Sabitlenmiş Tweet
Mabior Agau
1.9K posts


Mabior Agau
@_CyberMaster
Experienced Cybersecurity geek | Passionate about Shoring Up Vulnerabilities and Protecting Against Threat Actors | Dedicated to Safeguarding Digital Assets
Error: can't find the location Katılım Mayıs 2020
611 Takip Edilen324 Takipçiler
Mabior Agau retweetledi

🚨 BREAKING: cPanel and WHM, the control panels behind an estimated 70+ million websites, have a critical security flaw that lets anyone become root admin without a password. CVE-2026-41940 affects every supported version. It’s already being exploited in the wild.
watchTowr Labs published the full attack today, after the hosting company KnownHost confirmed the bug was already being used to break into a significant chunk of the internet.
If you've never heard of cPanel: it's the dashboard that hosting providers and millions of website owners use to manage their servers, domains, email accounts, databases, and SSL certificates. WHM is the admin version that controls the entire server. If someone gets root access to WHM, they get the keys to the kingdom and to every apartment inside it.
How the attack works, in plain English:
🔴 Step 1: The attacker sends a deliberately wrong login. cPanel still creates a temporary "you tried to log in" record on disk and gives the attacker a cookie tied to it.
🔴 Step 2: The attacker tweaks the cookie to disable cPanel's password encryption. Normally cPanel encrypts the password field on disk. With one small change to the cookie, cPanel just stores it as plain text instead.
🔴 Step 3: The attacker sends a fake login attempt where the password field secretly contains hidden line breaks. cPanel does not strip these line breaks out, so they get written straight to the session file. Each line break creates a brand new fake record. The attacker uses this to inject lines that say "this user is root" and "this user already authenticated successfully."
🔴 Step 4: The attacker visits one more random page on the site to nudge cPanel into re-reading the file. cPanel then promotes the injected fake lines into its main session memory.
🔴 Step 5: On the next request, cPanel sees a flag that says "this user already passed the password check." cPanel trusts that flag, skips checking the actual password, and lets the attacker in as root.
From start to finish, the attack takes a handful of HTTP requests.
If you run cPanel or WHM, the patched versions are:
🔴 cPanel/WHM 110.0.x → 11.110.0.97
🔴 cPanel/WHM 118.0.x → 11.118.0.63
🔴 cPanel/WHM 126.0.x → 11.126.0.54
🔴 cPanel/WHM 132.0.x → 11.132.0.29
🔴 cPanel/WHM 134.0.x → 11.134.0.20
🔴 cPanel/WHM 136.0.x → 11.136.0.5
If your version is older than these, assume someone has already broken in and act accordingly. Patch right now, then rotate every password and key the server touched: root passwords, API tokens, SSL private keys, SSH keys, mail passwords, and database passwords.


English
Mabior Agau retweetledi

MICROSOFT IGNORED HIM. NOW YOUR PC PAYS FOR IT
One researcher reported a critical Defender vulnerability privately. Microsoft dismissed it. So he published it - then dropped 2 more in 13 days.
The latest is called RedSun. It's unpatched. It works 100% reliably on Windows 10, 11 and Server right now.
It doesn't bypass your antivirus. It uses your antivirus as a weapon.
Defender tries to restore a flagged file - the exploit redirects that write into C:\Windows\System32. No admin. No popup. SYSTEM access in seconds.
-> BlueHammer - patched
-> UnDefend - breaks Defender updates forever
-> RedSun - unpatched, public PoC on GitHub
His message to Microsoft: "I was not bluffing. And I'm doing it again."
RCE is reportedly next. That one needs zero physical access.
impulsive@weezerOSINT
Windows defender has been compromised. right now there is a public unpatched exploit that gives any app on your windows PC full system admin access. no password. no popup. nothing your antivirus doesnt stop it. your antivirus IS the exploit. windows defender is the attack vector ransomware gangs can use this to encrypt your entire machine and steal every saved password, browser session, and discord token you have. fully patched windows 11. real time protection on thread
English

In South Sudan, holding public office is viewed as an opportunity to benefit one's community, rather than simply a civic responsibility. Communities heavily rely on their sons and daughters in government to secure financial support and other advantageous opportunities.
A government appointee from a specific community is regarded as a valuable asset, providing unparalleled access to essential resources and employment prospects. Upon appointment, community members gather at the appointee's residence to display loyalty, and resources are swiftly mobilised to stage celebrations, including congratulatory messages in newspapers and on billboards. Praise and songs are composed in honor of the appointee, as if he had won an election, despite being appointed by an individual. Entrepreneurs shower him with gifts, such as cars and hotel suites, in anticipation of lucrative contracts and kickbacks.
During the appointee's tenure, many community members transform into sycophants and self-appointed defenders. However, when the appointee is decreed out, the façade crumbles and allegiances dissolve.The sycophants then redirect their attention to the next appointee, initiating a fresh cycle of fervor.
Honestly, to fix this beloved country won't be easy at all, even after the fall of the baobab tree. It will require more than statesmanship, but also total liberation. If this post hurts you, I’m sorry! take a glass of cold water and you will be fine. #SSOX

