Lucas Leong retweetledi
Lucas Leong
1.4K posts

Lucas Leong
@_wmliang_
Play hard, Exploit hard @[email protected]
Taipei Katılım Kasım 2013
564 Takip Edilen2.4K Takipçiler
Lucas Leong retweetledi
Just derestricted a now-fixed kernel bug in Pixel 10. I think this ranks as the most easily exploited kernel bug of all time😬
Thanks to @tehjh for collab'ing on this driver and full credits for noticing this bug in the first 5 minutes of auditing😂
project-zero.issues.chromium.org/issues/4634382…
English
Lucas Leong retweetledi

Coruna exploit kit is targeting iOS.
Coruna leverages 23 exploits against Apple devices running iOS 13-17.2.1. It is being used for espionage, and by financially motivated actors to steal crypto.
Update your iOS devices, and learn more about this threat: bit.ly/4rbeltc

English
Lucas Leong retweetledi

A Race Within A Race: Exploiting CVE-2025-38617 in Linux Packet Sockets.
A step-by-step guide to exploiting a 20-year-old bug in the Linux kernel to achieve full privilege escalation and container escape, plus a cool bug-hunting heuristic.
open.substack.com/pub/calif/p/a-…
English
Lucas Leong retweetledi
Lucas Leong retweetledi

In the final part of his blog series, @tiraniddo tells the story of how a bug was introduced into a Windows API.
Code re-writes can improve security, but it’s important not to forget the security properties the code needs to enforce in the process.
projectzero.google/2026/02/gphfh-…
English
Lucas Leong retweetledi

Clang's -Wthread-safety, named "Context Analysis" for the Linux kernel finally merged after a year's worth of work: git.kernel.org/torvalds/c/092…
docs.kernel.org/next/dev-tools…
Currently opt-in; go and set 'CONTEXT_ANALYSIS := y' for any kernel code you're developing. Needs Clang 22+.
English
Lucas Leong retweetledi

New Engineering blog: We tasked Opus 4.6 using agent teams to build a C compiler. Then we (mostly) walked away. Two weeks later, it worked on the Linux kernel.
Here's what it taught us about the future of autonomous software development.
Read more: anthropic.com/engineering/bu…
English
Lucas Leong retweetledi

UAC-0001 (aka #APT28 or #FancyBear) exploits CVE-2026-21509 to target Ukraine and EU with COVENANT framework. Details (UA only): cert.gov.ua/article/6287250
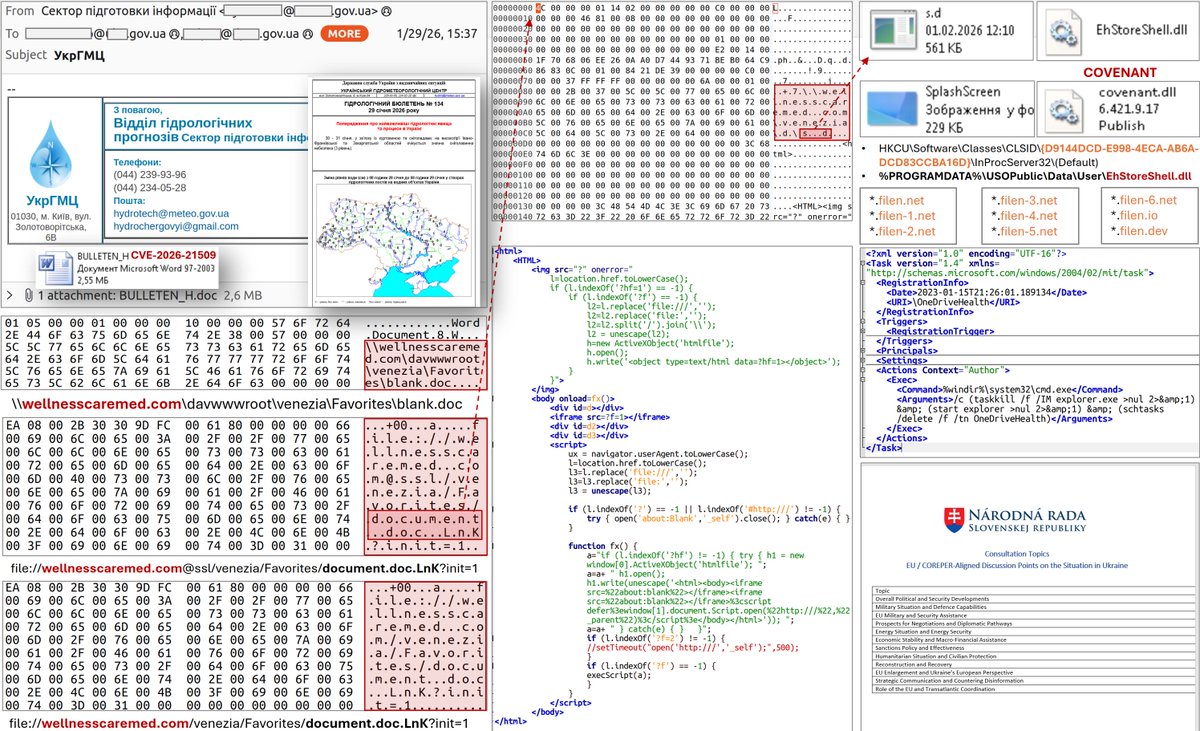
English
Lucas Leong retweetledi
It's been just over a year since CVE-2024-54529 was patched. To celebrate, I'm open-sourcing my full PoC exploit for this CoreAudio type confusion vulnerability 🔊
The code is right here! Enjoy: github.com/googleprojectz…
English
Lucas Leong retweetledi
Lucas Leong retweetledi

