L4ys
2.5K posts

@_L4ys
Co-Founder of @TrapaSecurity and @PwnableTW MSRC Top 100 / ZDI Platinum Hunting bugs for fun





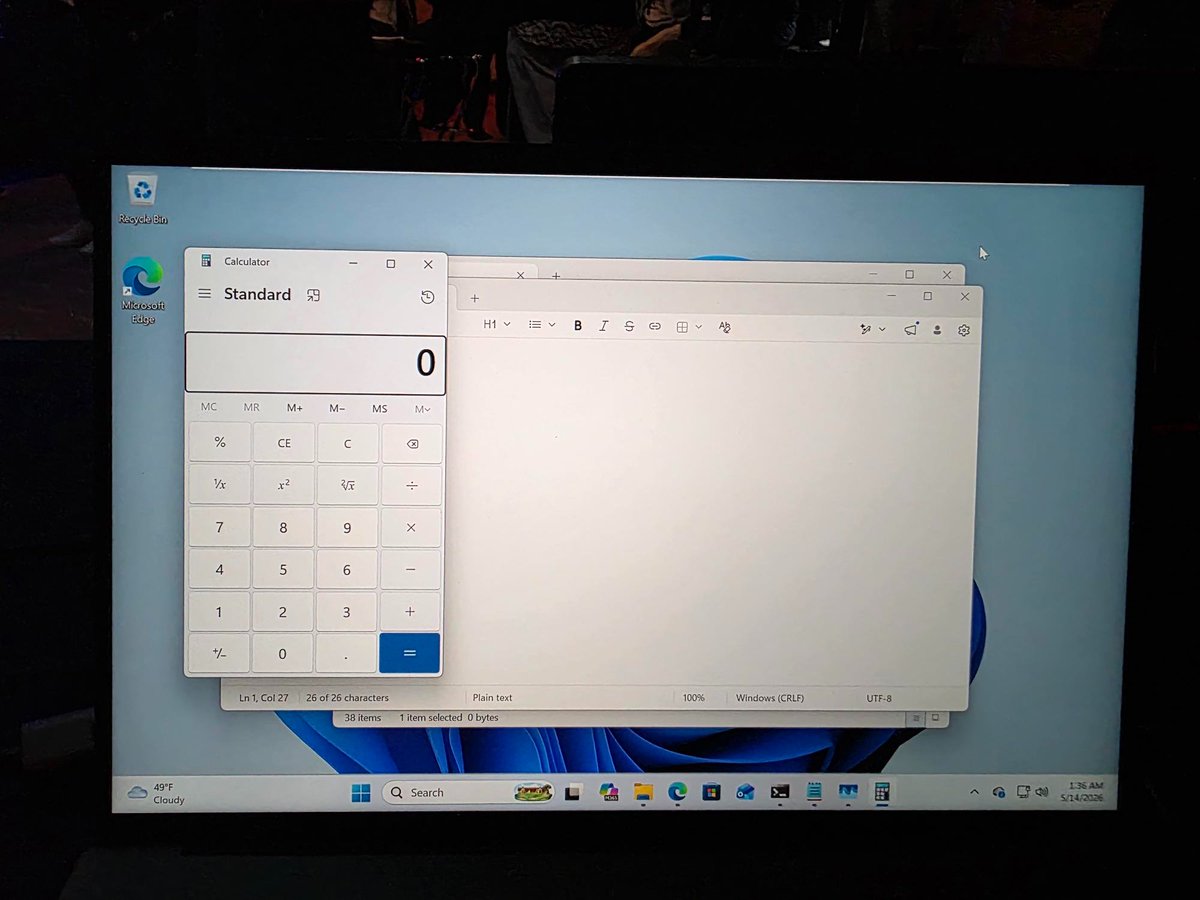


Amaze! Amaze! Amaze! @orange_8361 of DEVCORE Research Team was able to exploit Edge with a sandbox escape! If confirmed, we wins $175K. He's off to the disclosure room to explain how he did it. #Pwn2Own #P2OBerlin

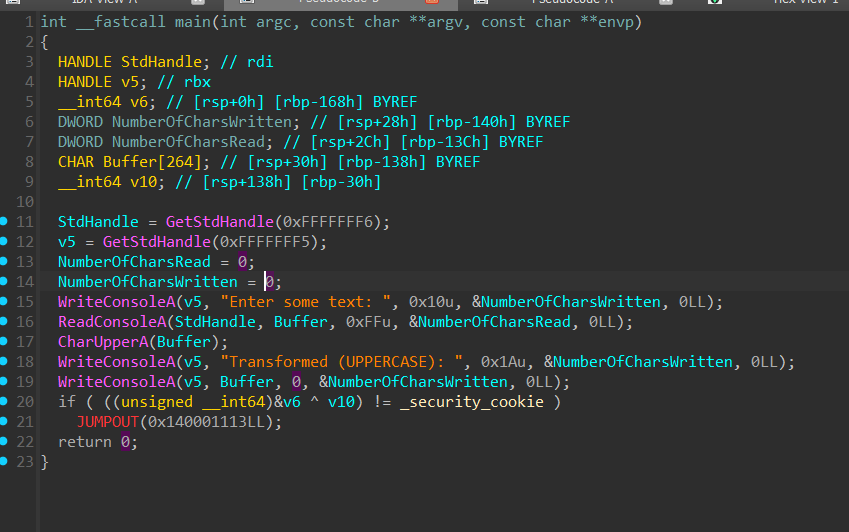
I’ll share the story behind CVE-2022-33649 in a few days before I forget…🤔 an interesting bug and methodology


I'm seeing this question being asked a lot! I think the traditional 90+30 day responsible disclosure standard is dead (or should be). It's too dangerous to be holding onto vulns for this long now. I've been thinking about alternative responsible disclosure policies that work better for a post-AI era but it's a pretty tricky problem!