Stefan Schmidt retweetledi
Stefan Schmidt
12.8K posts


Stefan Schmidt
@Zap42
🎧 🛀 🌌 👽☁ full stack begins at layer 1 | high speed copy&paste | only DNS is truly web-scale | his password ¯ \ _ (ツ) _ / ¯ @[email protected]
Berlin, Germany Katılım Kasım 2007
2.3K Takip Edilen627 Takipçiler
Stefan Schmidt retweetledi
Stefan Schmidt retweetledi

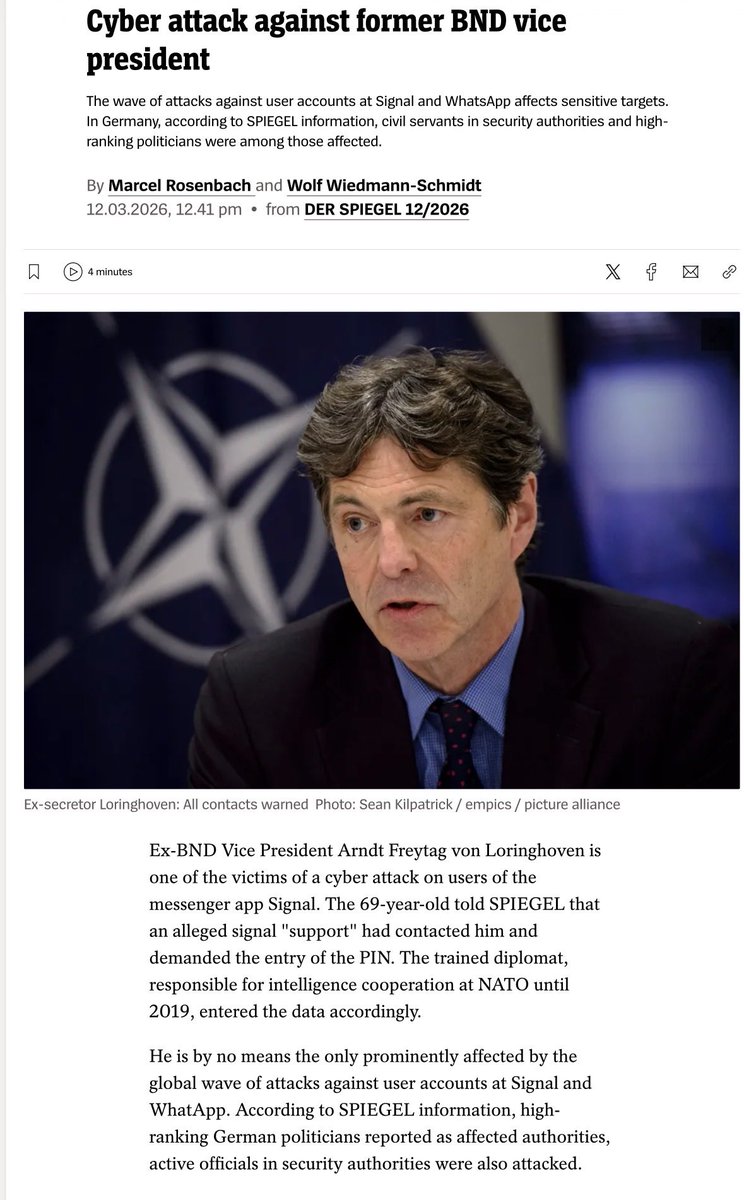
Ex-BND (German Foreign Intelligence Service) deputy chief Arndt Freytag von Loringhoven received a message from fake Signal “support” asking for his PIN. He typed it in.
His contacts then got a malicious link through his hijacked account.
He’s a former NATO intelligence chief, and the author of a book called Putin’s Attack on Germany, where he apparently covers Russian cyberattacks.
He fell for a fake customer service message.
English
Stefan Schmidt retweetledi

If you use a personal phone/laptop for your work, pay very close attention to this little detail.
Iran attackers wipe 200k devices at a company called Stryker. Within those devices appears to be employees PERSONAL devices.
The attackers used the company’s MDM software, which is basically IT management software running on everything. It’s an incredibly attractive backdoor to an attacker. I successfully targeted MDM software for several Red Team engagements. It’s… lots of fun :)
Anyway, a lot of companies require you to install their MDM software on your personal devices before you can access resources like Corp email. It’s used to keep devices updated, lock things down if they get stolen, etc. The company often promises that they won’t access personal data, erase any personal data, etc. But this is often ONLY POLICY. If a bad actor gains access to the MDM tool, as was the case here, then anything can happen.
People should be aware of these risks. I refused to run MDM software on any of my personal devices. The company needs to provide me with hardware if they want that. I personally isolate all corp devices to their own network too. If an adversary can get into the corp laptop, then can then get inside my network… there have been cases of it happening in the past.
Kim Zetter@KimZetter
I've published more details about the cyberattack in this piece: zetter-zeroday.com/iranian-hackti…
English

