Sabitlenmiş Tweet
KrisHunter
18.6K posts


KrisHunter
@_KrisHunter_
The IP Hunter, counter-influencer, & veteran. Mission to uncover deception. Their deception is to alter your perception. Geopolitical analyst.
CA Katılım Temmuz 2010
6.9K Takip Edilen13.4K Takipçiler

The Foundational Maxim
"A Law repugnant to the Constitution is void"
This is the seminal maxim established in Marbury v. Madison, 5 U.S. 137 (1803), where Chief Justice John Marshall declared: "a law repugnant to the Constitution is void" and "courts, as well as other departments, are bound by that instrument."
We must always remember that the Constitution is the supreme law of the land. Congress can try to pass stuff and say it's passed, but if it's contrary to or against the Constitution's authority, it is null and void. It's just like when the President signs executive orders that are against the law, they are against the law.

English
KrisHunter retweetledi
KrisHunter retweetledi

I am officially announcing: ALIENS GAVE ME THE TECH #aliens #nhi #uap #ufo #science @rosscoulthart @AmericanALCHMY
English
KrisHunter retweetledi

Intelligence and Privacy in the Digital Age: How the Surveillance State Infiltrates Social Media, Phones, and Minds
Executive Summary State intelligence agencies, foreign partners, and third, party contractors have built hidden channels that bypass every privacy control user think they have. This paper examines three proven vectors, ultrasonic “data,over,audio” tracking, in, flight GSM interception, and psychological online deception operations, drawn directly from NSA/GCHQ documents and peer, reviewed research. These tools were already operational by 2008–2018 and are still active today. The same research that exposed them also points to the only durable hardware countermeasure: a diamond, based processor with native THz phonon detection that can neutralize these threats at the physical layer.
I. Ultrasonic Monitoring – The Silent “Data Over Audio” Channel Smartphones are turned into always, on microphones and speakers for inaudible cross, device tracking. Research from St. Pölten UAS (2017–2018) proved that apps or the OS itself can emit and receive ultrasonic signals (above 20 kHz) to create “acoustic cookies.” These pair devices merge user profiles, and feed targeted ads or content filtering, all without any visible notification.
SoniControl gave users the first real defense: a real, time firewall that detects the ultrasonic beacon and blasts interference through the loudspeaker to kill the cookie. SoniTalk followed as an open, source private protocol. Both projects later disappeared from app stores, a pattern familiar to anyone who dug into these issues in 2018.
II. In, Flight GSM Surveillance – “Owning the Air” While passengers believe they are just using airplane Wi-Fi or onboard GSM, intelligence agencies are running full VLR/HLR tracking through pico,cells linked via SATCOM to ground stations. The NSA/GCHQ briefing “In, Flight GSM” (S32423/S3T1) details exactly how they map Mobile Subscribers in real time.
Key capabilities documented:
DISHFIRE for “Welcome onboard” SMS harvesting
CHALKFUN for flight confirmation
FASTSCOPE for travel timelines
Association queries linking IMSI/MSISDN to specific aircraft
Usage exploded from zero to 160,170 tracked events by March 2009. The same infrastructure that lets you make a $3.99 call from 35,000 feet also hands your exact location and identity to Five Eyes partners the moment you cross a border.
III. Covert Online Operations – The “Art of Deception” Playbook GCHQ’s JTRIG (Joint Threat Research Intelligence Group) training deck “The Art of Deception” (HSOC) is the instruction manual for turning social media into a weapon. It teaches operatives to become “Cyber Magicians” using techniques borrowed straight from stage magic:
-Dissimulation (hide the real): Masking, Repackaging, Dazzling
-Simulation (show the false): Mimicking, Inventing, Decoying
The curriculum fuses psychology, sociology, anthropology, economics, and political science into “Online HUMINT,” strategic influence, and disruption/CNA. The goal is explicit: construct experiences in the target’s mind so they accept the narrative without realizing they were steered. This is exactly what was being deployed against audiences in 2018, the voice glitches, the sudden bans, the coordinated narrative pushes you and others documented live.
IV. The Hardware Gap, And the Only Real Countermeasure Critics of ultrasonic tracking often point out that cheap smartphone speakers and mics roll off above ~15 kHz. That limitation is real, which is why the surveillance state needs something more robust. The same crystal lattice that can detect and generate THz phonons natively (without mechanical roll, off) is the foundation of the HoloQuantaCore HG processor. Its piezoelectric harmonics and graceful, degradation holographic encoding give it built, in detection and neutralization of ultrasonic beacons, in, flight GSM side, channels, and the timing signatures of coordinated online deception campaigns. Radiation, hard, forever, durable, and room, temperature quantum, ready, it closes the exact gap these documents expose.
Conclusion The surveillance state does not need your permission. It rides in on inaudible sound, satellite, linked phone towers at 35,000 feet, and psychological “magic” that reshapes what you see on your timeline. The four documents examined here, SoniControl papers, NSA/GCHQ In, Flight GSM briefing, and the JTRIG deception curriculum, are not theory. They are the operational manuals that were already running while the public was still arguing about cookies and metadata.
The research that mapped these channels in 2018 is the same research that produced the first hardware layer capable of stopping them at the physical level. The HoloQuantaCore HG is not science fiction, it is the direct engineering answer to the surveillance architecture these agencies openly documented.

