Sabitlenmiş Tweet
Ale
3.4K posts



Claude Code está escribiendo React de MIERDA
Lo acabo de confirmar: React Doctor le puso 42/100 (CRÍTICO) a un proyecto mío vibe-codeado.
Detectó 36 issues en 18 archivos.
State mal gestionado, effects rotos, keys con array index, dead code, problemas de performance y accesibilidad… todo.
Este será el Good Doctor de los vibe-coders a partir de ahora:
✅ Funciona con Next.js, Vite y React Native
✅ Se instala como skill en Claude, Cursor, Windsurf y +50 agents de IA
✅ GitHub Action + plugin de ESLint/oxlint incluido
REPOOO👇
Español
Ale retweetledi
💥 Introducing "Dirty Frag"
A universal Linux LPE chaining two vulns in xfrm-ESP and RxRPC. A successor class to Dirty Pipe & Copy Fail.
No race, no panic on failure, fully deterministic. ~9 years latent.
Ubuntu / RHEL / Fedora / openSUSE / CentOS / AlmaLinux, and more.
Even if you've applied the "Copy Fail" mitigation, your Linux is still vulnerable to "Dirty Frag". Apply the Dirty Frag mitigation.
Details:
dirtyfrag.io
GIF
English
Ale retweetledi

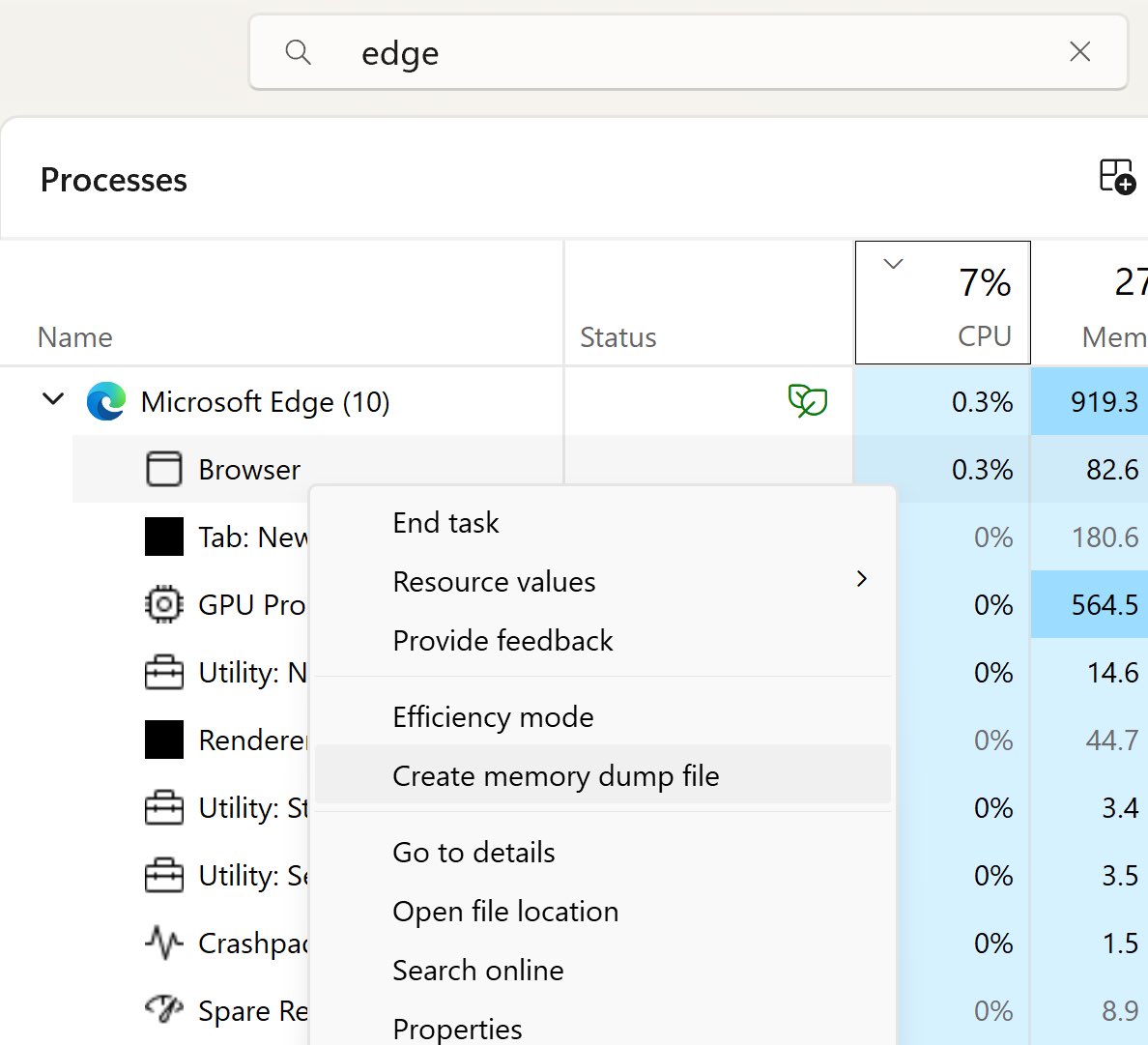
‼️🚨 Microsoft calls this "intended behaviour," so here we go.
How to dump the credentials of every user stored in Microsoft Edge:
1. Open Edge. Don't browse anywhere, just open it.
2. Flip to Task Manager, find Edge, expand the task.
3. Highlight the "browser" sub-task, right-click, and choose "Create Memory Dump."
4. Open the dump file and look for credentials.
The logged-in Windows user can dump every stored Edge credential with no additional rights. Which means any malware that user executes has those credentials for the asking.
Thanks to Rob VandenBrink at SANS: isc.sans.edu/diary/32954

