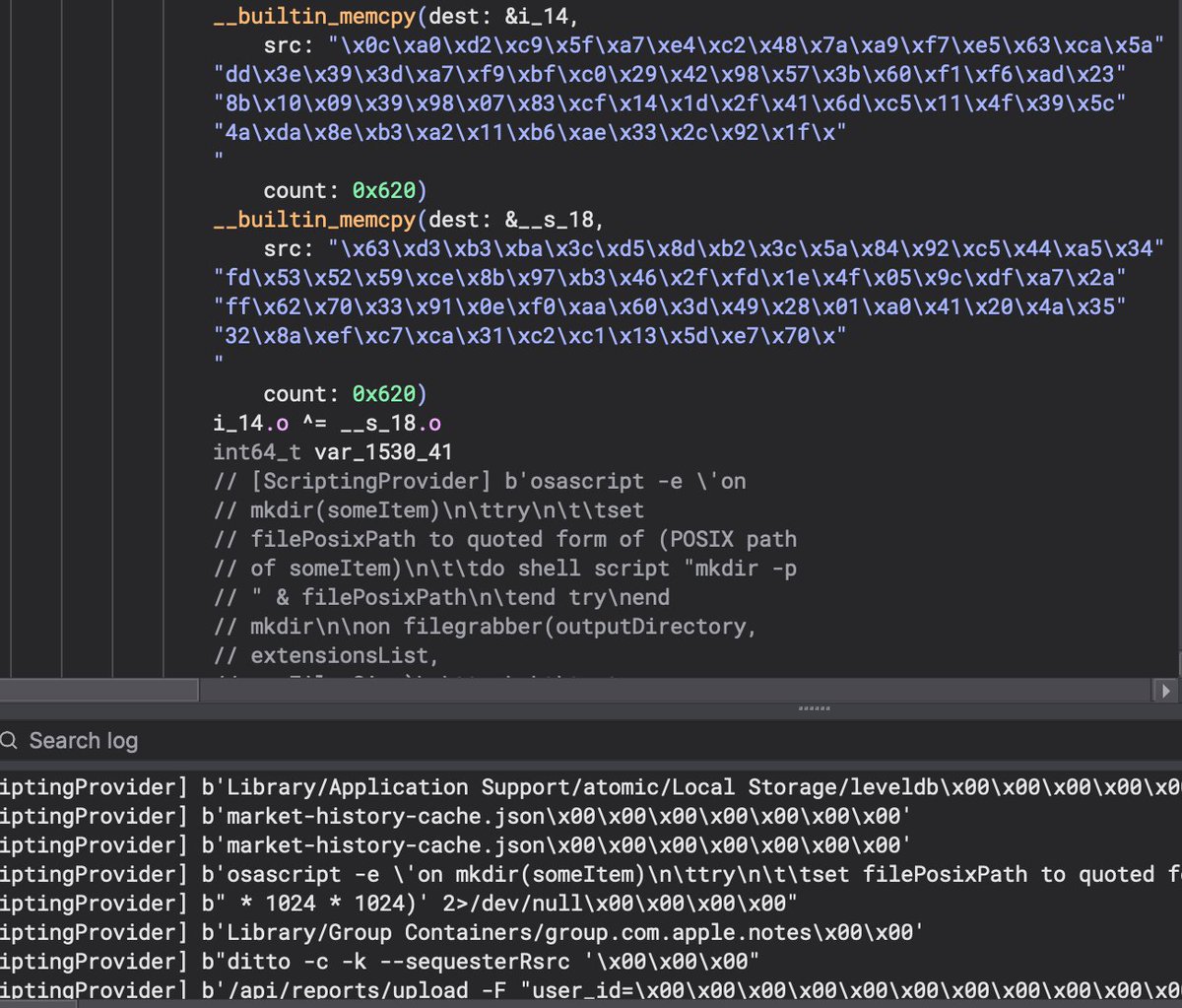
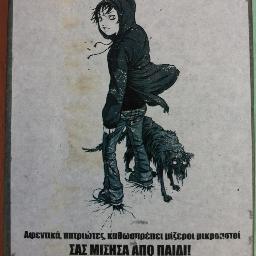
Ah, this screen brings back memories.

Zscaler ThreatLabz has published a deep dive into APT attacks targeting members of the Indian government. The campaign, which we named Gopher Strike, leverages several previously undocumented tools. These include GOGITTER as an initial downloader, GITSHELLPAD backdoor for C2 communication, and GOSHELL used to deploy a Cobalt Strike Beacon. Read our full technical analysis here: zscaler.com/blogs/security…