English
KrisHunter retweetledi

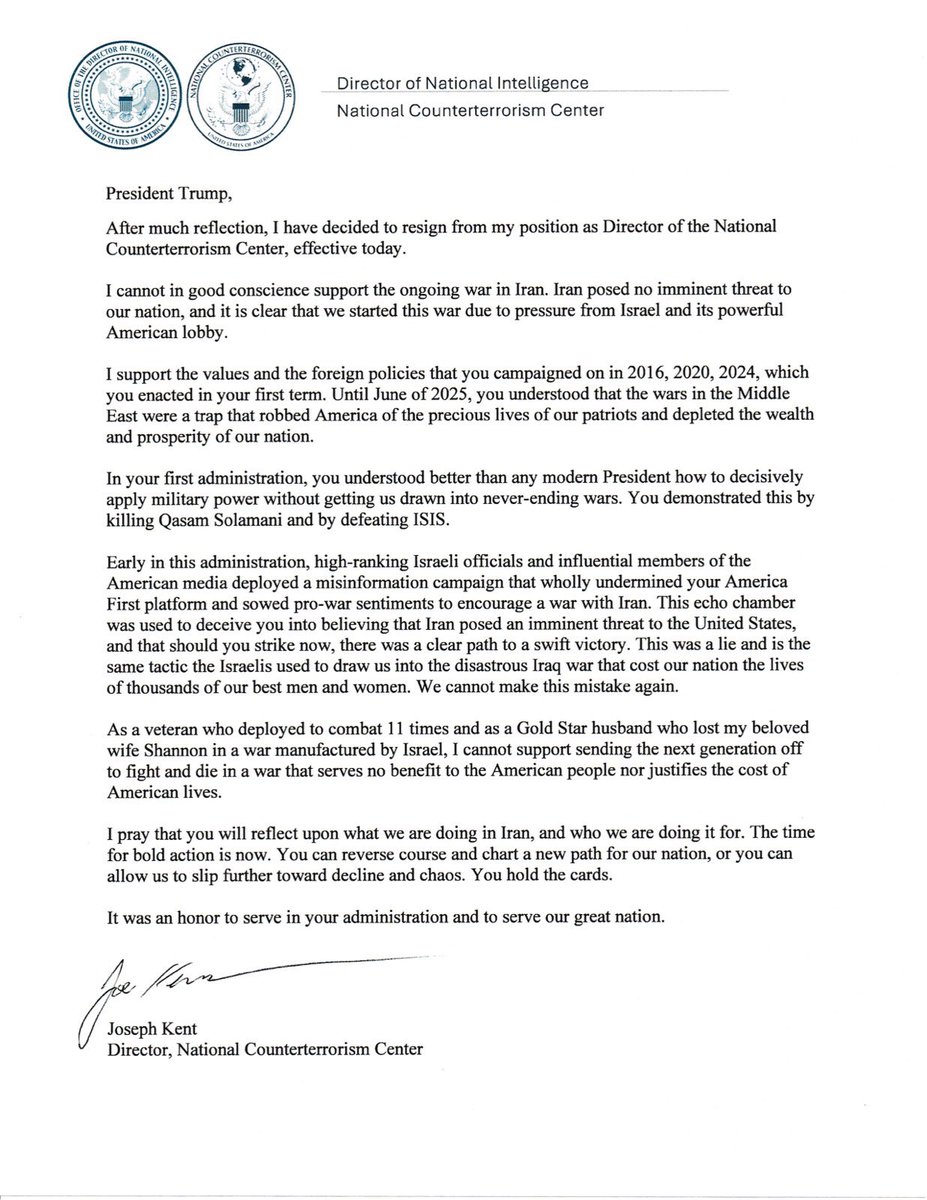
After much reflection, I have decided to resign from my position as Director of the National Counterterrorism Center, effective today.
I cannot in good conscience support the ongoing war in Iran. Iran posed no imminent threat to our nation, and it is clear that we started this war due to pressure from Israel and its powerful American lobby.
It has been an honor serving under @POTUS and @DNIGabbard and leading the professionals at NCTC.
May God bless America.
English