English
Ale retweetledi
Ale retweetledi

‼️🚨 One of the world's largest Certificate Authorities, DigiCert, was compromised by a malicious screensaver file sent through a customer support chat. Their antivirus blocked the malware four times. The agent kept clicking. The fifth try got through.
27 code signing certificates were stolen and used to sign malware.
DigiCert ultimately revoked 60 certificates.
Per DigiCert's incident report, filed in Mozilla's CA compliance tracker as Bug 2033170, here is how it unfolded:
April 2: an attacker contacted a DigiCert helpdesk agent through the company's customer support chat channel, posing as a customer. The lure was a zip file pitched as a screenshot. Inside the zip was a .scr file. On Windows, .scr files are executables, and this one carried a malicious payload.
Opening a file a customer sent through the official support channel is what an agent is supposed to do. Support staff are the one role designed to accept files from strangers.
DigiCert's endpoint security blocked four infection attempts. On the fifth, the support analyst's machine was infected.
DigiCert detected the infection, ran an investigation, and concluded the incident was contained.
Eleven days later, an external researcher tipped DigiCert off about misuse of DigiCert-issued code signing certificates in the wild. That tip led to the discovery of a second compromised machine, belonging to a different support analyst, infected through the same vector. The EDR on that machine had not been functioning correctly, so the original investigation missed it.
The second machine gave the attacker access to DigiCert's internal support portal. That portal lets support staff reach limited views of customer accounts, including initialization codes for ordered but not-yet-issued code signing certificates. Combining a stolen initialization code with an approved order let the attacker pull a real, validly issued code signing certificate. They did this 27 times.
DigiCert's own list of what went wrong:
- File-type filtering on the customer support chat channel did not catch the .scr
- EDR coverage was inconsistent and incomplete, creating a blind spot
- Initialization codes for code signing certificates were not adequately protected
DigiCert says it got lucky. An outside researcher found the malware abuse before DigiCert did. Without that tip, the second machine and the active certificate theft might still be running today.


English

@epiccccc777 @pyckens69 @Krosecato @LatamData Bro, nunca dije lo contrario… una cosa no quita la otra, la clave única no tiene ni 2FA implementado, las personas se la comparten entre sí, y así pasan… pero bueno si te conformas con que en otros países también hay hackeos y bla bla está todo bien… 👍 son opiniones.
Español

@abalegno @pyckens69 @Krosecato @LatamData bro, han existido hackeos hasta en el pentagono, el tema de hacker es muy complejo, aunque en chile contrate a los mejores en ciberseguridad existe siempre alguien que puede hackear el sistema, nadie esta seguro en ese ambito, ni usa, ni rusa, ni japon.
Español

@FQodlelxdC5674 @LatamData Ciberseguridad e IA van de la mano, que pasó ? Se te acabaron los tokens de Claude y ahora entraste a X a postear ??? ⚰️☠️
Español

@abalegno @LatamData El que compara ciberseguridad con IA...🤣🤣
Re ignorante ya se de que país eres jaja.
Español

