
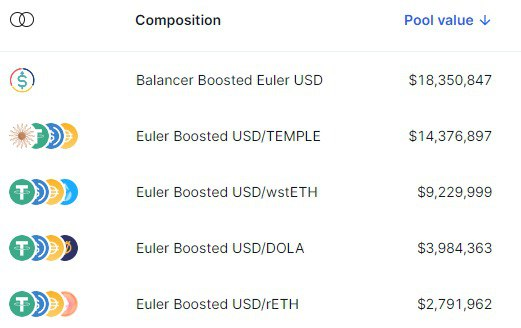
@ScopeProtocol @eulerfinance @AngleProtocol how about balancer bb-euler-usd?
18m liquidity, of which 8m is cash, will this be the only exit channel for euler users.
@templedao
must be in a hurry
English
W.Max
42 posts

@_William_Max
Solidity developer for #Defi. Auditor @code4rena.



It's times like this... $ERN


Keen to dig into asset management accounting, or maybe issuance and redemption logic? 🔎 Get amongst all of the above (and more!) in @EthosReserve's audit, with $144,750 USDC in the reward pool for Wardens who can find vulns. Start hunting now: rebrand.ly/C4-ethos-reser…










wstETH/ETH Curve gauge vaults on Arbitrum & Optimism were exploited a few hours ago, and we immediately paused the dForce Vaults - other parts of the protocol remain intact and user funds are SAFE with dForce Lending. We will come back with a detailed report and remedies soon.