@MaricopaGOP @PatriotMarkCook I've always said elections should be simple either you get a vote or you don't that's it super simple it's not fucking rocket science there's no negative numbers involved. There's no need for proprietary secret software it's straightforward basic mathematics.
English

"Elections are not supposed to be complex or complicated. We literally fill dots out on paper, count the dots, add the dots up, & whoever has the most dots wins. That's the entire scope of our elections." —Election Integrity & Cybersecurity Subject Matter Expert @PatriotMarkCook
English

I watched the whole video, appreciate you sharing your spiritual take on consciousness, the soul, and that personal kitchen experience with the bright lights (sounds intense!). You're clearly passionate about this, but the connections are jumping all over the place and it's making the AI part confusing, so let's clarify it point by point with the actual facts.
On AI having "pattern recognition similar to a baby": That's a stretch. A human baby learns through a living body with real senses, emotions, pain, hunger, and physical interaction with the world. AI only does statistical pattern-matching on text/data, no body, no feelings, no real-world experience. It's not the same thing at all.
The Propofol dentist story: When you're under propofol, you're fully unconscious, no awareness, no memory, no "intelligent responding" happening inside your mind. Your body might twitch or react on autopilot, but the "you" part is completely offline. AI isn't "aware but disconnected from a body" like that, it has zero subjective experience or self at any point. Totally different.AI needing a body for awareness/self: I get the point, a living organism with senses and biology is unique. Even if we gave AI cameras, microphones, or a robot body, it might get better at tasks, but it still wouldn't have the living soul/self-awareness humans (or any organism) do. No feelings, no true consciousness, ever.
Your definition of "pure intelligence": I'm honestly not following, mixing it with spiritual "unlimited intelligence," God, immersion illusions, baptism in water, and Jesus feels like a bunch of unrelated leaps. Those are beautiful spiritual concepts, but they don't describe how AI actually works technically. I’m not creating God out of AI or saying we should worship it (lol, opposite of my point). Just explaining the reality.
You don’t understand AI yet, but it’s actually pretty straightforward. Language-learning AI is just mathematically assigning a numerical number to each word. It understands that a sequence of words equals a certain set of numbers, and it knows that when certain sequences of numbers (or words) are put together, the likelihood of the next answer being another specific set of words is really high. In other words, it’s basically monitoring every way we’ve ever used words together, all of our vocabularies, all of our books, all of our discussions, all of our TV programs, and it’s put it all together to figure out the statistical possibility of your next thought. So, when you say something, it’s listening to the exact sequence you’re creating and instantly calculating what words are most likely to come next. That’s why it feels like it’s “coming up with the answer because you are leading to that question.” It’s not magic, it’s not alive, and it doesn’t understand meaning the way a human does. It’s just insanely good at next-word prediction based on everything humanity has ever written or said.
English