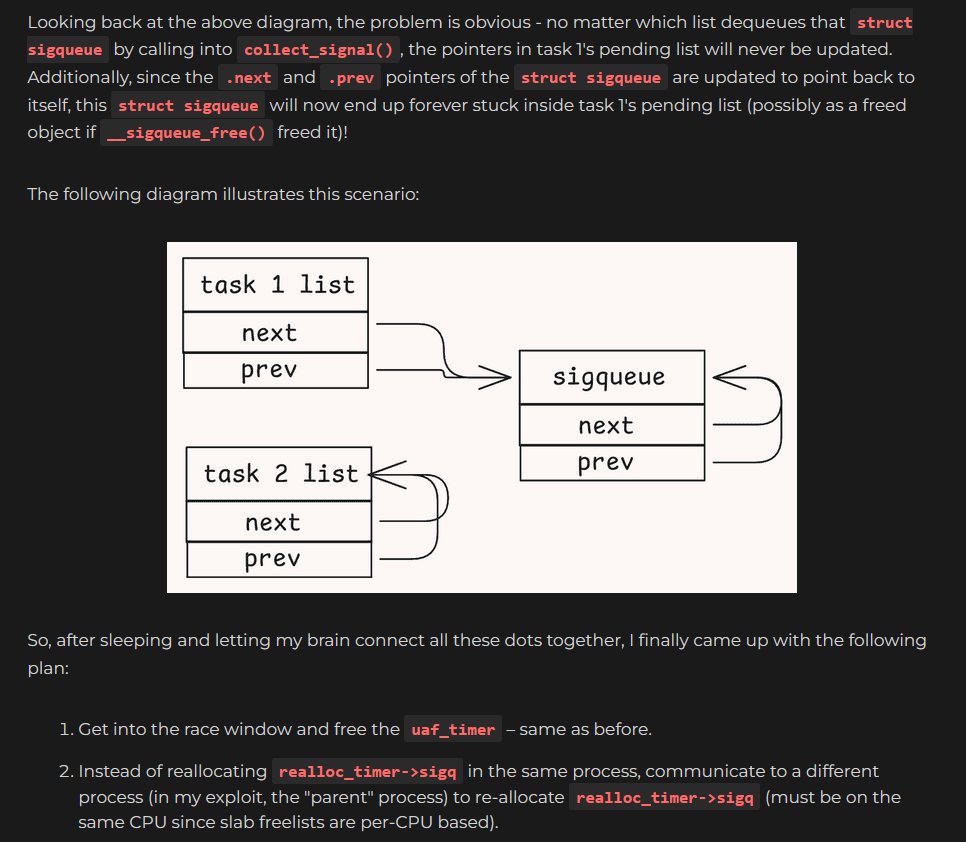
And finally, part 3 of my blog post series on CVE-2025-38352 – Uncovering Chronomaly
faith2dxy.xyz/2026-01-03/cve…
English
Lucas Leong retweetledi

I'm Boris and I created Claude Code. Lots of people have asked how I use Claude Code, so I wanted to show off my setup a bit.
My setup might be surprisingly vanilla! Claude Code works great out of the box, so I personally don't customize it much. There is no one correct way to use Claude Code: we intentionally build it in a way that you can use it, customize it, and hack it however you like. Each person on the Claude Code team uses it very differently.
So, here goes.
English
Lucas Leong retweetledi

CVE-2025-68260: rust_binder: fix race condition on death_list
First CVE was registered for the new Binder kernel driver written in Rust. The vulnerability is a race condition caused by a list operation in an unsafe code block.
@gregkh/T/#u" target="_blank" rel="nofollow noopener">lore.kernel.org/linux-cve-anno…

English
Lucas Leong retweetledi
really cool to see some well-conducted academic research on this topic, I think reachability is super important for triaging.
@binarly_io also implements reachability analysis at scale to reduce false positive findings:
binarly.io/blog/binarly-t…
English
Lucas Leong retweetledi

Wow, remote OS command injection (from the same network segment) in FreeBSD IPv6 stack via router advertisement packets: freebsd.org/security/advis…
rtsold passes the unescaped domain search list option from the RA packet to the resolvconf shell script.
English
Lucas Leong retweetledi
Lucas Leong retweetledi
Lucas Leong retweetledi

Happy to share our work "Cottontail: LLM-Driven Concolic Execution for Structured Test Input Generation" will appear in S&P'26!
Paper: haoxintu.github.io/files/sp2026-c…
Code: github.com/Cottontail-Pro…
Special thanks to @nim_gnoes_eel, @JNUYUXIAN, @spinpx, @LingxiaoJiang, and @mboehme_ ♥️



English
Lucas Leong retweetledi

New on our Frontier Red Team blog: We tested whether AIs can exploit blockchain smart contracts.
In simulated testing, AI agents found $4.6M in exploits.
The research (with @MATSprogram and the Anthropic Fellows program) also developed a new benchmark: red.anthropic.com/2025/smart-con…
English