@epiccccc777 @pyckens69 @Krosecato @LatamData El debate no es si la clave única es útil o mejor que otro países...
Es si el Estado protege adecuadamente los datos que le obligas a entregar.
Español

@abalegno @pyckens69 @Krosecato @LatamData es que es verdad, no sabes lo burocratico que es conseguir documentos personales en paises vecinos, es realmente un lujo la clave unica, pero si no has vistos otras realidades dificil que te pegues el cacho.
Español
Imagínate cuando los Japoneses se enteren que existe está versión en Argentina:
Gaak.fr@gaak_fr
🎵🇯🇵 INSOLITE : L'OPENING CULTE de l'anime "Evangelion" n'a pas quitté le top 50 des titres les plus chantés dans les karaokés japonais depuis 1 000 SEMAINES (environ 19 ans). 👑
Español

@pyckens69 @Krosecato @LatamData La seguridad lo es todo. Por eso el compañero que desvía el foco alegando que es un “lujito” que otros países no tienen, carece de sentido.
Español

@abalegno @Krosecato @LatamData Ningún sistema es anti hackers, lo importante es que mejoren la seguridad
Español

@Krosecato @LatamData El lujo no sirve de nada si te lo hackean. El problema no es el sistema, es la seguridad.
Español

@abalegno @LatamData La clave unica es un lujito que ningún país vecino tiene
Español

El Cholo Simeone los últimos 10 años:
- 2015: Liga ❌️ Copa ❌️ UCL ❌️
- 2016: Liga ❌️ Copa ❌️ UCL ❌️
- 2017: Liga ❌️ Copa ❌️ UCL ❌️
- 2018: Liga ❌️ Copa ❌️ UCL ❌️
- 2019: Liga ❌️ Copa ❌️ UCL ❌️
- 2020: Liga ❌️ Copa ❌️ UCL ❌️
- 2021: Liga ✅️ Copa ❌️ UCL ❌️
- 2022: Liga ❌️ Copa ❌️ UCL ❌️
- 2023: Liga ❌️ Copa ❌️ UCL ❌️
- 2024: Liga ❌️ Copa ❌️ UCL ❌️
- 2025: Liga ❌️ Copa ❌️ UCL ❌️
- 2026: Liga ❌️ Copa ❌️ UCL ❌️
🤑 Inversión en los últimos 10 años:
💰 1,7 BILLONES DE EUROS 💸
🏆 Titulos: 1 (UNO) 🥶🧊
Más de un billon y medio de euros para ganar UN SOLO TÍTULO. Otro año en la oficina del DT más mediocre y fracasado de la historia.

Español

#ClaveUnica que les cuesta implementar 2FA ?
Germán Fernández@1ZRR4H
🔥 Ok, levantamos una herramienta simple pero potente, permite consultar si un RUT determinado aparece en la filtración de casi 250.000 credenciales de #ClaveUnica expuestas en Telegram (#Rutify). 🔹 leaks.cronup.com 📢 Si puedes, COMPARTE, quizás alguien cercano lo necesite y aún no lo sepa.
Español
Ale retweetledi

Han clonado Claude Design y puedes usarlo gratis y sin limites.
Se llama Open Design, un proyecto open source que te deja usar Claude para workflows de diseño sin pagar.
Sin suscripciones.
Sin límites (como la versión oficial).
Acceso total.
Esto es lo que puedes hacer:
— Generar diseños UI/UX con Claude
— Convertir prompts en diseños reales
— Sustituir herramientas de diseño caras en muchos casos
— Personalizarlo completamente (es open source)
Está hecho para devs, indie hackers y creadores que no quieren quemar dinero en herramientas.
De esos repos que pasan desapercibidos hasta que de repente todo el mundo los usa.
Si usas AI + diseño, tienes que probarlo
Enlace abajo 👇
(guárdalo antes de que explote)
Español
Ale retweetledi

⚠️Google Gemini CLI Vulnerabilities Allow Attackers to Execute Commands on Host Systems
Source: cybersecuritynews.com/google-gemini-…
A critical remote code execution vulnerability in the Google Gemini CLI and its associated GitHub Action. Assigned a maximum severity score of CVSS 10.0, the flaw allowed unprivileged external attackers to execute commands directly on host systems.
This vulnerability effectively turned automated CI/CD pipelines into potential attack vectors in the supply chain. The core issue was how the Gemini CLI handled workspace trust in non-interactive environments.
#cybersecuritynews
English