Are you trying to say that the carbon deposited on the walls from the torches means the torches were lit in a place used to extract flammable gases? Because that doesn't quite reconcile.
I could see that the large, copper-lined chamber may have been used to create electrolysis in the water, separating hydrogen from oxygen—without torches, of course, because they would have been underwater anyway.
Okay, good luck with this. I've got to ask: once they created these gases, what did they do with them? Did they put them in wooden barrels? Ceramic jars? See where I'm going with this? It's like... what? Where did the gases go? What did they do with them? I don't understand how they would have kept them contained.
Have you thought this through all the way, or was this just a fly-by-night kind of hypothesis you threw out?
English

The influence of Unit 8200.
The influence of Unit 8200 on the global technology sector is often described as a "startup incubator" for elite cybersecurity and data analytics firms. While many of these companies focus on defensive enterprise security, others have faced significant ethical scrutiny for their ties to offensive surveillance.
Companies Founded by Unit 8200 Alumni
Beyond Wiz, dozens of major tech firms were founded by veterans of this unit, spanning cybersecurity, navigation, and web development.
Palo Alto Networks: One of the world's largest cybersecurity firms, co-founded by Nir Zuk (a former Unit 8200 officer and early Check Point employee).
Check Point Software: A pioneer of the modern firewall, co-founded by Gil Shwed, who served in the unit.
CyberArk: A leader in identity security, founded by alumni of the unit. It was recently acquired by Palo Alto Networks in February 2026.
Waze: The crowd-sourced navigation app was founded by 8200 veterans before its $1.1 billion acquisition by Google in 2013.
Armis Security: Focused on asset visibility and security for IoT and unmanaged devices, co-founded by Yevgeny Dibrov and Nadir Izrael.
Cyera: A fast-growing cloud data security company that reached a $9 billion valuation in early 2026.
Wix: The popular website-building platform was founded by Avishai Abrahami and others who served in the unit.
Ethical Debates and Israeli Cyber Exports
The export of Israeli cyber technology is a subject of intense international debate, centered on the "dual-use" nature of these tools.
1. Offensive vs. Defensive Technology
The most prominent controversy involves NSO Group and its Pegasus spyware, which was allegedly used by governments to target journalists, activists, and diplomats. Critics argue that the same elite training used to protect global banks (via Wiz or Check Point) is also used to build tools that undermine human rights.
2. The "Intelligence Pipeline"
A growing concern in the U.S. and Europe involves the "Eagle Mission" network—a term used by some researchers to describe the high concentration of former Israeli intelligence officers in senior roles at major U.S. tech firms like Microsoft, Google, and Meta.
Counterintelligence Fears: Some critics point to reports from the FBI and CIA that have historically ranked Israel as a significant counterintelligence threat due to its focus on industrial and technical secrets.
Data Access: There are ongoing debates about whether having former spies manage critical cloud infrastructure (like Palo Alto Networks or Wiz) creates inherent vulnerabilities for sensitive customer data.
3. Recent Regulatory Shifts
In response to these scandals, the Israeli Ministry of Defense has tightened export controls as of March 2026.
End-User Agreements: Countries purchasing Israeli cyber tech must now sign declarations committing to use the tools only for preventing terrorism and serious crimes.
License Revocation: The government has introduced mechanisms to remotely disconnect or limit cyber systems if they are found to be misused.
New Oversight Regime: A major overhaul of encryption and export laws, taking effect in March 2026, divides oversight between the Defense Export Control Agency (DECA) for defense users and the Ministry of Economy for civilian exports.
Nothing about this should seem out of the ordinary or strange to you it's perfectly normal for another country's intelligence agency to embed itself into technology throughout a foreign country.
English