English

@Miyen_mimdit These Zionists and Uncle Sam underestimated the Iranians, now they are panicking on how to get an offramp to end this conflict but can't get one. LOL.
English
Mabior Agau retweetledi

The U.S. Justice Department participated in a court-authorized law enforcement operation to disrupt Command and Control (C2) infrastructure used by the Aisuru, KimWolf, JackSkid, and Mossad Internet of Things (IoT) botnets.
The operation was conducted simultaneously with law enforcement actions conducted in Canada and Germany, which targeted individuals who operated these botnets. The four botnets launched Distributed Denial of Service (DDoS) attacks targeting victims around the world. Some of these attacks measured approximately 30 Terabits per second, which were record-breaking attacks. @FBIAnchorage
Read More: justice.gov/usao-ak/pr/aut…
English
Mabior Agau retweetledi

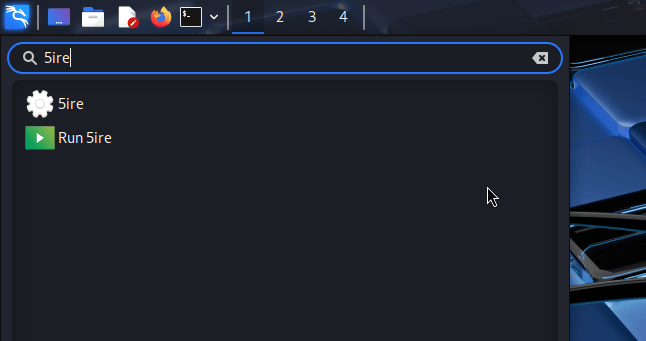
Kali & LLM: Completely local with Ollama & 5ire: We are extending our LLM-driven Kali series, where natural language replaces manual command input. This time however, we are doing everything locally and offline. We are using our own hardware and not… kali.org/blog/kali-llm-…
English
Mabior Agau retweetledi

@Miyen_mimdit Western hypocracy and double Standards is just so insane to the extent that an average person will will just notice how insane it is without any second thoughts. All these so called international bodies the likes of FIFA, UN etc are being exposed.
English

@_CyberMaster Now, international law and order is ineffective and only work for a few and the rest either fall in line or are eliminated.
English
Mabior Agau retweetledi

Mabior Agau retweetledi
Mabior Agau retweetledi

Exclusive: Obtained Starlink terminal debug data from Iran during the ongoing internet shutdown.
The telemetry shows direct evidence of GPS spoofing: the dish detected 18 GPS satellites with valid signal lock, but activated its anti-spoofing countermeasures (inhibitGps: true). This isn't simple jamming; the government appears to be broadcasting fake GPS signals to confuse terminals.
The impact: 20%+ sustained packet loss, connection never stabilized after 24 minutes, bandwidth restricted, and beam pointing ~1° off target. Starlink stayed online but was barely usable.
The anti-spoofing detection works, but SpaceX's fallback positioning can't currently maintain normal performance under electronic warfare.
First documented technical evidence of state-level GPS spoofing against consumer satellite internet.
github.com/narimangharib/…

English

@MickyJnr__ That Group D would be beyond being called the Group of Death.
English

Technical rehearsal before the official group stage draw.
The main draw starts in 4 hours! ⏳
Here’s how the test draw looked 👇🏽
Group A:
🇿🇦 Mamelodi Sundowns
🇹🇿 Yanga SC
🇩🇿 MC Alger
🇨🇩 St Eloi Lupopo
Group B:
🇲🇦 RS Berkane
🇸🇩 Al Hilal
🇦🇴 Petro Luanda
🇲🇱 Stade Malien
Group C:
🇪🇬 Al Ahly
🇹🇿 Simba SC
🇳🇬 Rivers United
🇿🇲 Power Dynamos
Group D:
🇹🇳 ES Tunis
🇪🇬 Pyramids FC
🇲🇦 AS FAR
🇩🇿 JS Kabylie
The official Champions League group stage draw takes place later today & that’s when the real groups will be confirmed.
#CAFCLwithMicky • #CAFCCwithMicky