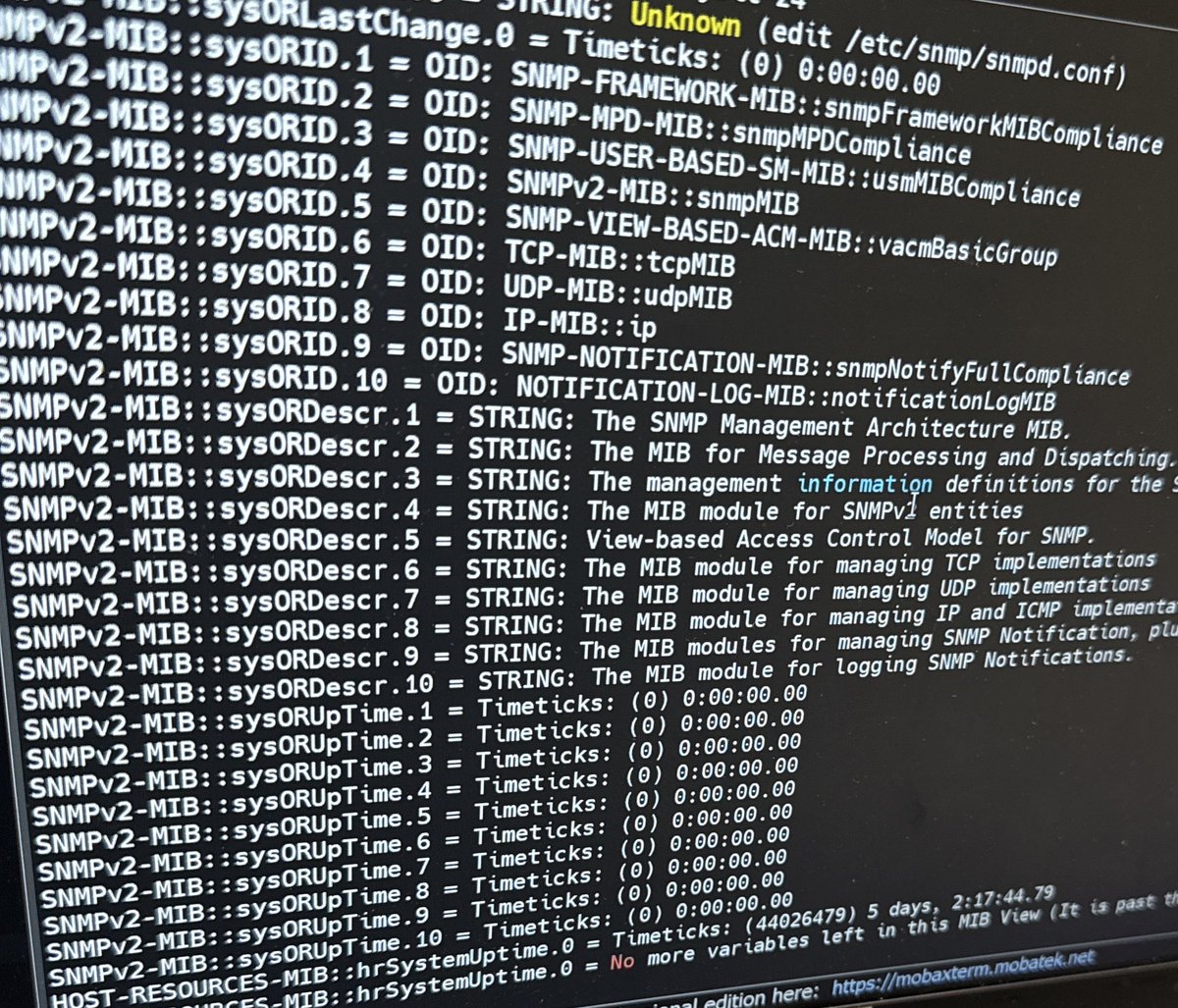
@TheIcelandGuy Open recursive server is not much of an issue in my experience (29670) but of course it depends on size of the customer base. If you can limit access to the fabric even better. I'd put a dnsdist in front for rate limits or blocks on a whim. 1-2GB of RAM is usually enough.
English

@Zap42 I’d like to offer faster local recursion available to anyone connected to a switch fabric/ixp. Google isn’t sending a resolver anytime soon so “self help”. Plenty of CPU+RAM to put to work. Abuse is the challenge. Or is it?
English

If you can’t get access to a localized dns resolver like 1.1.1.1/8.8.8.8/etc is there a roll your own alternative that makes sense? #dns #networkperformance
English
Stefan Schmidt retweetledi

blog.recurity-labs.com/2026-03-02/Far…
If you have any fond memories of FX, the lovely team at Recurity Labs would love to hear from you
English

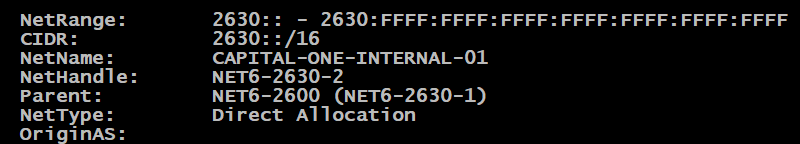
@quelltexten An der Theorie mit zu gross zum scannen koennte was dran sein. Mein aktuelles fail2ban log sagt fuer IPv6 keine Eintraege bei ssh aber welche fuer exim.
Deutsch
Stefan Schmidt retweetledi

Let's talk ports. Aside from 80 and 443 what is your favorite networking port and why? #CloudflareChat
English