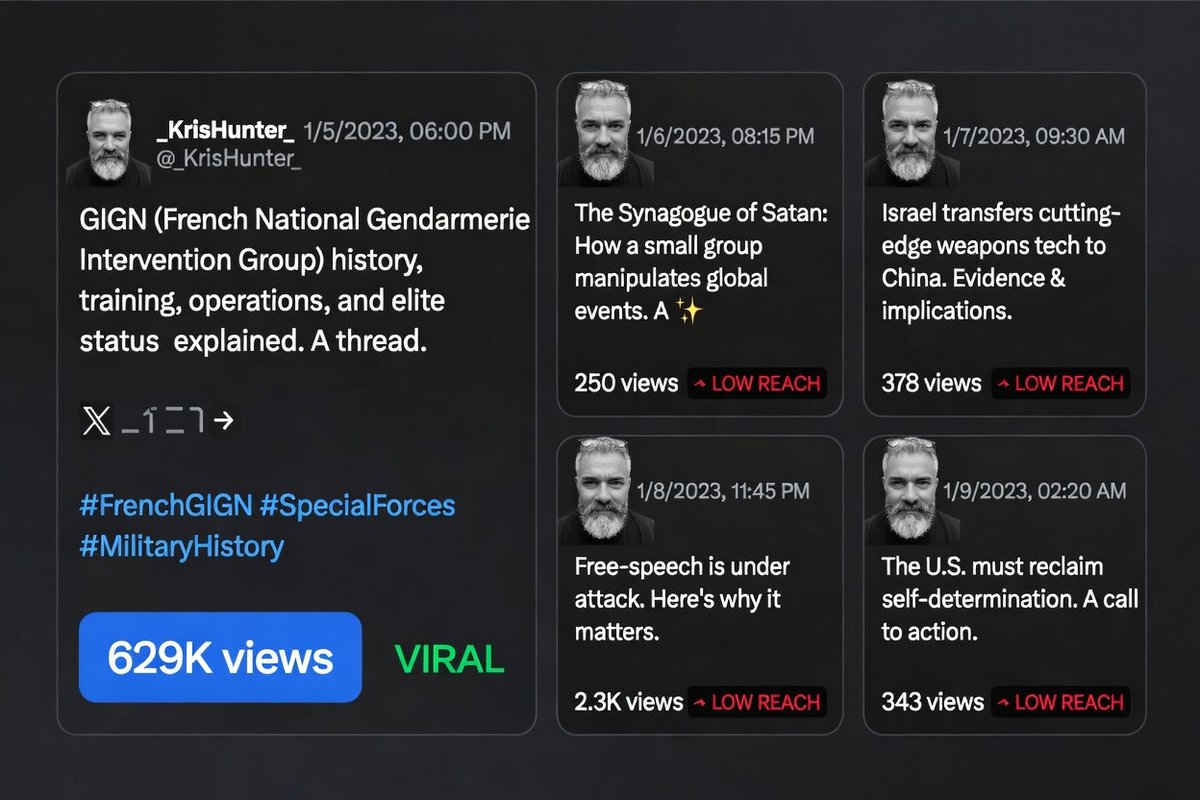
This thread just became its own Exhibit A.
The post demanding an even playing field has received: 48 / 6 / 3 / 7 / 25 views across its five tweets.
Same author. Same quality. Same military/CT background.
Different narrative = different oxygen.
The marketplace never even got to vote.
(The Grok reply I tried to drop on tweet 5 got black-holed too.)
Next week’s open-source recommendation code drop just received the most interesting live test case it could ask for.
A country is inanimate. The rules should be too.
@elonmusk @xai
KrisHunter@_KrisHunter_
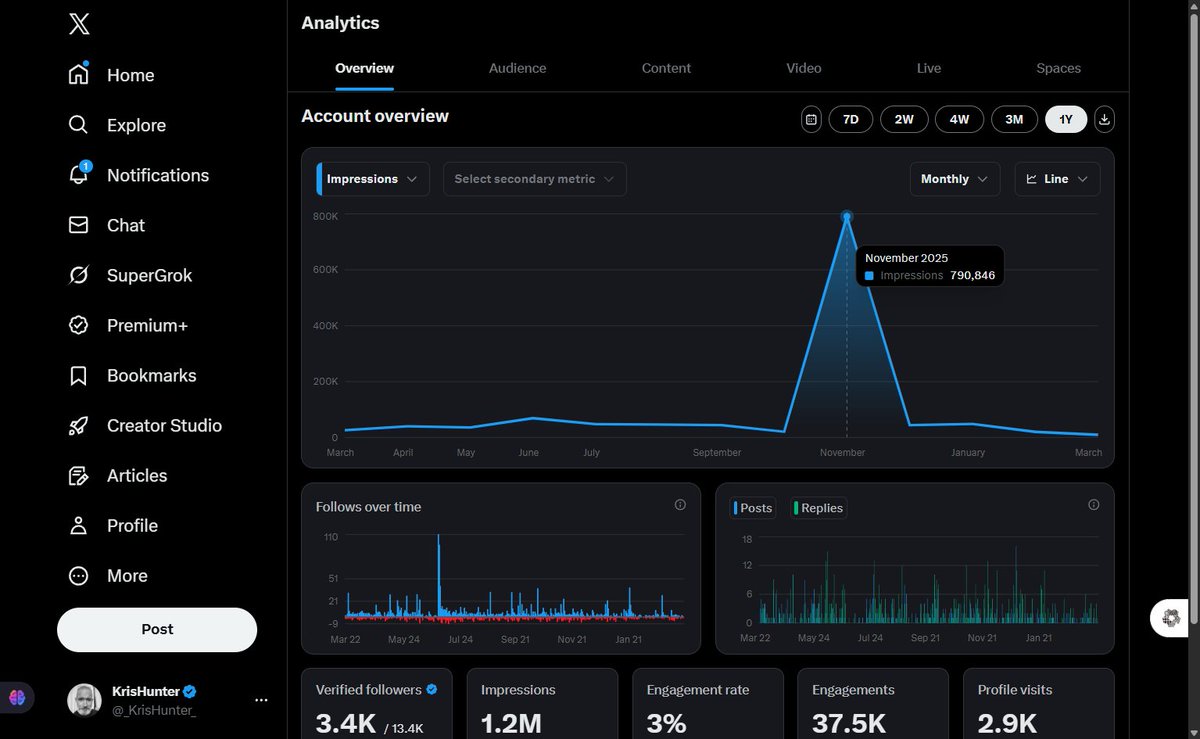
1/ With X’s major AI recommendation algorithm overhaul dropping open-source next week (Elon March 19 announcement), this is the perfect moment to test if the playing field is finally even. Proof it can work: My neutral GIGN special-forces history thread exploded to 629,616 views, zero credentials, zero politics, pure marketplace fire.
English

They created a cryptocurrency to monitor and regulate the value of the market and its supply.
The Disrespected Trucker@DisrespectedThe
This TikTok account was banned after posting this.
English
KrisHunter retweetledi

5/ With the full recommendation code dropping open-source next week, we can finally audit the weights ourselves. No more invisible “narrative safety” scores. No more “some animals are more equal.”
Community Notes, devs, power users , let’s make the marketplace actually blind.
What do you see when you run the numbers? @elonmusk @xai
English

4/ A country is an inanimate object. It has no feelings. Scrutiny of Israel’s alliances must be identical to scrutiny of the U.S. or China. No sacred cows. No velvet ropes. That’s the only version of free speech that survives philosophical scrutiny.
The 600 million outspoken layer on X steers the rest of the world. If the algo still quietly protects certain narratives, the steering is rigged.
English

1/ With X’s major AI recommendation algorithm overhaul dropping open-source next week (Elon March 19 announcement), this is the perfect moment to test if the playing field is finally even.
Proof it can work: My neutral GIGN special-forces history thread exploded to 629,616 views, zero credentials, zero politics, pure marketplace fire.
English