English

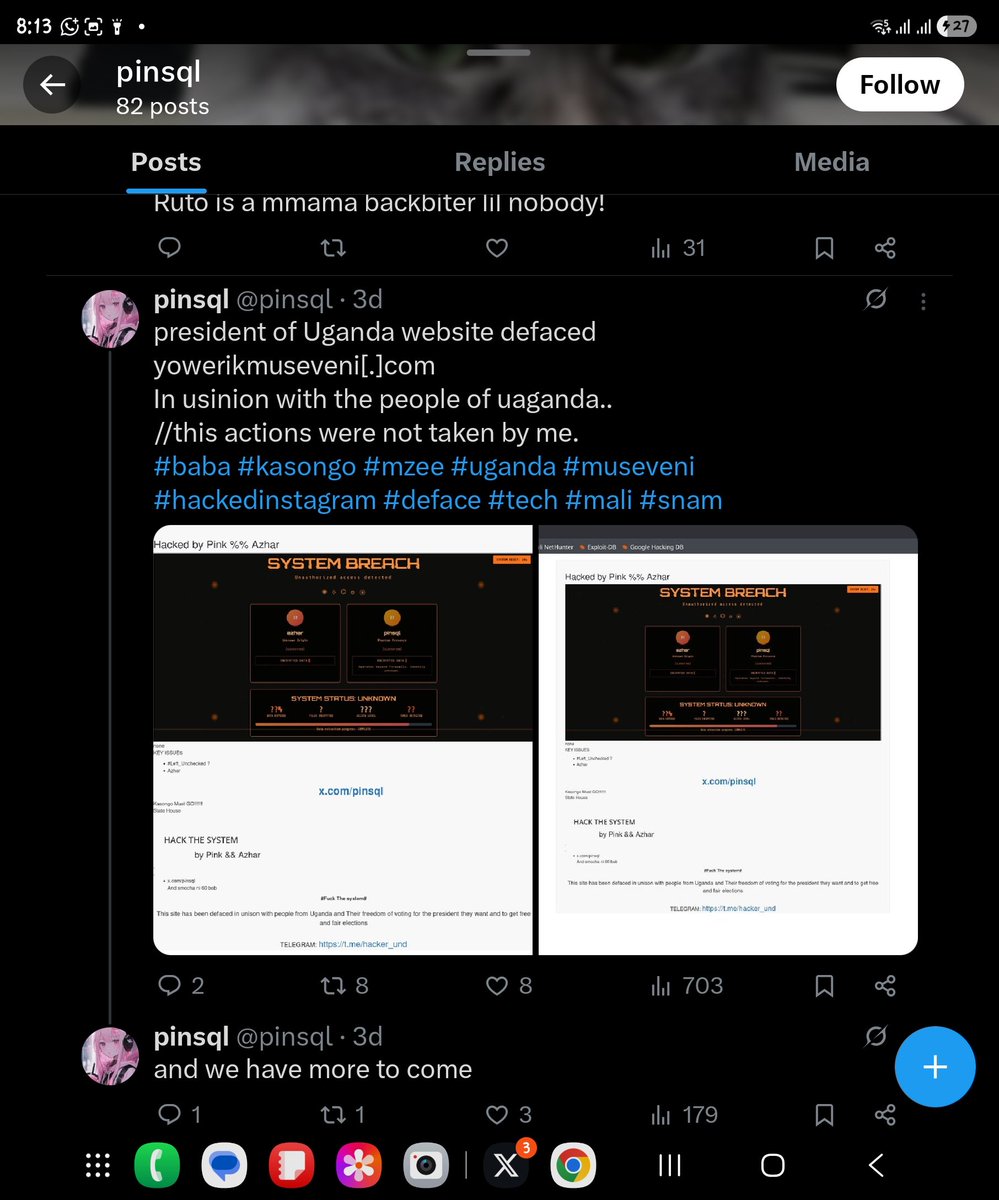
@pinsql @KagutaMuseveni @ntvuganda @nbstv @newvisionwire I'm curious how you pulled that off so easily without anyone noticing. That tells me how vulnerable that site must have been, mate!!
The maintainer/developer must be sweating somewhere.
English

It has been reported that the website of @KagutaMuseveni has allegedly been #Hacked by an anonymous entity known as @pinsql. According to a post by @pinsql on X, the incident occurred three days ago. As of the current time, the compromised content remains visible on the account.

English

@TeamYouTube Here is the URL to the channel. Thanks for the response, and I look forward to the best.
@slatinepro?si=y59Qr2UM-HE0i5Nn" target="_blank" rel="nofollow noopener">youtube.com/@slatinepro?si…
English

@_CyberMaster So sorry you're going through this. We need to get some information from you to share with the team in charge of restoring accounts. Can you share your channel URL so we can take a look?
English
Mabior Agau retweetledi





